botesjuan/Burp-Suite-Certified-Practitioner-Exam-Study
GitHub: botesjuan/Burp-Suite-Certified-Practitioner-Exam-Study
一份针对 Burp Suite 认证从业者(BSCP)考试的系统化学习指南,涵盖了 Web 漏洞利用技巧与工具高级用法。
Stars: 1325 | Forks: 365
# Burp Suite 认证从业者考试学习
**[扫描 (SCANNING)](#scanning) - 枚举**
[重点扫描](#focus-scanning)
[扫描非标准实体](#scanning-non-standard-data-structures)
**[立足点 (FOOTHOLD)](#foothold) - 阶段 1**
[内容发现](#content-discovery)
[DOM-XSS](#dom-based-xss)
[XSS 跨站脚本攻击](#cross-site-scripting)
[Web 缓存投毒](#web-cache-poison)
[Host 头](#host-headers)
[HTTP 请求走私](#http-request-smuggling)
[暴力破解](#brute-force)
[身份验证](#authentication)
**[权限提升 (PRIVILEGE ESCALATION)](#privilege-escalation) - 阶段 2**
[CSRF - 账户接管](#csrf-account-takeover)
[密码重置](#password-reset)
[SQLi - SQL 注入](#sql-injection)
[JWT - JSON Web Tokens](#jwt)
[原型污染](#prototype-pollution)
[API 测试](#api-testing)
[访问控制](#access-control)
[GraphQL API 端点](#graphql-api)
[CORS - 跨源资源共享](#cors)
**[数据渗出 (DATA EXFILTRATION)](#data-exfiltration) - 阶段 3**
[XXE - XML 实体与注入](#xxe-injections)
[SSRF - 服务端请求伪造](#ssrf---server-side-request-forgery)
[SSTI - 服务端模板注入](#ssti---server-side-template-injection)
[SSPP - 服务端原型污染](#sspp---server-side-prototype-pollution)
[LFI - 文件路径遍历](#file-path-traversal)
[文件上传](#file-uploads)
[反序列化](#deserialization)
[OS 命令注入](#os-command-injection)
**[附录 (APPENDIX)](#appendix)**
[Python 脚本](#python-scripts)
[Payloads](payloads/README.md)
[字典](https://github.com/botesjuan/Burp-Suite-Certified-Practitioner-Exam-Study/tree/main/wordlists)
[重点目标扫描](#focus-scanning)
[方法](#approach)
[额外培训内容](#extra-training-content)
[我的 Burp 技巧](#burp-exam-results)
[我的 Burp Suite 认证从业者证书。](https://portswigger.net/web-security/e/c/6e42f5738e5b9bf8?utm_source=office&utm_medium=email&utm_campaign=burp-prac-cert-pass-success)
# 扫描 (Scanning)
[重点扫描](#focus-scanning)
[扫描非标准实体](#scanning-non-standard-data-structures)
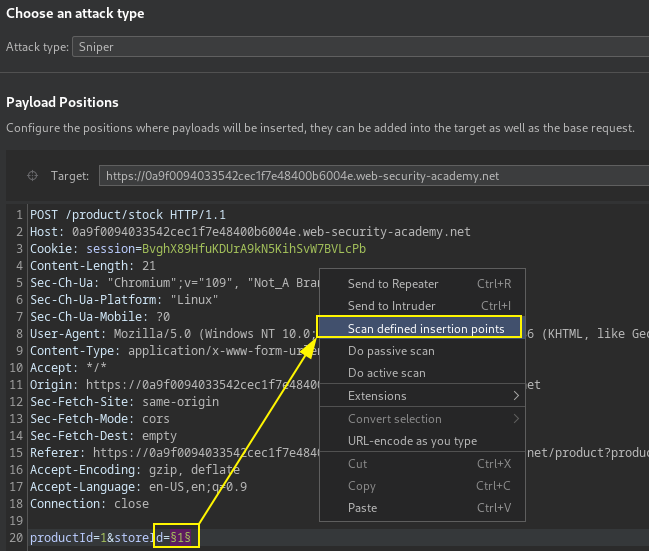
## 重点扫描
```