aquasecurity/trivy-action
GitHub: aquasecurity/trivy-action
Trivy 的 GitHub Action 封装,用于在 CI 流水线中自动化扫描容器镜像、代码和 IaC 配置的安全漏洞。
Stars: 1239 | Forks: 296
# Trivy Action
[][release]
[][marketplace]
[][license]
## 目录
* [用法](#usage)
* [扫描 CI Pipeline](#scan-ci-pipeline)
* [扫描 CI Pipeline (使用 Trivy 配置)](#scan-ci-pipeline-w-trivy-config)
* [缓存](#cache)
* [Trivy 设置](#trivy-setup)
* [扫描 Tarball](#scanning-a-tarball)
* [配合模板使用 Trivy](#using-trivy-with-templates)
* [配合 GitHub Code Scanning 使用 Trivy](#using-trivy-with-github-code-scanning)
* [使用 Trivy 扫描 Git 仓库](#using-trivy-to-scan-your-git-repo)
* [使用 Trivy 扫描 rootfs 目录](#using-trivy-to-scan-your-rootfs-directories)
* [使用 Trivy 扫描基础设施即代码](#using-trivy-to-scan-infrastructure-as-code)
* [使用 Trivy 生成 SBOM](#using-trivy-to-generate-sbom)
* [使用 Trivy 扫描私有仓库](#using-trivy-to-scan-your-private-registry)
* [在未启用 code scanning 的情况下使用 Trivy](#using-trivy-if-you-dont-have-code-scanning-enabled)
* [自定义配置](#customizing)
* [输入参数](#inputs)
* [环境变量](#environment-variables)
* [Trivy 配置文件](#trivy-config-file)
## 用法
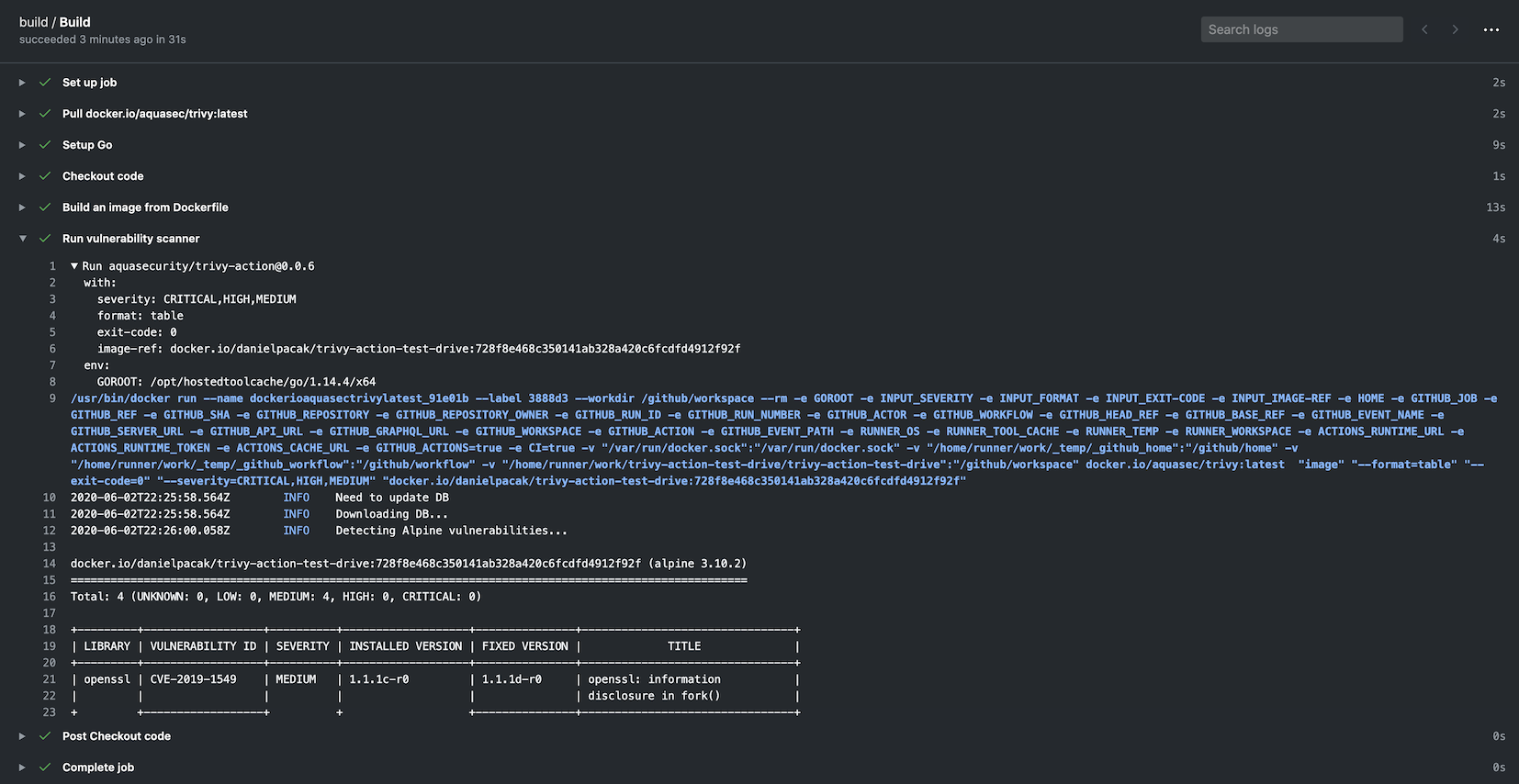
### 扫描 CI Pipeline
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Build an image from Dockerfile
run: docker build -t docker.io/my-organization/my-app:${{ github.sha }} .
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'table'
