cyb3rxp/awesome-soc
GitHub: cyb3rxp/awesome-soc
Stars: 1634 | Forks: 257
# Awesome SOC
收集了用于构建和运行 SOC(包括 CSIRT)的文档来源和领域最佳实践。
这些是基于我作为 SOC/CSIRT 分析师和团队经理的个人经验,以及知名论文的观点。重点更多在于 SOC 而非 CERT/CSIRT。
我的座右铭是:没有反应(响应),检测就是无用的。
注意:一般来说,这里的 SOC 指的是检测活动,而 CERT/CSIRT 指的是事件响应活动。CERT 是一个著名的(前)美国商标,由 [CERT-CC](https://www.sei.cmu.edu/about/divisions/cert/index.cfm) 管理,但我更喜欢 [CSIRT](https://www.enisa.europa.eu/sites/default/files/publications/Incident_Management_guide.pdf) 这个术语,因为它精确地指代了事件响应。
# 目录
* [必读](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#must-read)
* [基本概念](https://github.com/cyb3rxp/awesome-soc/blob/main/soc_basics.md)
* [关键任务手段(工具/传感器)](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#mission-critical-means-toolssensors)
* [IT/安全监控](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#itsecurity-watch)
* [SOAR](https://github.com/cyb3rxp/awesome-soc/blob/main/soar.md)
* [检测工程](https://github.com/cyb3rxp/awesome-soc/blob/main/detection_engineering.md)
* [威胁情报](https://github.com/cyb3rxp/awesome-soc/blob/main/threat_intelligence.md)
* [管理](https://github.com/cyb3rxp/awesome-soc/blob/main/management.md)
* [人力资源与培训](https://github.com/cyb3rxp/awesome-soc/blob/main/hr_training.md)
* [IT 架构](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#it-achitecture-of-a-soc)
* [进阶学习(后续步骤)](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#to-go-further)
* [附录](https://github.com/cyb3rxp/awesome-soc/blob/main/README.md#appendix)
# 必读
## 针对 SOC
* SOC 构建:
* MITRE, [11 strategies for a world-class SOC](https://www.mitre.org/publications/technical-papers/11-strategies-world-class-cybersecurity-operations-center)(或使用[本地文件](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf)):第 0 部分(基础)。
* FIRST, [Building a SOC](https://www.first.org/resources/guides/Factsheet_Building_a_SOC_start_small.pdf)
* NCSC, [Building a SOC](https://www.ncsc.gov.uk/collection/building-a-security-operations-centre)
* Gartner, [SOC model guide](https://fr.scribd.com/document/732782046/Gartner-SOC-Model-Guide-2023)
* Splunk, [State of Security 2023](https://www.splunk.com/en_us/pdfs/gated/ebooks/state-of-security-2023.pdf)
* Microsoft, [Secure your business with 365](https://learn.microsoft.com/en-us/microsoft-365/business-premium/secure-your-business-data?view=o365-worldwide)
* SOC 培训/面试:
* LetsDefend [SOC analyst interview questions](https://github.com/LetsDefend/SOC-Interview-Questions)
* SOC 管理:
* FIRST, [ISO 27035 Practical value for CSIRT and SOCs ](https://www.first.org/resources/papers/conf2023/FIRSTCON23-TLPCLEAR-Benetis-ISO-27035-practical-value-for-CSIRTs-and-SOCs.pdf)
* SANS, [2024 SOC survey](https://swimlane.com/wp-content/uploads/SANS-SOC-Survey_2024.pdf)
* SOC 评估:
* CMM, [SOC-CMM](https://www.soc-cmm.com/)
* Rabobank CDC, [DeTTECT](https://github.com/rabobank-cdc/DeTTECT)
* SANS, [Continous purple teaming](https://www.sans.org/blog/continuous-purple-teaming-practical-approach-strengthening-offensive-capabilities)
## 针对 CERT/CSIRT
* CSIRT 构建:
* FIRST, [CERT-in-a-box](https://www.first.org/resources/guides/cert-in-a-box.zip)
* FIRST, [CSIRT Services Framework](https://www.first.org/standards/frameworks/csirts/csirt_services_framework_v2.1)
* 安全事件响应管理:
* ENISA, [Good practice for incident management](https://www.enisa.europa.eu/publications/good-practice-guide-for-incident-management)
* EE-ISAC [Incident Response whitepaper](https://www.ee-isac.eu/media/2023/05/EE-ISAC-Incident-Response-White-Paper.pdf)
* LinkedIn Pulse, [Security incident management according to ISO 27005](https://www.linkedin.com/pulse/security-incident-management-according-iso-27035-dipen-das-)
* Microsoft/EY/Edelman, [Incident response reference guide](https://www.linkedin.com/posts/the-cyber-security-hub_incident-response-reference-guide-activity-7033563558642642944-0zav?utm_source=share&utm_medium=member_desktop)
* Microsoft, [IR lessons on cloud ID compromise](https://www.microsoft.com/en-us/security/blog/2023/12/05/microsoft-incident-response-lessons-on-preventing-cloud-identity-compromise/?msockid=07788c7fcb0c689a2a5d98f6ca0169fb)
* 取证 (Forensics):
* NIST, [SP800-86, integration forensics techniques into IR](https://nvlpubs.nist.gov/nistpubs/legacy/sp/nistspecialpublication800-86.pdf)
* [ForensicsArtefacts](https://github.com/ForensicArtifacts/artifacts)
* 事件响应 Playbook:
* Kaspersky, [Incident Response Playbook: Dark Web Breaches](https://dfi.kaspersky.com/blog/dark-web-threats-response-guideline#form)
* CISA, [Incident Response playbooks](https://www.cisa.gov/sites/default/files/2024-08/Federal_Government_Cybersecurity_Incident_and_Vulnerability_Response_Playbooks_508C.pdf)
* SANS, [IR Mitigations tasks](https://board.flexibleir.com/b/VtdssIfCJ6Z2LYLED/1)
## 全球范围(SOC 和 CERT/CSIRT)
* 术语和概念:
* Shubham, [Security 360](https://twitter.com/Shubham_pen/status/1655192003448020993?s=20)
* Vilius Benetis, [CSIRT, SOC, ISAC and PSIRT definitions](https://www.linkedin.com/pulse/csirt-soc-isac-psirt-definitions-vilius-benetis)
* Thomas Roccia, [Visual Threat Intelligence](https://www.amazon.fr/Visual-Threat-Intelligence-Illustrated-Researchers/dp/B0C7JCF8XD)
