kubearmor/KubeArmor
GitHub: kubearmor/KubeArmor
基于 LSM 的云原生运行时安全强制系统,实现容器工作负载的加固与最小权限策略执行。
Stars: 2056 | Forks: 438

[](https://github.com/kubearmor/KubeArmor/actions/workflows/ci-test-ginkgo.yml/)
[](https://bestpractices.coreinfrastructure.org/projects/5401)
[](https://clomonitor.io/projects/cncf/kubearmor)
[](https://securityscorecards.dev/viewer/?uri=github.com/kubearmor/KubeArmor)
[](https://app.fossa.com/projects/git%2Bgithub.com%2Fkubearmor%2FKubeArmor?ref=badge_shield)
[](https://app.fossa.com/projects/git%2Bgithub.com%2Fkubearmor%2FKubeArmor?ref=badge_shield)
[](https://cloud-native.slack.com/archives/C02R319HVL3)
[](https://github.com/kubearmor/KubeArmor/discussions)
[](https://hub.docker.com/r/kubearmor/kubearmor)
[](https://artifacthub.io/packages/search?kind=19)
KubeArmor 是一个云原生运行时安全强制系统,它在系统层面限制 Pod、容器和节点(VM)的行为(例如进程执行、文件访问和网络操作)。
KubeArmor 利用 [Linux 安全模块 (LSM)](https://en.wikipedia.org/wiki/Linux_Security_Modules),例如 [AppArmor](https://en.wikipedia.org/wiki/AppArmor)、[SELinux](https://en.wikipedia.org/wiki/Security-Enhanced_Linux) 或 [BPF-LSM](https://docs.kernel.org/bpf/prog_lsm.html) 来强制执行用户指定的策略。KubeArmor 通过利用 eBPF 生成带有容器/Pod/命名空间身份信息的丰富告警/遥测事件。
| | |
|:---|:---|
| :muscle: **[加固基础设施](getting-started/hardening_guide.md)**
:chains: 保护关键路径,例如证书包
:clipboard: 基于 MITRE、STIGs、CIS 的规则
:left_luggage: 限制对原始数据库表的访问 | :ring: **[最小权限访问](getting-started/least_permissive_access.md)**
:traffic_light: 进程白名单
:traffic_light: 网络白名单
:control_knobs: 控制对敏感资产的访问 | | :telescope: **[应用行为](getting-started/workload_visibility.md)**