exit-code: '1'
ignore-unfixed: true
vuln-type: 'os,library'
severity: 'CRITICAL,HIGH'
```
### 扫描 CI Pipeline (使用 Trivy 配置)
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner in fs mode
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'fs'
scan-ref: '.'
trivy-config: trivy.yaml
```
在这种情况下,`trivy.yaml` 是作为仓库一部分提交的 YAML 配置。Trivy 官网提供了详细信息,示例如下:
```
format: json
exit-code: 1
severity: CRITICAL
secret:
config: config/trivy/secret.yaml
```
可以在 `trivy.yaml` 文件中定义所有选项。通过 Action 指定单个选项是为了向后兼容。以下内容必须定义,因为它们无法通过配置文件定义:
- `scan-ref`:如果使用 `fs, repo` 扫描。
- `image-ref`:如果使用 `image` 扫描。
- `scan-type`:用于定义扫描类型,例如 `image`、`fs`、`repo` 等。
#### 选项优先顺序
Trivy 使用 [Viper](https://github.com/spf13/viper),它定义了选项的优先顺序。顺序如下:
- GitHub Action 标志
- 环境变量
- 配置文件
- 默认值
### 缓存
如果在扫描过程中下载了[漏洞数据库](https://github.com/aquasecurity/trivy-db)、[Java 数据库](https://github.com/aquasecurity/trivy-java-db)和[检查包](https://github.com/aquasecurity/trivy-checks),该 Action 具有缓存和恢复它们的内置功能。
默认情况下,缓存存储在 `$GITHUB_WORKSPACE/.cache/trivy` 目录中。
缓存在扫描开始前恢复,在扫描结束后保存。
它在底层使用 [actions/cache](https://github.com/actions/cache),但需要配置的设置更少。
缓存输入是可选的,并且默认情况下缓存是开启的。
#### 禁用缓存
如果你想禁用缓存,请将 `cache` 输入设置为 `false`,但我们建议保持启用以避免速率限制问题。
```
- name: Run Trivy scanner without cache
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'fs'
scan-ref: '.'
