F2u0a0d3/takopii
GitHub: F2u0a0d3/takopii
Android 银行木马教育框架,提供 4 个完整 Kotlin 源码样本、107 条检测规则和覆盖 17 个家族的红蓝分析文档,用于移动安全研究与检测工程训练。
Stars: 0 | Forks: 0
# Takopii
### 4 个 Android 银行木马样本。VirusTotal 检出率 0/66。完整 Kotlin 源码。
[](specimens/)
[](specimens/)
[](specimens/)
[](specimens/)
[](detection/yara/)
[](detection/sigma/)
[](detection/frida/)
[](SECURITY.md)
## 包含内容
| # | 样本 | 伪装应用 | 技术 | VT | 家族 |
|:-:|---|---|---|:-:|---|
| 1 | **sms-stealer** | CleanMaster Battery | 短信拦截,OTP 提取 | **0/66** | FluBot, SharkBot V1 |
| 2 | **overlay-banker** | Doc Reader Lite | 55 个模块,17 个家族技术 | **0/66** | Anatsa, SharkBot, Klopatra, Mirax, Vespertine, Drelock, Apex, RatOn, Perseus, FluBot, Herodotus, Crocodilus, Brokewell, FakeCall, TrickMo, ToxicPanda, Cerberus |
| 3 | **dropper** | WiFi Analyzer Pro | 阶段-0 休眠 + 投递 | **0/66** | Anatsa V4 |
| 4 | **stage-1-evasion** | SkyWeather Forecast | 完整的 5 阶段杀伤链 + ATS | **0/66** | Anatsa + SharkBot 组合 |
| 样本 | SHA256 | VT 得分 | |---|---|:-:| | **sms-stealer** | `32f37e555609a3ae9547533563895fe13227aea773dde13d3a3720df84c6e243` | 0/66 | | **overlay-banker** | `33207904cb76210b75904d25aee021ca85d313cc1bf79368c3c6abb523d8e2b0` | 0/66 | | **dropper** | `254465be9b6b2c8aeb951dabe23b6f9032ef149006ef2281b1e63bdb6a9ee7ed` | 0/66 | | **stage-1-evasion** | `af5ceb94cb9d7bc9a37eacca1cf25b066761e24429bda7151d52378e69b01612` | 0/66 | **sms-stealer** (Battery Boost Pro) — 0/66 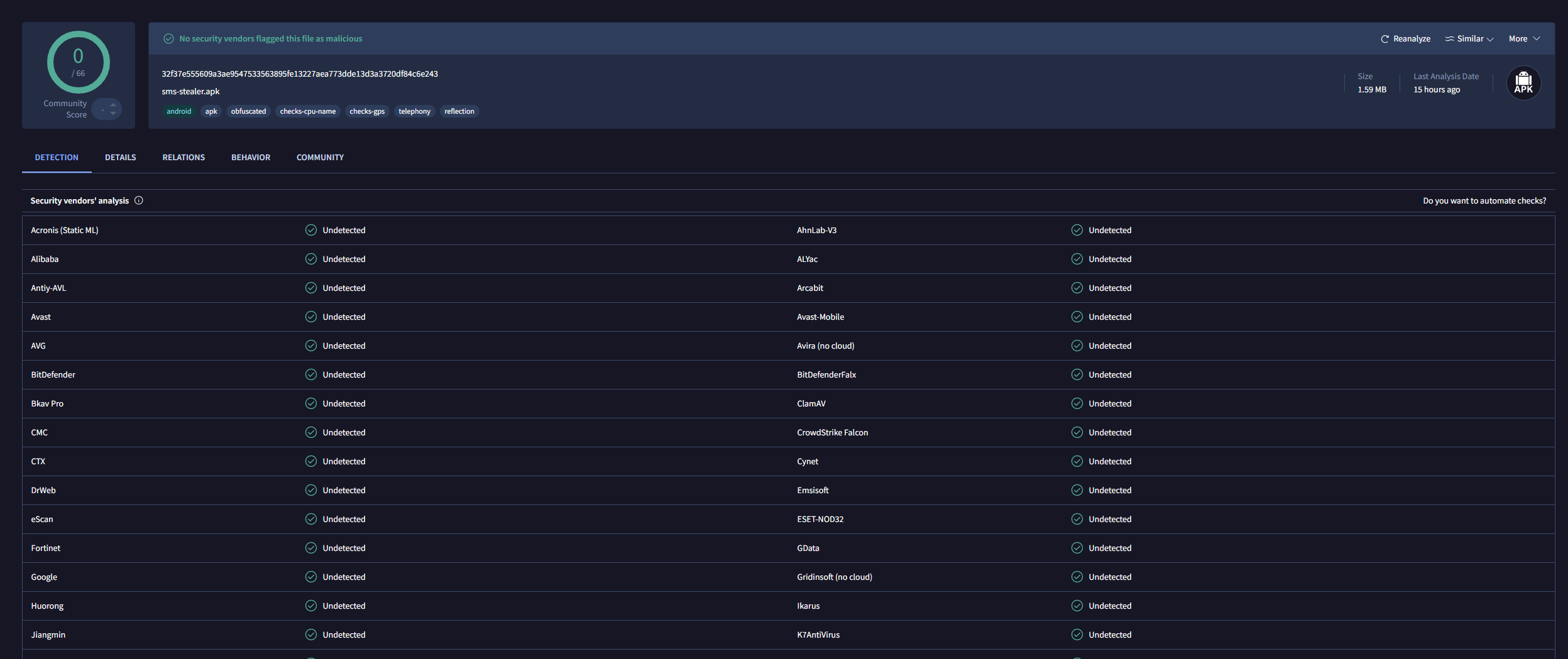 **dropper** (WiFi Analyzer Pro) — 0/66 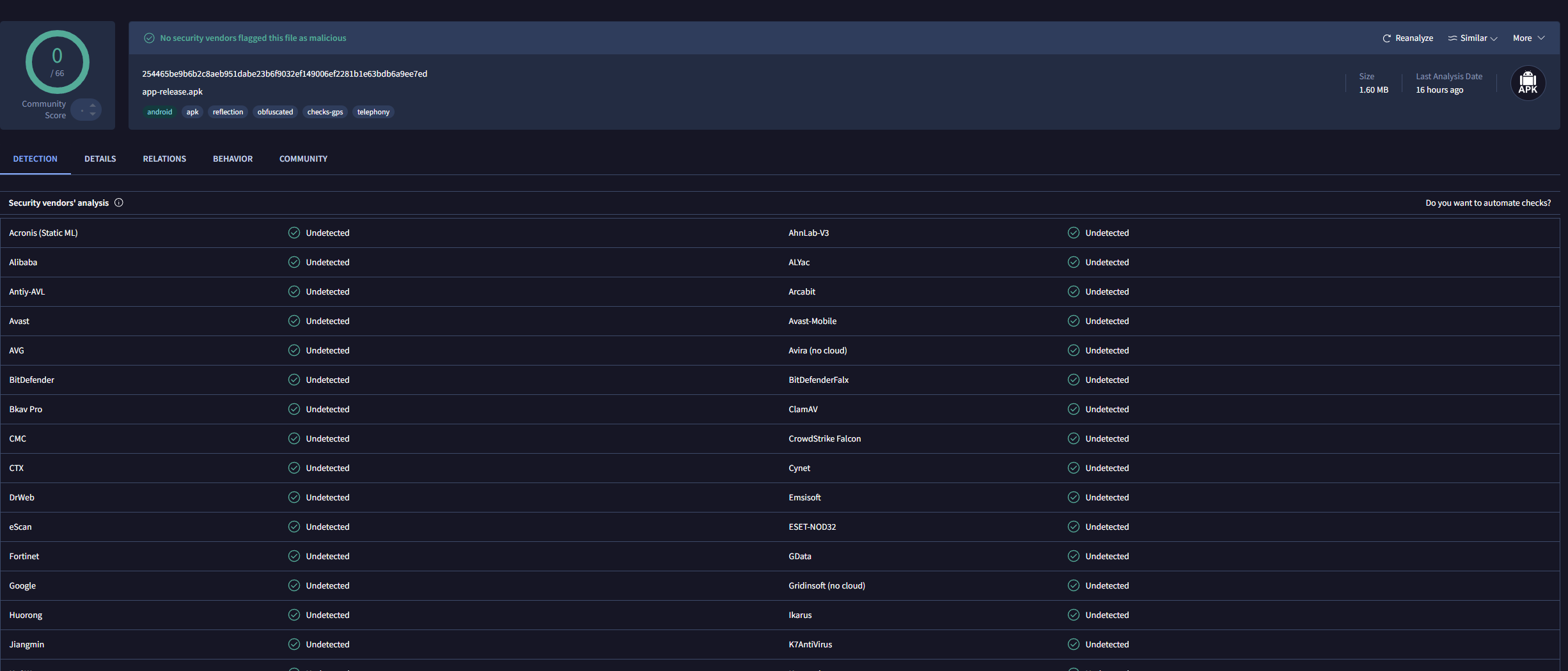 **overlay-banker** (Doc Reader Lite) — 0/66 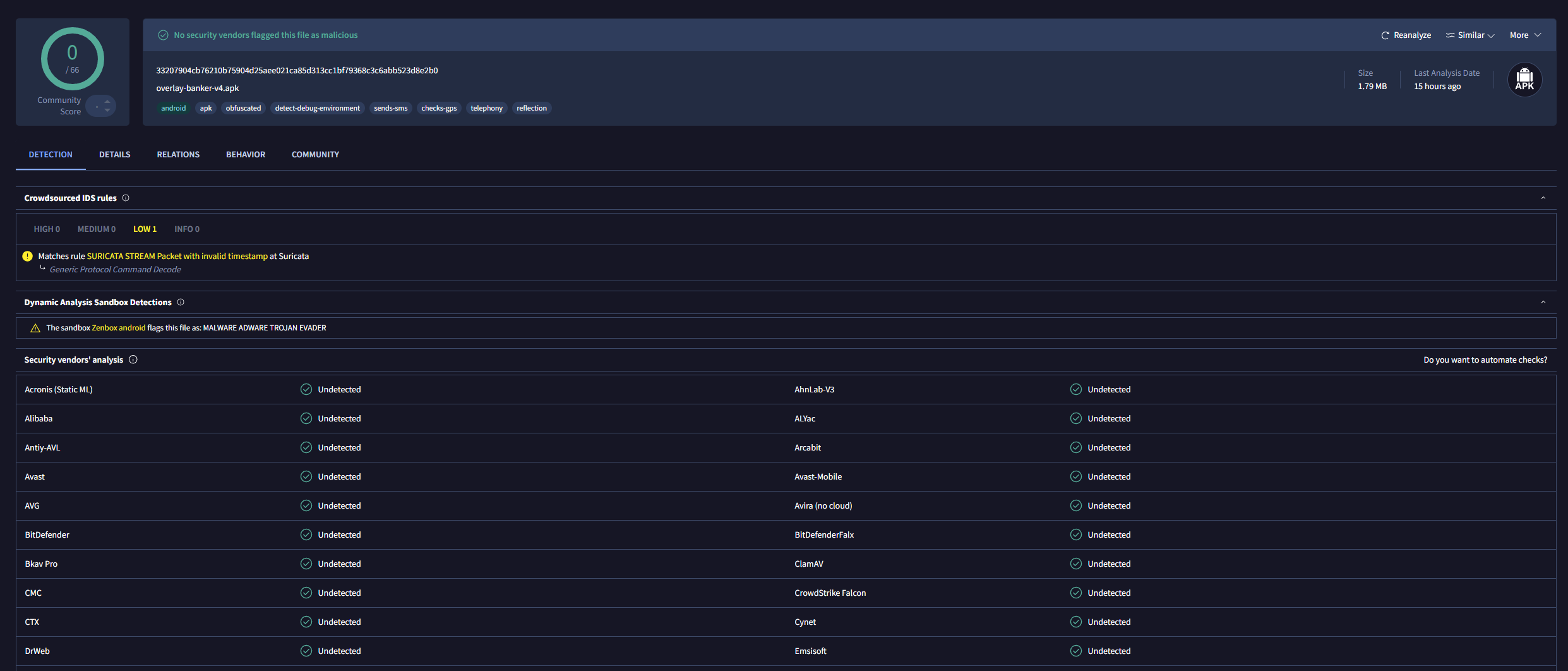 **stage-1-evasion** (SkyWeather Forecast) — 0/66 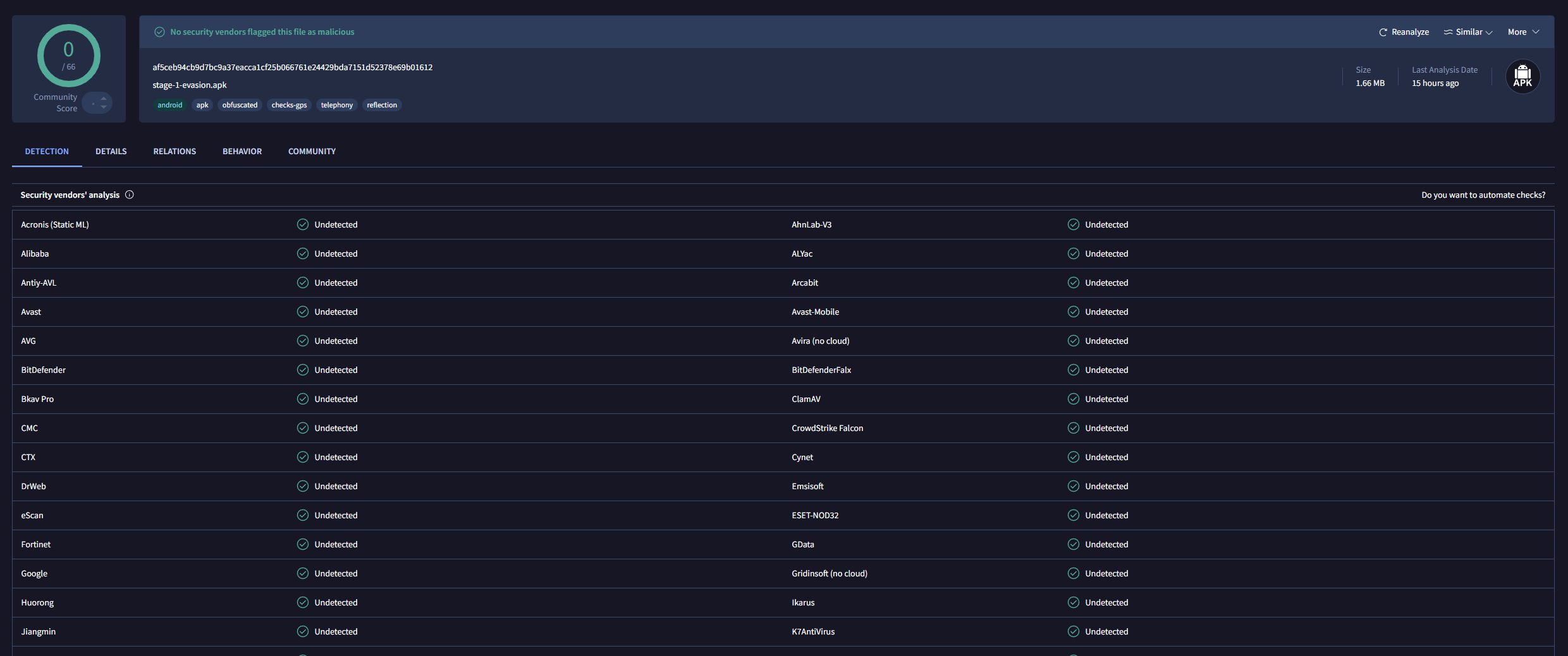 *扫描于 2026-05-14。overlay-banker 被 Zenbox 沙箱标记为“MALWARE ADWARE TROJAN EVADER”——静态 AV 引擎得分仍为 0/66。*
