keraattin/EmailAnalyzer
GitHub: keraattin/EmailAnalyzer
一款用于从 .eml 文件中提取邮件头、链接、附件和哈希值并自动生成威胁情报调查链接的钓鱼邮件分析 CLI 工具。
Stars: 290 | Forks: 41


# EmailAnalyzer
使用 EmailAnalyzer,您可以分析可疑电子邮件。您可以从 .eml 文件中提取邮件头、链接和哈希值。
## 用法
```
usage: email-analyzer.py [-h] [--version] -f FILENAME [-H] [-d] [-l] [-a] [-A] [-D] [-i] [-o OUTPUT]
options:
-h, --help show this help message and exit
--version Show program version and exit
-f, --filename FILENAME
Name of the EML file
-H, --headers To get the Headers of the Email
-d, --digests To get the Digests of the Email
-l, --links To get the Links from the Email
-a, --attachments To get the Attachments from the Email
-A, --authentication To get the Authentication Results of the Email (SPF, DKIM, DMARC)
-D, --defang Defang URLs in Links output (hxxps://, [.] notation)
-i, --investigate Activate if you want an investigation
-o OUTPUT, --output OUTPUT
Name of the Output file (Only HTML or JSON format supported)
```
## 运行所有分析
此命令将为您提供邮件头、链接、附件和摘要及其调查结果:
```
python3 email-analyzer.py -f
```
## 提取输出
如果您想将输出结果提取到文件中,可以使用以下命令:
```
python3 email-analyzer.py -f -o report.html
```
 或者
```
python3 email-analyzer.py -f
或者
```
python3 email-analyzer.py -f -o report.json
```
## 仅获取邮件头
```
python3 email-analyzer.py -f --headers
```
或者
```
python3 email-analyzer.py -f -H
```
```
██╗ ██╗███████╗ █████╗ ██████╗ ███████╗██████╗ ███████╗
██║ ██║██╔════╝██╔══██╗██╔══██╗██╔════╝██╔══██╗██╔════╝
███████║█████╗ ███████║██║ ██║█████╗ ██████╔╝███████╗
██╔══██║██╔══╝ ██╔══██║██║ ██║██╔══╝ ██╔══██╗╚════██║
██║ ██║███████╗██║ ██║██████╔╝███████╗██║ ██║███████║
╚═╝ ╚═╝╚══════╝╚═╝ ╚═╝╚═════╝ ╚══════╝╚═╝ ╚═╝╚══════╝
_________________________________________________________
[received]
from TEST.TEST.PROD.OUTLOOK.COM (2603:10a6:20b:4f2::13)
by TEST.TEST.PROD.OUTLOOK.COM with HTTPS; Fri, 25 Nov 2022
12:36:39 +0000
_________________________________________________________
_________________________________________________________
[content-type]
multipart/alternative; boundary=335b23d5689bd75ab002f9c46a6e8023c265d60dd923308dcc7eb7a2cf25
_________________________________________________________
_________________________________________________________
[date]
Fri, 25 Nov 2022 12:36:36 +0000 (UTC)
_________________________________________________________
_________________________________________________________
[subject]
How to use EmailAnalyzer
_________________________________________________________
_________________________________________________________
[reply-to]
info123@gmail.com
_________________________________________________________
_________________________________________________________
[from]
"Admin"
_________________________________________________________
_________________________________________________________
[to]
me
_________________________________________________________
_________________________________________________________
[x-sender-ip]
127.0.0.1
_________________________________________________________
```
## 调查邮件头
```
python3 email-analyzer.py -f --headers --investigate
```
或者
```
python3 email-analyzer.py -f -Hi
```
```
█████╗ ███╗ ██╗ █████╗ ██╗ ██╗ ██╗███████╗██╗███████╗
██╔══██╗████╗ ██║██╔══██╗██║ ╚██╗ ██╔╝██╔════╝██║██╔════╝
███████║██╔██╗ ██║███████║██║ ╚████╔╝ ███████╗██║███████╗
██╔══██║██║╚██╗██║██╔══██║██║ ╚██╔╝ ╚════██║██║╚════██║
██║ ██║██║ ╚████║██║ ██║███████╗██║ ███████║██║███████║
╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚══════╝╚═╝ ╚══════╝╚═╝╚══════╝
_________________________________________________________
[X-Sender-IP]
Virustotal:
https://www.virustotal.com/gui/search/127.0.0.1
Abuseipdb:
https://www.abuseipdb.com/check/127.0.0.1
_________________________________________________________
_________________________________________________________
[Spoof Check]
Reply-To:
info123@gmail.com
From:
info@officialmail.com
Conclusion:
Reply Address and From Address is NOT Same. This mail may be SPOOFED.
