arceuzvx/Cybersecurity_resources
GitHub: arceuzvx/Cybersecurity_resources
一份按学习路径组织的免费网络安全电子书合集,覆盖从入门到高级的红蓝队技能与实战平台导航。
Stars: 33 | Forks: 4
# 精选网络安全资源 (2026)
### 免费网络安全电子书、学习路线、CTF、参考资料与学习资源
[](https://awesome.re)
一个**全面的、以学习路线为驱动的免费网络安全电子书合集**,按**学习阶段和专业化方向**组织。
本仓库专为以下人群构建:
- 进入网络安全领域的学生和初学者
- SOC Analysts & Security Engineers
- 恶意软件分析师 & 数字取证学习者
- 渗透测试人员 & 红队后备军
- 正在准备实习、认证和求职的自学者
## 🧭 如何使用本仓库
- 遵循学习路线:**基础 → 防御 → 攻击 → 专业化方向**
- 电子书是**参考资料**,并非必读内容
- 选择与你的**职业赛道**相符的资源
- 你**不需要**阅读所有内容
# 初级 BEGINNER
## 🟢 基础知识 — 核心知识与技能
### 网络安全 Python 电子书
- [Python for Offensive PenTest – A Guide to Ethical Hacking and Penetration Testing](https://mega.nz/file/9zdQmAzA#G0umpFTkFzZBlobrlwP-7h2q1xty6N9fhKnWYAwN2o4)
- [Violent Python for Hackers, Forensic Analysts, Penetration Testers and Security Engineers](https://mega.nz/file/hrdyER4Z#Yw2RShTIlyv1oCj1pnrJKZ4bjRJB9ppF65g6_CkgB20)
- [Learning Python](https://mega.nz/file/cjcmTbaZ#wEBMHBdO6q-WKW1mkqeusEnjZAac5T1hXLWWr6pZFlE)
- [Black Hat Python – Programming for Hackers and Pentesters](https://mega.nz/file/F2dHVLhC#iw3gW9eyFP1nHl2OKDpWZAs4FTboWPlekx47iVGvU1)
- [Modern Python Cookbook](https://mega.nz/file/R78ijShK#wCgvS865nwiubZpIA6VkVqHfpVrktlcwWErbAuID5LI)
- [Hacking with Python – Ultimate Beginner's Guide](https://mega.nz/file/A3cxzDqI#DI5K27Fj-FjEWOUACH1t3XRTl3ieZIRggmDG8RG3C7k)
- [Python Web Penetration Testing Cookbook](https://mega.nz/file/I6tHCRAZ#XNwqVn6lGx0KmlGTopGPDj7ypF_BFCU4toxFtPZMKlw)
- [Mastering Python Networking](https://mega.nz/file/ArlEFIqa#fmNxFhInh04deqtoOiQREZG6Dtvqgla9LeLmdk0r5Bc)
- [Machine Learning and Security](https://mega.nz/file/UvdCRBpA#0Sy1Onol4pIV4qx5Om0huLh7pKx8QLpdrqmk6XQmTPU)
## 🟡 防御方向 — 蓝队、SOC 与事件响应
### 恶意软件分析电子书
- [Malware Analysis Fundamentals](https://mega.nz/file/s2tzEbDQ#dgL2kTCZ5PMGP_Ybb4x_nop7WsQP0nxAN7uUOvOjNeU)
- [THE IDA PRO BOOK](https://mega.nz/file/omMykYgZ#i6tgJkk6TDNltbGw-mCcetH9C4xmR6znKMXvHogWNx0)
- [Advanced Malware Analysis](https://mega.nz/file/47NRgY6Q#oqBx6sBDfrLd_FDgY-NWbb5KTcwd_ja0WZxClPxpMIA)
- [Detection of Intrusions and Malware, and Vulnerability Assessment](https://mega.nz/file/MiMXDCwS#n4dY2pM77egOgdMPlrYM782rwg4kWGDRYlG6XSOkKyI)
- [Learning Malware Analysis](https://mega.nz/file/9y1VELzA#Funa-9hdX-mQ4GfJXzE7fkzg2OjE1aZymn47EBmxCuA)
- [Malware Analyst's Tools and Techniques](https://mega.nz/file/9qUD2Z5Q#JRbX5yS5fJjokudYRFiPSWrnz-7sg23TT1MOhLrtw84)
