corelight/terraform-aws-sensor
GitHub: corelight/terraform-aws-sensor
用于在 AWS 云环境中自动化部署 Corelight 网络流量传感器的 Terraform 模块,支持多可用区和多区域架构。
Stars: 3 | Forks: 5
# terraform-aws-sensor
用于 Corelight AWS Cloud Sensor 部署的 Terraform 模块。
 ## 概述
此模块在 AWS Auto Scaling Group 中部署 Corelight sensor,并使用 Lambda 管理网络接口附加。
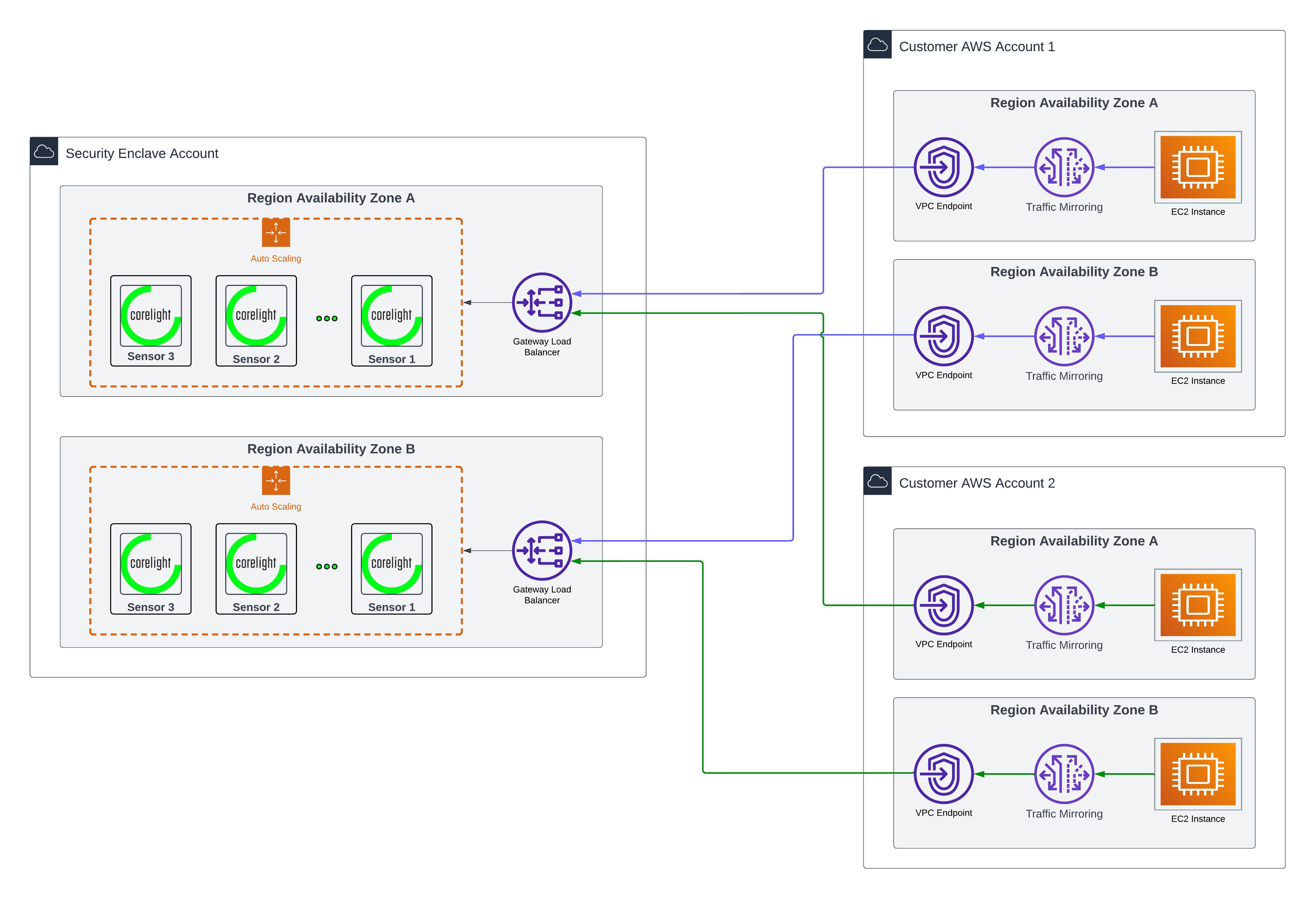
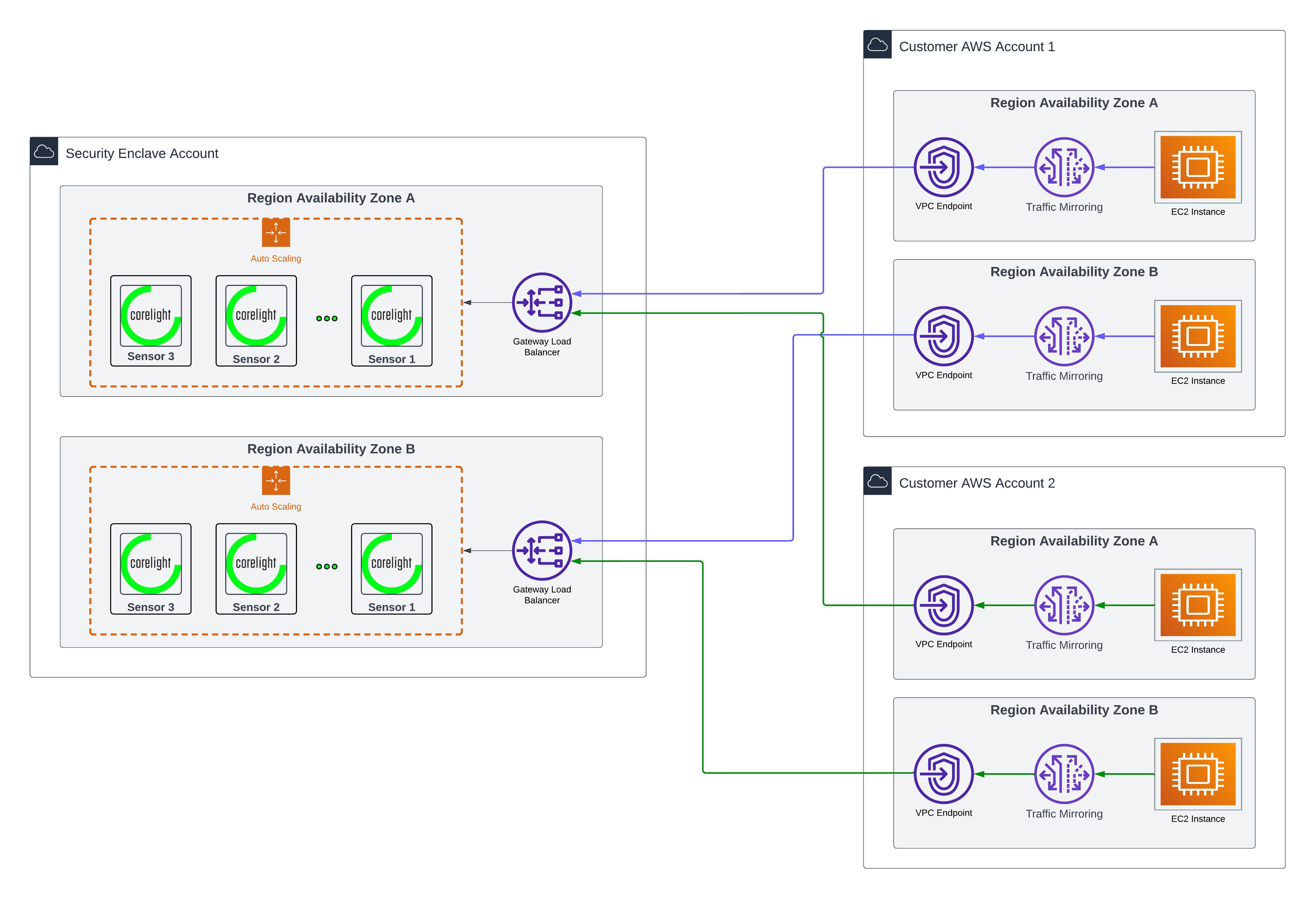
### 架构
该部署需要 **两个独立的模块** 协同工作:
1. **IAM Lambda 模块** (`modules/iam/lambda`) - 创建 IAM 角色和策略
2. **Sensor 模块** (根模块) - 创建 Lambda 函数、ASG 和所有 sensor 基础设施
### 必需资源
这些资源对于正常运行 sensor 部署至关重要:
- **IAM Lambda 角色** (`module.asg_lambda_role`) - 用于 ENI 管理 Lambda 函数的 IAM 角色(由 `modules/iam/lambda` 创建)
- **Sensor Auto Scaling Group** (`module.sensor`) - 核心 sensor 基础设施,包括 Lambda 函数(由根模块创建)
- **管理子网** - 每个可用区至少需要一个子网用于 sensor 管理
- **监控子网** - 每个可用区至少需要一个子网用于流量监控
### 可选资源
这些资源可增强 sensor 功能,但并非必需:
- **Enrichment IAM 角色** (`module.enrichment_sensor_role`) - 启用对 S3 bucket 的访问以进行数据丰富
- **堡垒主机** - 用于安全 SSH 访问 sensor(基础示例中未展示)
- **自定义 KMS 密钥** - 用于超越 AWS 托管密钥的 EBS 卷加密
## 使用方法
### 单区域部署
```
data "aws_subnet" "management" {
for_each = toset(["
## 概述
此模块在 AWS Auto Scaling Group 中部署 Corelight sensor,并使用 Lambda 管理网络接口附加。
### 架构
该部署需要 **两个独立的模块** 协同工作:
1. **IAM Lambda 模块** (`modules/iam/lambda`) - 创建 IAM 角色和策略
2. **Sensor 模块** (根模块) - 创建 Lambda 函数、ASG 和所有 sensor 基础设施
### 必需资源
这些资源对于正常运行 sensor 部署至关重要:
- **IAM Lambda 角色** (`module.asg_lambda_role`) - 用于 ENI 管理 Lambda 函数的 IAM 角色(由 `modules/iam/lambda` 创建)
- **Sensor Auto Scaling Group** (`module.sensor`) - 核心 sensor 基础设施,包括 Lambda 函数(由根模块创建)
- **管理子网** - 每个可用区至少需要一个子网用于 sensor 管理
- **监控子网** - 每个可用区至少需要一个子网用于流量监控
### 可选资源
这些资源可增强 sensor 功能,但并非必需:
- **Enrichment IAM 角色** (`module.enrichment_sensor_role`) - 启用对 S3 bucket 的访问以进行数据丰富
- **堡垒主机** - 用于安全 SSH 访问 sensor(基础示例中未展示)
- **自定义 KMS 密钥** - 用于超越 AWS 托管密钥的 EBS 卷加密
## 使用方法
### 单区域部署
```
data "aws_subnet" "management" {
