MistanKh/MistanKh
GitHub: MistanKh/MistanKh
一个展示个人安全技能与自动化 CVE 情报聚合的静态组合集,解决实时威胁信息整合与可视化的痛点。
Stars: 0 | Forks: 0
 # Mistan Khomdram
[](https://tryhackme.com/p/Mistan)
[](https://mistankh.github.io/MyPortfolio2)
[](https://tryhackme.com/p/Mistan)
[](https://app.hackthebox.com/profile/1709663)
[](https://www.linkedin.com/in/mistan-khomdram-ab056315a/)
# Mistan Khomdram
[](https://tryhackme.com/p/Mistan)
[](https://mistankh.github.io/MyPortfolio2)
[](https://tryhackme.com/p/Mistan)
[](https://app.hackthebox.com/profile/1709663)
[](https://www.linkedin.com/in/mistan-khomdram-ab056315a/)
[](https://github.com/MistanKh/MyPortfolio2/actions/workflows/deploy.yml)
[](https://github.com/MistanKh/MyPortfolio2/actions/workflows/cve-update.yml)
[](https://github.com/MistanKh/MyPortfolio2/actions/workflows/lighthouse.yml)
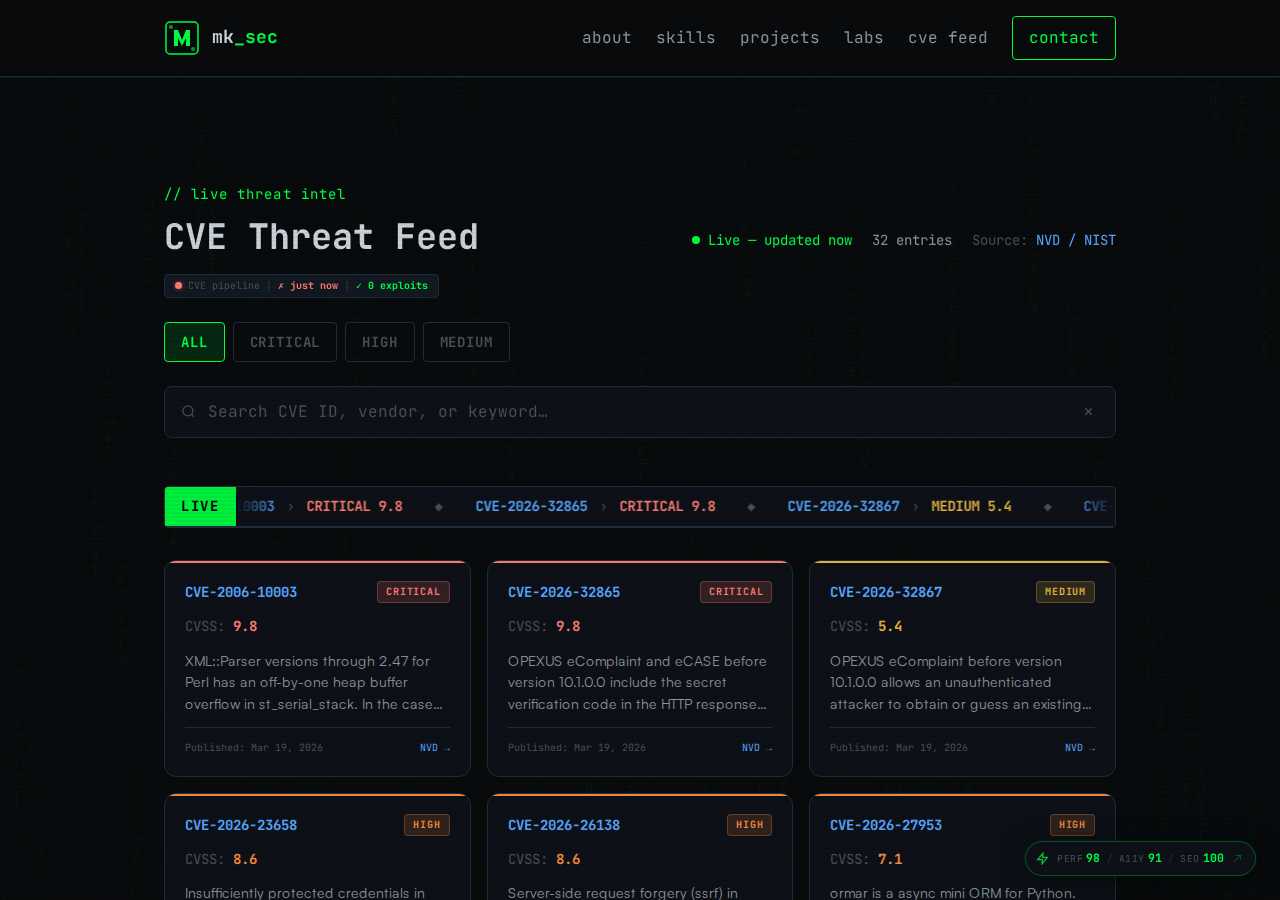
### ⚡ 实时 CVE 威胁源
[](https://mistankh.github.io/MyPortfolio2/#cve-feed)
该组合集从 [NVD API v2](https://nvd.nist.gov/developers/vulnerabilities) 获取 **实时 CRITICAL/HIGH CVE**:
- 实时关键词 / 供应商 / CVE-ID 搜索
- 每个 CVE 详情模态框(CVSS 指标、CWE、受影响产品、引用)
- **⚠ 漏洞利用** 徽章,交叉引用 [ExploitDB](https://www.exploit-db.com)(通过 GitHub Actions 每日刷新)
- 备用数据集每天 06:00 UTC 自动更新 — 从不陈旧
## 🛠️ 技能与工具












## 🏆 认证
| 认证 | 颁发机构 | 验证 |
|------|----------|------|
| eJPT — 初级渗透测试员 | eLearnSecurity | [🔗 验证](https://my.ine.com/certificate/ca491851-5381-4804-a23b-6e3742268342) |