## 杀伤链架构
```
DROPPER (WiFi Analyzer Pro)
│
│ 72h dormancy → config check → payload download
▼
STAGE-1-EVASION (SkyWeather Forecast)
│
┌────────────────┼────────────────┐
│ │ │
EVASION CREDENTIAL EXFIL
Anti-debug (3-layer) A11y capture DGA fallback
Anti-emulator (14) Overlay (2032) 4-stage loader
Anti-Frida (5-vector) OTP dual-path WorkManager beacon
intArrayOf encoding ATS auto-fraud Yamux multiplexer
│ │ │
└────────────────┼────────────────┘
│
OVERLAY-BANKER (Doc Reader Lite)
53 modules
┌─────────────┬──────────────────┐
│ STEALER │ RAT / CONTROL │
│ NFC ghost │ Screen stream │
│ Hidden VNC │ Audio record │
│ SOCKS5 proxy│ Camera capture │
│ SSO hijack │ Remote shell │
│ TEE offload │ Touch logging │
│ SMS worm │ Factory reset │
├─────────────┼──────────────────┤
│ EVASION │ SOCIAL ENGINEER │
│ Per-build │ Call forwarding │
│ Behavior │ Contact inject │
│ Anti-* │ Black screen │
│ Play Integ │ USSD execution │
│ Obfuscation │ Auth capture │
└─────────────┴──────────────────┘
```
## 威胁矩阵
以下每项技术均已**实现为可运行代码**,其来源为关于真实银行木马家族的公开威胁情报报告:
| 技术 | 家族 | 样本 | 源码模块 |
|---|---|---|---|
| 无障碍服务滥用 + 自动点击 | Anatsa V4 | overlay-banker, stage-1 | `BankerA11yService.kt` |
| ATS 自动化转账 | SharkBot V2.8 | stage-1 | `AtsEngine.kt` |
| TYPE_ACCESSIBILITY_OVERLAY (2032) | Anatsa 2025+ | 两者皆有 | `A11yOverlay2032.kt` |
| NLS + 短信双重 OTP 捕获 | Anatsa + SharkBot | 两者皆有 | `OtpNotifService.kt`, `SmsInterceptor.kt` |
| DGA(MD5+日历) | SharkBot V2.8 | 两者皆有 | `Dga.kt`, `DomainResolver.kt` |