_________________________________________________________
```
### 调查检查项
`-i` / `--investigate` 标志在与 `-H` 一起使用时,会启用以下所有检查:
| 检查项 | 检测内容 |
|---|---|
| **X-Sender-IP** | 为发送 IP 生成 VirusTotal 和 AbuseIPDB 查询链接 |
| **X-Originating-IP** | 当存在 `X-Originating-IP` 标头时,为其生成相同的查询链接 |
| **Received IPs** | 从 `Received` 标头中提取所有公共 IP 并生成查询链接 |
| **欺骗检查** | 当 `Reply-To` 和 `From` 地址不一致时进行标记 |
| **显示名称检查** | 当 `From` 显示名称包含与发送域不匹配的域时进行标记(例如,显示名称为 `"paypal.com"` 但从 `attacker@gmail.com` 发送) |
| **Reply-To 域检查** | 当 `Reply-To` 域与 `From` 域不同时进行标记——回复将被重定向到不同的域 |
| **可疑标头** | 标记缺失的 `Message-ID`、缺失的 `MIME-Version`、日期距离当前过去或未来太远(>2 天 / >30 天),以及已知的群发邮件 `X-Mailer` 值 |
## 获取身份验证结果
```
python3 email-analyzer.py -f --authentication
```
或者
```
python3 email-analyzer.py -f -A
```
解析 `Authentication-Results` 和 `Received-SPF` 标头,以提取 SPF、DKIM 和 DMARC 判定结果。
```
█████╗ ██╗ ██╗████████╗██╗ ██╗███████╗███╗ ██╗████████╗██╗ ██████╗ █████╗ ████████╗██╗ ██████╗ ███╗ ██╗
██╔══██╗██║ ██║╚══██╔══╝██║ ██║██╔════╝████╗ ██║╚══██╔══╝██║██╔════╝██╔══██╗╚══██╔══╝██║██╔═══██╗████╗ ██║
███████║██║ ██║ ██║ ███████║█████╗ ██╔██╗ ██║ ██║ ██║██║ ███████║ ██║ ██║██║ ██║██╔██╗ ██║
██╔══██║██║ ██║ ██║ ██╔══██║██╔══╝ ██║╚██╗██║ ██║ ██║██║ ██╔══██║ ██║ ██║██║ ██║██║╚██╗██║
██║ ██║╚██████╔╝ ██║ ██║ ██║███████╗██║ ╚████║ ██║ ██║╚██████╗██║ ██║ ██║ ██║╚██████╔╝██║ ╚████║
╚═╝ ╚═╝ ╚═════╝ ╚═╝ ╚═╝ ╚═╝╚══════╝╚═╝ ╚═══╝ ╚═╝ ╚═╝ ╚═════╝╚═╝ ╚═╝ ╚═╝ ╚═╝ ╚═════╝ ╚═╝ ╚═══╝
_________________________________________________________
[SPF]
pass
_________________________________________________________
_________________________________________________________
[DKIM]
pass
_________________________________________________________
_________________________________________________________
[DMARC]
pass
_________________________________________________________
```
## 获取 eml 文件及其内容的哈希值
```
python3 email-analyzer.py -f --digests
```
或者
```
python3 email-analyzer.py -f -d
```
```
██████╗ ██╗ ██████╗ ███████╗███████╗████████╗███████╗
██╔══██╗██║██╔════╝ ██╔════╝██╔════╝╚══██╔══╝██╔════╝
██║ ██║██║██║ ███╗█████╗ ███████╗ ██║ ███████╗