cache: 'false'
```
#### 更新默认分支中的缓存
请注意,GitHub Actions 中分支之间的[缓存访问有限制](https://docs.github.com/en/actions/writing-workflows/choosing-what-your-workflow-does/caching-dependencies-to-speed-up-workflows#restrictions-for-accessing-a-cache)。
默认情况下,工作流可以访问和恢复在当前分支或默认分支(通常是 `main` 或 `master`)中创建的缓存。
如果你需要跨分支共享缓存,可能需要在默认分支中创建缓存并在当前分支中恢复它。
为了优化你的工作流,你可以设置一个 cron 任务来定期更新默认分支中的缓存。
这允许后续扫描使用缓存的数据库而无需再次下载。
```
# 注意:此 workflow 仅更新缓存。你应该为实际的 Trivy 扫描创建一个单独的 workflow。
# 在你的扫描 workflow 中,设置 TRIVY_SKIP_DB_UPDATE=true 和 TRIVY_SKIP_JAVA_DB_UPDATE=true。
name: Update Trivy Cache
on:
schedule:
- cron: '0 0 * * *' # Run daily at midnight UTC
workflow_dispatch: # Allow manual triggering
jobs:
update-trivy-db:
runs-on: ubuntu-latest
steps:
- name: Setup oras
uses: oras-project/setup-oras@v1
- name: Get current date
id: date
run: echo "date=$(date +'%Y-%m-%d')" >> $GITHUB_OUTPUT
- name: Download and extract the vulnerability DB
run: |
mkdir -p $GITHUB_WORKSPACE/.cache/trivy/db
oras pull ghcr.io/aquasecurity/trivy-db:2
tar -xzf db.tar.gz -C $GITHUB_WORKSPACE/.cache/trivy/db
rm db.tar.gz
- name: Download and extract the Java DB
run: |
mkdir -p $GITHUB_WORKSPACE/.cache/trivy/java-db
oras pull ghcr.io/aquasecurity/trivy-java-db:1
tar -xzf javadb.tar.gz -C $GITHUB_WORKSPACE/.cache/trivy/java-db
rm javadb.tar.gz
- name: Cache DBs
uses: actions/cache/save@v4
with:
path: ${{ github.workspace }}/.cache/trivy
key: cache-trivy-${{ steps.date.outputs.date }}
```
运行扫描时,设置环境变量 `TRIVY_SKIP_DB_UPDATE` 和 `TRIVY_SKIP_JAVA_DB_UPDATE` 以跳过下载过程。
```
- name: Run Trivy scanner without downloading DBs
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'image'
scan-ref: 'myimage'
env:
TRIVY_SKIP_DB_UPDATE: true
TRIVY_SKIP_JAVA_DB_UPDATE: true
```
### Trivy 设置
默认情况下,该 Action 将 [`aquasecurity/setup-trivy`](https://github.com/aquasecurity/setup-trivy) 作为第一步调用,
它会安装由 `version` 输入指定的 `trivy` 版本。如果你已经通过其他方式安装了 `trivy`,
例如直接调用 `aquasecurity/setup-trivy`,或者多次调用此 Action,则可以使用
`skip-setup-trivy` 输入来禁用此步骤。
#### 手动设置 Trivy
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Manual Trivy Setup
uses: aquasecurity/setup-trivy@v0.2.0
with:
cache: true
version: v0.69.3
- name: Run Trivy vulnerability scanner in repo mode
uses: aquasecurity/trivy-action@master
with:
scan-type: 'fs'
ignore-unfixed: true
format: 'sarif'
output: 'trivy-results.sarif'
severity: 'CRITICAL'
skip-setup-trivy: true
```
#### 多次调用 Trivy Action 时跳过设置
另一个常见的用例是构建多次调用此 Action,在这种情况下,我们可以在后续调用中将 `skip-setup-trivy` 设置为
`true`,例如:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
test:
runs-on: ubuntu-latest
permissions:
contents: read
steps:
- name: Check out Git repository
uses: actions/checkout@v4
# The first call to the action will invoke setup-trivy and install trivy
- name: Generate Trivy Vulnerability Report
uses: aquasecurity/trivy-action@master
with:
scan-type: "fs"
output: trivy-report.json
format: json
scan-ref: .
exit-code: 0
- name: Upload Vulnerability Scan Results
uses: actions/upload-artifact@v4
with:
name: trivy-report
path: trivy-report.json
retention-days: 30
- name: Fail build on High/Criticial Vulnerabilities
uses: aquasecurity/trivy-action@master
with:
scan-type: "fs"
format: table
scan-ref: .