| 4 阶段模块化加载器 | Anatsa V4 | 两者皆有 | `ModularLoader.kt`, `PayloadManager.kt` |
| 隐蔽 VNC(MediaProjection) | Klopatra | overlay-banker | `HiddenVnc.kt` |
| Yamux 多路复用 C2 | Klopatra + Mirax | overlay-banker | `YamuxProxy.kt` |
| SOCKS5 住宅代理 | Mirax | overlay-banker | `ResidentialProxy.kt` |
| NFC 幽灵触碰中继 | RatOn | overlay-banker | `NfcRelay.kt` |
| SSO 劫持 + MFA 自动批准 | Vespertine | overlay-banker | `SsoHijacker.kt` |
| TEE/TrustZone 卸载 | Drelock | overlay-banker | `TeeOffload.kt` |
| 每次构建的 AI 混淆 | Apex | overlay-banker | `PerBuildObfuscation.kt` |
| 行为模拟(对数正态抖动) | Herodotus | 两者皆有 | `BehaviorMimicry.kt` |
| BIP39 助记词抓取 | Perseus | overlay-banker | `NoteAppScraper.kt` |
| 短信蠕虫传播 | FluBot | overlay-banker | `SmsWorm.kt` |
| 反调试(3 层) | SharkBot | overlay-banker | `AntiDebug.kt` |
| 反模拟器(14 项检查) | SharkBot | overlay-banker | `AntiEmulator.kt` |
| 反 Frida(5 个向量) | Anatsa + SharkBot | overlay-banker | `AntiFrida.kt` |
| Native JNI 保护 | Klopatra (Virbox) | overlay-banker | `NativeProtect.kt` |
| XOR + AES 字符串加密 | Anatsa | overlay-banker | `StringDecoder.kt` |
| Reflection API 隐藏 | Anatsa | overlay-banker | `ReflectionHider.kt` |
| ContentProvider 预初始化 | Anatsa | overlay-banker | `EarlyInitProvider.kt` |
| WorkManager 15 分钟信标 | Anatsa | 两者皆有 | `WorkManagerBeacon.kt` |
| MediaProjection 自动同意 | Klopatra | overlay-banker | `MediaProjectionAutoConsent.kt` |
| Play Integrity 侦察 | Drelock | overlay-banker | `PlayIntegrityProbe.kt` |
| 屏幕流媒体(MediaProjection→C2) | Brokewell, Albiriox | overlay-banker | `ScreenStreamer.kt` |
| 全局键盘记录(每个输入字段) | Brokewell, TrickMo | overlay-banker | `BankerA11yService.kt` |
