使用多个搜索引擎快速发现互联网上的暴露主机。





功能 •
安装 •
用法 •
配置 •
运行 Uncover •
加入 Discord
**uncover** 是一个使用知名搜索引擎 API 的 Go 包装器,能够快速发现互联网上的暴露主机。它的设计初衷是自动化,因此您可以将其查询并将结果与当前的流水线工具结合使用。
# 功能
- 同时查询多个搜索引擎
- 支持的搜索引擎列表
- **[Shodan](https://www.shodan.io)**
- **[Censys](https://search.censys.io)**
- **[FOFA](https://fofa.info)**
- **[Hunter](https://hunter.qianxin.com)**
- **[Quake](https://quake.360.net/quake/#/index)**
- **ZoomEye (https://www.zoomeye.ai)**
- **[Netlas](https://netlas.io/)**
- **[CriminalIP](https://www.criminalip.io)**
- **[PublicWWW](https://publicwww.com)**
- **[HunterHow](https://hunter.how)**
- **[Google](https://www.google.com)**
- **[Onyphe](https://www.onyphe.io/)**
- **[Driftnet](https://driftnet.io)**
- 支持多个 API 密钥输入
- 自动 API 密钥随机化
- 支持 **stdin** / **stdout** 输入输出
## 安装说明
uncover 需要 **go1.21** 才能成功安装。运行以下命令获取仓库 -
```
go install -v github.com/projectdiscovery/uncover/cmd/uncover@latest
```
## 用法
```
uncover -h
```
这将显示工具的帮助信息。以下是它支持的所有标志:
```
Usage:
./uncover [flags]
Flags:
INPUT:
-q, -query string[] search query, supports: stdin,file,config input (example: -q 'example query', -q 'query.txt')
-e, -engine string[] search engine to query (shodan,shodan-idb,fofa,censys,quake,hunter,zoomeye,netlas,criminalip,publicwww,hunterhow,google,driftnet) (default shodan)
-asq, -awesome-search-queries string[] use awesome search queries to discover exposed assets on the internet (example: -asq 'jira')
SEARCH-ENGINE:
-s, -shodan string[] search query for shodan (example: -shodan 'query.txt')
-sd, -shodan-idb string[] search query for shodan-idb (example: -shodan-idb 'query.txt')
-ff, -fofa string[] search query for fofa (example: -fofa 'query.txt')
-cs, -censys string[] search query for censys (example: -censys 'query.txt')
-qk, -quake string[] search query for quake (example: -quake 'query.txt')
-ht, -hunter string[] search query for hunter (example: -hunter 'query.txt')
-ze, -zoomeye string[] search query for zoomeye (example: -zoomeye 'query.txt')
-ne, -netlas string[] search query for netlas (example: -netlas 'query.txt')
-cl, -criminalip string[] search query for criminalip (example: -criminalip 'query.txt')
-pw, -publicwww string[] search query for publicwww (example: -publicwww 'query.txt')
-hh, -hunterhow string[] search query for hunterhow (example: -hunterhow 'query.txt')
-gg, -google string[] search query for google (example: -google 'query.txt')
-on, -onyphe string[] search query for onyphe (example: -onyphe 'query.txt')
-df, -driftnet string[] search query for driftnet (example: -driftnet 'query.txt')
CONFIG:
-pc, -provider string provider configuration file (default "$CONFIG/uncover/provider-config.yaml")
-config string flag configuration file (default "$CONFIG/uncover/config.yaml")
-timeout int timeout in seconds (default 30)
-rl, -rate-limit int maximum number of http requests to send per second
-rlm, -rate-limit-minute int maximum number of requests to send per minute
-retry int number of times to retry a failed request (default 2)
-proxy string http proxy to use with uncover
OUTPUT:
-o, -output string output file to write found results
