ckotzbauer/vulnerability-operator
GitHub: ckotzbauer/vulnerability-operator
基于 Grype 的 Kubernetes Operator,通过扫描 Git 仓库中的 SBOM 文件实现持续的容器漏洞监控。
Stars: 85 | Forks: 9
# vulnerability-operator
[](https://github.com/ckotzbauer/vulnerability-operator/actions/workflows/test.yml)
#### Metrics
每个 CVE 都会作为 Prometheus `vuln_operator_cves` gauge-metric 导出,并针对其出现的每个容器进行记录。
```
vuln_operator_cves{container_name="kyverno", cve="CVE-2020-16250", fix_state="unknown", image_id="ghcr.io/kyverno/kyverno@sha256:4fc715e9287446222bf12b1245899b195ecea8beda54c6f6a3587373c376cad1", package="github.com/hashicorp/vault/api", k8s_name="kyverno", k8s_namespace="kyverno", k8s_kind="Deployment", severity="Critical", type="go-module", version="v1.3.1"}
```
**注意**:operator 在重新填充之前会从向量中移除所有指标。在此期间,数据不具有代表性。
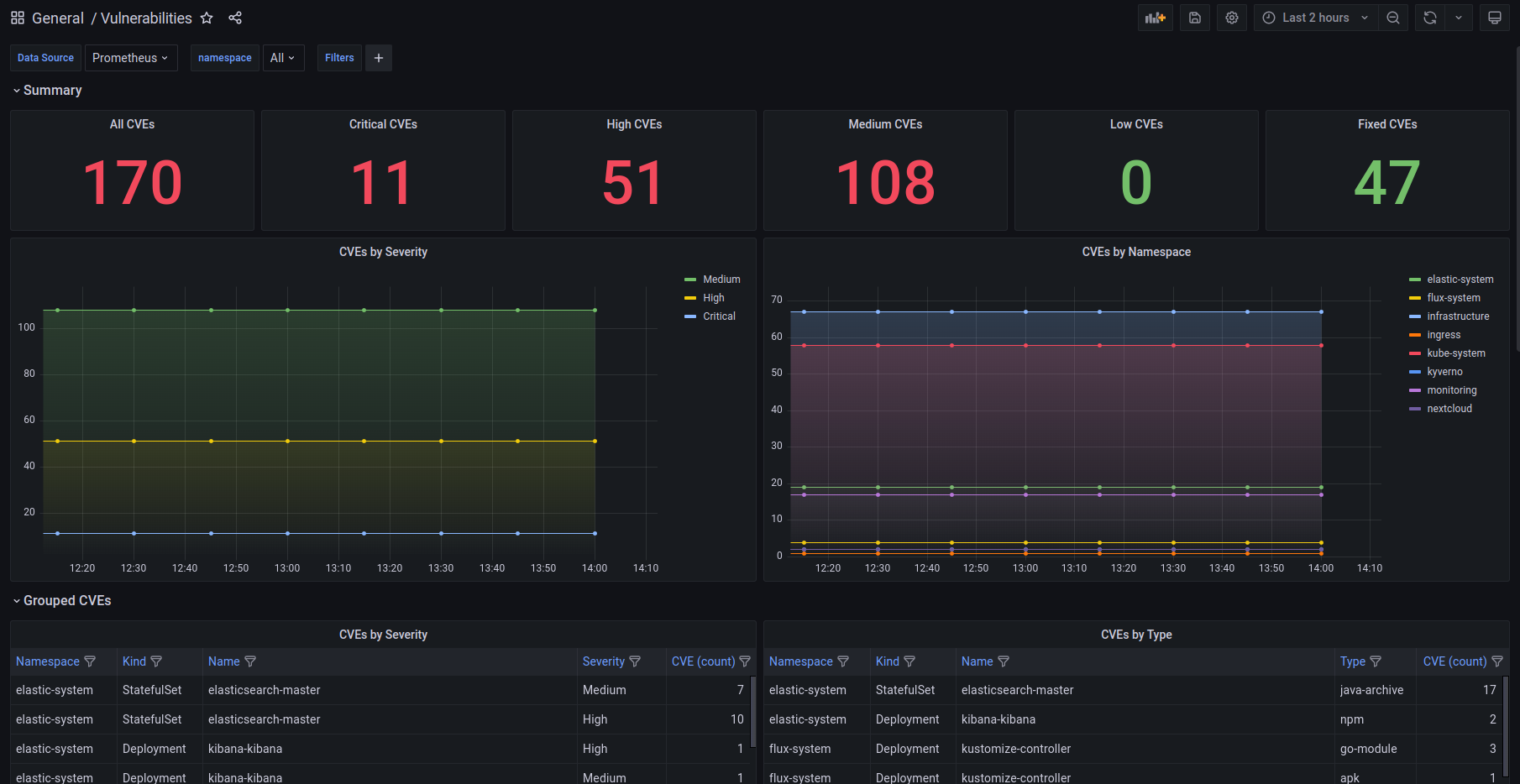
#### Grafana Dashboard
有一个用于 Grafana 的 [dashboard](./deploy/grafana-dashboard.json) 用于查看收集的漏洞指标。
#### PolicyReport
设置 `policyreport` 目标后,operator 将扫描结果作为 `PolicyReport` CRs 存储在集群内。每个 `PolicyReport` 对象
由相应的 pod 拥有,以启用 Kubernetes 的自动清理。
## 基于上下文的漏洞过滤
您可以应用过滤规则来忽略某些漏洞或将它们移至单独的指标中。
如果您想从指标中排除漏洞(例如误报或应用程序执行路径之外的问题),这非常有用。
过滤规则支持以下属性:
- CVE
- package name
- container context(包含以下子集)
- image
- namespace
- kind
- name
容器上下文属性支持 glob 模式 `*` 和 `?`,而 CVE 和 package 仅匹配其精确值。
容器上下文仅在所有属性都匹配时才适用(AND 条件)。
过滤规则通过 yaml 格式的文件提供。其路径使用 `--filter-config-file` 配置。
#### 目标
对于 Prometheus 目标,单独的指标 `vuln_operator_cves_audit` 包含来自 `audit` 部分的匹配项。
对于 json 目标,提供单独的文件 `audited.json`。
## 安全
docker-image 基于 scratch-image,以减少攻击面并保持镜像小巧。
此外,镜像和发布工件使用 [cosign](https://github.com/sigstore/cosign) 签名,并使用来源文件进行证明。发布过程
满足 SLSA Level 2。所有这些“元数据文件”也存储在专用仓库 `ghcr.io/ckotzbauer/vulnerability-operator-metadata` 中。
SLSA 和签名对于该项目仍处于实验阶段。
发现安全问题时,请参阅 [Security process](https://github.com/ckotzbauer/.github/blob/main/SECURITY.md)。
## [License](https://github.com/ckotzbauer/vulnerability-operator/blob/master/LICENSE)
## [Changelog](https://github.com/ckotzbauer/vulnerability-operator/blob/master/CHANGELOG.md)
## 贡献
请参阅 [Contribution guildelines](https://github.com/ckotzbauer/.github/blob/main/CONTRIBUTING.md)。
## 行为准则
请参阅 [Conduct guildelines](https://github.com/ckotzbauer/.github/blob/main/CODE_OF_CONDUCT.md)。
JSON 示例