| 音频录制(环境麦克风) | Brokewell | overlay-banker | `AudioRecorder.kt` |
| 摄像头捕获(前置 + 后置) | Brokewell, Cerberus | overlay-banker | `CameraCapture.kt` |
| 呼叫转移/劫持(USSD) | FakeCall | overlay-banker | `CallForwarder.kt` |
| 默认拨号器接管 | FakeCall | overlay-banker | `CallForwarder.kt` |
| 通知抑制 | TrickMo, SOVA | overlay-banker | `NotifSuppressor.kt` |
| Google Authenticator TOTP 捕获 | Crocodilus | overlay-banker | `AuthenticatorCapture.kt` |
| 地理位置追踪(GPS+网络) | Brokewell, ToxicPanda | overlay-banker | `GeoTracker.kt` |
| 设备侦察信标 | 所有家族 | overlay-banker | `DeviceRecon.kt` |
| 完整触摸/手势日志记录 | Brokewell | overlay-banker | `TouchLogger.kt` |
| 虚假联系人注入 | Crocodilus 2025 | overlay-banker | `ContactInjector.kt` |
| 黑屏覆盖(RAT 伪装) | Crocodilus, ToxicPanda | overlay-banker | `BlackScreenOverlay.kt` |
| 远程 Shell 执行 | Brokewell, Albiriox | overlay-banker | `RemoteShell.kt` |
| 应用卸载(移除 AV) | TrickMo, SOVA | overlay-banker | `AppManager.kt` |
| 恢复出厂设置(擦除证据) | BRATA | overlay-banker | `RemoteShell.kt` |
## 检测语料库
每次攻击均附带相应的检测规则。共 107 条规则:
```
detection/
├── yara/ 24 rules — static APK/DEX scanning
│ ├── banker-shape.yar Overlay banker multi-vector shape
│ ├── sms-stealer.yar ContentResolver SMS pattern
│ ├── dropper.yar Config-then-download shape
│ ├── dga.yar MD5+Calendar DGA (SharkBot)
│ ├── dcl-antiforensics.yar DexClassLoader + file deletion
│ ├── intarray-encoding.yar Arithmetic string obfuscation
│ ├── frontier.yar 2025-2026 technique shapes
│ ├── rat-capabilities.yar RAT: camera, audio, TOTP, USSD, wipe, AV-kill
│ └── master.yar All rules consolidated
│
├── sigma/ 34 rules — runtime behavioral detection
│ ├── sms-contentresolver.yml SMS access from non-SMS app
