twelvesec/PwnPad
GitHub: twelvesec/PwnPad
PwnPad 是一个面向硬件安全学习的低成本动手平台,通过可扩展的挑战套件解决理论与实践脱节的问题。
Stars: 515 | Forks: 38

# PwnPad:硬件黑客学习平台
       
## 📖 PwnPad Wiki
Want to build your own PwnPad? The PwnPad Wiki has a thorough guide, documentation, and a step-by-step hardware hacking learning path: https://github.com/twelvesec/PwnPadWiki/wiki - it’s the best place to begin.
## 🎯 目标
**PwnPad** was created for anyone curious about hardware hacking, no prior experience required. The project is designed to be as affordable and accessible as possible: you can build the entire setup for **under \$20**, and complete all existing challenges using about **\$50 worth of basic tools**.
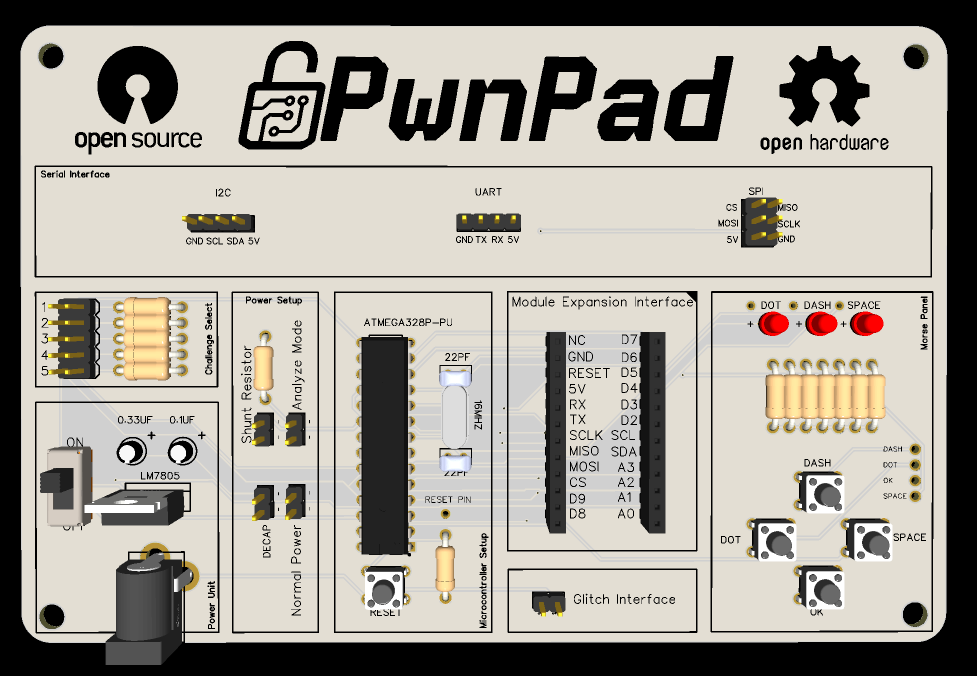
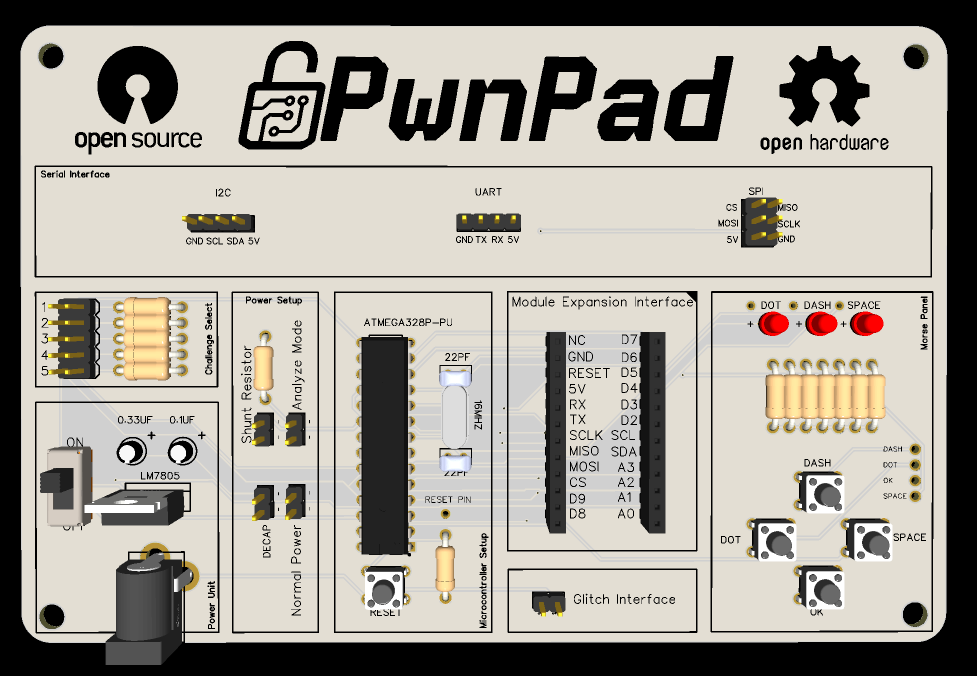
Through hands-on learning, PwnPad guides you from the very beginning — including PCB manufacturing, soldering, and firmware extraction, all the way to advanced exploitation techniques. You'll gain practical experience with:
* Serial communication protocols like **UART**, **SPI**, and **I2C**
* **Firmware extraction** via ISP and EEPROM dumps
* Building your own **ISP programmer**
* Performing **voltage fault injections** and **timing-based side-channel attacks**
A key feature of PwnPad is its **challenge selector via jumper pins**, no need to reflash the device when switching between challenges. Simply set the pins to load a different challenge from the pre-flashed firmware.