* SentinelOne, [What is SecOps](https://www.sentinelone.com/cybersecurity-101/secops/?utm_content=white-paper&utm_medium=paid-display&utm_source=gdn-paid&utm_campaign=emea-t1-en-g-dsa&utm_term={demo-request}&utm_campaignid=19179764064&gclid=EAIaIQobChMItYzg5amQ_gIV6pBoCR1u0ACxEAAYAiAAEgJ1ofD_BwE)
* Purp1eW0lf, [Blue Team Notes](https://github.com/Purp1eW0lf/Blue-Team-Notes)
* PAN, [Security orchestration for dummies](https://www.paloaltonetworks.com/content/dam/pan/en_US/assets/pdf/cortex-xsoar/Security-Orchestration-For-Dummies-Demisto-Special-Edition.pdf)
* ThreatConnect, [SIRP / SOA / TIP benefits](https://threatconnect.com/blog/realizing-the-benefits-of-security-orchestration-automation-and-response-soar/)
* Medium, [Compromise assessment methodology](https://evrenbey.medium.com/compromise-assessment-methodology-820910efb6a4)
* SOC/CSIRT 流程:
* NIST, [SP800-61 rev3, incident handling guide](https://csrc.nist.gov/pubs/sp/800/61/r3/ipd)
* CSIRT 构建:
* ENISA, [How to set-up a CSIRT and SOC](https://www.enisa.europa.eu/publications/how-to-set-up-csirt-and-soc)
* 框架和资料:
* MITRE, [ATT&CK: Getting started](https://attack.mitre.org/resources/getting-started/)
* NIST, [Cybersecurity framework](https://www.nist.gov/cyberframework)
* FIRST, [CVSS v4 specs](https://www.first.org/cvss/v4-0/)
* CERT-EU, [CTI Framework](https://www.cert.europa.eu/publications/threat-intelligence/cyber-threat-intelligence-framework/)
* OASIS Open, [STIX](https://oasis-open.github.io/cti-documentation/stix/intro.html)
* FIRST, [TLP](https://www.first.org/tlp/)(情报共享和保密性),以及 [PAP](https://cert.ssi.gouv.fr/csirt/sharing-policy/)
* CIS, [18 critical security controls](https://www.cisecurity.org/controls/cis-controls-list)
* 安全能力映射:
* CTID, [Mappings explorer](https://center-for-threat-informed-defense.github.io/mappings-explorer/external/)
* 威胁矩阵:
* Push Security, [SaaS attack matrix](https://github.com/pushsecurity/saas-attacks#the-saas-attacks-matrix)
* Microsoft, [Threat Matrix for Azure Storage services](https://microsoft.github.io/Threat-matrix-for-storage-services/)
* MITRE, [Threat Matrix for AI-systems](https://github.com/mitre/advmlthreatmatrix/blob/master/pages/adversarial-ml-threat-matrix.md#adversarial-ml-threat-matrix)
* SOAR 解决方案:
* Swimlane, [Cyber Threat readiness report 2023](https://swimlane.com/wp-content/uploads/Cyber-Threat-Readiness-Report-2023.pdf);
* Gartner, [Market Guide for Security Orchestration, Automation and Response Solutions](https://fr.scribd.com/document/619736260/Gartner-Market-Guide-for-Security-Orchestration-Automation)
* NIS2:
* NIS2Directive: [NIS2 10 main requirements](https://nis2directive.eu/nis2-requirements/)
* LinkedIn: [How will NIS2 impact your organization?](https://www.linkedin.com/pulse/how-eu-directive-nis2-impact-your-organization-anders-fleinert-larsen%3FtrackingId=Vq3GCGlOTXe1u0dllhn9MA%253D%253D/?_l=fr_FR)
* CyberArk: [NIS2, how to address the security control gaps](https://event.on24.com/eventRegistration/console/apollox/mainEvent?simulive=y&eventid=4110743&sessionid=1&username=&partnerref=&format=fhvideo1&mobile=&flashsupportedmobiledevice=&helpcenter=&key=588150776CAE70D7F02ECF2848FF11FA&newConsole=true&nxChe=true&newTabCon=true&consoleEarEventConsole=false&text_language_id=en&playerwidth=748&playerheight=526&eventuserid=600843623&contenttype=A&mediametricsessionid=517006274&mediametricid=5797475&usercd=600843623&mode=launch)
* ENISA: [NIS2 technical implementation guidance](https://www.enisa.europa.eu/publications/nis2-technical-implementation-guidance)
* AI 模型与系统:
* ETSI, [Baseline Cyber Security Requirements for AI Models and Systems](https://www.etsi.org/deliver/etsi_en/304200_304299/304223/02.01.01_60/en_304223v020101p.pdf)
* NIST, [R 8596, Cybersecurity Framework Profile for Artificial Intelligence](https://csrc.nist.gov/pubs/ir/8596/iprd)
* Microsoft [Turning threat reports into detection insights with AI](https://www.microsoft.com/en-us/security/blog/2026/01/29/turning-threat-reports-detection-insights-ai/)
* 管理:
* Gartner, [Cybersecurity business value benchmark](https://emtemp.gcom.cloud/ngw/globalassets/en/doc/documents/775537-gartner-cybersecurity-business-value-benchmark-1st-generation.pdf)
* CrowdStrike, [State of SIEM market 2025](https://go.crowdstrike.com/rs/281-OBQ-266/images/Whitepaper2025StateofSIEMMarketCribl.pdf?version=0)
* Microsoft, ["While the initial trigger event was a Distributed Denial-of-Service (DDoS) attack... initial investigations suggest that an error in the implementation of our defences amplified the impact of the attack rather than mitigating it"](https://www.bbc.com/news/articles/c903e793w74o)
* SOP (标准操作程序):
* [Antimalware check SOP](https://github.com/cyb3rxp/awesome-soc/blob/main/sop_malware_critical_controls.md)
* [M365/Azure compromise asssessment SOP](https://github.com/cyb3rxp/awesome-soc/blob/main/sop_M365_compromise_assessment.md)
* [Web server compromise assessment SOP](https://github.com/cyb3rxp/awesome-soc/blob/main/sop_web_server_compromise_assessment.md)
# 基本概念
## 概念、工具、任务、攻击生命周期、红/蓝/紫队
### MITRE 参考:
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 5:优先考虑事件响应,第 101-123 页,