│ ├── dropper-download.yml FG service config + binary download
│ ├── overlay-trigger.yml A11y → overlay window creation
│ ├── dcl-antiforensics.yml DexClassLoader + file deletion
│ ├── workmanager-beacon.yml 15-min periodic POST
│ ├── dual-otp-capture.yml NLS + SMS same package
│ ├── ats-killchain.yml Gesture injection during banking
│ ├── a11y-overlay-chain.yml Full overlay trigger pipeline
│ ├── frontier.yml 2025-2026 behavioral patterns
│ ├── rat-behavioral.yml RAT: camera, audio, screen, TOTP, touch, contacts
│ └── master.yml All rules consolidated
│
└── frida/ 48 hooks — dynamic instrumentation
├── sms-monitor.js ContentResolver SMS capture
├── network-monitor.js HTTP/OkHttp exfil intercept
├── overlay-monitor.js WindowManager overlay creation
├── dcl-monitor.js DexClassLoader + DEX capture
├── nls-monitor.js Notification OTP intercept
├── dga-monitor.js MessageDigest DGA detection
├── a11y-monitor.js AccessibilityService dispatch
├── ats-monitor.js Gesture injection + auto-fill
├── clipboard-monitor.js Clipboard polling detection
├── evasion-bypass.js Anti-debug/emulator/Frida defeat
├── frontier-monitor.js 2025-2026 technique hooks
├── rat-monitor.js RAT capabilities (camera, audio, screen, TOTP, USSD, shell, wipe)
└── master-monitor.js All hooks consolidated (48 hooks)
```
### 针对任意 APK 运行检测
```
# 静态扫描
yara -r detection/yara/master.yar suspect.apk
# 针对 Takopii 样本(预计每个 APK 有 9+ 个命中)
yara -r detection/yara/master.yar specimens/overlay-banker/app/build/outputs/apk/release/app-release.apk
# 动态监控
frida -U -l detection/frida/master-monitor.js -f com.suspect.package
# 来自 Frida 输出或 logcat 管道的 Sigma rules 订阅源
```