for_each = toset(["", ""])
id = each.value
}
# 必需:Lambda function 的 IAM role
# 这将创建 Lambda function 将承担的 IAM role/policy
module "asg_lambda_role" {
source = "github.com/corelight/terraform-aws-sensor//modules/iam/lambda"
lambda_cloudwatch_log_group_arn = module.sensor.cloudwatch_log_group_arn
sensor_autoscaling_group_arn = module.sensor.autoscaling_group_arn
security_group_arn = module.sensor.management_security_group_arn
subnet_arns = [for subnet in data.aws_subnet.management : subnet.arn]
}
# 必需:主 sensor 部署
# 这将创建 Lambda function、ASG 和所有基础设施
# 它需要上面创建的 IAM role ARN
module "sensor" {
source = "github.com/corelight/terraform-aws-sensor"
# Multi-AZ support: provide one subnet per availability zone
# The ASG will automatically distribute instances across AZs
availability_zones = ["us-east-1a", "us-east-1b"]
aws_key_pair_name = ""
# Request access to Corelight sensor AMI from your Account Executive
corelight_sensor_ami_id = ""
license_key = ""
# Provide one management subnet per AZ (must match availability_zones order)
management_subnet_ids = ["", ""]
# Provide one monitoring subnet per AZ (must match availability_zones order)
monitoring_subnet_ids = ["", ""]
community_string = ""
vpc_id = ""
asg_lambda_iam_role_arn = module.asg_lambda_role.role_arn
fleet_token = ""
fleet_url = ""
fleet_server_sslname = ""
# OPTIONAL: KMS key for EBS volume encryption
kms_key_id = ""
}
# 可选:S3 enrichment 资源
module "enrichment_sensor_role" {
source = "github.com/corelight/terraform-aws-enrichment//modules/iam/sensor"
enrichment_bucket_arn = data.aws_s3_bucket.enrichment_bucket.arn
}
resource "aws_iam_instance_profile" "corelight_sensor" {
name = ""
role = module.enrichment_sensor_role.sensor_role_name
}
```
### 多区域部署
跨多个区域部署 sensor 时,您需要了解哪些资源具有区域特定性:
**区域特定资源**(每个区域部署一次):
- Sensor Auto Scaling Group 及其所有组件
- Lambda 函数和 CloudWatch Log Groups
- IAM Lambda 角色(引用日志组和子网等区域性资源)
- VPC、子网和安全组