### 专用页面
参见:[SOC/CSIRT 基本和基础概念](https://github.com/cyb3rxp/awesome-soc/blob/main/soc_basics.md)。
## SOC 核心
### MITRE 参考:
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 8:利用工具支持分析师工作流,第 101-123 页,
### 从日志到警报:通用全局工作流
引用自[这篇文章](https://www.managedsentinel.com/siem-traditional-vs-cloud/):
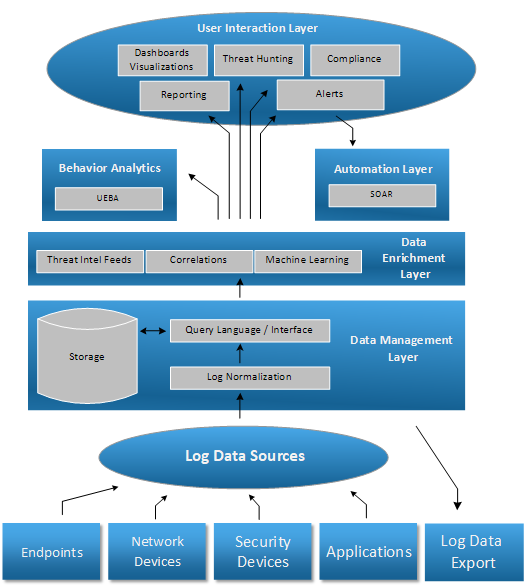
顺着箭头,我们从日志数据源进入数据管理层,然后到数据富化层(检测发生的地方),最后结束于行为分析或用户交互层(警报、威胁搜寻……)。所有这些都由自动化启用和支持。
### SOC 检测架构
基于 [CYRAIL 的论文图解](https://slideplayer.com/slide/15779727/),我稍作修改,这是一个检测架构(SIEM, SIRP, TIP 互连)和工作流的示例:
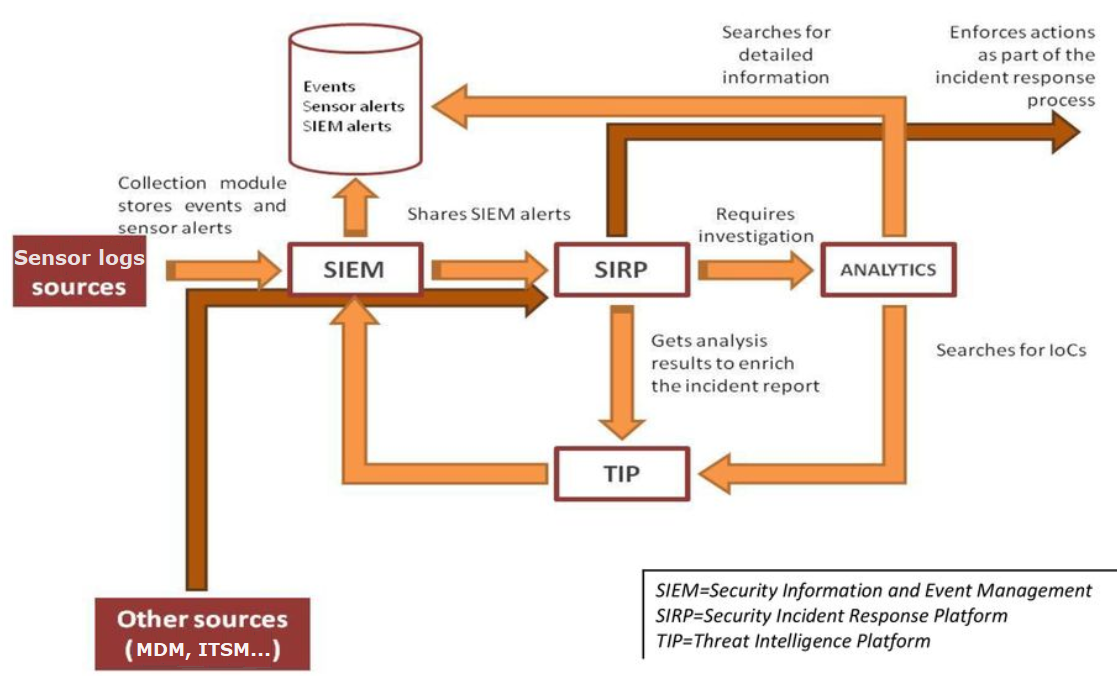
* 传感器日志源可能是:审计日志、安全传感器(反恶意软件、防火墙、NIDS、代理、EDR、NDR、CASB、身份威胁检测、蜜罐……)。
# 关键任务手段(工具/传感器)
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 7:选择并收集正确的数据,第 101-123 页,
## SOC/CSIRT 的关键工具
* **[SIEM](https://www.gartner.com/en/information-technology/glossary/security-information-and-event-management-siem)**:
* 参阅 [Gartner magic quadrant](https://www.bitdefender.com/en-us/business/campaign/2025-gartner-magic-quadrant-for-epp-the-only-visionary) 和 [Gartner critical SIEM capabilities](https://www.splunk.com/en_us/form/gartner-critical-capabilities-siem.html)
* 我的推荐:[Microsoft Azure Sentinel](https://azure.microsoft.com/en-us/products/microsoft-sentinel/#overview)、[Sekoia.io XDR](https://www.sekoia.io/en/sekoia-io-xdr/)、[Splunk](https://www.splunk.com)、[Graylog](https://graylog.org/)。
* **[SIRP](https://d3security.com/blog/whats-the-difference-between-soar-and-sao/)**:
* 例如:[IBM Resilient](https://www.ibm.com/qradar/security-qradar-soar?utm_content=SRCWW&p1=Search&p4=43700068028974608&p5=e&gclid=Cj0KCQjw9ZGYBhCEARIsAEUXITW2yUqAfNqWNeYXyENeUAoqLxV543LT0n2oYhYxEQ47Yjm7NfYTFHAaAtwpEALw_wcB&gclsrc=aw.ds)、[TheHive](https://thehive-project.org/)、[SwimLane](https://swimlane.com/)、[PAN Cortex XSOAR](https://www.paloaltonetworks.com/cortex/cortex-xsoar)
* 我的推荐:[TheHive](https://thehive-project.org/)、[PAN Cortex XSOAR](https://www.paloaltonetworks.com/cortex/cortex-xsoar)
* **[SOA](https://d3security.com/blog/whats-the-difference-between-soar-and-sao/)**:
* 我建议阅读 SoftwareReview 的 [SOAR Data quadrant awards](https://swimlane.com/resources/reports/soar-quadrant/)
* 例如:[IBM Resilient](https://www.ibm.com/qradar/security-qradar-soar?utm_content=SRCWW&p1=Search&p4=43700068028974608&p5=e&gclid=Cj0KCQjw9ZGYBhCEARIsAEUXITW2yUqAfNqWNeYXyENeUAoqLxV543LT0n2oYhYxEQ47Yjm7NfYTFHAaAtwpEALw_wcB&gclsrc=aw.ds)、[SwimLane](https://swimlane.com/)、[TheHive](https://thehive-project.org/)、[PAN Cortex XSOAR](https://www.paloaltonetworks.com/cortex/cortex-xsoar)、[Microsoft Logic Apps](https://learn.microsoft.com/en-us/azure/logic-apps/logic-apps-overview)
* 我的推荐:[SwimLane](https://swimlane.com/)、[TheHive](https://thehive-project.org/)、[PAN Cortex XSOAR](https://www.paloaltonetworks.com/cortex/cortex-xsoar)
* **[TIP](https://www.enisa.europa.eu/sites/default/files/publications/ENISA%20Report%20-%20How%20to%20setup%20CSIRT%20and%20SOC.pdf)**:
* 参阅 [威胁情报页面](https://github.com/cyb3rxp/awesome-soc/blob/main/threat_intelligence.md)
## SOC 的关键传感器
* **反恶意软件/杀毒软件**(你可能想看看[我的杀毒软件与 EDR 对比]([https://github.com/cyb3rxp/awesome-soc/blob/main/soc_basics.md#difference-between-antivirus-and-edr](https://github.com/cyb3rxp/awesome-soc/blob/main/soc_basics.md#what-are-the-differences-between-antivirus-and-edr)):
* 参阅 [Gartner magic quadrant](https://www.linkedin.com/posts/philipcao_gartnermq2025-epp-activity-7354304314963542016-1dzo/) 或 [Forrester Wave](https://explore.bitdefender.com/epp-nurture-2023_2/report-forrester-wave-endpoint-security-q4-2023?cid=emm%7Cb%7Chubspot%7Cnrt-epp-2023&utm_campaign=nurture-epp-2023&utm_medium=email&_hsmi=280555694&utm_content=280555694&utm_source=hs_automation)
* 我的推荐:[Microsoft Defender](https://docs.microsoft.com/en-us/microsoft-365/security/defender-endpoint/microsoft-defender-antivirus-windows?view=o365-worldwide)、[ESET Nod32](https://www.eset.com/int/business/solutions/learn-more-about-endpoint-protection/)、[BitDefender](https://www.bitdefender.fr/business/products/workstation-security.html)、[WithSecure Elements EPP](https://www.withsecure.com/fr/solutions/software-and-services/elements-endpoint-protection/computer)
* **[Endpoint Detection and Response](https://www.gartner.com/reviews/market/endpoint-detection-and-response-solutions)**:
* 参阅 [Gartner magic quadrant](https://www.sentinelone.com/lp/gartnermq/)、[MITRE ATT&CK Evaluations](https://evals.mitre.org/results/enterprise?view=cohort&evaluation=er7&result_type=DETECTION&scenarios=1,2) 和 [Forrester Wave](https://www.crowdstrike.com/resources/reports/crowdstrike-recognized-as-dominant-endpoint-solution-with-superior-vision/)
* 我的推荐:[SentinelOne](https://www.sentinelone.com/blog/active-edr-feature-spotlight/)、[Microsoft Defender for Endpoint](https://docs.microsoft.com/en-us/microsoft-365/security/defender-endpoint/microsoft-defender-endpoint?view=o365-worldwide)、[Harfanglab](https://harfanglab.io/)、[ESET XDR](https://www.eset.com/int/business/enterprise-protection-bundle/)、[WithSecure Elements EDR](https://www.withsecure.com/us-en/solutions/software-and-services/elements-endpoint-detection-and-response)、[CrowdStrike Falcon EDR](https://www.crowdstrike.com/wp-content/uploads/2022/03/crowdstrike-falcon-insight-data-sheet.pdf)、[Tanium](https://www.tanium.com/products/tanium-threat-response/)、[Wazuh](https://wazuh.com/)