- [Malware Detection – Advances in Information Security](https://mega.nz/file/N6FEBBxb#-sdpvizm2p_f3i11mnz4zpusFCZl-UhWUF-vqLi3ZiQ)
- [The Rootkit ARSENAL](https://mega.nz/file/I68SGB4Z#7IWsn4GvMmRL8ZTJBMs9ySoLIrt2Pn1PJ7IrXeqNbYw)
- [Windows Malware Analysis Essentials](https://mega.nz/file/l7912D4Z#cpN3yzhyYJNyMBupvFX5S9ScC0rdZ2yYpNUvlVgRiWE)
- [PRACTICAL MALWARE ANALYSIS](https://mega.nz/file/Bi8xkKZb#7zP3Xbj-KsEn0Tnp1VM8sluT-tdPnvxIR4IZacLhHL8)
- [Writing Security Tools and Exploits](https://mega.nz/file/Ii92QKqB#VWwxBrfi84zMoZjg28ArxeX8fCF8EvTyfOFt7JazmGA)
- [Windows Virus and Malware Troubleshooting](https://mega.nz/file/oiFTwRAa#sNinIxV03YguAgcsePEX9ZnqxQ8MfQx_nz1_osw2mQ0)
- [Rootkits and Bootkits: Reversing Modern Malware and Next-Generation Threats](https://mega.nz/file/kuMl2ZwK#rHQoTkzP4aKzAx2-tAFzIhAnH02a0bQDbs0CbN275RE)
- [Malware Analysis Techniques: Tricks for the Triage of Adversarial Software](https://mega.nz/file/tu91TKLY#KpPfG5VV3qPTnBQqnfeTacR_DPwmCJSlW1g91TsRssU)
- [Malware Data Science: Attack Detection and Attribution](https://mega.nz/file/pmEB2LTZ#p-PuEhR6TCtcpT5V2UevJAzy0wrjxjBvwjByGVn886A)
# 中级 INTERMEDIATE
## 🧠 数字取证与事件响应
### 数字取证分析电子书
- [The Art of Memory Forensics](https://mega.nz/file/hr0z2TqQ#8WI3aZG37uDroAW4mzouyxbR9aMeej0TdktNlIFa9S0)
- [Practical Forensic Imaging](https://mega.nz/file/VvliCSID#4VG28zt7zII8dYd3I0K5gPOkBYA2G_spCRMgb2T6C94)
- [Malware Forensics Field Guide for Windows Systems](https://mega.nz/file/U2E3hDBI#kKAeC5d0_0I0tjtcVD0-lxF3mWOm_YRy0_wtAqTllN4)
- [Cyber Forensics: A Field Manual for Collecting](https://mega.nz/file/Ij0ljJYK#TeOboJs3E2YlqCAorbGMjN2zLgo_IiFasI9rnpVo0bE)
- [Attacking Network Protocols](https://mega.nz/file/Zv11kRKZ#XjNVv6LSkeqvmrJXc7m0nJLl_z4GbRRJiR-IUCNIwsA)
- [Digital Forensics With Open Source Tools](https://mega.nz/file/Yv11HLgT#Eiq1E2v9QMccojtdubLKcUnj2hDIH1R-22FA_5h58Oc)
- [Cyber Forensics](https://mega.nz/file/J6U0AYbR#Wayy_YHd4d5zIiUNhokwWb2XcwtTBde_EosZXRoBOa4)
- [Hacking Exposed Malware And Rootkit](https://mega.nz/file/kidBUSwB#JSGadYAZ7Lf5SB7fsaaBH9tW2x4DsU0MomafBX1qS1U)
- [Digital Forensics](https://mega.nz/file/c7ER2QDa#S6yGqVQtb9Uo8-jdhMxpaonyU6PjwuH6KtrynEDtTlc)
- [Windows Forensic](https://mega.nz/file/V2MEza5Y#1BXvdWTPZqhkxBxjeMoA926aQLfthBPFv45tlY7Z6GM)