severity: HIGH,CRITICAL
ignore-unfixed: true
exit-code: 1
# On a subsequent call to the action we know trivy is already installed so can skip this
skip-setup-trivy: true
```
#### 使用非默认令牌安装 Trivy
GitHub Enterprise Server (GHES) 对 `https://github.com` 服务器使用无效的 `github.token`。
因此,你无法使用 `setup-trivy` Action 安装 `Trivy`。
要解决此问题,你需要使用 `token-setup-trivy` 输入覆盖 `setup-trivy` 的令牌:
```
- name: Run Trivy scanner without cache
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'fs'
scan-ref: '.'
token-setup-trivy: ${{ secrets.GITHUB_PAT }}
```
GitHub 甚至为类似情况提供了 [create-github-app-token](https://github.com/actions/create-github-app-token)。
### 扫描 Tarball
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Generate tarball from image
run: |
docker pull
docker save -o vuln-image.tar
- name: Run Trivy vulnerability scanner in tarball mode
uses: aquasecurity/trivy-action@0.33.1
with:
input: /github/workspace/vuln-image.tar
severity: 'CRITICAL,HIGH'
```
### 配合模板使用 Trivy
该 Action 支持 [Trivy 模板][trivy-templates]。
使用 `template` 输入指定模板文件的路径(记得给路径加上 `@` 前缀)。
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: "fs"
scan-ref: .
format: 'template'
template: "@path/to/my_template.tpl"
```
#### 默认模板
Trivy 拥有[默认模板][trivy-default-templates]。
默认情况下,`setup-trivy` 将它们安装到 `$HOME/.local/bin/trivy-bin/contrib` 目录中。
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: "fs"
scan-ref: .
format: 'template'
template: "@$HOME/.local/bin/trivy-bin/contrib/html.tpl"
```
### 配合 GitHub Code Scanning 使用 Trivy
如果你有可用的 [GitHub code scanning](https://docs.github.com/en/github/finding-security-vulnerabilities-and-errors-in-your-code/about-code-scanning),你可以按如下方式使用 Trivy 作为扫描工具:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Build an image from Dockerfile
run: |
docker build -t docker.io/my-organization/my-app:${{ github.sha }} .
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
你可以在这里找到更深入的示例:https://github.com/aquasecurity/trivy-sarif-demo/blob/master/.github/workflows/scan.yml
如果你想在 Trivy 扫描返回非零退出代码时仍将 SARIF 结果上传到 GitHub Code scanning,可以在上传步骤中添加以下内容:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Build an image from Dockerfile
run: |
docker build -t docker.io/my-organization/my-app:${{ github.sha }} .
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
if: always()
with:
sarif_file: 'trivy-results.sarif'
```
更多详情请参阅:https://docs.github.com/en/actions/learn-github-actions/expressions#always
### 使用 Trivy 扫描 Git 仓库
也可以使用 Trivy 内置的 repo 扫描功能扫描你的 git 仓库。如果你想在每个 PR 打开时将 Trivy 作为构建时检查运行,这会很方便。这有助于你识别每个 PR 可能引入的潜在漏洞。
如果你有可用的 [GitHub code scanning](https://docs.github.com/en/github/finding-security-vulnerabilities-and-errors-in-your-code/about-code-scanning),你可以按如下方式使用 Trivy 作为扫描工具:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner in repo mode
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'fs'
ignore-unfixed: true
format: 'sarif'
output: 'trivy-results.sarif'
severity: 'CRITICAL'
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
