b3n-j4m1n/snrublist3r
GitHub: b3n-j4m1n/snrublist3r
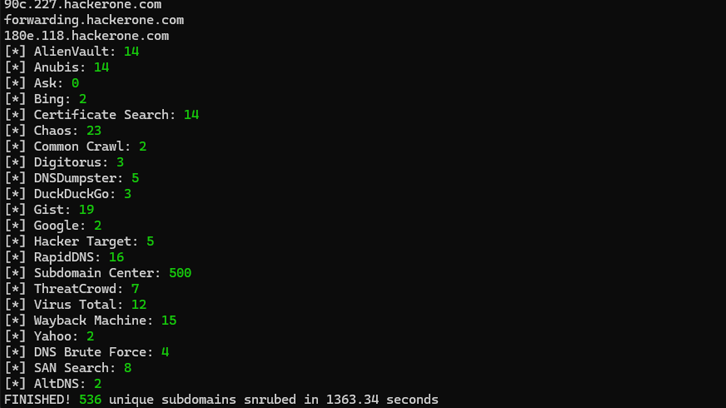
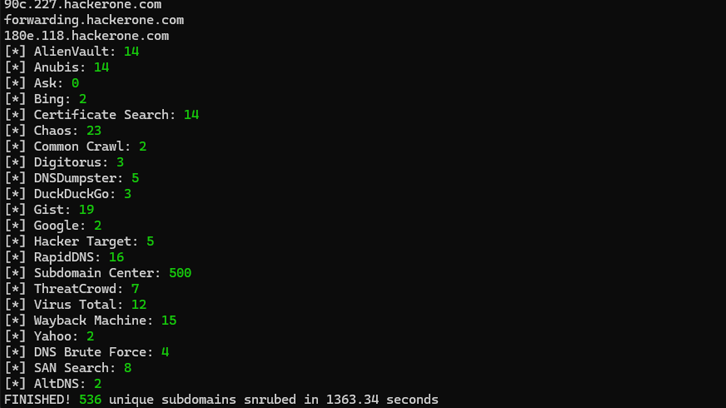
一款基于多源并行与暴力破解的子域名枚举工具,旨在高效发现目标域名的隐藏子域。
Stars: 25 | Forks: 2

🍩
关键特性 •
使用方法 •
安装 •
致谢
🍺
## 关键特性
- 19个来源,全部无密钥(无需订阅)
- 异步暴力破解,富有激情,每秒2000+请求(取决于解析器和网络性能)
- 变异暴力破解,即对发现的域名进行排列组合后用于暴力破解
- TLS证书主题备用名称(SAN)枚举
- 支持Linux和Windows
#### 来源
[AlienVault](https://otx.alienvault.com/), [Anubis](https://github.com/jonluca/Anubis), [Ask](https://www.ask.com/), [Bing](https://www.bing.com/), [Certificate Search](https://crt.sh/), [Chaos](https://chaos.projectdiscovery.io/), [Common Crawl](https://commoncrawl.org/), [Digitorus](https://www.digitorus.com/), [DNSDumpster](https://dnsdumpster.com/), [DuckDuckGo](https://duckduckgo.com/), [Gist](https://gist.github.com/), [Google](https://www.google.com), [Hacker Target](https://hackertarget.com/), [RapidDNS](https://rapiddns.io/), [ARPSyndicate](https://www.subdomain.center/), [ThreatCrowd](http://ci-www.threatcrowd.org/), [VirusTotal](https://www.virustotal.com/), [WayBack Machine](https://archive.org/web/), [Yahoo](https://yahoo.com/)
## 使用方法
```
usage: snrublist3r.py [-h] [-d DOMAIN] [-df DOMAINS_FILE] [-s SOURCES]
[--fast] [--proxy PROXY] [--disable-scraping] [-b]
[-sf SUBDOMAINS_FILE] [-rf RESOLVERS_FILE]
[--tasks TASKS] [--timeout TIMEOUT]
[--dns-retries DNS_RETRIES] [-m]
[-pf PERMUTATION_FILE] [--autopilot] [--max-alts MAX_ALTS]
[--san] [--loop] [-o OUTPUT_FILE] [-v] [--debug]
[--silent]
optional arguments:
-h, --help show this help message and exit
TARGET(S):
-d DOMAIN, --domain DOMAIN
root domain
-df DOMAINS_FILE, --domains-file DOMAINS_FILE
input file of line-separated root domains
SCRAPING:
-s SOURCES, --sources SOURCES
comma-separated list of sources, options are alienvault,
anubis, ask, bing, certificatesearch, chaos,
commoncrawl, digitorus, dnsdumpster, duckduckgo, gist,
google, hackertarget, rapiddns, subdomaincenter,
threatcrowd, virustotal, waybackmachine,
yahoo (default is all)
--fast run only fast scraping modules (excludes Common Crawl,
DuckDuckGo, Gist)
--proxy PROXY proxy used for source scraper, e.g.