- [Windows Malware Analysis Accelerated with Memory Dumps](https://mega.nz/file/x200zRJT#6t_W3yzAmXTP-dNLcygH00Sr-L6dwLRah16YtM6Mkyw)
- [Computer Viruses and Malware](https://mega.nz/file/k6cREYKC#BHYswqQpBT_zmXAZ3pOcUAOsAgyU6UXHjUM3QjktIfM)
- [Wireshark for Security Professionals](https://mega.nz/file/NzFnDJpI#2rPNrehkvzSVwy_5i-ktbgZPLao-o31opDH2pIdsS3U)
- [Reverse Engineering for Beginners](https://mega.nz/file/R3lFlbRK#uzDu-PFA1Qwz3Tt2jKSML2Hib3TJA3eO3rutrFlbv2Q)
- [Computer and Information Security Handbook](https://mega.nz/file/U711ECoa#-oNBfIpZMin9aHkSqp9c53ROujnOG_HBtBzYHnXorpc)
- [Windows Forensic Analysis](https://mega.nz/file/UqsmWRTS#7U8K11sWb2BHsygebX51mT6WweWeNpa2EJnOXG_HncQ)
- [Computer Viruses for Dummies](https://mega.nz/file/MnsH1R4T#oMEWe0WyZV_HGl3zLIwY_TeuwTiv9jew8doLMBUcTqw)
- [Binary Instrumentation for Security Professionals](https://mega.nz/file/o2VGCABa#eRXjukBE-IqbZQKW9YGRIsvonIxCthU0aiXS-7ws3IY)
- [Hacking Exposed Computer Forensics](https://mega.nz/file/4y8wyQaC#fmhtss1-psHBcW687dAEWY0awXHN21GaumGtftAEOcY)
- [Learn Computer Forensics](https://mega.nz/file/lz1TEKgB#tuxEfI_SUMi7Psas_AFNS64Etzscv331eNuUGATxXVE)
- [Linux Malware Incident Response](https://mega.nz/file/tyc3HARB#hjThv-RgjOuNSdoNZ3-NadhN9bty58GAoFje_59Y4_w)
- [The Basics of Digital Forensics](https://mega.nz/file/Bi8FTYwa#D_vvp3RXTzRYheq50n2Eryc6JSIVgsaO84LkQxSt4Xw)
- [Digital Forensics Basics: A Practical Guide Using Windows OS](https://mega.nz/file/4ismHSrb#l6Ew0KtqM12bz3luNiO6vQOb9_OwWycMWurNTLN_fC4)
- [PowerShell and Python Together](https://mega.nz/file/BrESBCCD#HJZx8SyTAgrbeBeK8n5jw7zg-0lQ5Yv0ah_98XQ7m1Y)
- [Incident Response & Computer Forensics, Third Edition](https://mega.nz/file/An9GSTbR#CDNGd7HsS-1JsA61Zk3G0Y9v6SMbvczDttPG5VBlryE)
- [Computer Forensics: Cybercriminals, Laws, and Evidence](https://mega.nz/file/sz8hxRIQ#wuDQusUYkuRu6hZMRDazgcR2GqhoBGJHcrYNJw03Riw)
- [Guide to Computer Forensics and Investigations](https://mega.nz/file/5u8UBBIT#TsKEgmARIQXrtTJRrOGRFX-Mr1nJofCW5lFtcKx712c)
- [Hacks, Leaks, and Revelations](https://mega.nz/file/VyUWGaZZ#OsY7iomYuRGWzOym8YW-xRTfZjYYJ7tJ9p7-Mbcy4Jk)
## 🔴 攻击方向 — 渗透测试与红队
### 黑客/渗透测试电子书
- [Gray Hat Hacking The Ethical Hacker's Handbook](https://mega.nz/file/hyNkjYzI#2r_6HvaezNHX6-mUjdsVEnSHTFBk4OYQ6pK8QCtzDIw)
