Serp07/updater_list_for_mikrotik
GitHub: Serp07/updater_list_for_mikrotik
为MikroTik路由器提供自动更新的IP黑名单,聚合多个威胁情报源帮助用户在防火墙层面拦截已知恶意连接。
Stars: 6 | Forks: 1

 [](https://mikrotik.com/download/changel
[](https://mikrotik.com/download/changel
 [](https://mikrotik.com/download/changelogs/)
[](https://mikrotik.com/download/changelogs/)
# MikroTik 自动更新地址列表
### 问题
当你提供对服务的公共访问时,要区分恶意连接和正常连接可能会相当困难。
### 解决方案
MikroTik 借助地址列表(address lists)来解决此问题……只需将恶意地址放入列表并阻止列表中的所有内容。听起来很有趣对吧……或者也许并非如此?当然,你可以(也应该)手动创建规则来检测滥用行为并动态创建列表……但是你还可以做更多,你可以订阅由其他人维护的列表,如 Spamhaus、dshield 等,
### 解析列表示例
由 Serp07 生成于 2024-02-24 01:59:30
/ip firewall address-list
add list=blacklist address=1.4.0.0/17 comment=SpamHaus
add list=blacklist address=1.10.16.0/20 comment=SpamHaus
add list=blacklist address=1.116.0.0/14 comment=SpamHaus
...
### 实现方式
实现起来非常简单……将以下代码粘贴到任何 MikroTik 的终端中,你的路由器就会获取最新版本的脚本文件并定期运行它。
### [适用于 RouterOs v6.xx ](updater_list_script_for_v6.xx.rsc)
```
/system scheduler
add comment="Apply combined List" interval=1d name=Update_combined on-event=Updater_List policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon start-date=feb/24/2024 start-time=20:08:41
/system script
add dont-require-permissions=no name=Updater_List owner=admin policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon source="/tool fetch url=\"https://raw.githubusercontent.co\
m/Serp07/updater_list_for_mikrotik/main/combined.rsc\" mode=https dst-path=combined.rsc;\
\n\r\
\n\r\
\n:log info \"Downloaded autoaddresslist from github/Serp07 \";\r\
\n\r\
\n/ip firewall address-list remove [find where comment=\"Auto_address_List\"];\r\
\n/ip firewall address-list remove [find where comment=\"Bruteforce_Blocker\"];\r\
\n\
\n\r\
\n:log info \"Removed old autoaddresslist records and imported new list\";\r\
\n\
\n\r\
\n/import file-name=combined.rsc;\r\
\n\r\
\n#/file/remove combined.rsc"
/ip firewall filter
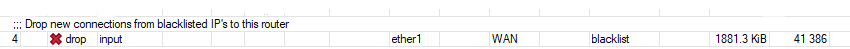
add action=drop chain=input comment="Drop new connections from blacklisted IP's to this router" connection-state=new \
in-interface=ether1 in-interface-list=WAN src-address-list=blacklist
```
### [适用于 RouterOs v7.xx ](updater_list_script_for_v7.xx.rsc)
```
/system scheduler
add comment="Apply combined List" interval=1d name=Update_combined on-event=\
Updater_List policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon \
start-date=2024-02-24 start-time=15:50:16
/system script
add dont-require-permissions=no name=Updater_List owner=admin policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon source="/tool/fetch url=\"https://raw.githubuserc\
ontent.com/Serp07/updater_list_for_mikrotik/main/combined.rsc\" mode=https dst-path=combined.rsc;\
\n\r\
\n:log info \"Downloaded autoaddresslist from github/Serp07 \";\r\
\n/ip/firewall/address-list/remove [find where comment=\"Auto_address_List\"&\"Bruteforce_Blocker\"]\
\n/import file-name=combined.rsc;\r\
\n\
\n:log info \"Removed old autoaddresslist records and imported new list\";\r\
\n\
\n#/file/remove combined.rsc"
/ip firewall filter
add action=drop chain=input comment="Drop new connections from blacklisted IP's to this router" connection-state=new \
in-interface=ether1 in-interface-list=WAN src-address-list=blacklist
```
以下操作不会阻止任何内容,它只会将 IP 添加到你的地址列表中。你仍然需要创建一条防火墙规则,匹配 `src-address-list=blacklist` 并在你的 input 和/或 forward 链中丢弃流量。
为了使用以下任何列表,你需要在 input 或 forward 链中添加类似以下的规则:
add chain=input action=drop comment="Drop new connections from blacklisted IP's to this router" \
connection-state=new src-address-list=blacklist in-interface=ether1-Internet
# 结果
[](https://mikrotik.com/download/changelogs/)
[](https://mikrotik.com/download/changelogs/)
# MikroTik 自动更新地址列表
### 问题
当你提供对服务的公共访问时,要区分恶意连接和正常连接可能会相当困难。
### 解决方案
MikroTik 借助地址列表(address lists)来解决此问题……只需将恶意地址放入列表并阻止列表中的所有内容。听起来很有趣对吧……或者也许并非如此?当然,你可以(也应该)手动创建规则来检测滥用行为并动态创建列表……但是你还可以做更多,你可以订阅由其他人维护的列表,如 Spamhaus、dshield 等,
### 解析列表示例
由 Serp07 生成于 2024-02-24 01:59:30
/ip firewall address-list
add list=blacklist address=1.4.0.0/17 comment=SpamHaus
add list=blacklist address=1.10.16.0/20 comment=SpamHaus
add list=blacklist address=1.116.0.0/14 comment=SpamHaus
...