* **[Secure Email Gateway](https://www.proofpoint.com/fr/threat-reference/email-gateway)** (SEG):
* 参阅 [Gartner reviews and ratings](https://www.gartner.com/reviews/market/email-security)
* 我的推荐:[Microsoft Defender for Office365](https://www.microsoft.com/en-us/security/business/siem-and-xdr/microsoft-defender-office-365)、[ProofPoint](https://www.proofpoint.com/fr/threat-reference/email-gateway)、[Mimecast](https://www.mimecast.com/products/email-security/secure-email-gateway/)、[WithSecure Elements Collaboration Protection](https://www.withsecure.com/en/solutions/software-and-services/elements-collaboration-protection)
* **[Secure Web Gateway](https://www.gartner.com/en/information-technology/glossary/secure-web-gateway)** (SWG) / Security Service Edge:
* 参阅 [Forrester wave for SSE](https://www.netskope.com/wp-content/uploads/2024/03/forrester-wave-sse-solutions-diagram-1340x1640-1.png)
* 我的推荐:[BlueCoat Edge SWG](https://www.broadcom.com/products/cybersecurity/network/web-protection/proxy-sg-and-advanced-secure-gateway)、[CISCO SASE](https://www.cisco.com/site/us/en/solutions/secure-access-service-edge-sase/index.html)、[Zscaler Cloud proxy](https://www.zscaler.com/resources/security-terms-glossary/what-is-cloud-proxy)、[Netskope](https://www.netskope.com/security-defined/what-is-casb)。
* **[Identity Threat Detection and Response](https://www.semperis.com/blog/evaluating-identity-threat-detection-response-solutions/)** **(ITDR)** 用于身份和 AD/AAD 安全(审计日志或特定监控解决方案):
* 我的推荐:[Semperis Directory Services Protector](https://www.semperis.com/active-directory-security/)
* 用于 AD 和 Enta ID 的一次性安全评估,我推荐:[Semperis Purple Knight](https://www.semperis.com/purple-knight/) 或 [PingCastle](https://www.pingcastle.com/download/)
* **EASM**: 外部资产安全监控 / 外部攻击面管理:
* 我的推荐:[Intrinsec](https://www.intrinsec.com/en/easm-external-attack-surface-management/)、[Mandiant](https://cloud.google.com/security/products/attack-surface-management)、[Qualys EASM](https://www.qualys.com/apps/external-attack-surface-management/)
* 用于安全检查:
* 网站的快速安全评估:[ImmuniWeb](https://www.immuniweb.com/websec/)
* AWS/Azure/GCP 安全评估(社区工具):[ScootSuite](https://github.com/nccgroup/ScoutSuite)
* **CASB**: [Cloud Access Security Broker](https://www.gartner.com/en/information-technology/glossary/cloud-access-security-brokers-casbs),如果公司的 IT 环境使用大量外部服务,如 SaaS/IaaS:
* 参阅 [Gartner magic quadrant](https://www.netskope.com/wp-content/uploads/2025/05/2025-05-SSE-MQ-site-1040x1094-1-768x808.png)
* 我的推荐:[Microsoft MCAS](https://www.microsoft.com/en-us/security/business/siem-and-xdr/microsoft-defender-cloud-apps)、[Zscaler](https://info.zscaler.com/resources-white-papers-data-protection-challenges?_bt=534426399999&_bk=%2Bzscaler%20%2Bcasb&_bm=b&_bn=g&_bg=121807608181&utm_source=google&utm_medium=cpc&utm_campaign=google-ads-na&gclid=CjwKCAjwu5yYBhAjEiwAKXk_eKLlKaMfJ-oGYItPTHguAmCA_b9WP0zNZgLPqGKjfC19IGmQFFG_9RoCgJAQAvD_BwE)、[Netskope](https://www.netskope.com/security-defined/what-is-casb)。
* **移动威胁防御 (Mobile Threat Defense):**
* 参阅[最新的 Forrester Wave 关于 MTD 的报告](https://reprint.forrester.com/reports/the-forrester-wave-tm-mobile-threat-defense-solutions-q3-2024-fd48faab/index.html)
* 我的推荐:[Zimperium MTD](https://www.zimperium.com/mtd/)
## CSIRT 的关键工具
* **入侵评估工具 (Compromise assessment tools)**:
* 我的推荐:
* 付费:
* [Thor Cloud lite](https://www.nextron-systems.com/2023/10/30/introducing-thor-cloud-lite-seamless-on-demand-security-scanning-made-easy/);
* [WithSecure Elements EDR](https://www.withsecure.com/us-en/solutions/software-and-services/elements-endpoint-detection-and-response);
* 免费:
* 针对 Linux:
* WithSecure [Cat-Scale](https://labs.withsecure.com/tools/cat-scale-linux-incident-response-collection);
* [UAC](https://github.com/tclahr/uac);
* 针对 Windows:
* 简单但高效的 ESET [Sysinspector](https://www.eset.com/int/support/sysinspector/);
* [Velociraptor](https://docs.velociraptor.app/docs/);
* [Powershell Hunter](https://github.com/MHaggis/PowerShell-Hunter/tree/main)
* [DFIR-ORC](https://github.com/dfir-orc);
* [Sysmon](https://learn.microsoft.com/fr-fr/sysinternals/downloads/sysmon):
* 安装它(如果尚未安装,让其运行几小时/几天),使用 [Olaf Hartong 的配置](https://github.com/olafhartong/sysmon-modular/blob/master/sysmonconfig.xml);
* 然后使用常规 SIEM 或 [Zircolite](https://github.com/wagga40/Zircolite) 调查其日志
* 针对 AD:
* 简单但高效的 [ADRecon](https://github.com/tomwechsler/Active_Directory_Advanced_Threat_Hunting/blob/main/Different_hunting_methods/In-depth_investigation_active_directory.md);
* [ADTrapper](https://github.com/MHaggis/ADTrapper);
* [Semperis Purple Knight](https://www.semperis.com/purple-knight/);
* [BloodHound Community](https://github.com/SpecterOps/BloodHound)
* 针对 MS Entra ID & M365:
* [CrowdStrike Reporting Tool for Azure](https://github.com/CrowdStrike/CRT)
* [Semperis Purple Knight](https://www.semperis.com/purple-knight/);
* [365Inspect](https://github.com/soteria-security/365Inspect);
* [Azure AD Incident Response Powershell](https://github.com/reprise99/kql-for-dfir/tree/main/Azure%20Active%20Directory)