- [Gray Hat Hacking: The Ethical Hacker's Handbook, Fifth Edition](https://mega.nz/file/w6MxHaQJ#2OCTuDz-kH2XdlaBVbieBOchECCPVa4KQsKQWlhlNIQ)
- [Gray Hat Hacking: The Ethical Hacker's Handbook, Fourth Edition](https://mega.nz/file/tiETAAgK#Oe6V2B2rvfX1fVw9zIoZrJ5UokqTsEzvmU6BcIv7KnM)
- [Gray Hat Hacking: The Ethical Hacker's Handbook, Second Edition](https://mega.nz/file/xqNTkDSZ#damPBWDgfZSDorPNK1PcFQEy7kkcD7OzjMgecy-_RlY)
- [Penetration Testing: A Survival Guide](https://mega.nz/file/R6lg1ZpA#XiOurtVzYTYQhhcey363DndjpCr6Vik6ZGThPfsrEd4)
- [Mastering Modern Web Penetration Testing](https://mega.nz/file/56kFwRYI#EuxppH8ffTGex-nE4OadcPZKbFmsmi7B9ckjxOsxs6k)
- [The Hacker Playbook 2: Practical Guide to Penetration Testing](https://mega.nz/file/xvFAXbbY#46O9rVl5M1XD_rX9C6kxtCtyugbcCBRaVQpQCWJLHzU)
- [The Basics of Hacking and Penetration Testing](https://mega.nz/file/8zE3DYaQ#32J57fId1svnszA22E8EQ6oHRpOfynWqIENZ1aTCcSs)
- [Quick Start Guide to Penetration Testing](https://mega.nz/file/ljsTEYgL#R83W1gxgSHZxPMMdJ-jbV80GnQbn5q5x7y2W0cWbctU)
- [Ethical Hacking and Penetration Testing Guide](https://mega.nz/file/Fq8RkDBT#D01uZMeHOW_lH-btEYu1lW2qCJK0MNMzW_TyX8wAHiI)
- [Ethical Hacking 101: How to Conduct Professional Pentestings in 21 Days or Less!](https://mega.nz/file/53FmySJD#w-NFfIYil_UV_KduI7PSPYg_EGMtEdNlHWelmYVHI7U)
- [HackLOG Security & Ethical Hacking Handbook Volume 1: Anonymity](https://mega.nz/file/8jUi2QRa#3QayQ3fmTSE5bne-7BnfWiPyV6fnNoxAzhKbyZMiAhY)
- [The Hacker Playbook 3: Practical Guide to Penetration Testing](https://mega.nz/file/F6dGHYZL#WnL2FGRQf5aKm1YBRGTUAMvIbTXFLnB49XZWi4-cp0g)
- [Hacking: The Ultimate Hacking for Beginners](https://mega.nz/file/RzFkQaqL#5Nsce2J0a3JQD73DrG7HOTpU_mUZ41rWf_DtOQiGbRQ)
- [Prophet Hacker: Android Hacking Book](https://mega.nz/file/Un9kGKYK#7-5VZohI9LOai6zMe79h_8GDLWAzqlqxqK7o8QAv1-c)
- [Hacking Bible](https://mega.nz/file/Y7F2FBbS#EbZXkvsx5W5i6wDjWGWzRrUTSbm735qHJL3Zey4p1qU)
- [Web App Hacking (Hackers Handbook)](https://mega.nz/file/8uFDQCaK#7a0gMH7SLAUZ3fkjEgZ_Tgyq79FxWgCVFD9TgLOZbyE)
- [Pentesting Azure Applications](https://mega.nz/file/83UxGLDY#-mz_Yfuh3aTNSIDWWB4YjKm8bDZVko6fHxGjOjp8Om4)
- [Gray Hat C#: A Hacker's Guide to Creating and Automating Security Tools](https://mega.nz/file/561VBTYL#lhOPeO9DWei3ZLFCbNRpTuSKbLQk1PjSWpPDuvVhT0w)
- [Antivirus Hackers Handbook](https://mega.nz/file/ArUjmSyZ#zVtTgrPpxUhpm4FvS81x1zV9QxByHQ2Jdu62gfM-Ymg)