██║ ██║██║██║ ██║██╔══╝ ╚════██║ ██║ ╚════██║
██████╔╝██║╚██████╔╝███████╗███████║ ██║ ███████║
╚═════╝ ╚═╝ ╚═════╝ ╚══════╝╚══════╝ ╚═╝ ╚══════╝
_________________________________________________________
[File MD5]
81dc9bdb52d04dc20036dbd8313ed055
_________________________________________________________
_________________________________________________________
[File SHA1]
7110eda4d09e062aa5e4a390b0a572ac0d2c0220
_________________________________________________________
_________________________________________________________
[File SHA256]
03ac674216f3e15c761ee1a5e255f067953623c8b388b4459e13f978d7c846f4
_________________________________________________________
_________________________________________________________
[Content MD5]
827ccb0eea8a706c4c34a16891f84e7b
_________________________________________________________
_________________________________________________________
[Content SHA1]
8cb2237d0679ca88db6464eac60da96345513964
_________________________________________________________
_________________________________________________________
[Content SHA256]
5994471abb01112afcc18159f6cc74b4f511b99806da59b3caf5a9c173cacfc5
_________________________________________________________
```
## 调查摘要
```
python3 email-analyzer.py -f --digests --investigate
```
或者
```
python3 email-analyzer.py -f -di
```
```
█████╗ ███╗ ██╗ █████╗ ██╗ ██╗ ██╗███████╗██╗███████╗
██╔══██╗████╗ ██║██╔══██╗██║ ╚██╗ ██╔╝██╔════╝██║██╔════╝
███████║██╔██╗ ██║███████║██║ ╚████╔╝ ███████╗██║███████╗
██╔══██║██║╚██╗██║██╔══██║██║ ╚██╔╝ ╚════██║██║╚════██║
██║ ██║██║ ╚████║██║ ██║███████╗██║ ███████║██║███████║
╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚══════╝╚═╝ ╚══════╝╚═╝╚══════╝
_________________________________________________________
[File MD5]
Virustotal:
https://www.virustotal.com/gui/search/81dc9bdb52d04dc20036dbd8313ed055
_________________________________________________________
_________________________________________________________
[File SHA1]
Virustotal:
https://www.virustotal.com/gui/search/7110eda4d09e062aa5e4a390b0a572ac0d2c0220