* 针对 Azure / GCP / AWS:
* [ScootSuite](https://github.com/nccgroup/ScoutSuite)
* **按需易失性数据收集工具**:
* 我的推荐:[FastIR](https://github.com/OWNsecurity/fastir_artifacts)、[VARC](https://github.com/cado-security/varc)、[FireEye Redline](https://fireeye.market/apps/211364)、[DFIR-ORC](https://github.com/dfir-orc);
* **可执行远程操作的工具(即:远程 shell 或等效工具)**:
* 我的推荐:[CIMSweep](https://github.com/mattifestation/CimSweep)、[Velociraptor](https://docs.velociraptor.app/docs/deployment/)、[CrowdStrike Falcon Toolkit](https://github.com/CrowdStrike/Falcon-Toolkit) 但它依赖于 CrowdStrike EDR,[GRR](https://github.com/google/grr) 但它需要安装代理。
* **按需沙箱 (On-demand sandbox)**:
* 我推荐的在线沙箱:[Joe's sandbox](https://www.joesandbox.com/#windows)、[Hybrid Analysis](https://www.hybrid-analysis.com/) 等;
* 我推荐的本地沙箱:
* Windows 10 原生沙箱,带[自动化](https://megamorf.gitlab.io/2020/07/19/automating-the-windows-sandbox/)。
* Linux/Docker : [CISA Thorium](https://github.com/cisagov/thorium?tab=readme-ov-file)
* **取证和逆向工程工具套件**:
* 我的推荐:[SIFT Workstation](https://www.sans.org/tools/sift-workstation/) 或 [Tsurugi](https://tsurugi-linux.org/);
* 我推荐的 Windows 下逆向工程和恶意软件分析工具:[FireEye Flare-VM](https://github.com/mandiant/flare-vm);
* 我推荐的 Linux 下纯恶意软件分析工具:[Remnux](https://remnux.org/)。
* **事件管理跟踪器**:
* 我的推荐:[Timesketch](https://timesketch.org/)、[DFIR IRIS](https://dfir-iris.org/)
* **扫描器**:
* IOC 扫描器:
* 我的推荐:[Loki](https://github.com/Neo23x0/Loki)、[DFIR-ORC](https://github.com/dfir-orc)
* 针对智能手机:[Tiny Check](https://tiny-check.com/#/)
* 用于扫描器的 IOC 仓库:
* Google [CTI's repo](https://github.com/chronicle/GCTI/tree/main/YARA): 针对 Cobalt Strike 和其他的 Yara 规则。
* [Yara-rules GitHub repo](https://github.com/Yara-Rules/rules): 多种 Yara 规则类型。
* Spectre [Yara rules repo](https://github.com/phbiohazard/Yara)
* Neo23x0 [Community Yara rules](https://github.com/Neo23x0/signature-base)
* 以及这里列出的,[Awesome threat intel](https://github.com/hslatman/awesome-threat-intelligence)
* 离线反恶意软件扫描器:
* 我的推荐:[Windows Defender Offline](https://support.microsoft.com/en-us/windows/help-protect-my-pc-with-microsoft-defender-offline-9306d528-64bf-4668-5b80-ff533f183d6c)
* **具有检测能力的日志分析器**:
* 我的推荐:
* 付费:[Sekoia XDR](https://www.sekoia.io/en/product/xdr/),
* 社区提供/免费:[Zircolite](https://github.com/wagga40/Zircolite)、[DeepBlue](https://github.com/sans-blue-team/DeepBlueCLI)、[CrowdSec](https://doc.crowdsec.net/docs/user_guides/replay_mode)
## SOC 和 CERT/CSIRT 的其他关键工具
* **安全秘密共享**:
* [OneTimeSecret](https://onetimesecret.com/)
* **数据分析工具**:
* 我的推荐:[CyberChef](https://github.com/NextronSystems/CyberChef)、[Notepad++](https://notepad-plus-plus.org/downloads/)
* **管理工具**:
* 我推荐的(免费)管理工具:[Azure AD Internals suite](https://aadinternals.com/)、[SysInternals Suite](https://learn.microsoft.com/fr-fr/sysinternals/downloads/sysinternals-suite)、[MRemoteNG](https://mremoteng.org/)
* 我推荐的(免费)远程部署工具:[EMCO Remote installer](https://emcosoftware.com/remote-installer)
* **内部工单系统**(注意:**不是** SIRP,不用于事件响应!):
* 我的推荐:[GitLab](https://github.com/diffblue/gitlab/blob/master/doc/operations/incident_management/incidents.md)
* **知识共享和管理工具**:
* 我的推荐:[Microsoft SharePoint](https://www.microsoft.com/en-us/microsoft-365/sharepoint/collaboration)、Wiki(选择你喜欢的,或者[将 GitLab 用作 Wiki](https://docs.gitlab.com/ee/user/project/wiki/))。
* **用于 OSINT 搜索和 IOC 的可视化工具**:
* 我的推荐:[OSINTracker](https://app.osintracker.com/)
* **安全文件共享服务**:
* 我的推荐:[Chapril](https://drop.chapril.org/)
# IT/安全监控
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 6:利用网络威胁情报照亮对手,第 101-123 页,
## 推荐来源
* RSS:
* CISA [alerts](https://www.us-cert.gov/ncas/alerts.xml)
* [Ransomware live feeds](https://ransomware.live/rss.xml)
* CERT EU [Security advisories](https://cert.europa.eu/publications/security-advisories-rss)
* NIST [news](https://www.nist.gov/news-events/cybersecurity/rss.xml)
* Google [Online Security blog](http://feeds.feedburner.com/GoogleOnlineSecurityBlog)
* TheRecord [Recorded Future News](https://therecord.media/feed)
* [TheHacker news](http://feeds.feedburner.com/TheHackersNews?format=xml)
* Dark Reading [All stories](https://www.darkreading.com/rss.xml)
* Medium [CyberSecurity](https://medium.com/feed/tag/cybersecurity)
* [Krebs on security](https://krebsonsecurity.com/feed/)
* [Graham Cluley's blog](https://grahamcluley.com/feed/)
* [Schneier on Security](http://feeds.feedburner.com/schneier/excerpts)
* ZDI [Upcoming advisories](https://www.zerodayinitiative.com/rss/upcoming/)
* ESET [We Live Security](http://feeds.feedburner.com/eset/blog?format=xml)
* [CrowdStrike](https://www.crowdstrike.com/blog/feed)
* [PacketStorm Security](https://packetstorm.news/rss/news)
* Kaspersky [SecureList](https://securelist.com/feed/)
* [ProofPoint](https://www.proofpoint.com/us/rss.xml)
* 已知被利用的漏洞 + 0day:
* [CISA catalog](https://www.cisa.gov/known-exploited-vulnerabilities-catalog)
* [Top 0days "in the wild"](https://docs.google.com/spreadsheets/d/1lkNJ0uQwbeC1ZTRrxdtuPLCIl7mlUreoKfSIgajnSyY/edit?gid=1331951416#gid=1331951416)
* LinkedIn / Twitter:
* 例如:[LinkedIn Information Security Community group](https://www.linkedin.com/groups/38412/)
* 政府 CERT,行业相关的 CERT...