- [Hacking Exposed™ 6: Network Security Secrets & Solutions](https://mega.nz/file/grlikLyJ#fd4RF5d3Osharerzu68dKbJZAhydAvTsn9ooYc6dMF4)
- [Hacking Secrets Exposed - A Beginner's Guide](https://mega.nz/file/l70g0byK#OnlDJs4uaTVATnieZdkbxfCJzWD9ozwN8omFin-2-FY)
- [Hacking Exposed™ Web Applications 3](https://mega.nz/file/xmkAhYYB#izv3v9qLfoZpoml6AjkjFQFbTnt1C_rbPMmv3Rw4j4k)
- [Hacking Exposed: Network Security Secrets & Solutions 2nd Edition](https://mega.nz/file/JvUWFIST#8Ptt4_bT6nurez4C7iBxOuxYEqVyketPHzKZF7deQhE)
- [Hacking Exposed™ Windows](https://mega.nz/file/MiUHiSZa#gccpQGFJ-U2E17im4yAHHNODIv6n_C7AXE82fkil5rY)
- [Hacking Exposed - Linux: Linux Security Secrets](https://mega.nz/file/wnkTUZha#h3B2LOczQ0NQlEB18UVCPl_E-e5G5bbR5ZtntZaLdFE)
- [Black Hat Bash Scripting for Hackers and Pentesters](https://mega.nz/file/1r9ViKjJ#rCjNeEx4eQgt4TnrC73DB-nv2IMDQ8LZOiqX5AvLHFg)
- [Black Hat Go: Programming for Hackers and Pentesters](https://mega.nz/file/1r9ViKjJ#rCjNeEx4eQgt4TnrC73DB-nv2IMDQ8LZOiqX5AvLHFg)
# 高级 ADVANCED
## 🔵 专业化方向 — 平台与领域
### Kali Linux 电子书
- [Basic Security Testing with Kali Linux](https://mega.nz/file/k7lGhLwb#ge8EiyjxBhz3UK2B9PyatlDeDa73C_s_aEOFQhlkUvE)
- [Kali Linux Network Scanning Cookbook](https://mega.nz/file/gi9zlZRA#txHoGtSR6LkqCZRSaezXZAKugmcczLL8tQ8hGipGBFQ)
- [Kali Linux - Assuring Security by Penetration Testing](https://mega.nz/file/1vsjARwb#GOZqRaCMBdl9K7ARlzi-we8ZbWudqdOi1W1Ogux0abg)
- [Kali Linux 2 Windows Penetration Testing](https://mega.nz/file/IjlgABCI#kGwicfEkg-DXKEemI1XEcsG6LJ-gU0LZW5VojiXSDE8)
- [Kali Linux Cookbook](https://mega.nz/file/BnlmCK5L#MnP9bVCWmupj1s116lwYFUiCpSgt0RecAAmllklzZd0)
- [Web Penetration Testing with Kali Linux](https://mega.nz/file/03kQGCIb#isjHmE1tDHlN87F5NeYgBLhmkicLkW5cqb85dq43Ua4)
- [The Ultimate Kali Linux Book - Perform Advanced Penetration Testing](https://drive.google.com/file/d/16tl5Fw6E21bN5Sl2osHW5lv923nl0Cgq/view)
- [Web Penetration Testing with Kali Linux (Build your defense against web attacks)](https://mega.nz/file/1mFlwKzC#brozDpcIwJB3hJ9cPi1Dx8jZthb8rIHvp_NbEq7Hj_8)
- [Hands-On Penetration Testing on Windows](https://mega.nz/file/xnlj3YYA#wXuHHZ4Lj8na6IZ-avxvrdF4I2ceOt_r1TB6fT8Pd6s)
- [Kali Linux Tools (Digital Forensics Penetration Testing)](https://mega.nz/file/9mcByDzA#Vmdj_zjB-6sYRPw94pwuhoo6_V-RLkYQZLFesAqFZHQ)