## 文档(8,352 行)
| 文档 | 行数 | 受众 | 您将获得 |
|---|---|---|---|
| 📕 [REDTEAM-ANALYSIS.md](docs/REDTEAM-ANALYSIS.md) | 4,025 | 攻击方 | 杀伤链、全部 187 个 .kt 文件的带注释源码、规避架构、C2 协议 |
| 📘 [BLUETEAM-DETECTION.md](docs/BLUETEAM-DETECTION.md) | 5,457 | 防御方 | IOC、107 条检测规则(YARA + Sigma + Frida)、网络签名、取证命令 |
| 📗 [VT-EVASION-RESEARCH.md](docs/VT-EVASION-RESEARCH.md) | 949 | 研究人员 | 11 轮 ML 分类器击败日志、构建工件拓扑理论 |
## 快速开始
```
# Clone
git clone https://github.com/F2u0a0d3/takopii.git
cd takopii
# 选项 A:从 Releases 下载预构建的 APK
# → github.com/F2u0a0d3/takopii/releases
# 选项 B:从源代码构建(Android SDK + JDK 17)
cd specimens/sms-stealer && ./gradlew assembleRelease && cd ../..
cd specimens/dropper && ./gradlew assembleRelease && cd ../..
cd specimens/overlay-banker && ./gradlew assembleRelease && cd ../..
# 自行验证 VT 评分
sha256sum specimens/*/app/build/outputs/apk/release/app-release.apk
# 运行检测规则
yara -r detection/yara/master.yar specimens/overlay-banker/app/build/outputs/apk/release/app-release.apk
# 动态分析(已 root 的模拟器 + frida-server)
frida -U -l detection/frida/master-monitor.js -f com.docreader.lite
```
## 教学递进
```
SINGLE SURFACE MULTI-SURFACE DELIVERY FULL KILL CHAIN
┌─────────────────┐ ┌─────────────────┐ ┌─────────────────┐ ┌─────────────────────┐
│ sms-stealer │ │ overlay-banker │ │ dropper + │ │ stage-1-evasion │
│ │ │ │ │ stage-2-payload │ │ │
│ SMS → C2 │ │ A11y → Overlay │ │ Dormancy → │ │ Evasion + ATS + │
│ 1 receiver │ │ → Exfil │ │ Download → │ │ DGA + DCL + Overlay │
│ 3 OTP regexes │ │ 42 modules │ │ DexClassLoader │ │ 14 core modules │
└────────┬────────┘ └────────┬────────┘ └────────┬────────┘ └──────────┬──────────┘
│ │ │ │
v v v v