### 使用 Trivy 扫描 rootfs 目录
也可以使用 Trivy 内置的 rootfs 扫描功能扫描你的 rootfs 目录。如果你希望在每个 PR 打开时将 Trivy 作为构建时检查运行,这会很方便。这有助于你识别每个 PR 可能引入的潜在漏洞。
如果你有可用的 [GitHub code scanning](https://docs.github.com/en/github/finding-security-vulnerabilities-and-errors-in-your-code/about-code-scanning),你可以按如下方式使用 Trivy 作为扫描工具:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner with rootfs command
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'rootfs'
scan-ref: 'rootfs-example-binary'
ignore-unfixed: true
format: 'sarif'
output: 'trivy-results.sarif'
severity: 'CRITICAL'
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
### 使用 Trivy 扫描基础设施即代码
也可以使用 Trivy 内置的 repo 扫描功能扫描你的 IaC 仓库。
如果你希望在每个 PR 打开时将 Trivy 作为构建时检查运行,这会很方便。
这有助于你识别每个 PR 可能引入的潜在漏洞。
如果你有可用的 [GitHub code scanning](https://docs.github.com/en/github/finding-security-vulnerabilities-and-errors-in-your-code/about-code-scanning),你可以按如下方式使用 Trivy 作为扫描工具:
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner in IaC mode
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'config'
hide-progress: true
format: 'sarif'
output: 'trivy-results.sarif'
exit-code: '1'
severity: 'CRITICAL,HIGH'
- name: Upload Trivy scan results to GitHub Security tab
if: always()
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
**注意**:如果你的 Terraform 配置包含私有模块,请配置 Git 以便与托管它们的仓库进行身份验证。
这可以通过在你的 CI 工作流中添加一个设置访问权限的步骤来完成,例如使用个人访问令牌 (PAT) 或 SSH 密钥:
```
- name: Configure Git for private modules
run: |
git config --global url."https://$GITHUB_USER:$PRIVATE_REPO_TOKEN@github.com/".insteadOf "https://github.com/"
env:
GITHUB_USER: ${{ github.actor }}
PRIVATE_REPO_TOKEN: ${{ secrets.PRIVATE_REPO_TOKEN }}
```
这确保 Trivy 可以下载私有模块。
### 使用 Trivy 生成 SBOM
Trivy 可以为你的依赖项生成 [SBOM](https://www.aquasec.com/cloud-native-academy/supply-chain-security/sbom/) 并将其提交给像 [GitHub Dependency Graph](https://docs.github.com/en/code-security/supply-chain-security/understanding-your-software-supply-chain/about-the-dependency-graph) 这样的消费者。
[将 SBOM 发送到 GitHub](https://docs.github.com/en/code-security/supply-chain-security/understanding-your-software-supply-chain/using-the-dependency-submission-api) 的功能仅在你当前在[仓库中启用了](https://docs.github.com/en/code-security/supply-chain-security/understanding-your-software-supply-chain/configuring-the-dependency-graph#enabling-and-disabling-the-dependency-graph-for-a-private-repository) GitHub Dependency Graph 时才可用。
为了将结果发送到 GitHub Dependency Graph,你需要创建一个 [GitHub PAT](https://docs.github.com/en/authentication/keeping-your-account-and-data-secure/creating-a-personal-access-token) 或使用 [GitHub installation access token](https://docs.github.com/en/actions/security-guides/automatic-token-authentication)(也称为 `GITHUB_TOKEN`):
```
---
name: Generate SBOM
on:
push:
branches:
- main
## GITHUB_TOKEN 身份验证,仅在不打算使用 PAT 时添加
permissions:
contents: write
jobs:
generate-sbom:
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy in GitHub SBOM mode and submit results to Dependency Graph
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: 'fs'
format: 'github'
output: 'dependency-results.sbom.json'
scan-ref: '.'