- [Kali Linux Wireless Pentesting and Security for Beginners](https://mega.nz/file/prshWa4Y#bfTx1vFAAUN0FvIUIFYgEPjPqrv81l2Rj76rf4r7Kq0)
- [Linux Basics for Hackers](https://mega.nz/file/8zFxxYxY#fEFPbl7BSNg8WbFNPSCH-BXhNX4EFbduLmO_Sv-zgBs)
- [Kali Linux Revealed - Mastering the Penetration Testing Distribution](https://mega.nz/file/8zEGlJ7b#q4b3CqhClGIWdcDuBmOjQl_AUdwoWpYJi9m2bYPScCs)
### 移动安全黑客
- [Android Hacker's Handbook](https://mega.nz/file/pyczWCLI#mv8ZE0K7e2IfHnqj4rX1gq-BoKKJEWm5NHnL2yMpHpg)
- [iOS Application Security](https://mega.nz/file/gnk3mYSB#lIeHw3ySAKIwtDp2ERmAKBoiDMbVOMh-6A7Q0rdv55E)
- [Mobile Pentesting with FRIDA](https://mega.nz/file/UrNkjI5D#X_d1sYnieUrq77Bo5CYn24ngwYuGNHjxqNNKgJKl7sw)
- [Mobile Security For Dummies](https://mega.nz/file/ZrUyUCjJ#epVsuCmoK2RZ5mka69lhfAyAa3admVldvI51jb_5zEo)
- [Android Application Security](https://mega.nz/file/8mU3yRTZ#r-a15ykdqYapnkidh8W5xTZ44DZ5jOkcej1Wk2WPCYk)
- [Mobile Device Exploitation Cookbook](https://mega.nz/file/EusVDQgD#fQ57ItOigNa8PwGEGMYWD1yUBGKeAsAhMxR5f7_y-Pw)
- [Hacking Android](https://mega.nz/file/FiMyFAhQ#wrmfTZB6VwNn3GTXH5WrsUgBxUXaaEnkPr_VHdwVtj0)
- [Mobile Exploitation - The Past, Present, and the Future](https://mega.nz/file/FrER3SLY#zVEsbehZCea4f4OS0uM7fRBxA8B1VkBZtXS7QQlF8eY)
- [Android Security Internals - An In-Depth Guide to Android's Security Architecture](https://mega.nz/file/0vcDASoC#3y9VyNUvXR_8-eRkhfRneWwafPGQW87rbyU2DZ_STUE)
### IOT 黑客
- [IOT Security Guide 2022](https://mega.nz/file/8jkBRRSI#k8NCiCLFW5l9xiPkCcyTfNs3kpr89dYQtQ60jFSTTDM)
- [Handbook of Big Data and IoT Security](https://mega.nz/file/Jz0C3YQT#Vyn175zwT3B_qCarZXXha4Vmh2eBELaXAgNNdHT1b14)
- [Hacking IoT for Bug Bounties](https://mega.nz/file/V3VliDhJ#Y2i3KnZYJW1tfLrznZWYOBmezukmbDzdANoNGw1vOTI)
- [The IoT Hacker's Handbook](https://mega.nz/file/8jV0AZiD#EWm8ZQhWcJO4FnYpM_CLfwMaRjg0PrNFip1cX0W9PDY)
- [PRACTICAL IOT HACKING: The Definitive Guide to Attacking the Internet of Things](https://mega.nz/file/d2E0DA7L#V198m-Q_fPYSpuH0ZFRbooC526GQbMdIkFOAVHruz-c)
### API 安全
- [Extreme Networks Security API Reference Guide](https://mega.nz/file/4ykznCDK#owaKNuTUJTC4ElZD8G6ylhvqxig3ssEO4b8ZTM5w0rY)
- [Advanced API Security](https://mega.nz/file/13sgFQKS#QbWazP_Rho4ABzfvRXGVh0iVDUM8HkgGVcRMJhJ2wD4)