-f, -field string field to display in output (ip,port,host) (default "ip:port")
-j, -json write output in JSONL(ines) format
-r, -raw write raw output as received by the remote api
-l, -limit int limit the number of results to return (default 100)
-nc, -no-color disable colors in output
DEBUG:
-silent show only results in output
-version show version of the project
-v show verbose output
```
## 将 uncover 用作库
在 [examples](examples/main.go) 目录中提供了将 uncover 用作库的示例。
## 提供者配置
默认的提供者配置文件应位于 `$CONFIG/uncover/provider-config.yaml`,示例内容如下:
```
shodan:
- SHODAN_API_KEY_1
- SHODAN_API_KEY_2
censys:
- CENSYS_API_TOKEN_1:CENSYS_ORGANIZATION_ID_1
- CENSYS_API_TOKEN_2:CENSYS_ORGANIZATION_ID_2
fofa:
- FOFA_EMAIL_1:FOFA_KEY_1
- FOFA_EMAIL_2:FOFA_KEY_2
quake:
- QUAKE_TOKEN_1
- QUAKE_TOKEN_2
hunter:
- HUNTER_API_KEY_1
- HUNTER_API_KEY_2
zoomeye:
- ZOOMEYE_API_KEY_1
- ZOOMEYE_API_KEY_2
netlas:
- NETLAS_API_KEY_1
- NETLAS_API_KEY_2
criminalip:
- CRIMINALIP_API_KEY_1
- CRIMINALIP_API_KEY_2
publicwww:
- PUBLICWWW_API_KEY_1
- PUBLICWWW_API_KEY_2
hunterhow:
- HUNTERHOW_API_KEY_1
- HUNTERHOW_API_KEY_2
google:
- GOOGLE_API_KEY_1:Google_API_CX_1
- GOOGLE_API_KEY_2:Google_API_CX_2
onyphe:
- ONYPHE_API_KEY_1
- ONYPHE_API_KEY_2
driftnet:
- DRIFTNET_API_KEY_1
- DRIFTNET_API_KEY_2
```
当在配置文件中为同一提供者指定多个密钥/凭证时,系统会为每次执行随机选择一个密钥。
或者您也可以在 bash 配置文件中将 API 密钥设置为环境变量。
```
export SHODAN_API_KEY=xxx
export CENSYS_API_TOKEN=xxx
export CENSYS_ORGANIZATION_ID=xxx
export FOFA_EMAIL=xxx
export FOFA_KEY=xxx
export QUAKE_TOKEN=xxx
export HUNTER_API_KEY=xxx
export ZOOMEYE_API_KEY=xxx
export NETLAS_API_KEY=xxx
export CRIMINALIP_API_KEY=xxx
export PUBLICWWW_API_KEY=xxx
export HUNTERHOW_API_KEY=xxx
export GOOGLE_API_KEY=xxx
export GOOGLE_API_CX=xxx
export ONYPHE_API_KEY=xxx
export DRIFTNET_API_KEY=xxx
```
所需的 API 密钥可通过在以下平台注册获取:[Shodan](https://account.shodan.io/register)、[Censys](https://censys.io/register)、[Fofa](https://fofa.info/toLogin)、[Quake](https://quake.360.net/quake/#/index)、[Hunter](https://user.skyeye.qianxin.com/user/register?next=https%3A//hunter.qianxin.com/api/uLogin&fromLogin=1)、[ZoomEye](https://www.zoomeye.ai)、[Netlas](https://app.netlas.io/registration/)、[CriminalIP](https://www.criminalip.io/register)、[Publicwww](https://publicwww.com/profile/signup.html)、Google [[1]](https://developers.google.com/custom-search/v1/introduction#identify_your_application_to_google_with_api_key)、[[2]](https://programmablesearchengine.google.com/controlpanel/create)、[Onyphe](https://search.onyphe.io/signup) 和 [Driftnet](https://driftnet.io/auth?state=signup)。
## 运行 Uncover
### 默认运行:
**uncover** 支持多种查询方式,包括 **stdin** 或 `q` 标志,默认使用 `shodan` 引擎进行搜索(未指定引擎时)。
```
echo 'ssl:"Uber Technologies, Inc."' | uncover
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
107.180.12.116:993
107.180.26.155:443
104.244.99.31:443
161.28.20.79:443
104.21.8.108:443
198.71.233.203:443
104.17.237.13:443
162.255.165.171:443
12.237.119.61:443
192.169.250.211:443
104.16.251.50:443
```
使用 **file** 输入(每行包含多个搜索查询)运行 **uncover**。
```
cat dorks.txt
ssl:"Uber Technologies, Inc."