### 实现方式
实现起来非常简单……将以下代码粘贴到任何 MikroTik 的终端中,你的路由器就会获取最新版本的脚本文件并定期运行它。
### [适用于 RouterOs v6.xx ](updater_list_script_for_v6.xx.rsc)
```
/system scheduler
add comment="Apply combined List" interval=1d name=Update_combined on-event=Updater_List policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon start-date=feb/24/2024 start-time=20:08:41
/system script
add dont-require-permissions=no name=Updater_List owner=admin policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon source="/tool fetch url=\"https://raw.githubusercontent.co\
m/Serp07/updater_list_for_mikrotik/main/combined.rsc\" mode=https dst-path=combined.rsc;\
\n\r\
\n\r\
\n:log info \"Downloaded autoaddresslist from github/Serp07 \";\r\
\n\r\
\n/ip firewall address-list remove [find where comment=\"Auto_address_List\"];\r\
\n/ip firewall address-list remove [find where comment=\"Bruteforce_Blocker\"];\r\
\n\
\n\r\
\n:log info \"Removed old autoaddresslist records and imported new list\";\r\
\n\
\n\r\
\n/import file-name=combined.rsc;\r\
\n\r\
\n#/file/remove combined.rsc"
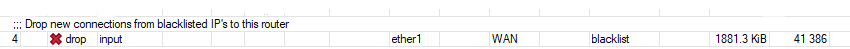
/ip firewall filter
add action=drop chain=input comment="Drop new connections from blacklisted IP's to this router" connection-state=new \
in-interface=ether1 in-interface-list=WAN src-address-list=blacklist
```
### [适用于 RouterOs v7.xx ](updater_list_script_for_v7.xx.rsc)
```
/system scheduler
add comment="Apply combined List" interval=1d name=Update_combined on-event=\
Updater_List policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon \
start-date=2024-02-24 start-time=15:50:16
/system script
add dont-require-permissions=no name=Updater_List owner=admin policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon source="/tool/fetch url=\"https://raw.githubuserc\
ontent.com/Serp07/updater_list_for_mikrotik/main/combined.rsc\" mode=https dst-path=combined.rsc;\
\n\r\
\n:log info \"Downloaded autoaddresslist from github/Serp07 \";\r\
\n/ip/firewall/address-list/remove [find where comment=\"Auto_address_List\"&\"Bruteforce_Blocker\"]\
\n/import file-name=combined.rsc;\r\
\n\
\n:log info \"Removed old autoaddresslist records and imported new list\";\r\
\n\
\n#/file/remove combined.rsc"
/ip firewall filter
add action=drop chain=input comment="Drop new connections from blacklisted IP's to this router" connection-state=new \
in-interface=ether1 in-interface-list=WAN src-address-list=blacklist
```
以下操作不会阻止任何内容,它只会将 IP 添加到你的地址列表中。你仍然需要创建一条防火墙规则,匹配 `src-address-list=blacklist` 并在你的 input 和/或 forward 链中丢弃流量。
为了使用以下任何列表,你需要在 input 或 forward 链中添加类似以下的规则:
add chain=input action=drop comment="Drop new connections from blacklisted IP's to this router" \
connection-state=new src-address-list=blacklist in-interface=ether1-Internet
# 结果
标签:DShield, IP 地址批量处理, IP黑名单, MikroTik, RouterOS, Spamhaus, Streamlit, 地址列表, 威胁情报, 开发者工具, 恶意IP拦截, 数字取证, 系统调度, 网络安全, 自动化脚本, 访问控制, 路由器配置, 运维自动化, 防火墙, 隐私保护