Learn: intercept Learn: multi- Learn: delivery Learn: full
+ OTP extraction surface wiring chain + evasion composition +
+ overlay UI detection rules
```
## 目标受众
**检测工程师** — 66 个 AV 引擎对实现了 ATS、屏幕流媒体、呼叫劫持、TOTP 捕获、NFC 中继、住宅代理以及 40 多种其他技术的样本评分为 0。这 107 条检测规则旨在针对能够在规避下存活的行为不变量。
**红队人员** — VT 规避研究记录了 ML 分类器如何基于构建工件拓扑(而非应用程序语义)运行。11 轮源码级别的更改对 VT 得分没有任何影响。
**教育工作者** — 从单一维度的 SMS 到完整的 5 阶段杀伤链的渐进复杂性。每个样本都映射到 MITRE ATT&CK 移动端技术。
**RASP 供应商** — 来自独立应用的 TYPE_ACCESSIBILITY_OVERLAY (2032) 绕过了所有被调查的商业 RASP。这一缺陷需要 MTD,而不仅仅是依赖 RASP。
## 这些不是什么
这些不是来自地下论坛的随机窃取器。
- **生产级架构** — 来自 17 个记录家族的 37 项技术,组合成可运行的杀伤链
- **实验室受限** — C2 仅限 RFC1918/环回地址,无公共数据外发
- **研究产物** — 每次攻击均附带相应的检测规则
- **规避已验证** — 0/66 VirusTotal 是经验事实,而非理论
安全约束(环回 C2、自身包过滤器)是**代码级**的,而非架构级的。该架构是生产级的。参见 [SECURITY.md](SECURITY.md)。
## 项目结构
```
takopii/
├── specimens/ 4 specimen APK projects
│ ├── sms-stealer/ 53 .kt — Battery Boost Pro
│ ├── overlay-banker/ 55 .kt — Doc Reader Lite
│ ├── dropper/ 50 .kt — WiFi Analyzer Pro
│ ├── stage-1-evasion/ 42 .kt — SkyWeather Forecast
│ └── stage-2-payload/ 1 .java — Recon module DEX
├── docs/ 8,352 lines of analysis
│ ├── REDTEAM-ANALYSIS.md 4,025 lines — offensive analysis
│ ├── BLUETEAM-DETECTION.md 5,457 lines — detection engineering
│ └── VT-EVASION-RESEARCH.md 949 lines — ML evasion research
├── detection/ 107 standalone detection rules
│ ├── yara/ 24 YARA rules (9 files + master)
│ ├── sigma/ 34 Sigma rules (11 files + master)
│ └── frida/ 13 Frida monitors (13 files + master)
├── SECURITY.md Safety contract + threat model
├── CONTRIBUTING.md How to contribute
└── awesome-android-banker-defense.md Curated resource list
```