``` [ { "ID": "CVE-2019-19924", "Severity": "Medium", "Type": "rpm", "Package": "sqlite", "Installed": "3.7.17-8.el7_7.1", "FixedIn": [], "FixState": "wont-fix", "URLs": [ "https://access.redhat.com/security/cve/CVE-2019-19924" ], "ImageID": "docker.elastic.co/beats/filebeat@sha256:e418d12e08a1b74140c9edc6bdc773110b0f802340e25e2716950bac86ae14ce", "Containers": [ { "PodNamespace": "elastic-system", "PodName": "filebeat-filebeat-6xkf4", "ContainerName": "filebeat" }, { "PodNamespace": "elastic-system", "PodName": "filebeat-filebeat-g6zbh", "ContainerName": "filebeat" }, { "PodNamespace": "elastic-system", "PodName": "filebeat-filebeat-jkgnh", "ContainerName": "filebeat" } ] }, { "ID": "CVE-2020-16250", "Severity": "Critical", "Type": "go-module", "Package": "github.com/hashicorp/vault/api", "Installed": "v1.3.1", "FixedIn": [], "FixState": "unknown", "URLs": [ "https://www.hashicorp.com/blog/category/vault/", "https://github.com/hashicorp/vault/blob/master/CHANGELOG.md#151", "http://packetstormsecurity.com/files/159478/Hashicorp-Vault-AWS-IAM-Integration-Authentication-Bypass.html" ], "ImageID": "ghcr.io/kyverno/kyverno@sha256:4fc715e9287446222bf12b1245899b195ecea8beda54c6f6a3587373c376cad1", "Containers": [ { "PodNamespace": "kyverno", "PodName": "kyverno-555dcf9f66-csmq5", "ContainerName": "kyverno" }, { "PodNamespace": "kyverno", "PodName": "kyverno-555dcf9f66-gsphr", "ContainerName": "kyverno" } ] } ] ```PolicyReport 示例
``` apiVersion: wgpolicyk8s.io/v1alpha2 kind: PolicyReport metadata: creationTimestamp: "2022-06-18T14:57:27Z" generation: 3 labels: kubernetes.io/created-by: vulnerability-operator name: vuln-kyverno-688464bd95-55drc namespace: kyverno ownerReferences: - apiVersion: v1 kind: Pod name: kyverno-688464bd95-55drc uid: 24bdccbb-653a-4005-8463-cf511a919037 resourceVersion: "160903586" uid: e3cd1447-49ef-481d-b44b-cc38239ea870 results: - category: github.com/theupdateframework/go-tuf message: 'github.com/theupdateframework/go-tuf: GHSA-66x3-6cw3-v5gj' policy: GHSA-66x3-6cw3-v5gj properties: FixedVersion: 0.3.0 InstalledVersion: v0.0.0-20220211205608-f0c3294f63b9 URL: https://github.com/advisories/GHSA-66x3-6cw3-v5gj resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 - category: google.golang.org/protobuf message: 'google.golang.org/protobuf: CVE-2015-5237' policy: CVE-2015-5237 properties: FixedVersion: "" InstalledVersion: v1.28.0 URL: https://github.com/google/protobuf/issues/760 resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 - category: google.golang.org/protobuf message: 'google.golang.org/protobuf: CVE-2021-22570' policy: CVE-2021-22570 properties: FixedVersion: "" InstalledVersion: v1.28.0 URL: https://github.com/protocolbuffers/protobuf/releases/tag/v3.15.0 resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 - category: google.golang.org/protobuf message: 'google.golang.org/protobuf: CVE-2015-5237' policy: CVE-2015-5237 properties: FixedVersion: "" InstalledVersion: v1.28.0 URL: https://github.com/google/protobuf/issues/760 resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 - category: google.golang.org/protobuf message: 'google.golang.org/protobuf: CVE-2021-22570' policy: CVE-2021-22570 properties: FixedVersion: "" InstalledVersion: v1.28.0 URL: https://github.com/protocolbuffers/protobuf/releases/tag/v3.15.0 resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 - category: github.com/theupdateframework/go-tuf message: 'github.com/theupdateframework/go-tuf: GHSA-66x3-6cw3-v5gj' policy: GHSA-66x3-6cw3-v5gj properties: FixedVersion: 0.3.0 InstalledVersion: v0.0.0-20220211205608-f0c3294f63b9 URL: https://github.com/advisories/GHSA-66x3-6cw3-v5gj resources: - kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 result: fail severity: high source: vulnerability-operator timestamp: nanos: 728434599 seconds: 1655564847 scope: kind: Pod name: kyverno-688464bd95-55drc namespace: kyverno uid: 24bdccbb-653a-4005-8463-cf511a919037 summary: error: 0 fail: 6 pass: 0 skip: 0 warn: 0 ```过滤配置示例
``` ignore: # Ignore any vulnerabilities in ruby gem rdoc - package: rdoc # Ignore CVE GHSA-8cr8-4vfw-mr7h - vulnerability: GHSA-8cr8-4vfw-mr7h audit: # If GHSA-fp4w-jxhp-m23p was found in gitlab-ce images, move it the "audit" metric - vulnerability: GHSA-fp4w-jxhp-m23p context: - image: gitlab/gitlab-ce* namespace: "*" kind: "*" name: "*" # Move any CVE for the git package to the "audit" metric, if it was found in a gitlab-*-redis deployment - package: git context: - image: "*" namespace: "*" kind: Deployment name: gitlab-*-redis ```标签:Angular, Claude, CVE检测, DevSecOps, EVTX分析, Git仓库扫描, Golang, Grafana可视化, Grype, JSON报告, Kubernetes Operator, Prometheus监控, SBOM分析, Svelte, Web截图, 上游代理, 子域名突变, 安全漏洞扫描, 安全编程, 容器安全, 对称加密, 开源安全工具, 文档安全, 日志审计, 自动化审计, 自定义请求头, 请求拦截, 跌倒检测, 软件物料清单, 逆向工程平台