* 例如:[CERT-FR](https://www.cert.ssi.gouv.fr/avis/),
* [CERT-US](https://www.cisa.gov/uscert/ncas/alerts)
* [ISC] [Diaries](https://isc.sans.edu/diary/0)
* ENISA [Threat landscape 2025](https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025)
* SIEM 规则发布:
* [Sigma HQ (detection rules)](https://github.com/SigmaHQ/sigma/tree/master/rules)
* [Splunk Security content (free detection rules for Splunk)](https://research.splunk.com/)
* [SOC Prime](https://tdm.socprime.com/)
* [Michel De Crevoisier's Git](https://github.com/mdecrevoisier/SIGMA-detection-rules)
* 安全厂商的威胁态势/网络安全事件报告:
* Microsoft [Digital Defense Report](https://www.microsoft.com/en-us/corporate-responsibility/cybersecurity/)
* ESET [Threat report](https://www.welivesecurity.com/en/eset-research/)
* Verizon [Databreach reports](https://www.verizon.com/business/resources/reports/dbir/)
* 新闻通讯:
* 例如:[TheRecord.media](https://therecord.media/subscribe)、[Intrinsec Threat Landscape](https://intrinsec.us13.list-manage.com/subscribe?u=403249ad144b732517b9fca94&id=041976f275) & [LinkedIn posts](https://www.linkedin.com/company/intrinsec/?lipi=urn%3Ali%3Apage%3Ad_flagship3_search_srp_all%3BAyS%2B%2F6ysQ5G%2BBlZQjTWrKg%3D%3D)
* 播客:
* WithSecure [Xposed](https://www.withsecure.com/en/expertise/podcasts)
* 其他有趣的网站:
* 例如:[ISC](https://isc.sans.edu/)、[ENISA](https://www.enisa.europa.eu/publications)、[ThreatPost](https://threatpost.com/) ...
# SOAR
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 8:利用工具支持分析师工作流,第 101-123 页,
## 专用页面
参见 [SOAR 页面](https://github.com/cyb3rxp/awesome-soc/blob/main/soar.md)
# 检测工程
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 1:知道你在保护什么以及为什么,第 101-123 页,
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 7:选择并收集正确的数据,第 101-123 页,
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 11:通过扩展 SOC 功能来扩大规模,第 101-123 页,
## 专用页面
参见 [检测工程页面](https://github.com/cyb3rxp/awesome-soc/blob/main/detection_engineering.md)。
# 威胁情报
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 6:利用网络威胁情报照亮对手,第 101-123 页,
## 专用页面
参见 [威胁情报页面](https://github.com/cyb3rxp/awesome-soc/blob/main/threat_intelligence.md)。
# 管理
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 1:知道你在保护什么以及为什么,第 101-123 页
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 3:建立符合组织需求的 SOC 结构,第 101-123 页
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 9:清晰沟通,经常协作,慷慨分享,第 101-123 页
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 10:衡量绩效以提升绩效,第 101-123 页
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 11:通过扩展 SOC 功能来扩大规模,第 101-123 页
## 专用页面
参见 [管理页面](https://github.com/cyb3rxp/awesome-soc/blob/main/management.md)。
# 人力资源与培训
## MITRE 参考
* [11 strategies for a world-class SOC](https://github.com/cyb3rxp/awesome-soc/blob/main/11-strategies-of-a-world-class-cybersecurity-operations-center.pdf),策略 4:雇佣并培养优质员工,第 101-123 页
## 专用页面
参见 [人力资源与培训页面](https://github.com/cyb3rxp/awesome-soc/blob/main/hr_training.md)。
# SOC 的 IT 架构
## 拥有单一且集中的平台('单一控制台')
根据 [NCSC 网站](https://www.ncsc.gov.uk/collection/building-a-security-operations-centre/detection/detection-practices#section_2):
## 将 SOC 与受监控环境(尽可能)断开
目标是防止攻击者从受损的监控区域横向移动到 SOC/CSIRT 工作区域。
### 安全区域 (Enclave):
* 实施 SOC 安全区域(通过网络隔离),正如 MITRE 论文图解所示:

* 只允许日志收集器和 WEF 向 SOC/CSIRT 安全区域发送数据。只要可能,SOC 工具应从受监控环境中拉取数据,而不是相反;
* 在 SOC 安全区域之上,至少实施[二级网络分段](https://github.com/sergiomarotco/Network-segmentation-cheat-sheet#level-2-of-network-segmentation-adoption-of-basic-security-practices);
SOC 的资产应属于单独的[受限 AD 林](https://learn.microsoft.com/en-us/windows-server/identity/ad-ds/plan/forest-design-models ),以允许与其余受监控 AD 域进行 AD 隔离。
### 终端加固:
* SOC/CSIRT 的终端应按照相关指南进行加固;
* 我的推荐:[CIS benchmarks](https://www.cisecurity.org/cis-benchmarks/)、[Microsoft Security Compliance Toolkit](https://www.microsoft.com/en-us/download/details.aspx?id=55319)
# 进阶学习
## 必读
* MITRE, [11 strategies for a world-class SOC (remaining of PDF)](https://www.mitre.org/publications/technical-papers/11-strategies-world-class-cybersecurity-operations-center)
* CISA, [Cyber Defense Incident Responder role](https://www.cisa.gov/cyber-defense-incident-responder)
* Kaspersky, [AV / EP / EPP / EDR / XDR](https://usa.kaspersky.com/blog/introducing-kedr-optimum/27062/?reseller=usa_regular-sm_acq_ona_smm__onl_b2c_lii_post_sm-team______&utm_source=linkedin&utm_medium=social&utm_campaign=us_regular-sm_en0177&utm_content=sm-post&utm_term=us_linkedin_organic_pmgk1776sk4g1qp)
* Wavestone, [Security bastion (PAM) and Active Directory tiering mode: how to reconcile the two paradigms?](https://www.riskinsight-wavestone.com/en/2022/10/security-bastion-pam-and-active-directory-tiering-mode-how-to-reconcile-the-two-paradigms/)
* MalAPI, [list of Windows API and their potential use in offensive security](https://malapi.io/)
* FireEye, [OpenIOC format](https://github.com/fireeye/OpenIOC_1.1/blob/master/IOC_Terms_Defs.md)
* Herman Slatman, [Awesome Threat Intel](https://github.com/hslatman/awesome-threat-intelligence)
* Microsoft, [SOC/IR hierarchy of needs](https://github.com/swannman/ircapabilities)
* Betaalvereniging, [TaHiTI (threat hunting methodology)](https://www.betaalvereniging.nl/wp-content/uploads/TaHiTI-Threat-Hunting-Methodology-whitepaper.pdf)
* ANSSI (FR), [EBIOS RM methodology](https://messervices.cyber.gouv.fr/guides/en-ebios-risk-manager-method)
* GMU, [Improving Social Maturity of Cybersecurity Incident Response Teams](https://web.archive.org/web/20250816141217/https://edu.anarcho-copy.org/Against%20Security%20-%20Self%20Security/GMU_Cybersecurity_Incident_Response_Team_social_maturity_handbook.pdf)
* J0hnbX, [RedTeam resources](https://archive.org/details/github.com-J0hnbX-RedTeam-Resources_-_2022-02-20_01-12-12)
* Fabacab, [Awesome CyberSecurity BlueTeam](https://github.com/fabacab/awesome-cybersecurity-blueteam)
* Microsoft, [Windows 10 and Windows Server 2016 security auditing and monitoring reference](https://www.microsoft.com/en-us/download/details.aspx?id=52630).