:dna: 进程执行,文件系统访问
:compass: 服务绑定,入口和出口连接
:microscope: 敏感系统调用分析 | :snowflake: **[部署模型](getting-started/deployment_models.md)**
:wheel_of_dharma: Kubernetes 部署
:whale2: 容器化部署
:computer: 虚拟机/裸机部署 | ## 架构概览 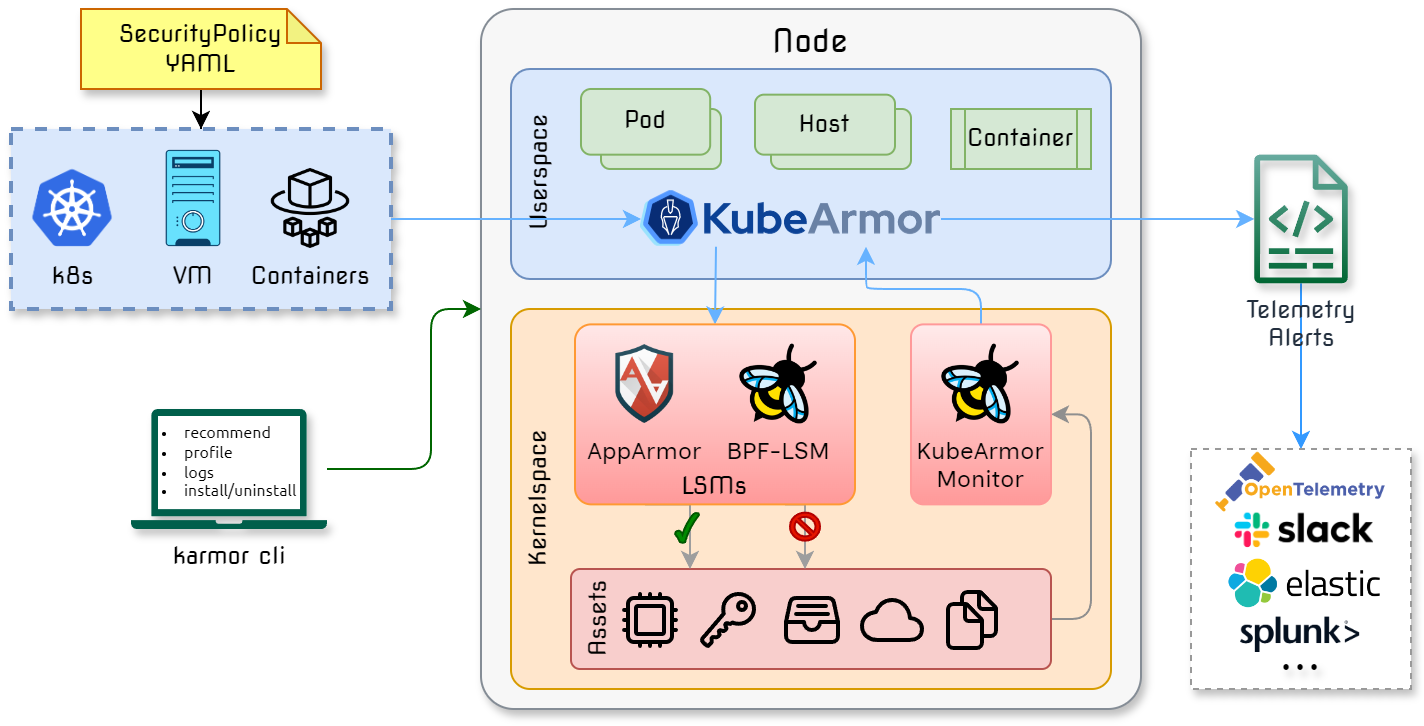 ## 文档 :notebook: * :point_right: [入门指南](getting-started/deployment_guide.md) * :dart: [用例](getting-started/use-cases/hardening.md) * :heavy_check_mark: [KubeArmor 支持矩阵](getting-started/support_matrix.md) * :chess_pawn: [KubeArmor 有何不同?](getting-started/differentiation.md) * :scroll: Pod/容器安全策略 [[规范](getting-started/security_policy_specification.md)] [[示例](getting-started/security_policy_examples.md)] * :scroll: 集群级 Pod/容器安全策略 [[规范](getting-started/cluster_security_policy_specification.md)] [[示例](getting-started/cluster_security_policy_examples.md)] * :scroll: 主机/节点安全策略 [[规范](getting-started/host_security_policy_specification.md)] [[示例](getting-started/host_security_policy_examples.md)]
... [详细文档](https://docs.kubearmor.io/kubearmor/) ### 双周会议 - :speaking_head: [Zoom 链接](http://zoom.kubearmor.io) - :page_facing_up: 会议纪要:[文档](https://docs.google.com/document/d/1IqIIG9Vz-PYpbUwrH0u99KYEM1mtnYe6BHrson4NqEs/edit) - :calendar: 日历邀请:[Google 日历](http://www.google.com/calendar/event?action=TEMPLATE&dates=20220210T150000Z%2F20220210T153000Z&text=KubeArmor%20Community%20Call&location=&details=%3Ca%20href%3D%22https%3A%2F%2Fdocs.google.com%2Fdocument%2Fd%2F1IqIIG9Vz-PYpbUwrH0u99KYEM1mtnYe6BHrson4NqEs%2Fedit%22%3EMinutes%20of%20Meeting%3C%2Fa%3E%0A%0A%3Ca%20href%3D%22%20http%3A%2F%2Fzoom.kubearmor.io%22%3EZoom%20Link%3C%2Fa%3E&recur=RRULE:FREQ=WEEKLY;INTERVAL=2;BYDAY=TH&ctz=Asia/Calcutta),[ICS 