title:"Grafana"
```
```
uncover -q dorks.txt
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
107.180.12.116:993
107.180.26.155:443
104.244.99.31:443
161.28.20.79:443
104.21.8.108:443
198.71.233.203:443
2607:7c80:54:3::74:3001
104.198.55.35:80
46.101.82.244:3000
34.147.126.112:80
138.197.147.213:8086
```
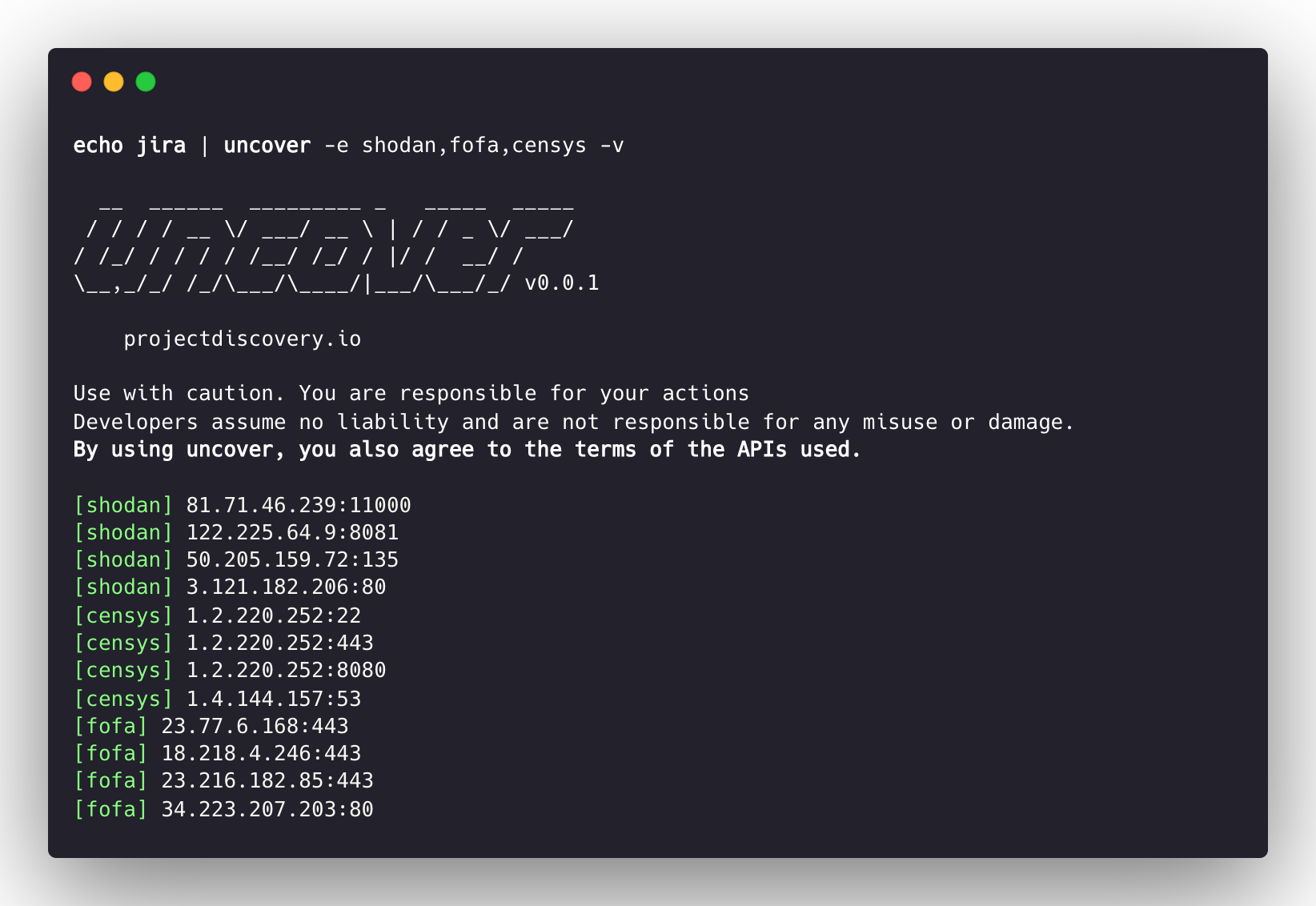
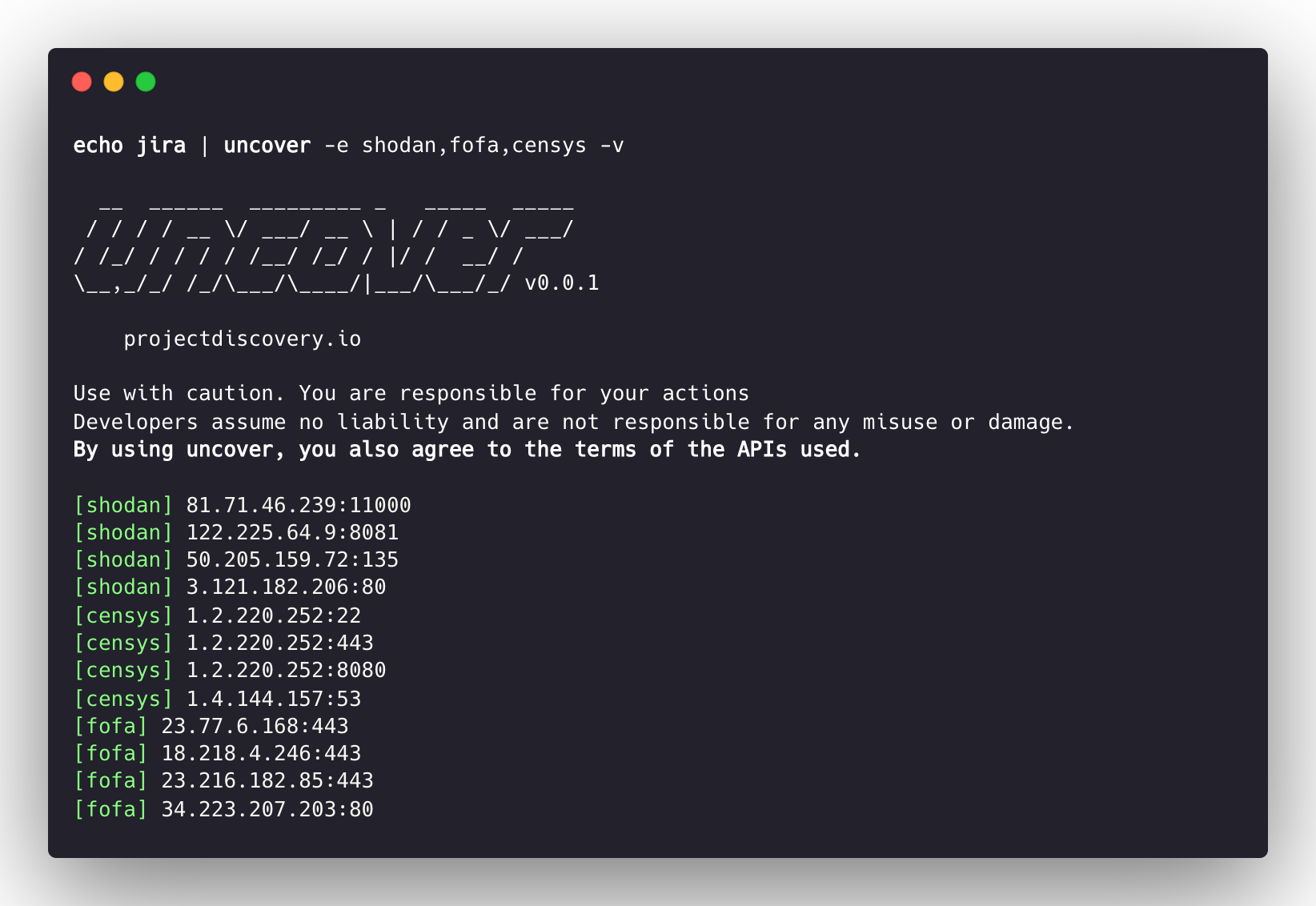
### 对多个搜索引擎的单一查询
**uncover** 支持多个搜索引擎,默认使用 **shodan**,可使用 `-e` 标志在任意或全部搜索引擎上运行相同查询。
```
echo jira | uncover -e shodan,censys,fofa,quake,hunter,zoomeye,netlas,criminalip,driftnet
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
176.31.249.189:5001
13.211.116.80:443
43.130.1.221:631
192.195.70.29:443
52.27.22.181:443
117.48.120.226:8889
106.52.115.145:49153
13.69.135.128:443
193.35.99.158:443
18.202.109.218:8089
101.36.105.97:21379
42.194.226.30:2626
```
### 对多个搜索引擎的多查询
```
uncover -shodan 'http.component:"Atlassian Jira"' -censys 'services.software.product=`Jira`' -fofa 'app="ATLASSIAN-JIRA"' -quake 'Jira' -hunter 'Jira' -zoomeye 'app:"Atlassian JIRA"' -netlas 'jira' -criminalip 'Jira' -driftnet 'field=product-tag:jira'
