sandworm-hq/sandworm-audit
GitHub: sandworm-hq/sandworm-audit
JavaScript/PHP 项目依赖项的安全漏洞扫描与许可证合规审计工具
Stars: 477 | Forks: 6

为您应用程序依赖项生成的精美安全与许可证合规报告 🪱 ## 概述 - 免费开源命令行工具 - 适用于 [npm](http://npmjs.com/)、[Yarn](https://yarnpkg.com/)、[pnpm](https://pnpm.io/) 和 [Composer](https://getcomposer.org/) - 扫描您的项目和依赖项,发现漏洞、许可证和元数据问题 - 支持 npm/Yarn/pnpm workspaces - 支持[将问题标记为已解决](https://docs.sandworm.dev/audit/resolving-issues) - 支持[自定义许可证策略](https://docs.sandworm.dev/audit/license-policies) - 适用于 CI/GIT hook 工作流的[可配置失败条件](https://docs.sandworm.dev/audit/fail-policies) - 可连接到[私有/自定义 npm 源](https://docs.sandworm.dev/audit/custom-registries) - 输出: - JSON 问题与许可证使用报告 - 易于理解的 SVG 依赖树与树图可视化 - 由 D3 提供支持 - 叠加安全漏洞信息 - 叠加包许可证信息 - 所有依赖项与许可证信息的 CSV ### 生成报告  ### 浏览图表  ### CSV 输出  ### JSON 输出 ``` { "createdAt": "...", "packageManager": "...", "name": "...", "version": "...", "rootVulnerabilities": [...], "dependencyVulnerabilities": [...], "licenseUsage": {...}, "licenseIssues": [...], "metaIssues": [...], "errors": [...], } ``` 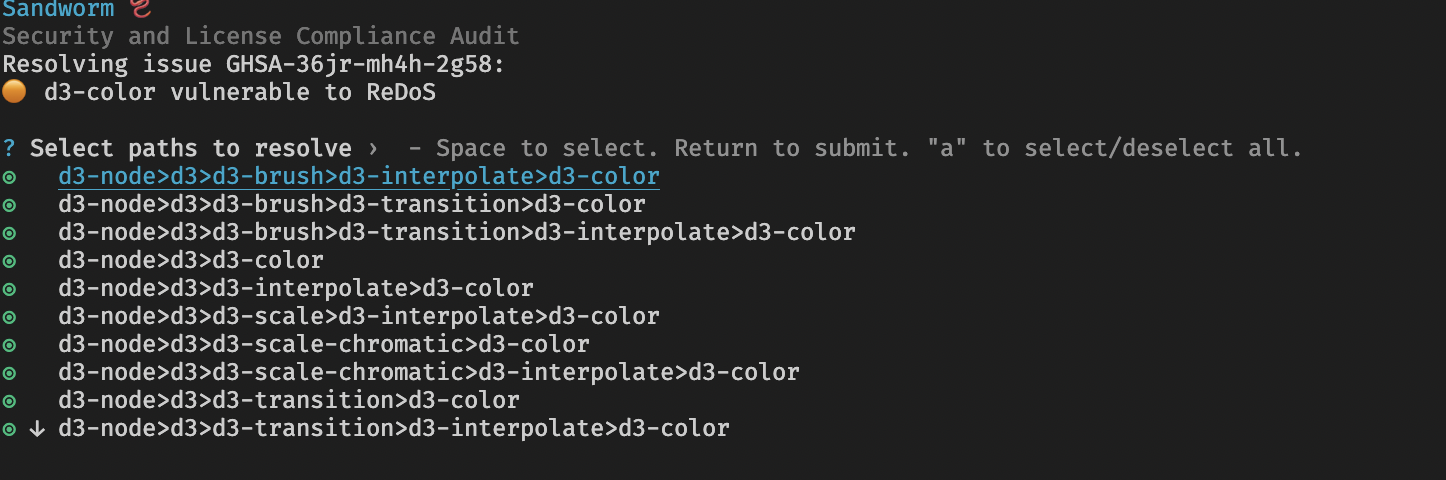 ### 参与其中 - 有支持问题?[在此发布](https://github.com/sandworm-hq/sandworm-audit/discussions/categories/q-a)。 - 有功能请求?[在此发布](https://github.com/sandworm-hq/sandworm-audit/discussions/categories/ideas)。 - 发现了安全问题?[请参阅 SECURITY.md](SECURITY.md)。 - 发现了错误?[提交 issue](https://github.com/sandworm-hq/sandworm-audit/issues/new/choose)。 - 想要编写代码?请参阅 [CONTRIBUTING.md](CONTRIBUTING.md)。 ## 快速开始 通过您喜欢的包管理器全局安装 `sandworm-audit`: ``` npm install -g @sandworm/audit # 或 yarn global add @sandworm/audit # 或 pnpm add -g @sandworm/audit ``` 然后,在应用程序的根目录中运行 `sandworm-audit`。请确保存在清单文件和锁文件(lockfile)。 您也可以通过以下方式直接运行而无需安装: ``` npx @sandworm/audit@latest # 或 yarn dlx -p @sandworm/audit sandworm # 或 pnpm --package=@sandworm/audit dlx sandworm ``` 可用选项: ``` Options: -v, --version Show version number [boolean] --help Show help [boolean] -o, --output-path The path of the output directory, relative to the application path [string] [default: "sandworm"] -d, --include-dev Include dev dependencies[boolean] [default: false] --sv, --show-versions Show package versions in chart names [boolean] [default: false] -p, --path The path to the application to audit [string] --md, --max-depth Max depth to represent in charts [number] --ms, --min-severity Min issue severity to represent in charts [string] --lp, --license-policy Custom license policy JSON string [string] -f, --from Load data from "registry" or "disk" [string] [default: "registry"] --fo, --fail-on Fail policy JSON string [string] [default: "[]"] -s, --summary Print a summary of the audit results to the console [boolean] [default: true] --root-vulnerabilites Include vulnerabilities for the root project [boolean] [default: false] --skip-license-issues Skip scanning for license issues [boolean] [default: false] --skip-meta-issues Skip scanning for meta issues [boolean] [default: false] --skip-tree Don't output the dependency tree chart [boolean] [default: false] --force-tree Force build large dependency tree charts [boolean] [default: false] --skip-treemap Don't output the dependency treemap chart [boolean] [default: false] --skip-csv Don't output the dependency csv file [boolean] [default: false] --skip-report Don't output the report json file [boolean] [default: false] --skip-all Don't output any file [boolean] [default: false] --show-tips Show usage tips [boolean] [default: true] ``` ### 文档 ## Sandworm.dev 上的示例 - [Apollo Client](https://sandworm.dev/npm/package/apollo-client) - [AWS SDK](https://sandworm.dev/npm/package/aws-sdk) - [Express](https://sandworm.dev/npm/package/express) - [Mocha](https://sandworm.dev/npm/package/mocha) - [Mongoose](https://sandworm.dev/npm/package/mongoose) - [Nest.js](https://sandworm.dev/npm/package/@nestjs/cli) - [Redis](https://sandworm.dev/npm/package/redis)
标签:Composer, D3.js, JavaScript安全, LNA, MITM代理, Node.js安全, npm审计, pnpm, Yarn, 云安全监控, 依赖关系可视化, 依赖性检查, 合规性报告, 开源组件治理, 暗色界面, 网络安全, 聊天机器人, 自定义脚本, 自定义脚本, 许可证合规, 软件供应链安全, 远程方法调用, 隐私保护, 静态分析