文件](getting-started/resources/KubeArmorMeetup.ics) ## 声明/致谢 :handshake: - KubeArmor 使用了 [Tracee](https://github.com/aquasecurity/tracee/) 的系统调用工具函数。 ## 云原生计算基金会 KubeArmor 是云原生计算基金会的 [沙箱项目](https://www.cncf.io/projects/kubearmor/)。  ## 路线图 KubeArmor 的路线图通过 [KubeArmor Projects](https://github.com/orgs/kubearmor/projects?query=is%3Aopen) 进行跟踪
:chains: 保护关键路径,例如证书包
:clipboard: 基于 MITRE、STIGs、CIS 的规则
:left_luggage: 限制对原始数据库表的访问 | :ring: **[最小权限访问](getting-started/least_permissive_access.md)**
:traffic_light: 进程白名单
:traffic_light: 网络白名单
:control_knobs: 控制对敏感资产的访问 | | :telescope: **[应用行为](getting-started/workload_visibility.md)**
:dna: 进程执行,文件系统访问
:compass: 服务绑定,入口和出口连接
:microscope: 敏感系统调用分析 | :snowflake: **[部署模型](getting-started/deployment_models.md)**
:wheel_of_dharma: Kubernetes 部署
:whale2: 容器化部署
:computer: 虚拟机/裸机部署 | ## 架构概览 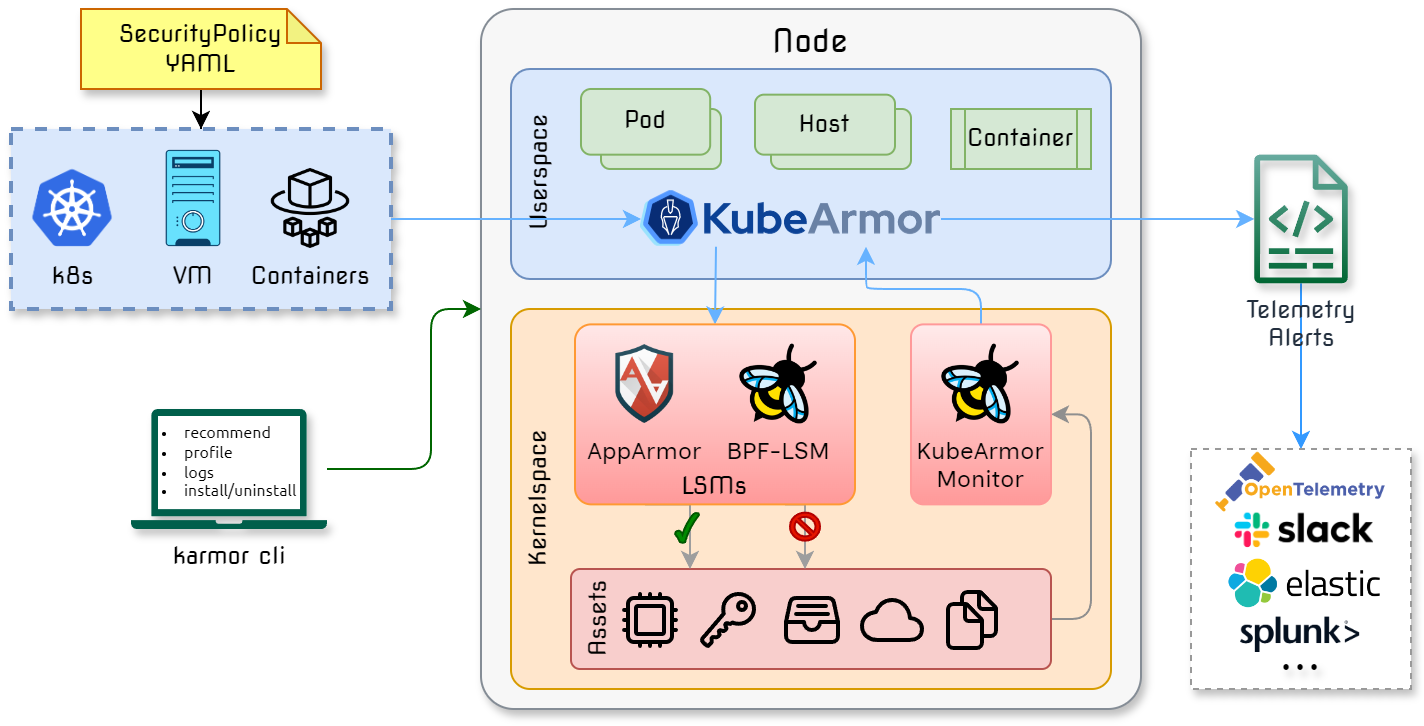 ## 文档 :notebook: * :point_right: [入门指南](getting-started/deployment_guide.md) * :dart: [用例](getting-started/use-cases/hardening.md) * :heavy_check_mark: [KubeArmor 支持矩阵](getting-started/support_matrix.md) * :chess_pawn: [KubeArmor 有何不同?](getting-started/differentiation.md) * :scroll: Pod/容器安全策略 [[规范](getting-started/security_policy_specification.md)] [[示例](getting-started/security_policy_examples.md)] * :scroll: 集群级 Pod/容器安全策略 [[规范](getting-started/cluster_security_policy_specification.md)] [[示例](getting-started/cluster_security_policy_examples.md)] * :scroll: 主机/节点安全策略 [[规范](getting-started/host_security_policy_specification.md)] [[示例](getting-started/host_security_policy_examples.md)]