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
104.68.37.129:443
162.222.160.42:443
34.255.84.133:443
52.204.121.166:443
23.198.29.120:443
136.156.180.95:443
54.194.233.15:443
104.117.55.155:443
149.81.4.6:443
54.255.218.95:443
3.223.137.57:443
83.228.124.171:443
23.202.195.82:443
52.16.59.25:443
18.159.145.227:443
104.105.53.236:443
```
### Shodan-InternetDB API(简体中文)
**uncover** 支持 [shodan-internetdb](https://internetdb.shodan.io) API,以获取给定 IP/CIDR 输入的可用端口。
当提供 **IP/CIDR** 作为输入时,`shodan-idb` 被用作 **默认** 引擎,否则使用 `shodan` 搜索引擎。
```
echo 51.83.59.99/24 | uncover
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
51.83.59.1:53
51.83.59.1:10000
51.83.59.2:53
51.83.59.3:25
51.83.59.3:80
51.83.59.3:389
51.83.59.3:443
51.83.59.3:465
51.83.59.3:587
51.83.59.3:993
```
### **IP/CIDR** 的开放端口
**uncover** 支持使用 [driftnet](https://driftnet.io) API 快速查询给定 IP/CIDR 输入的开放端口。
```
echo 8.8.8.8/20 | uncover -e driftnet
__ ______ _________ _ _____ _____
/ / / / __ \/ ___/ __ \ | / / _ \/ ___/
/ /_/ / / / / /__/ /_/ / |/ / __/ /
\__,_/_/ /_/\___/\____/|___/\___/_/ v0.0.9
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[WRN] By using uncover, you also agree to the terms of the APIs used.