* iDNA, [how to mange FP in a SOC?](https://www.idna.fr/2018/11/06/comment-gerer-les-faux-positifs-dans-un-soc/),法文
* Soufiane Tahiri, [Playbook for ransomware incident response](https://github.com/soufianetahiri/ransomware_Incident_Response_FR),法文
* PwnDefend, [AD post-compromise checklist](https://www.pwndefend.com/2021/09/15/post-compromise-active-directory-checklist/)
* Gartner, [Market guide for NDR](https://stellarcyber.ai/learn/gartner-ndr/)
* Rawsec, [Resources inventory](https://inventory.raw.pm/resources.html)
* Quest, [Best practices for AD disaster recovery](https://www.quest.com/webcast-ondemandt/best-practices-for-active-directory-disaster-recovery/?param=L4qcdiH1R46lWbN5Jxs%2fNN0Qky57LDYQTnsyaoWVqKYZTocd3n1RpFTyQegqps0MbW7yx4UWSKyVRVyz%2bwo0XRB2%2fXpFzrMZeOA%2fne%2f4Fm3oH5YJAnFCP%2fnRqs9Rq%2fRD0VTXvdBaojCx5J46htyILvanM5FhOVa7MCGDGYBcq6925YtpmANy9OA1%2fjdtlDrp)
* Microsoft, [Isolate Tier 0 assets with group policy](https://techcommunity.microsoft.com/t5/core-infrastructure-and-security/initially-isolate-tier-0-assets-with-group-policy-to-start/ba-p/1184934)
* Securenvoy, [How to be compliant with NIS2?](https://securenvoy.com/blog/how-to-be-compliant-with-new-nis-directive/)
* CyberVigilance, [Mitre Engenuity Evaluations 2022 review](https://www.cybervigilance.uk/post/2022-mitre-att-ck-engenuity-results)
* [Wazuh at the heart of a SOC architecture for public/critical infrastructures](https://medium.com/@ludovic.doamba/wazuh-at-the-heart-of-sovereign-soc-architecture-for-public-and-critical-infrastructures-f0d18562d14b)
* ENISA, [List of trusted cybersecurity services providers](https://www.enisa.europa.eu/sites/default/files/2025-07/EU%20Cybersecurity%20Reserve%20companies.pdf)
## 值得一读
* NIST, [SP800-53 rev5 (Security and Privacy Controls for Information Systems and Organizations)](https://csrc.nist.gov/publications/detail/sp/800-53/rev-5/final)
* Amazon, [AWS Security Fundamentals](https://aws.amazon.com/fr/training/digital/aws-security-fundamentals/)
* Microsoft, [PAW Microsoft](https://docs.microsoft.com/en-us/security/compass/privileged-access-devices)
* CIS, [Business Impact Assessment](https://bia.cisecurity.org/)
* Abdessabour Boukari, [RACI template (in French)](https://github.com/cyberabdou/SOC/blob/77f01ba82c22cb11028cde4a862ae0bea4258378/SOC%20RACI.xlsx)
* Sekoia, [What is XDR?](https://www.sekoia.io/en/glossary/what-is-xdr/)
* Elastic, [BEATS agents](https://www.elastic.co/beats/)
* [V1D1AN's Drawing: architecture of detection](https://github.com/V1D1AN/S1EM/wiki/Architecture-guide#the-architecture-of-detection),
* [RFC2350](https://www.cert.ssi.gouv.fr/uploads/CERT-FR_RFC2350_EN.pdf) (CERT 描述)
* [Awesome Security Resources](https://github.com/Johnson90512/Awesome-Security-Resources)
* [Incident Response & Computer Forensics, 3rd ed](https://www.google.fr/books/edition/Incident_Response_Computer_Forensics_Thi/LuWINQEACAAJ?hl=fr)
* [GDPR cybersecurity implications (in French)](https://atelier-rgpd.cnil.fr/)
* [SANS SOC survey 2022](https://www.splunk.com/en_us/pdfs/resources/whitepaper/sans-soc-survey-2022.pdf)
* Soufiane Tahiri, [Digital Forensocs Incident Response Git](https://github.com/soufianetahiri/Digital-Forensics-Incident-Response)
* Austin Songer, [Incident playbook](https://github.com/austinsonger/Incident-Playbook)
* CISA, [Cybersecurity incident and vulnerability response playbooks](https://www.cisa.gov/sites/default/files/publications/Federal_Government_Cybersecurity_Incident_and_Vulnerability_Response_Playbooks_508C.pdf)
* Reprise99, [Microsoft Sentinel queries](https://github.com/reprise99/Sentinel-Queries)
* MyFaberSecurity, [MS Sentinel architecture and recommendations for MSSP](https://myfabersecurity.com/2023/03/31/sentinel-poc-architecture-and-recommendations-for-mssps-part-1/)
* Gartner, [PAM Magic Quadrant reprint](https://www.beyondtrust.com/resources/gartner-magic-quadrant-for-pam)
* Rawsec, [Tools inventory](https://inventory.raw.pm/tools.html)
* Microsoft, [command line reference](https://cmd.ms/)
* Microsoft, [Sentinel data collection scenarios](https://learn.microsoft.com/en-us/azure/sentinel/connect-cef-ama#how-collection-works-with-the-common-event-format-cef-via-ama-connector)
* SOC CMM, [SOCTOM](https://soc-cmm.com/img/upload/files/54-soctom-whitepaper.pdf)