_________________________________________________________
_________________________________________________________
[File SHA256]
Virustotal:
https://www.virustotal.com/gui/search/03ac674216f3e15c761ee1a5e255f067953623c8b388b4459e13f978d7c846f4
_________________________________________________________
_________________________________________________________
[Content MD5]
Virustotal:
https://www.virustotal.com/gui/search/827ccb0eea8a706c4c34a16891f84e7b
_________________________________________________________
_________________________________________________________
[Content SHA1]
Virustotal:
https://www.virustotal.com/gui/search/8cb2237d0679ca88db6464eac60da96345513964
_________________________________________________________
_________________________________________________________
[Content SHA256]
Virustotal:
https://www.virustotal.com/gui/search/5994471abb01112afcc18159f6cc74b4f511b99806da59b3caf5a9c173cacfc5
_________________________________________________________
```
## 从 eml 文件中获取链接
```
python3 email-analyzer.py -f --links
```
或者
```
python3 email-analyzer.py -f -l
```
```
██╗ ██╗███╗ ██╗██╗ ██╗███████╗
██║ ██║████╗ ██║██║ ██╔╝██╔════╝
██║ ██║██╔██╗ ██║█████╔╝ ███████╗
██║ ██║██║╚██╗██║██╔═██╗ ╚════██║
███████╗██║██║ ╚████║██║ ██╗███████║
╚══════╝╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚══════╝
[1]->https://example.com
[2]->https://testlinks.com/campaing/123124
```
## 获取净化链接
添加 `-D` / `--defang` 可将 URL 转换为净化格式(`hxxps://`,使用 `[.]` 替代域名的点)。在报告中分享是安全的,不会生成可点击的链接。
```
python3 email-analyzer.py -f --links --defang
```
或者
```
python3 email-analyzer.py -f -lD
```
```
[1]->hxxps://example[.]com
[2]->hxxps://testlinks[.]com/campaing/123124
```
## 调查链接
```
python3 email-analyzer.py -f --links --investigate
```
或者
```
python3 email-analyzer.py -f --li
```
```
█████╗ ███╗ ██╗ █████╗ ██╗ ██╗ ██╗███████╗██╗███████╗
██╔══██╗████╗ ██║██╔══██╗██║ ╚██╗ ██╔╝██╔════╝██║██╔════╝
███████║██╔██╗ ██║███████║██║ ╚████╔╝ ███████╗██║███████╗
██╔══██║██║╚██╗██║██╔══██║██║ ╚██╔╝ ╚════██║██║╚════██║
██║ ██║██║ ╚████║██║ ██║███████╗██║ ███████║██║███████║
╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚══════╝╚═╝ ╚══════╝╚═╝╚══════╝