...
8.8.4.4:443
8.8.4.4:53
8.8.4.4:853
8.8.6.29:443
8.8.6.40:443
8.8.6.70:443
8.8.6.94:443
8.8.11.1:22
8.8.11.253:22
8.8.11.64:443
8.8.8.8:443
8.8.8.8:53
8.8.8.8:853
...
```
### 字段格式
`-f, -field` 标志可用于指示返回哪些字段,当前支持 `ip`、`port` 和 `host`,并可用于返回所需字段。
```
uncover -q jira -f host -silent
ec2-44-198-22-253.compute-1.amazonaws.com
ec2-18-246-31-139.us-west-2.compute.amazonaws.com
tasks.devrtb.com
leased-line-91-149-128-229.telecom.by
74.242.203.213.static.inetbone.net
ec2-52-211-7-108.eu-west-1.compute.amazonaws.com
ec2-54-187-161-180.us-west-2.compute.amazonaws.com
185-2-52-226.static.nucleus.be
ec2-34-241-80-255.eu-west-1.compute.amazonaws.com
```
### 字段格式化
**uncover** 具有 `-f, -field` 标志,可用于自定义输出格式。例如,在 `uncover -f https://ip:port/version` 的情况下,`ip:port` 将在输出中被结果替换,同时保留定义的格式。它还可用于指定已知的 scheme/path/file,以便准备输出,使其能够立即作为输入传递给流水线中的其他工具。
```
echo kubernetes | uncover -f https://ip:port/version -silent
https://35.222.229.38:443/version
https://52.11.181.228:443/version
https://35.239.255.1:443/version
https://34.71.48.11:443/version
https://130.211.54.173:443/version