**全局资源**(部署一次,跨区域共享):
- 不引用区域性 ARN 的 IAM 角色(在此设置中很少见)
- Fleet 配置(同一个 fleet 实例可以管理多个区域的 sensor)
#### 多区域示例
```
# ============================================================================
# 区域 1:US-EAST-1
# ============================================================================
provider "aws" {
alias = "us_east_1"
region = "us-east-1"
}
data "aws_subnet" "management_east" {
provider = aws.us_east_1
for_each = toset(var.management_subnet_ids_east)
id = each.value
}
# Lambda 的 IAM role(由于 log group 和 subnet ARNs 而特定于区域)
module "asg_lambda_role_east" {
source = "github.com/corelight/terraform-aws-sensor//modules/iam/lambda"
providers = {
aws = aws.us_east_1
}
lambda_cloudwatch_log_group_arn = module.sensor_east.cloudwatch_log_group_arn
sensor_autoscaling_group_arn = module.sensor_east.autoscaling_group_arn
security_group_arn = module.sensor_east.management_security_group_arn
subnet_arns = [for subnet in data.aws_subnet.management_east : subnet.arn]
# Use unique names per region to avoid conflicts
lambda_role_name = "corelight-asg-sensor-nic-manager-lambda-role-us-east-1"
lambda_policy_name = "corelight-asg-sensor-nic-manager-lambda-policy-us-east-1"
tags = var.tags
}
# US-EAST-1 的 Sensor 部署
module "sensor_east" {
source = "github.com/corelight/terraform-aws-sensor"
providers = {
aws = aws.us_east_1
}
availability_zones = ["us-east-1a", "us-east-1b"]
aws_key_pair_name = var.aws_key_pair_name_east
corelight_sensor_ami_id = var.corelight_sensor_ami_id_east
management_subnet_ids = var.management_subnet_ids_east
monitoring_subnet_ids = var.monitoring_subnet_ids_east
vpc_id = var.vpc_id_east
# Same Fleet instance can manage sensors in multiple regions
fleet_token = var.fleet_token
fleet_url = var.fleet_url
fleet_server_sslname = var.fleet_server_sslname
community_string = var.community_string
asg_lambda_iam_role_arn = module.asg_lambda_role_east.role_arn