... [详细文档](https://docs.kubearmor.io/kubearmor/) ### 双周会议 - :speaking_head: [Zoom 链接](http://zoom.kubearmor.io) - :page_facing_up: 会议纪要:[文档](https://docs.google.com/document/d/1IqIIG9Vz-PYpbUwrH0u99KYEM1mtnYe6BHrson4NqEs/edit) - :calendar: 日历邀请:[Google 日历](http://www.google.com/calendar/event?action=TEMPLATE&dates=20220210T150000Z%2F20220210T153000Z&text=KubeArmor%20Community%20Call&location=&details=%3Ca%20href%3D%22https%3A%2F%2Fdocs.google.com%2Fdocument%2Fd%2F1IqIIG9Vz-PYpbUwrH0u99KYEM1mtnYe6BHrson4NqEs%2Fedit%22%3EMinutes%20of%20Meeting%3C%2Fa%3E%0A%0A%3Ca%20href%3D%22%20http%3A%2F%2Fzoom.kubearmor.io%22%3EZoom%20Link%3C%2Fa%3E&recur=RRULE:FREQ=WEEKLY;INTERVAL=2;BYDAY=TH&ctz=Asia/Calcutta),[ICS 文件](getting-started/resources/KubeArmorMeetup.ics) ## 声明/致谢 :handshake: - KubeArmor 使用了 [Tracee](https://github.com/aquasecurity/tracee/) 的系统调用工具函数。 ## 云原生计算基金会 KubeArmor 是云原生计算基金会的 [沙箱项目](https://www.cncf.io/projects/kubearmor/)。  ## 路线图 KubeArmor 的路线图通过 [KubeArmor Projects](https://github.com/orgs/kubearmor/projects?query=is%3Aopen) 进行跟踪
标签:AppArmor, Chrome Headless, CNCF, Docker镜像, EVTX分析, EVTX分析, HTTP工具, JSONLines, Kubernetes安全, Lerna, LSM, SELinux, Web截图, web渗透, 人工智能安全, 入侵防御, 合规性, 子域名突变, 安全策略管理, 容器安全, 工作负载保护, 文件访问控制, 日志审计, 最小权限, 沙箱, 策略执行, 系统加固, 网络安全审计, 网络策略, 行为监控, 请求拦截, 足迹分析, 进程隔离, 零信任