- [Pro ASP-NET Web API Security](https://mega.nz/file/ZyMjWRiJ#Ehhh5CU8JC5tB4dMzUrwG2uV9iBy29nXVLqOw3byltI)
### 密码学
- [Serious Cryptography](https://mega.nz/file/Z2U3CCab#WYCVOgxexq2nh2L62Dpr4_H5EvbMPWWIHmym6qm92cQ)
- [Introduction to Cryptography](https://mega.nz/file/Nn8yGQwB#ADGkRTRD_hHMuZUByRHmzsui1q1sbRXb6f5y1YFGk-8)
- [Cryptography and Network Security](https://mega.nz/file/AzdHGQwb#FD9UriZIOdFm7AxWqKlpUhVaMMwfTSWwm7O4Fp7JAD8)
- [Applied Cryptography in .NET and Azure Key Vault](https://mega.nz/file/47E3UYDJ#BGt8WpTKUTRXnfQ1wjkQslv5vglUkfO1UtHLeRqq1zs)
- [Hands-On Cryptography with Python](https://mega.nz/file/ImVnBQaR#ecVuKeVLL9N_139KX9YHXbScK8UTVdxl1Asw-vymMxs)
- [Cracking Codes with Python](https://mega.nz/file/x3MwwLbI#o6VSk3Fiowt_EO4ldD1uNezWCXuDCbE_yUUvh_QXL3Q)
### 其他资源
- [Cyber Security on Azure: An IT Professional's Guide to Microsoft Azure Security Center](https://mega.nz/file/Vr80RQJb#uNZoG733rEGmqVgf2NkHuBu9KOVvXt0afP1JE6kDlKg)
- [Practical Cloud Security: A Guide for Secure Design and Deployment](https://mega.nz/file/Z6cUnAAR#986xZSb6MhdMbK-kN1ov4lCnro9lDdLdy5juL-Kgp3A)
- [The Tangled Web: A Guide to Securing Modern Web Applications](https://mega.nz/file/9msyETrZ#hNtuGngzjjlJ6UFOkXlc7QhNY5XN_mv3QIae2iqS3S4)
- [Linux Command Line and Shell Scripting Bible (1052 pages)](https://mega.nz/file/h6NVVLoB#-C4siioCXHXS4iTOg3UHI5t0twmxOUeG4W8Nj_2rALY)
- [Nmap Official Guide + Scripts](https://mega.nz/file/A21nTB5S#9rfwjADO1qrXhP2Nbd1U8EKaV3LFf8Lg3xsT-5NNkUc)
- [Network Security Bible](https://mega.nz/file/AuVFSRzJ#W3Xg4TkWvRYPCOzPbdTK3wCfh_ThEXPcybGeClxdAGI)
- [Anti-Hacker Tool Kit](https://mega.nz/file/Rm1RlZBI#ej1Xr-0Fa1xARsOh9wpFzkCy9DomxenKuGHf4RSy8yU)
- [TOR DARKNET BUNDLE (5-in-1): Master the Art of Invisibility](https://mega.nz/file/kudhSLYR#zX9PBwSRMLlIy4X-uYkhqu-tb3Ia2ALzSeJYKvsLiyY)
- [Evading EDR: A Comprehensive Guide to Defeating Endpoint Detection Systems](https://mega.nz/file/Eu8VSABD#kSLyZzsjA2lQx9hYx3axSENdEtd7AmkTIxhXFT6WKdo)
- [Evading EDR: The Definitive Guide to Defeating Endpoint Detection Systems](https://mega.nz/file/JmE0XbpI#LRG5b4zrZHWgXDZuFcrdWV1GlObkDVZt25H23gt2lOI)
- [Windows Security Internals with PowerShell](https://mega.nz/file/83d1BBja#INXRQ_tj5frJtUiQt-XzXBAxTzETVzU0ZSPJCqPocHc)
- [Infrastructure as Code: Evolving Systems in the Cloud](https://mega.nz/file/hz1lVCSZ#RzOhoiYFfaRs-FBHrDDXIjoMfhl6au4cl1U9gIHkTtc)