_________________________________________________________
[1]
VirusTotal:
https://www.virustotal.com/gui/search/example.com
UrlScan:
https://urlscan.io/search/#example.com
_________________________________________________________
_________________________________________________________
[2]
VirusTotal:
https://www.virustotal.com/gui/search/testlinks.com/campaing/123124
UrlScan:
https://urlscan.io/search/#testlinks.com/campaing/123124
_________________________________________________________
```
## 从 eml 文件中获取附件
```
python3 email-analyzer.py -f --attachments
```
或者
```
python3 email-analyzer.py -f -a
```
```
█████╗ ████████╗████████╗ █████╗ ██████╗██╗ ██╗███████╗
██╔══██╗╚══██╔══╝╚══██╔══╝██╔══██╗██╔════╝██║ ██║██╔════╝
███████║ ██║ ██║ ███████║██║ ███████║███████╗
██╔══██║ ██║ ██║ ██╔══██║██║ ██╔══██║╚════██║
██║ ██║ ██║ ██║ ██║ ██║╚██████╗██║ ██║███████║
╚═╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝ ╚═════╝╚═╝ ╚═╝╚══════╝
[1] example.pdf (application/pdf)
_________________________________________________________
[2] malicious.pdf (application/octet-stream)
_________________________________________________________
```
## 调查附件
```
python3 email-analyzer.py -f --attachments --investigate
```
或者
```
python3 email-analyzer.py -f -ai
```
```
█████╗ ███╗ ██╗ █████╗ ██╗ ██╗ ██╗███████╗██╗███████╗
██╔══██╗████╗ ██║██╔══██╗██║ ╚██╗ ██╔╝██╔════╝██║██╔════╝
███████║██╔██╗ ██║███████║██║ ╚████╔╝ ███████╗██║███████╗
██╔══██║██║╚██╗██║██╔══██║██║ ╚██╔╝ ╚════██║██║╚════██║
██║ ██║██║ ╚████║██║ ██║███████╗██║ ███████║██║███████║
╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚══════╝╚═╝ ╚══════╝╚═╝╚══════╝
_________________________________________________________
- example.pdf
Virustotal:
[Name Search]->https://www.virustotal.com/gui/search/example.pdf
[MD5]->https://www.virustotal.com/gui/search/81dc9bdb52d04dc20036dbd8313ed055
[SHA1]->https://www.virustotal.com/gui/search/7110eda4d09e062aa5e4a390b0a572ac0d2c0220
[SHA256]->https://www.virustotal.com/gui/search/03ac674216f3e15c761ee1a5e255f067953623c8b388b4459e13f978d7c846f4