'http://127.0.0.1:8080'
--disable-scraping disable scraping of any sources (use with brute force
options)
BRUTE FORCE:
-b enable raw brute force
-sf SUBDOMAINS_FILE, --subdomains-file SUBDOMAINS_FILE
input file of line-separated subdomains used in the DNS
brute force (default is bitquark-subdomains-top100000.txt)
-rf RESOLVERS_FILE, --resolvers-file RESOLVERS_FILE
input file of line-separated resolver IPs used in the
DNS brute force
--tasks TASKS number of concurrent tasks in the brute-force queue
(default is 256)
--timeout TIMEOUT timeout on DNS resolution (default is 45)
--dns-retries DNS_RETRIES
retries for DNS resolution (default is 2)
-m enable mutation brute force
-pf PERMUTATION_FILE, --permutation-file PERMUTATION_FILE
input file of line-separated strings used in the
mutation DNS brute force (default is
permutation-strings.txt)
--autopilot ignore input() prompts
--max-alts MAX_ALTS generated mutations limit, which if exceeded the
mutation brute force will not run (useful with
--autopilot), default is ~500,000
SAN SEARCH:
--san enable Subject Alt Names search
CONFIGURATIONS:
--loop run in a continuous loop
OUTPUT:
-o OUTPUT_FILE, --output OUTPUT_FILE
output file to save results
VERBOSITY:
-v enable verbosity
--debug enable debug log level
--silent disable terminal output
```
#### 示例用法
##### 快速
```
python snrublist3r.py -d example.com -v --fast
```
##### 全面的
```
python snrublist3r.py -d example.com -v -b --subdomains ./lists/shubs-subdomains.txt -m
```
##### 仅暴力破解
```
python snrublist3r.py -d example.com -v -b -m --disable-scraping
```
🧠 _注意:默认将使用系统DNS解析器,因此为了追求速度并避免DoS攻击自身,建议不要这样做,而是使用提供的 ./lists/top-resolvers.txt 选项 `-rf`,这将在Cloudflare、Google、OpenDNS和Quad9 DNS解析器之间轮换。_
## 安装
**建议使用 Python 3.9.0+** 以使用 removeprefix() 函数
#### Linux
```
git clone https://github.com/b3n-j4m1n/snrublist3r.git
cd snrublist3r
python -m venv snrublist3r
source ./snrublist3r/bin/activate
pip install -r requirements.txt
```
#### Windows
```
git clone https://github.com/b3n-j4m1n/snrublist3r.git
cd snrublist3r
python -m venv snrublist3r
.\snrublist3r\Scripts\Activate.ps1
pip install -r requirements.txt
```
## 致谢
- [Async DNS Brute](https://github.com/blark/aiodnsbrute) 提供了快速无比的异步DNS暴力破解参考材料。
- [AltDNS](https://awesomeopensource.com/project/elangosundar/awesome-README-templates) 提供了子域名变异模块。
- [SecLists](https://github.com/danielmiessler/SecLists) 提供了词汇表。
- [resolvers](https://github.com/trickest/resolvers) 提供了解析器。
- [Sublist3r](https://github.com/aboul3la/Sublist3r),一个出色的工具,包含许多经过深思熟虑的实用想法。它多年来确保了漏洞赏金的安全。
标签:Anubis, Ask搜索, Crt.sh, DNSDumpster, DNS枚举, Linux工具, SAN枚举, SEO, TLS证书枚举, VirusTotal, Wayback Machine, Windows工具, 二进制发布, 反汇编, 变异爆破, 域名枚举, 多源枚举, 子域名枚举, 子域名爆破, 密钥来源枚举, 开源工具, 异步并发, 排列组合爆破, 端口探测, 系统安全, 网络安全工具, 逆向工具, 高性能请求