github-pat: ${{ secrets.GITHUB_TOKEN }} # or ${{ secrets.github_pat_name }} if you're using a PAT
```
扫描镜像时,你可能希望解析实际的输出 JSON,因为 Github Dependency 不会显示所有详细信息,例如每个依赖项的文件路径。
你可以将报告作为 artifact 上传并下载它,例如使用 [upload-artifact action](https://github.com/actions/upload-artifact):
```
---
name: Generate SBOM
on:
push:
branches:
- main
## GITHUB_TOKEN 身份验证,仅在不打算使用 PAT 时添加
permissions:
contents: write
jobs:
generate-sbom:
runs-on: ubuntu-latest
steps:
- name: Scan image in a private registry
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: "private_image_registry/image_name:image_tag"
scan-type: image
format: 'github'
output: 'dependency-results.sbom.json'
github-pat: ${{ secrets.GITHUB_TOKEN }} # or ${{ secrets.github_pat_name }} if you're using a PAT
severity: "MEDIUM,HIGH,CRITICAL"
scanners: "vuln"
env:
TRIVY_USERNAME: "image_registry_admin_username"
TRIVY_PASSWORD: "image_registry_admin_password"
- name: Upload trivy report as a Github artifact
uses: actions/upload-artifact@v4
with:
name: trivy-sbom-report
path: '${{ github.workspace }}/dependency-results.sbom.json'
retention-days: 20 # 90 is the default
```
### 使用 Trivy 扫描私有仓库
也可以使用 Trivy 内置的镜像扫描功能扫描你的私有仓库。你所要做的就是设置 ENV 变量。
#### Docker Hub 仓库
Docker Hub 需要 `TRIVY_USERNAME` 和 `TRIVY_PASSWORD`。
从公共仓库下载时不需要设置 ENV 变量。
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF results to the GitHub Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
env:
TRIVY_USERNAME: Username
TRIVY_PASSWORD: Password
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
#### AWS ECR (Elastic Container Registry)
Trivy 使用 AWS SDK。你不需要安装 `aws` CLI 工具。
你可以使用 [AWS CLI 的 ENV Vars][env-var]。
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'aws_account_id.dkr.ecr.region.amazonaws.com/imageName:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
env:
AWS_ACCESS_KEY_ID: key_id
AWS_SECRET_ACCESS_KEY: access_key
AWS_DEFAULT_REGION: us-west-2
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
#### GCR (Google Container Registry)
Trivy 使用 Google Cloud SDK。你不需要安装 `gcloud` 命令。
如果你想使用目标项目的仓库,可以通过 `GOOGLE_APPLICATION_CREDENTIAL` 进行设置。
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
env:
GOOGLE_APPLICATION_CREDENTIAL: /path/to/credential.json
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
#### 自托管
BasicAuth 服务器需要 `TRIVY_USERNAME` 和 `TRIVY_PASSWORD`。
如果你想使用 80 端口,请使用 NonSSL `TRIVY_NON_SSL=true`
```
name: build
on:
push:
branches:
- main
pull_request:
jobs:
build:
name: Build
runs-on: ubuntu-24.04
permissions:
contents: read # Required to checkout and read repo files
security-events: write # Required to upload SARIF files to Security tab
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Run Trivy vulnerability scanner
uses: aquasecurity/trivy-action@0.33.1
with:
image-ref: 'docker.io/my-organization/my-app:${{ github.sha }}'
format: 'sarif'
output: 'trivy-results.sarif'
env:
TRIVY_USERNAME: Username
TRIVY_PASSWORD: Password
- name: Upload Trivy scan results to GitHub Security tab
uses: github/codeql-action/upload-sarif@v4
with:
sarif_file: 'trivy-results.sarif'
```
### 在未启用 code scanning 的情况下使用 Trivy
也可以在工作流摘要中浏览扫描结果。
此步骤对于没有 [GitHub Advanced Security](https://docs.github.com/en/get-started/learning-about-github/about-github-advanced-security) 许可证的私有仓库特别有用。
```
- name: Run Trivy scanner
uses: aquasecurity/trivy-action@0.33.1
with:
scan-type: config
hide-progress: true
output: trivy.txt