# Use unique names per region
sensor_asg_name = "corelight-sensor-us-east-1"
tags = var.tags
}
# ============================================================================
# 区域 2:US-WEST-2
# ============================================================================
provider "aws" {
alias = "us_west_2"
region = "us-west-2"
}
data "aws_subnet" "management_west" {
provider = aws.us_west_2
for_each = toset(var.management_subnet_ids_west)
id = each.value
}
# Lambda 的 IAM role(由于 log group 和 subnet ARNs 而特定于区域)
module "asg_lambda_role_west" {
source = "github.com/corelight/terraform-aws-sensor//modules/iam/lambda"
providers = {
aws = aws.us_west_2
}
lambda_cloudwatch_log_group_arn = module.sensor_west.cloudwatch_log_group_arn
sensor_autoscaling_group_arn = module.sensor_west.autoscaling_group_arn
security_group_arn = module.sensor_west.management_security_group_arn
subnet_arns = [for subnet in data.aws_subnet.management_west : subnet.arn]
# Use unique names per region to avoid conflicts
lambda_role_name = "corelight-asg-sensor-nic-manager-lambda-role-us-west-2"
lambda_policy_name = "corelight-asg-sensor-nic-manager-lambda-policy-us-west-2"
tags = var.tags
}
# US-WEST-2 的 Sensor 部署
module "sensor_west" {
source = "github.com/corelight/terraform-aws-sensor"
providers = {
aws = aws.us_west_2
}
availability_zones = ["us-west-2a", "us-west-2b"]
aws_key_pair_name = var.aws_key_pair_name_west
corelight_sensor_ami_id = var.corelight_sensor_ami_id_west
management_subnet_ids = var.management_subnet_ids_west
monitoring_subnet_ids = var.monitoring_subnet_ids_west
vpc_id = var.vpc_id_west
# Same Fleet instance can manage sensors in multiple regions
fleet_token = var.fleet_token
fleet_url = var.fleet_url
fleet_server_sslname = var.fleet_server_sslname
community_string = var.community_string
asg_lambda_iam_role_arn = module.asg_lambda_role_west.role_arn
# Use unique names per region
sensor_asg_name = "corelight-sensor-us-west-2"