PwnPad aims to bridge the gap between theory and practice by offering a structured, hands-on path into the world of embedded systems and hardware security.
## 📦 文件夹概览
| Folder | Description |
| ------------- | -------------------------------------- |
| `firmware/` | Firmware for each challenge |
| `hardware/` | Schematics, PCB layout, BOM, 3D Models |
| `challenges/` | Learning objectives per challenge |
| `tools/` | Scripts for building/flashing |
| `docs/` | Miscellaneous resources |
| `modules` | Modules' Gerbers & Schematics |
## 🔍 挑战概览
|#|Name|Topics|Description|
|---|---|---|---|
|1|Serial Snitch|`#UART`|Intercept and decode UART communication.|
|2|Echo Chamber|`#UART`|Intercept and decode UART communication, with security through obscurity.|
|3|Bus Whisperer|`#I2C`|Spy on I2C traffic to extract secrets.|
|4|Invisible Wires|`#I2C`|Attack I2C when slave devices are missing.|
|5|Code Heist|`#SPI` `#ISP` `#Flash` `#UART`|Dump and analyze firmware from flash.|
|6|Hard Leak|`#SPI` `#ISP` `#EEPROM`|Extract data from the internal EEPROM.|
|7|Power Trip|`#FaultInjection` `#UART`|Use glitching to bypass dead code statements.|
|8|Glitch Storm|`#FaultInjection` `#UART`|Use glitching to bypass password verification.|
|9|Clock Spy|`#SideChannel` `#UART`|Leak secrets using timing variations.|
|10|Tempo Leak|`#SideChannel` `#UART`|Leak secrets using timing variations with a twist.|
|11|Chaos Chain: Glitchgate|`#FaultInjection` `#UART` |Combine UART and glitch attacks to break in.|
|12|Chaos Chain: Timebomb|`#UART` `#SideChannel`|Combine UART and chain timing leaks to break in.|
|13|Pizza Order|`#SPA` `#SideChannel`|Use a basic oscilloscope to exfiltrate the password.|
|14|Ladybirds|`#SWD` `#Reversing` `STM32`|Use a SWD debugger and patch the memmory to access the safe.|
|15|Ladybird I Am Your Father|`#JTAG` `#Reversing` `STM32`|Extract the firmware using JTAG and later patch the memmory to access the safe.|
## 🚀 入门指南
You can find the complete building instructions in the file: `docs/PwnPad_building_instruction.pdf`
If you're new to soldering or just getting started with hardware hacking, this video will guide you through assembling your PwnPad.
[](https://www.youtube.com/watch?v=uaiB-Esttt4)
📺 **Click the image above to watch the tutorial on YouTube.**
### 🔬 解决挑战的推荐设备
- Multimeter
- Arduino UNO
- Logic Analyzer
- Jumper Wires
- Raspberry Pi Pico & MOSFET for the voltage fault injection challenges.
### 🕹️ 游戏玩法
Once you've assembled and flashed your PwnPad, navigate to the challenges/ directory and open the objective file for the specific gamified challenge you want to play.
To get started, simply configure the jumpers as described in the challenge instructions and press the RESET button on your PwnPad.