_________________________________________________________
_________________________________________________________
- malicious.pdf
Virustotal:
[Name Search]->https://www.virustotal.com/gui/search/malicious.pdf
[MD5]->https://www.virustotal.com/gui/search/827ccb0eea8a706c4c34a16891f84e7b
[SHA1]->https://www.virustotal.com/gui/search/8cb2237d0679ca88db6464eac60da96345513964
[SHA256]->https://www.virustotal.com/gui/search/5994471abb01112afcc18159f6cc74b4f511b99806da59b3caf5a9c173cacfc5
_________________________________________________________
_________________________________________________________
- Duplicate Warning
[03ac674216f3e15c761ee1a5e255f067953623c8b388b4459e13f978d7c846f4]
example.pdf
malicious.pdf
_________________________________________________________
```
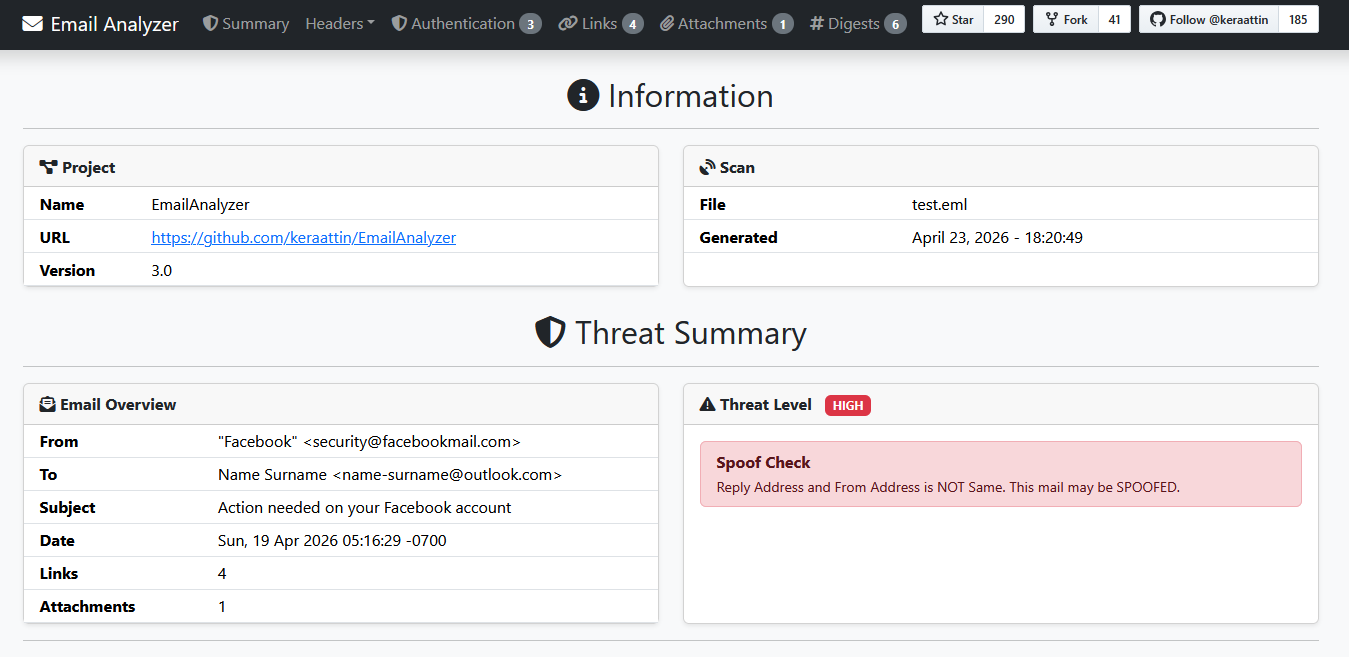
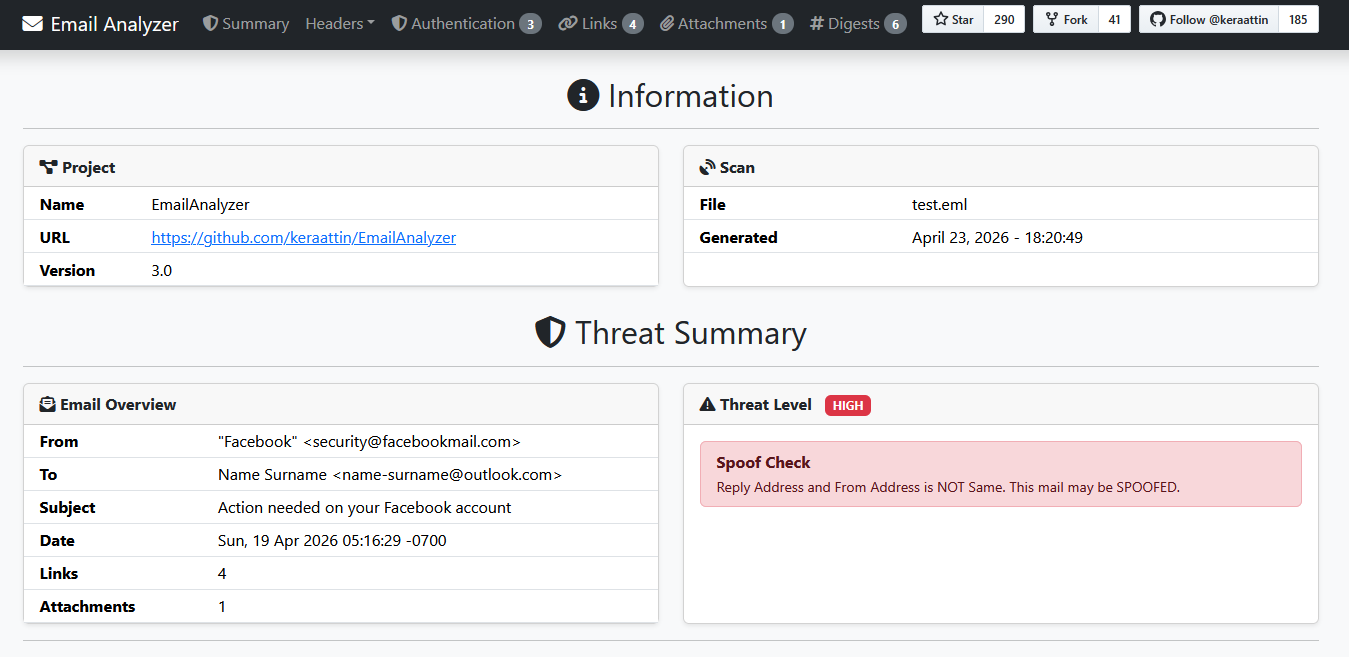
## HTML 报告
生成一个包含 Bootstrap 5 样式的独立 HTML 报告:
```
python3 email-analyzer.py -f -o report.html
```
HTML 报告包含:
- **威胁摘要** — 电子邮件概览(发件人、收件人、主题、日期、链接/附件数量),威胁级别徽章(低 / 中 / 高),以及针对每个触发的调查检查项的 Bootstrap 警告卡片
- **固定导航栏** — 滚动时始终可见,带有指向每个部分的跳转链接
- **复制到剪贴板按钮** — 位于每个哈希值和 URL 旁边,便于快速进行威胁情报查询
- **可点击的调查链接** — 所有 VirusTotal、AbuseIPDB 和 URLscan 条目均渲染为锚点标签
- **合并表格** — 链接、附件和摘要各自在统一的表格中显示数据和扫描链接
## 检查版本
```
python3 email-analyzer.py --version
```
## 测试
测试套件使用 [pytest](https://pytest.org)。在运行测试之前请先安装它:
```
pip install pytest
```
从项目根目录运行所有测试:
```
python3 -m pytest tests/ -v
```
运行特定的测试文件:
```
python3 -m pytest tests/test_headers.py -v
python3 -m pytest tests/test_links.py -v
python3 -m pytest tests/test_digests.py -v
python3 -m pytest tests/test_attachments.py -v
python3 -m pytest tests/test_auth_results.py -v
python3 -m pytest tests/test_defang.py -v
python3 -m pytest tests/test_duplicate_attachments.py -v
python3 -m pytest tests/test_cli.py -v
```
### 测试结构
```
tests/
├── fixtures/ # Sample .eml files used by tests
│ ├── basic.eml
│ ├── spoofed.eml
│ ├── not_spoofed.eml
│ ├── display_name_only.eml
│ ├── quoted_printable.eml
│ ├── no_links.eml
│ ├── binary_attachment.eml
│ ├── multi_attachment.eml
│ ├── image_attachment.eml
│ ├── no_attachment.eml