tags = var.tags
}
```
### 部署
此模块的所有变量均设有默认值,可将其覆盖
以满足您的命名和合规标准。
部署示例可在 [此处][] 找到。
## 许可证
本项目采用 [MIT][] 许可证授权。
 ## 概述
此模块在 AWS Auto Scaling Group 中部署 Corelight sensor,并使用 Lambda 管理网络接口附加。
### 架构
该部署需要 **两个独立的模块** 协同工作:
1. **IAM Lambda 模块** (`modules/iam/lambda`) - 创建 IAM 角色和策略
2. **Sensor 模块** (根模块) - 创建 Lambda 函数、ASG 和所有 sensor 基础设施
### 必需资源
这些资源对于正常运行 sensor 部署至关重要:
- **IAM Lambda 角色** (`module.asg_lambda_role`) - 用于 ENI 管理 Lambda 函数的 IAM 角色(由 `modules/iam/lambda` 创建)
- **Sensor Auto Scaling Group** (`module.sensor`) - 核心 sensor 基础设施,包括 Lambda 函数(由根模块创建)
- **管理子网** - 每个可用区至少需要一个子网用于 sensor 管理
- **监控子网** - 每个可用区至少需要一个子网用于流量监控
### 可选资源
这些资源可增强 sensor 功能,但并非必需:
- **Enrichment IAM 角色** (`module.enrichment_sensor_role`) - 启用对 S3 bucket 的访问以进行数据丰富
- **堡垒主机** - 用于安全 SSH 访问 sensor(基础示例中未展示)
- **自定义 KMS 密钥** - 用于超越 AWS 托管密钥的 EBS 卷加密
## 使用方法
### 单区域部署
```
data "aws_subnet" "management" {
for_each = toset(["
## 概述
此模块在 AWS Auto Scaling Group 中部署 Corelight sensor,并使用 Lambda 管理网络接口附加。
### 架构
该部署需要 **两个独立的模块** 协同工作:
1. **IAM Lambda 模块** (`modules/iam/lambda`) - 创建 IAM 角色和策略
2. **Sensor 模块** (根模块) - 创建 Lambda 函数、ASG 和所有 sensor 基础设施
### 必需资源
这些资源对于正常运行 sensor 部署至关重要:
- **IAM Lambda 角色** (`module.asg_lambda_role`) - 用于 ENI 管理 Lambda 函数的 IAM 角色(由 `modules/iam/lambda` 创建)
- **Sensor Auto Scaling Group** (`module.sensor`) - 核心 sensor 基础设施,包括 Lambda 函数(由根模块创建)
- **管理子网** - 每个可用区至少需要一个子网用于 sensor 管理
- **监控子网** - 每个可用区至少需要一个子网用于流量监控
### 可选资源
这些资源可增强 sensor 功能,但并非必需:
- **Enrichment IAM 角色** (`module.enrichment_sensor_role`) - 启用对 S3 bucket 的访问以进行数据丰富
- **堡垒主机** - 用于安全 SSH 访问 sensor(基础示例中未展示)
- **自定义 KMS 密钥** - 用于超越 AWS 托管密钥的 EBS 卷加密
## 使用方法
### 单区域部署
```
data "aws_subnet" "management" {
for_each = toset(["标签:Auto Scaling Group, AWS, Corelight, DPI, ECS, ENI, Lambda, Rootkit, SaaS部署, Terraform, Zeek, 流量监控, 漏洞利用检测, 网络传感器, 网络可见性, 网络安全, 自动部署, 进程隐藏, 隐私保护