## 🧪 实战平台
通过实验室、挑战和模拟环境练习网络安全技能的动手平台。
### 通用网络安全实验室
- [TryHackMe](https://tryhackme.com/) – 适合初学者的引导式网络安全实验室和学习路径。
- [Hack The Box](https://www.hackthebox.com/) – 高级渗透测试实验室,包含逼真的易受攻击机器。
- [OverTheWire](https://overthewire.org/wargames/) – 专注于 Linux、网络和安全基础知识的战争游戏。
- [PicoCTF](https://picoctf.org/) – 面向初学者的 CTF 平台,挑战来自卡内基梅隆大学。
- [VulnHub](https://www.vulnhub.com/) – 可下载的易受攻击虚拟机,用于离线练习。
- [RangeForce Community Edition](https://rangeforce.com/) – 蓝队和防御性安全培训实验室。
### Web 安全练习
- [PortSwigger Web Security Academy](https://portswigger.net/web-security) – 涵盖 Web 漏洞的互动实验室。
- [PentesterLab](https://pentesterlab.com/) – 动手实践 Web 利用练习。
- [Root Me](https://www.root-me.org/) – Web 黑客攻击、密码学、逆向工程等内容。
- [OWASP Juice Shop](https://owasp.org/www-project-juice-shop/) – 具有故意漏洞的 Web 应用程序。
- [Google Gruyere](https://google-gruyere.appspot.com/) – Google 提供的 Web 漏洞培训应用。
### 夺旗 (CTF) 平台
- [CTFtime](https://ctftime.org/) – CTF 竞赛的全球日历和排名。
- [pwnable.kr](https://pwnable.kr/) – 二进制利用和 pwn 挑战。
- [pwnable.tw](https://pwnable.tw/) – 高级利用挑战。
- [RingZer0 CTF](https://ringzer0ctf.com/) – 包括密码学、Web 和逆向工程等多个类别。
### 云安全练习
- [CloudGoat](https://github.com/RhinoSecurityLabs/cloudgoat) – 用于动手学习的 AWS 安全场景。
- [flAWS Cloud](http://flaws.cloud/) – AWS 安全挑战环境。
- [flAWS2](http://flaws2.cloud/) – 高级 AWS 安全挑战。
- [Cloud Security Labs](https://cloudsecuritylabs.com/) – 交互式云安全练习。
### 恶意软件分析练习
- [Malware Traffic Analysis](https://www.malware-traffic-analysis.net/) – 真实的恶意软件网络流量样本。
- [Malware Unicorn Workshops](https://malwareunicorn.org/workshops/) – 恶意软件分析培训资料。
### 蓝队 / 防御性安全
- [Blue Team Labs Online](https://blueteamlabs.online/) – SOC 和事件响应培训实验室。
- [CyberDefenders](https://cyberdefenders.org/) – DFIR 和蓝队挑战。
- [LetsDefend](https://letsdefend.io/) – SOC 分析师模拟平台。
### 逆向工程练习
- [Crackmes.one](https://crackmes.one/) – 逆向工程挑战。
- [Microcorruption](https://microcorruption.com/) – 嵌入式系统利用战争游戏。
## Star 历史
[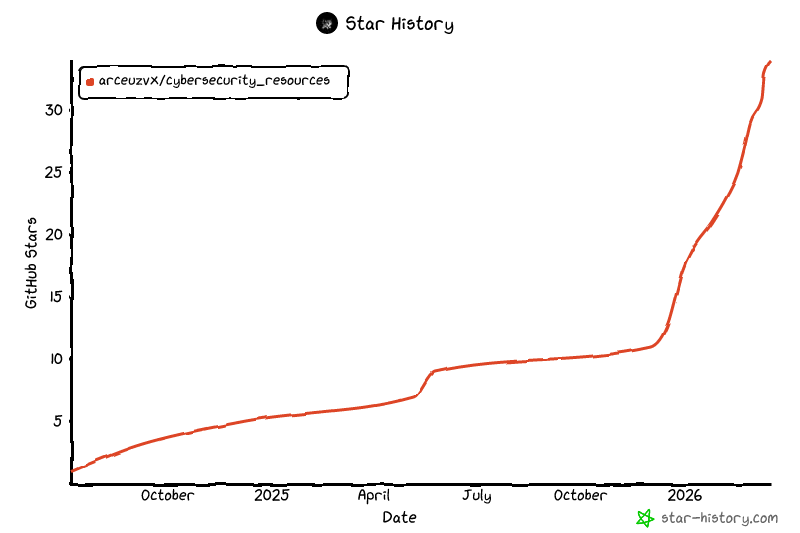](https://www.star-history.com/?repos=arceuzvx%2FCybersecurity_resources&type=date&legend=top-left)
### 觉得这个项目有帮助?
点个 🌟 并与你的网络安全爱好者伙伴分享 📎,一起开始学习吧! 🤩
在 [X/twitter](https://x.com/arceuzvx) 上关注我,建立联系 🩷
标签:AI合规, CTI, DAST, IT安全, meg, Python安全编程, SOC分析师, Windows内核, 事件响应, 信息安全, 免费资源, 域环境安全, 学习路线图, 安全认证, 应用安全, 恶意软件分析, 数字取证, 数据展示, 漏洞利用检测, 电子书合集, 白帽子, 红队, 编程书籍, 网络安全, 网络安全基础, 网络安全工程师, 自动化脚本, 自学资料, 逆向工具, 隐私保护, 黑客技术