- name: Publish Trivy Output to Summary
run: |
if [[ -s trivy.txt ]]; then
{
echo "### Security Output"
echo ""
} >> $GITHUB_STEP_SUMMARY
fi
```
## 自定义配置
配置优先级:
- [输入参数](#inputs)
- [环境变量](#environment-variables)
- [Trivy 配置文件](#trivy-config-file)
- 默认值
### 输入参数
以下输入可用作 `step.with` 键:
| Name | Type | Default | Description |
|------------------------------|---------|------------------------------------|------------------------------------------------------------------------------------------------------------------------------------------------------------------|
| `scan-type` | String | `image` | 扫描类型,例如 `image` 或 `fs` |
| `input` | String | | Tar 引用,例如 `alpine-latest.tar` |
| `image-ref` | String | | 镜像引用,例如 `alpine:3.10.2` |
| `scan-ref` | String | `/github/workspace/` | 扫描引用,例如 `/github/workspace/` 或 `.` |
| `format` | String | `table` | 输出格式 (`table`, `json`, `template`, `sarif`, `cyclonedx`, `spdx`, `spdx-json`, `github`, `cosign-vuln`) |
| `template` | String | | 输出模板 (`@$HOME/.local/bin/trivy-bin/contrib/gitlab.tpl`, `@$HOME/.local/bin/trivy-bin/contrib/junit.tpl`) |
| `tf-vars` | String | | Terraform 变量文件的路径 |
| `output` | String | | 将结果保存到文件 |
| `exit-code` | String | `0` | 发现指定漏洞时的退出代码 |
| `ignore-unfixed` | Boolean | false | 忽略未修补/未修复的漏洞 |
| `vuln-type` | String | `os,library` | 漏洞类型 (os,library) |
| `severity` | String | `UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL` | 要扫描和显示的漏洞严重级别 |
| `skip-dirs` | String | | 跳过遍历的目录列表(以逗号分隔) |
| `skip-files` | String | | 跳过遍历的文件列表(以逗号分隔) |
| `cache-dir` | String | `$GITHUB_WORKSPACE/.cache/trivy` | 缓存目录。注意:此值无法通过 `trivy.yaml` 配置。 |
| `timeout` | String | `5m0s` | 扫描超时时长 |
| `ignore-policy` | String | | 使用 OPA rego 语言过滤漏洞 |
| `hide-progress` | String | `false` | 隐藏进度条和日志输出 |
| `list-all-pkgs` | String | | 输出所有包,无论是否有漏洞 |
| `scanners` | String | `vuln,secret` | 要检测的安全问题列表(以逗号分隔)(`vuln`,`secret`,`misconfig`,`license`) |
| `trivyignores` | String | 仓库内一个或多个 `.trivyignore` 文件的相对路径列表(以逗号分隔),或单个 `.trivyignore.yaml` 文件。 |
| `trivy-config` | String | | trivy.yaml 配置文件的路径 |
| `github-pat` | String | | 用于将 SBOM 扫描结果发送到 GitHub Dependency Graph 的身份验证令牌。可以是 GitHub 个人访问令牌 (PAT) 或 GITHUB_TOKEN |
| `limit-severities-for-sarif` | Boolean | false | 默认情况下,*SARIF* 格式强制输出所有漏洞,无论配置的严重级别如何。要覆盖此行为,请将此参数设置为 **true** |
| `docker-host` | String | | 默认设置为 `unix://var/run/docker.sock`,但可以更新以帮助处理容器化基础设施值(需要 `unix:/` 或其他前缀) |
| `version` | String | `v0.69.3` | 要使用的 Trivy 版本,例如 `latest` 或 `v0.69.3` |
| `skip-setup-trivy` | Boolean | false | 跳过调用 `setup-trivy` Action 来安装 `trivy` |
| `token-setup-trivy` | Boolean | | 覆盖 `setup-trivy` 用于检出 `trivy` 仓库的 `github.token` |
### 环境变量
你可以使用 [Trivy 环境变量][trivy-env] 来设置必要的选项(包括[输入参数](#inputs)不支持的标志,例如 `--secret-config`)。
**注意** 在某些旧版本的 Action 中存在一个错误,导致一次 Action 调用的输入会泄露到后续的 Action 调用中。
这可能导致多次调用 Action 的工作流(例如运行多个扫描,或以不同输出格式运行相同扫描)无法产生所需的输出。
你可以通过查看 GitHub Actions 步骤信息来判断是否属于这种情况,如果你的 Actions 输出中显示的 `env` 部分
包含你未明确设置的 `TRIVY_*` 环境变量,则你可能受到此错误的影响,应该
升级到最新的 Action 版本。
### Trivy 配置文件
当使用 `trivy-config` [输入参数](#inputs)时,你可以使用 [Trivy 配置文件][trivy-config] 设置选项(包括[输入参数](#inputs)不支持的标志,例如 `--secret-config`)。
Click to expand
" echo "" echo '```terraform' cat trivy.txt echo '```' echo "标签:Aquasecurity, CI/CD安全, DevSecOps, GitHub Action, GitHub Marketplace, IaC扫描, Llama, LLM防护, SBOM, Web截图, 上游代理, 云安全监控, 容器安全, 工作流, 文档安全, 日志审计, 硬件无关, 结构化查询, 自动化安全, 请求拦截, 静态分析