| CEH — 认证道德黑客 | EC-Council | [🔗 验证](https://aspen.eccouncil.org/verify) · ID: ECC6281540739 |
| CompTIA Security+ | CompTIA | [🔗 验证](https://www.credly.com/badges/fd83e162-9f9a-4cbd-a6b3-f6e65dc78ab8) |
## 📌 特色项目
| 项目 | 描述 | 技术栈 |
|------|----------|--------|
| [**MyPortfolio2**](https://github.com/MistanKh/MyPortfolio2) | 黑客组合集 — 实时 CVE 源、THM 小部件、ExploitDB 标志、CI/CD | HTML · CSS · JS · GitHub Actions |
| [**LazyChad**](https://github.com/MistanKh/LazyChad) | Neovim/NvChad 包装器 — AUR、deb、rpm 包 | Lua · Shell |
| [**python-for-cybersecurity**](https://github.com/MistanKh/python-for-cybersecurity) | 漏洞利用开发与安全脚本实践 | Python |
| [**Kali-Scripts**](https://github.com/MistanKh/Kali-Scripts) | 自动安装 Neovim + GitHub CLI 脚本 | Shell |
| [**kvm-qemu-setup**](https://github.com/MistanKh/kvm-qemu-setup) | QEMU/KVM 虚拟化配置(Arch Linux) | Shell |
## 📊 TryHackMe 统计
[](https://tryhackme.com/p/Mistan)
| 指标 | 值 |
|------|-----|
| 排名 | #29,210 |
| 前 2% | 2% |
| 等级 | 13 |
| 完成房间数 | 153 |
| 获得徽章数 | 29 |
## 📈 GitHub 统计


📍 印度曼尼普尔邦因帕尔 · 📧 [mistankhomdram@gmail.com](mailto:mistankhomdram@gmail.com)
"你越安静,就越能听见更多。"
标签:CEH, CTF选手, CVE, eJPT, GitHub Pages, HackTheBox, Lighthouse, rizin, Security+, SEO优化, TryHackMe, Web渗透, 个人品牌, 在线简历, 多模态安全, 威胁情报, 安全认证, 安全运营中心, 应用安全, 开发者工具, 技术博客, 数字签名, 数据可视化, 数据统计, 漏洞分析, 特权提升, 社会工程, 端口扫描, 网络安全分析师, 网络映射, 自动化部署, 路径探测, 逆向工具