* [PTES](http://www.pentest-standard.org/index.php/Main_Page)
* OWASP, [WSTG](https://owasp.org/www-project-web-security-testing-guide/)
* BitDefender, [Analyzing MITRE ATT&CK evaluations 2023](https://explore.bitdefender.com/epp-nurture-2023_2/blog-mitre-attck-evaluations-2023?cid=emm%7Cb%7Chubspot%7Cnrt-epp-2023&utm_campaign=nurture-epp-2023&utm_medium=email&_hsmi=280552612&utm_content=280552612&utm_source=hs_automation)
* Microsoft, [Licensing maps, eg. for Defender](https://m365maps.com/) & [Modern work plan comparison SMB](https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/final/en-us/microsoft-brand/documents/modern-work-plan-comparison-smb5.pdf)
* CyberFlooD [SwitchToOpen](https://github.com/CyberFlooD/SwitchToOpen)
## SOC 传感器,锦上添花
* **暗网监控**(数据泄露等)
* 我的推荐:[AIL Framework](https://github.com/CIRCL/AIL-framework)
* 对于付费 SaaS 解决方案,我建议看看这个[前十名](https://expertinsights.com/insights/the-top-dark-web-monitoring-solutions/)
* **欺骗技术:**
* 我的推荐:实施 [AD decoy acounts](https://medium.com/securonix-tech-blog/detecting-ldap-enumeration-and-bloodhound-s-sharphound-collector-using-active-directory-decoys-dfc840f2f644) 和 [AD DNS canary](https://www.protect.airbus.com/blog/active-directory-a-canary-under-your-hat/)
* 面向互联网的网站/应用的 WAF:
* 我的推荐:
* FOSS: [Crowdsec WAF](https://www.crowdsec.net/solutions/application-security)、[Bunkerweb](https://github.com/bunkerity/bunkerweb?tab=readme-ov-file=)
* 付费但价格合理:[CloudFlare](https://www.cloudflare.com/plans/)
* MDM:
* 我的推荐:[Microsoft Intune](https://docs.microsoft.com/en-us/mem/intune/fundamentals/what-is-intune)
* (全功能)蜜罐:
* 我的推荐:[Canary.tools](https://canary.tools/)
* 或者,看看 [Awesome honeypots Git](https://github.com/paralax/awesome-honeypots)
* 钓鱼和品牌侵权保护(域名):
* 我的推荐:[PhishLabs](https://www.phishlabs.com/)、[Netcraft](https://www.netcraft.com/cybercrime/fraud-detection/)
* NIDS:
* 我的推荐:[Crowdsec](https://www.crowdsec.net/product/crowdsec-security-engine)
* NDR:
* 我的推荐:[Gatewatcher](https://www.gatewatcher.com/en/our-solutions/trackwatch/)
* 参阅 [Gartner MAgic Quadrant for NDR](https://www.gatewatcher.com/en/resource/2025-gartner-magic-quadrant-for-network-detection-and-response/)
* DLP:
* 参阅 [Gartner reviews and ratings](https://www.gartner.com/reviews/market/data-loss-prevention)
* OT (工业) NIDS:
* 我的推荐:[Nozomi Guardian](https://www.nozominetworks.com/products/guardian/)
* 网络 TAP:
* 我的推荐:[Gigamon](https://www.gigamon.com/products/access-traffic/network-taps.html)
* 移动网络安全 (2G/3G):
* 我的推荐:Dust Mobile.
## 加固 SOC/CSIRT 环境
* 在 SOC 工作站、服务器和使用的 IT 服务上(如果可能)实施加固措施。
* 例如:[CIS](https://www.cisecurity.org/)、[Microsoft Security Compliance Toolkit](https://www.microsoft.com/en-us/download/details.aspx?id=55319)
* 将 SOC 资产放在单独的 AD 林中,因为[林是 AD 安全边界](https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/gathering-information-about-your-active-directory-deployment),以便在全球企业 IT 遭到入侵时进行隔离
* 为 SOC 资产和资源制定/提供灾难恢复计划。
* 实施管理堡垒和孤岛来管理 SOC 环境(设备、服务器、终端):
* 我的建议:将 SOC 环境视为由 **Tier 1** 管理,如果可能的话,使用专用的管理堡垒。这是来自 Wavestone 文章的通用图解(见必读参考资料): 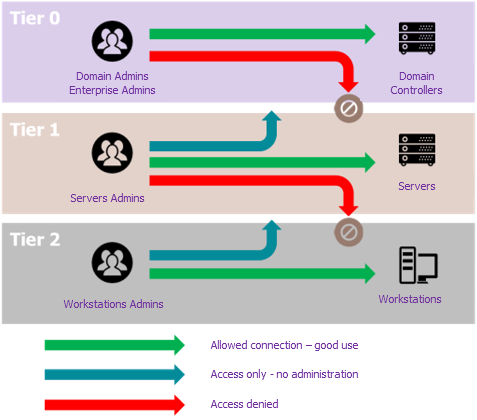
* 推荐的技术选择:[Wallix PAM](https://www.wallix.com/privileged-access-management/)
* 实施[三级网络分段](https://github.com/sergiomarotco/Network-segmentation-cheat-sheet#level-3-of-network-segmentation-high-adoption-of-security-practices)
* 你可能希望为事件响应或特定样本分析使用一次性机器(虚拟机)。以下是我的推荐:
* [Microsoft Developer virtual machines](https://developer.microsoft.com/en-us/windows/downloads/virtual-machines/);
* Windows 11 [clean-up script](https://github.com/simeononsecurity/Windows-Optimize-Harden-Debloat);
* Windows 11 [hardening tool](https://apps.microsoft.com/detail/9p7ggfl7dx57?hl=en-US&gl=US)
* 如果需要,[Flare-VM](https://github.com/mandiant/flare-vm) 框架用于自动化分析师工作站上的安全工具安装;
# 附录
## 许可证
[CC-BY-SA](https://en.wikipedia.org/wiki/Creative_Commons_license)
## 特别感谢
Yann F., Wojtek S., Nicolas R., Clément G., Alexandre C., Jean B., Frédérique B., Pierre d'H., Julien C., Hamdi C., Fabien L., Michel de C., Gilles B., Olivier R., Jean-François L., Fabrice M., Pascal R., Florian S., Maxime P., Pascal L., Jérémy d'A., Olivier C. x2, David G., Guillaume D., Patrick C., Lesley K., Gérald G., Jean-Baptiste V., Antoine C. ...
标签:Awesome 列表, CSIRT, SOAR, 企业安全, 威胁情报, 子域枚举, 安全建设, 安全架构, 安全管理, 安全运营中心, 库, 应急响应, 开发者工具, 文档资源, 最佳实践, 网络安全, 网络映射, 网络资产管理, 计算机应急响应组, 运维指南, 隐私保护