│ ├── no_filename_attachment.eml
│ ├── multipart_alternative.eml
│ ├── duplicate_attachments.eml
│ ├── rfc2047_encoded.eml
│ ├── rfc2047_qp_encoded.eml
│ ├── rfc2047_mixed.eml
│ ├── received_public_ips.eml
│ ├── received_mixed_ips.eml
│ ├── auth_pass_all.eml
│ ├── auth_fail_spf_dkim.eml
│ ├── auth_softfail_spf.eml
│ ├── auth_received_spf_only.eml
│ ├── auth_no_headers.eml
│ ├── phishing_displayname.eml
│ ├── legitimate_displayname.eml
│ ├── suspicious_no_message_id.eml
│ ├── suspicious_future_date.eml
│ ├── suspicious_old_date.eml
│ ├── suspicious_xmailer.eml
│ ├── clean_headers.eml
│ ├── originating_ip.eml
│ ├── replyto_diff_domain.eml
│ └── replyto_same_domain.eml
├── conftest.py # Shared fixtures and module loader
├── test_headers.py # Tests for get_headers()
├── test_links.py # Tests for get_links()
├── test_digests.py # Tests for get_digests()
├── test_attachments.py # Tests for get_attachments()
├── test_attachment_mime.py # Tests for MIME type in attachment output
├── test_duplicate_attachments.py # Tests for duplicate attachment detection
├── test_rfc2047.py # Tests for RFC 2047 encoded header decoding
├── test_received_ips.py # Tests for Received header IP extraction
├── test_auth_results.py # Tests for SPF/DKIM/DMARC parsing
├── test_defang.py # Tests for defanged URL output
├── test_plaintext_links.py # Tests for plain-text URL extraction
├── test_display_name.py # Tests for display name spoofing detection
├── test_suspicious_headers.py # Tests for suspicious header pattern detection
├── test_originating_ip.py # Tests for X-Originating-IP investigation
├── test_replyto_domain.py # Tests for Reply-To domain check
├── test_html_generator.py # Tests for HTML report generation and XSS escaping
├── test_cli.py # Tests for CLI argument validation
└── test_encoding.py # Tests for non-UTF-8 email encoding handling
```
 或者
```
python3 email-analyzer.py -f
或者
```
python3 email-analyzer.py -f 标签:CISA项目, Defang URL, EML解析, Python, Python扩展, SPF/DKIM/DMARC验证, 哈希提取, 威胁情报, 安全分析工具, 安全取证, 安全规则引擎, 开发者工具, 开源安全工具, 无后门, 电子邮件分析, 网络安全, 自动化分析, 跨站脚本, 逆向工程平台, 邮件头提取, 钓鱼邮件检测, 链接提取, 附件分析, 隐私保护