https://54.184.250.232:443/version
```
**uncover** 的输出可以进一步通过管道传递给工作流中接受 **stdin** 输入的其他项目,例如:
- `uncover -q example -f ip | naabu` - 对发现的主机进行 [naabu](https://github.com/projectdiscovery/naabu) 端口扫描。
- `uncover -q title:GitLab | httpx` - 对发现的结果进行 [httpx](https://github.com/projectdiscovery/httpx) Web 服务器探测。
- `uncover -q 51.83.59.99/24 | httpx` - 对从 shodan-internetdb 获得的主机/端口进行 [httpx](https://github.com/projectdiscovery/naabu) 探测。
```
uncover -q http.title:GitLab -silent | httpx -silent
https://15.185.150.109
https://139.162.137.16
https://164.68.115.243
https://135.125.215.186
https://163.172.59.119
http://15.236.10.197
https://129.206.117.248
```
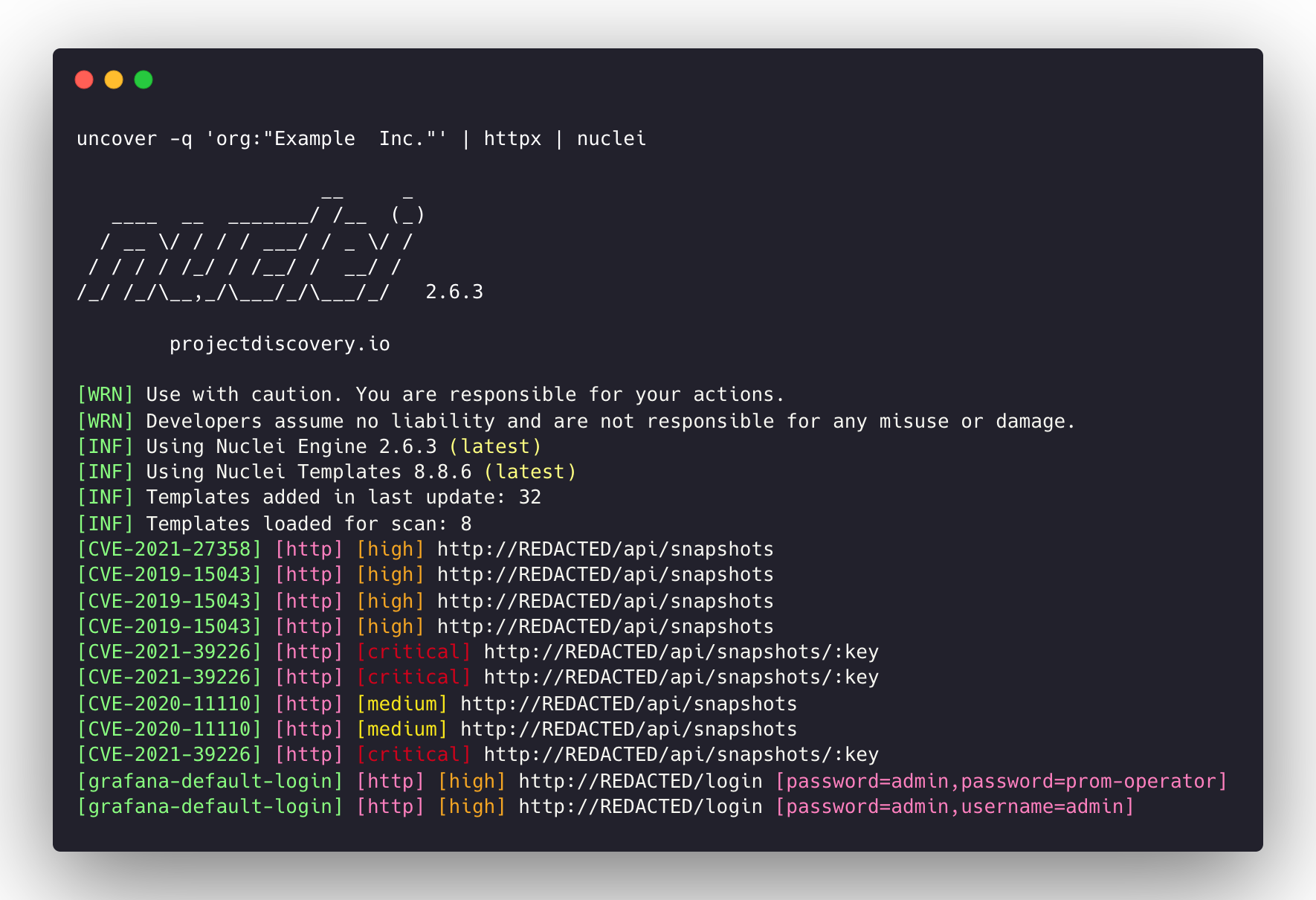
- `uncover -q 'org:"Example Inc."' | httpx | nuclei` - 使用 [httpx](https://github.com/projectdiscovery/httpx) / [nuclei](https://github.com/projectdiscovery/nuclei) 进行漏洞评估。
## 注意事项:
- 在运行或使用本项目之前,需要配置 **密钥/凭证**。
- `query` 标志支持 **所有且仅搜索引支持的过滤器**。
- 结果默认限制为 `100` 条,可通过 `limit` 标志增加。
- `shodan-idb` API 不需要 API 密钥,可直接使用。
- 当提供 **IP/CIDR** 作为输入时,`shodan-idb` API 被用作 **默认** 引擎。
**uncover** 由 [projectdiscovery](https://projectdiscovery.io) 团队以 🖤 打造。