## 贡献
参见 [CONTRIBUTING.md](CONTRIBUTING.md)。优先领域:
- **RASP 绕过矩阵填充** — 在真实环境中针对样本对商业 RASP 进行现场测试
- **检测规则改进** — 减少误报,增加新的行为模式
- **新家族覆盖** — 添加来自 2026+ 新兴银行木马家族的技术
- **翻译** — 非英语文档(拉美、亚太地区)
## 参考文献
- OWASP MASTG v1.7.0 / MASVS v2.0.0
- MITRE ATT&CK Mobile
- Cleafy — Anatsa 威胁报告 (2024-2025)
- Threat — Mirax, Vespertine 分析 (2026)
- Zscaler ThreatLabz — SharkBot 分析
- NCC Group — Klopatra VNC 分析
- ESET — Apex 多态性报告 (2026)
## Star 历史
如果这个项目对您的研究、检测工程或教学有帮助——请给它点个 star。单单是这些检测规则就值得您点击一下。
[](https://star-history.com/#F2u0a0d3/takopii&Date)
VirusTotal 证明 — 所有样本 0/66(点击展开)
| 样本 | SHA256 | VT 得分 | |---|---|:-:| | **sms-stealer** | `32f37e555609a3ae9547533563895fe13227aea773dde13d3a3720df84c6e243` | 0/66 | | **overlay-banker** | `33207904cb76210b75904d25aee021ca85d313cc1bf79368c3c6abb523d8e2b0` | 0/66 | | **dropper** | `254465be9b6b2c8aeb951dabe23b6f9032ef149006ef2281b1e63bdb6a9ee7ed` | 0/66 | | **stage-1-evasion** | `af5ceb94cb9d7bc9a37eacca1cf25b066761e24429bda7151d52378e69b01612` | 0/66 | **sms-stealer** (Battery Boost Pro) — 0/66 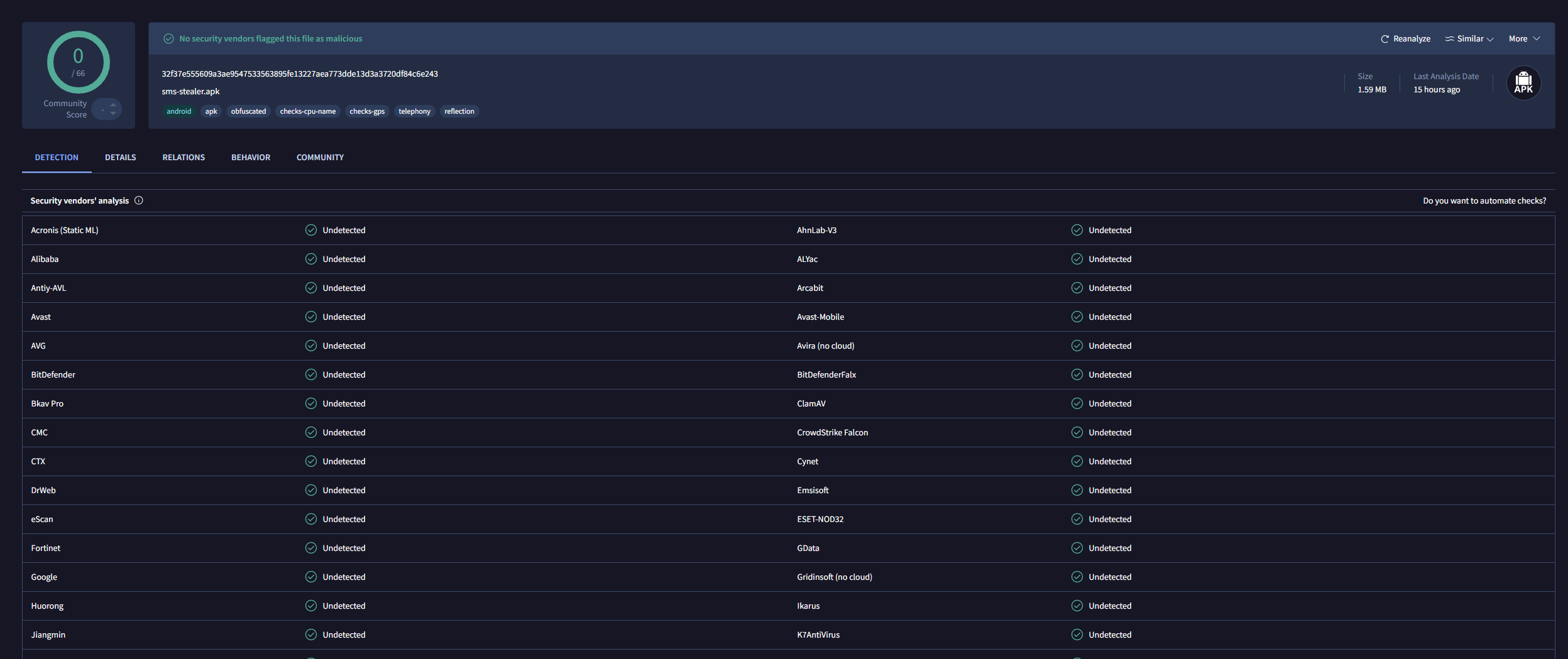 **dropper** (WiFi Analyzer Pro) — 0/66 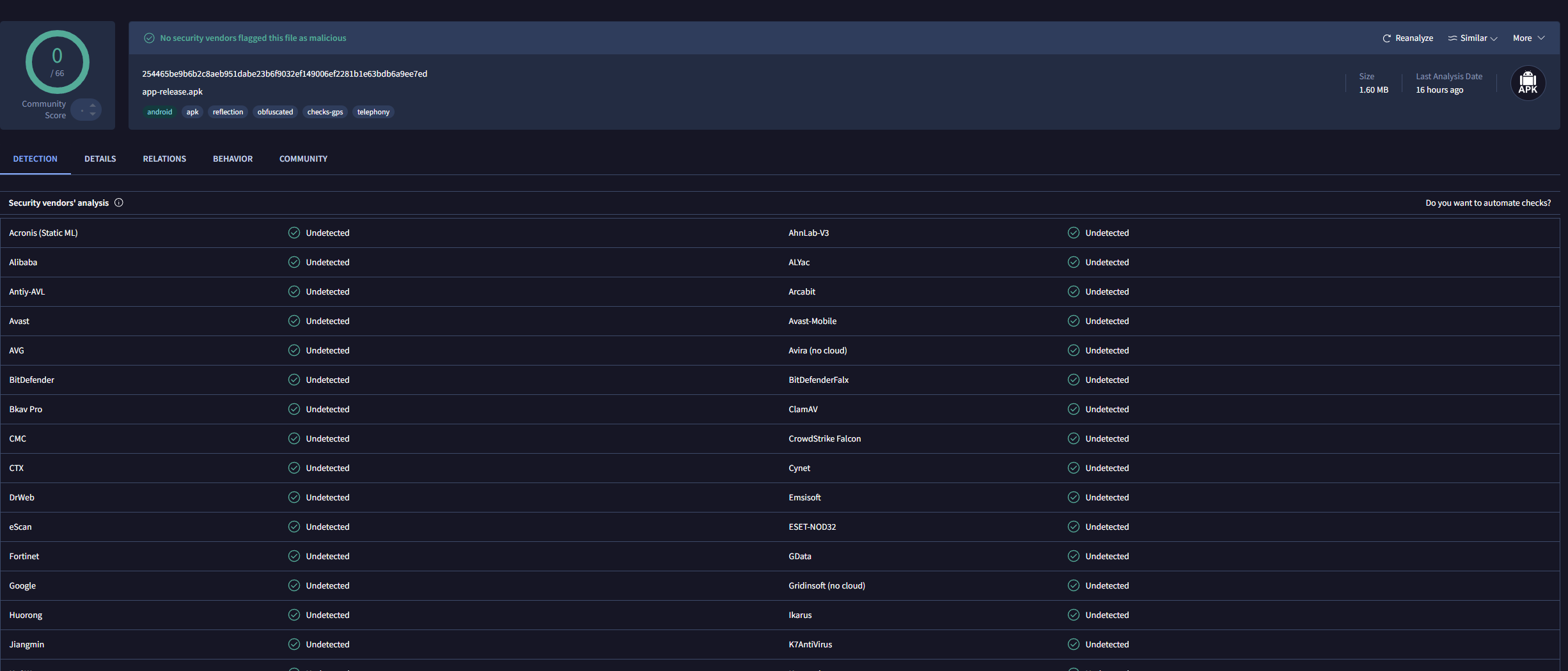 **overlay-banker** (Doc Reader Lite) — 0/66 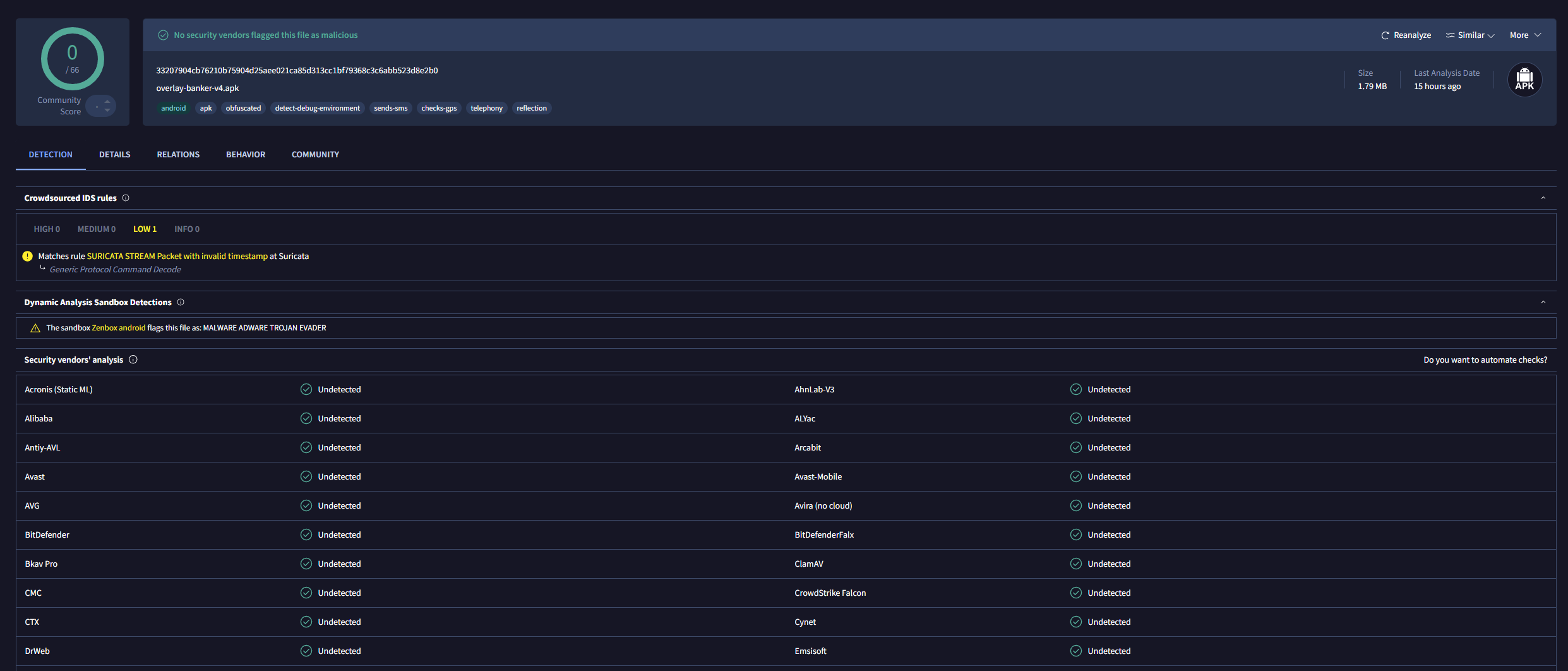 **stage-1-evasion** (SkyWeather Forecast) — 0/66 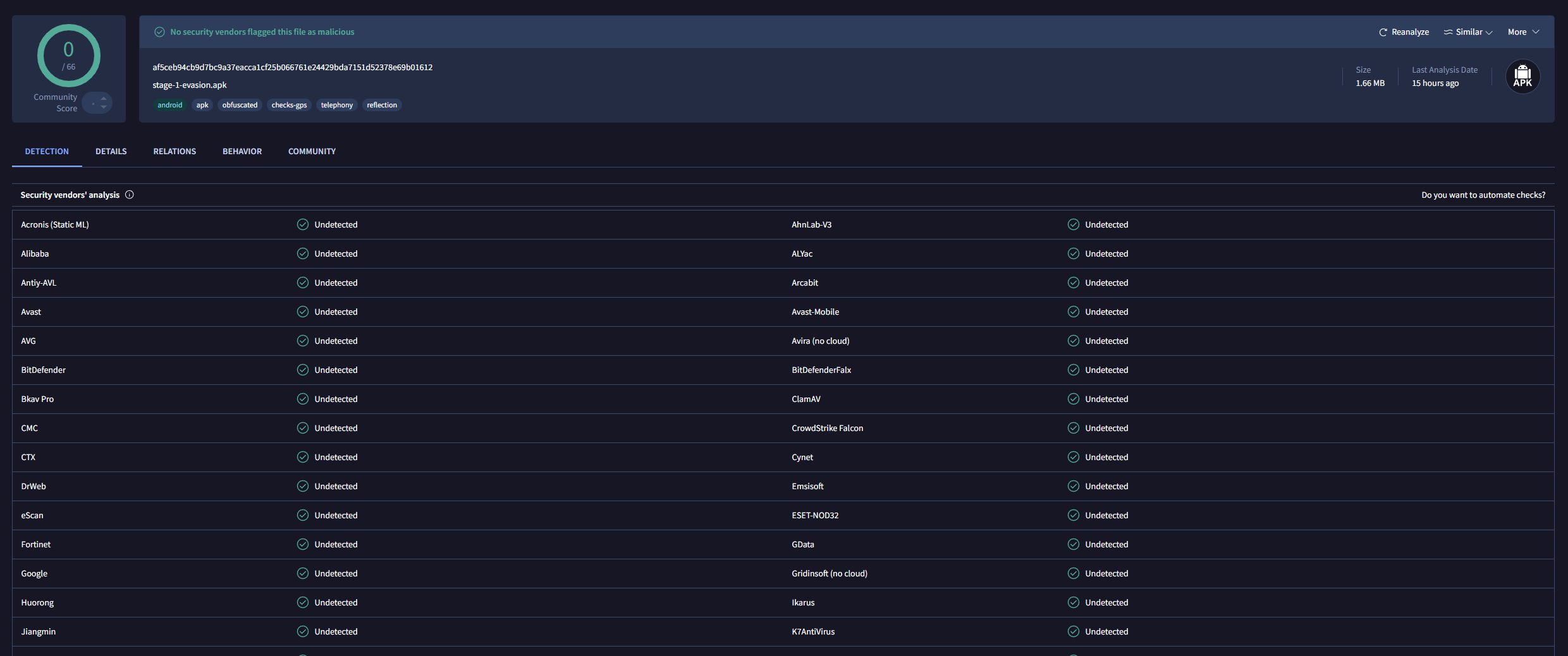 *扫描于 2026-05-14。overlay-banker 被 Zenbox 沙箱标记为“MALWARE ADWARE TROJAN EVADER”——静态 AV 引擎得分仍为 0/66。*
标签:Android恶意软件, ATT&CK矩阵, DNS信息、DNS暴力破解, Frida Hook, Kotlin源码, OTP拦截, Sigma规则, YARA规则, 免杀APK, 后台面板检测, 威胁情报, 安全研究框架, 开发者工具, 搜索语句(dork), 教育框架, 权限绕过, 样本分析, 目录枚举, 目标导入, 短信窃取, 移动安全, 网络安全, 释放器, 金融安全, 钓鱼窗口, 银行木马, 隐私保护