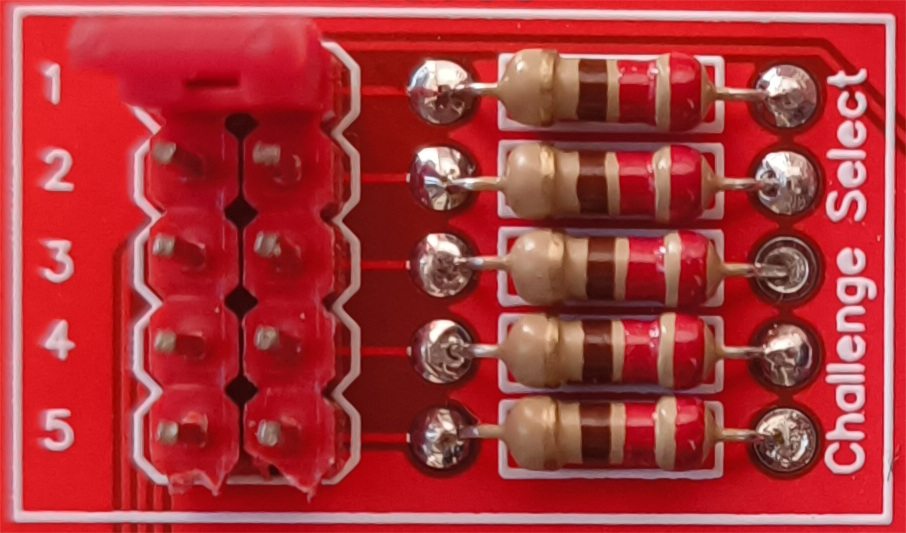
For instance, to play the challenge "Serial Snitch", go to challenges/Serial Snitch.md and set the jumper pins as shown in the image below:
```
# **挑战 1:"Serial Snitch"**
As a skilled hardware hacker, you've intercepted a mysterious device recovered from a rogue tech syndicate. The device, dubbed **"Specter-1"**, controls access to a secret underground server, but its interface remains locked behind an unknown UART configuration.
Your mission is clear:
1. **Identify the UART pins** you've uncovered during your investigation.
2. **Determine the correct baud rate** to establish a stable connection.
3. **Access the device’s command interface** and unlock control over the system’s lighting grid.
## 挑战选择
1 --> 1
2 --> 0
3 --> 0
4 --> 0
5 --> 0
```
If you'd like to track your challenge progress and submit flags, run:
```
bash ./tools/webapp/start.sh
```
Then open your browser and navigate to: `http://127.0.0.1:12530`
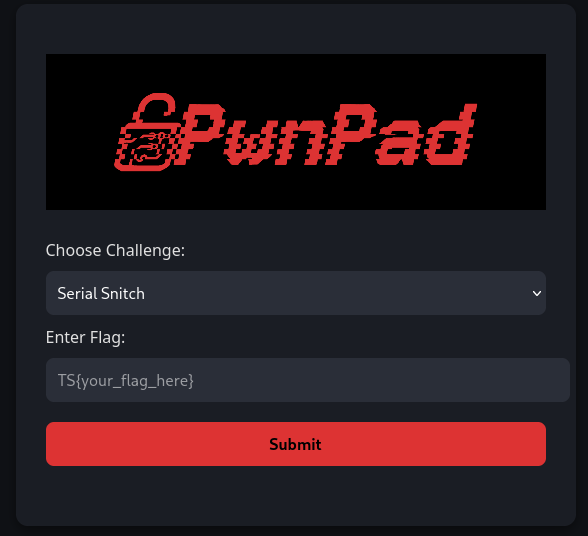
There you can submit your flags and monitor your progress.
### 🧩 创建新挑战
1. **Add a Header File**
Create a new header file named something like `challenge13.h`.
2. **Define Your Challenge Function**
Inside the header file, define your challenge function using this template:
void challenge_template(void) {
// Initialize I/O
while (1) {
// Your Main Challenge Logic
}
}
### 🔀 注册您的挑战
3. **Update the Main Switch**
In `PwnPad.ino`, locate the `switch` statement used for challenge selection. Add a new `case` for your challenge number, and call your function from there.
4. **Challenge Selector Logic**
The challenge selection is handled using **5 binary jumper pins**, where:
- **Pin 1** = Least Significant Bit (LSB)
- **Pin 5** = Most Significant Bit (MSB)
For example:
Binary: 00011 → Decimal: 3 → Selects Challenge 3
Make sure your challenge is self-contained, documented, and has clear **goals** in its own folder.
## 🛣️ 路线图
### 🧠 软件增强
- [x] Introduce a Simple Power Analysis (SPA) challenge
- [ ] Introduce a Differential Power Analysis (DPA) challenge
### 🔧 硬件升级
- [x] Simplify the Fault Injection interface usingIP switches to disable capacitors
- [x] Implement an interface for external module plug-ins
- [x] Develop new add-on modules (fully backward-compatible with existing PwnPad versions):
- [x] External Storage Module
- [x] BLE (Bluetooth Low Energy) Module
- [ ] RF (Radio Frequency) Module
## 🪪 许可
This project is licensed under the **GNU General Public License v3.0**. See [LICENSE](LICENSE) for full text.
Created by Georgios Roumeliotis from TwelveSec
标签:Arduino, Black Hat Arsenal, CMS安全, CSS3, EEPROM, HTML5, I2C, ISP编程, JavaScript, PCB设计, SPI, UART, 低成本实验, 固件提取, 学习平台, 实践教学, 开源硬件, 手把手实验, 数据可视化, 时序侧信道攻击, 电压故障注入, 电子工程, 硬件安全, 硬件攻击, 硬件黑客, 网络安全, 跳线选择挑战, 隐私保护