ExploitEoom/CVE-2026-31431
GitHub: ExploitEoom/CVE-2026-31431
针对 Linux 内核 CVE-2026-31431(CopyFail)漏洞的本地提权利用工具集,涵盖漏洞验证、提权利用和受损恢复。
Stars: 2 | Forks: 0
# CVE-2026-31431
 ## CopyFail 标准二进制文件
在
## CopyFail 标准二进制文件
在 获取所有最新 CVE 警报
```
mail :: ~/Desktop/CVE-2026 » file *
exploit: ELF 64-bit LSB executable, x86-64, version 1 (GNU/Linux), statically linked, BuildID[sha1]=9454dbdde0ac2d1a8981c06db89f24a4753ec3b7, for GNU/Linux 3.2.0, not stripped
payload: ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, BuildID[sha1]=9b0f16503767336bc8a821482933c1111aafa23a, stripped
verify_vulneurable: ELF 64-bit LSB executable, x86-64, version 1 (GNU/Linux), statically linked, BuildID[sha1]=a79c6ab7e9d14e60af8d7dfc1c102e3bc93a910b, for GNU/Linux 3.2.0, not stripped
mail :: ~/Desktop/CVE-2026 »
```
## 如何使用
```
git clone https://github.com/ExploitEoom/CVE-2026-31431.git
cd CVE-2026-31431
chmod +x *
./verify_vulneurable
./exploit
```
https://github.com/user-attachments/assets/27e0f28e-0cb8-438d-9fe4-ebd56035adad
## 理解被利用的部分
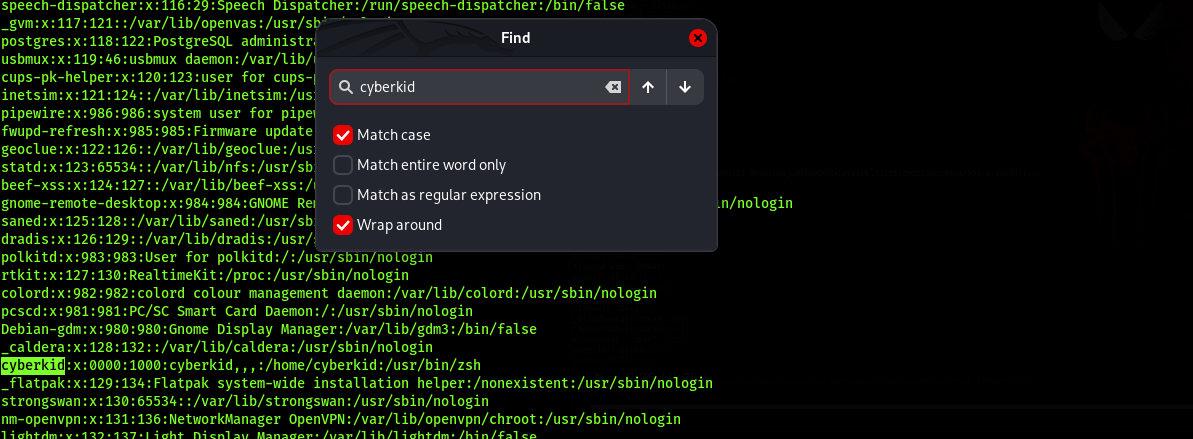
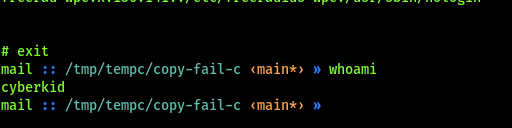
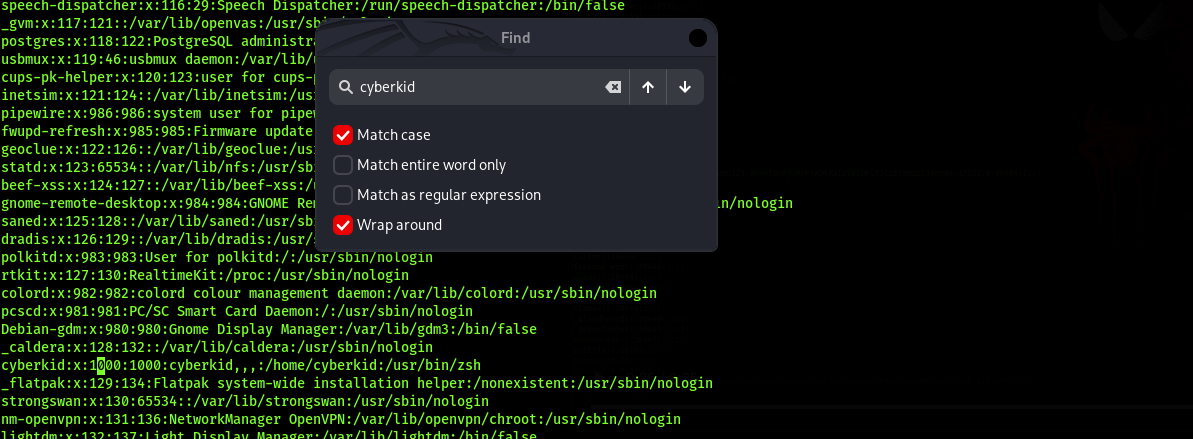
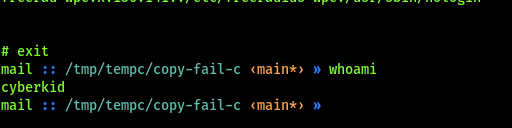
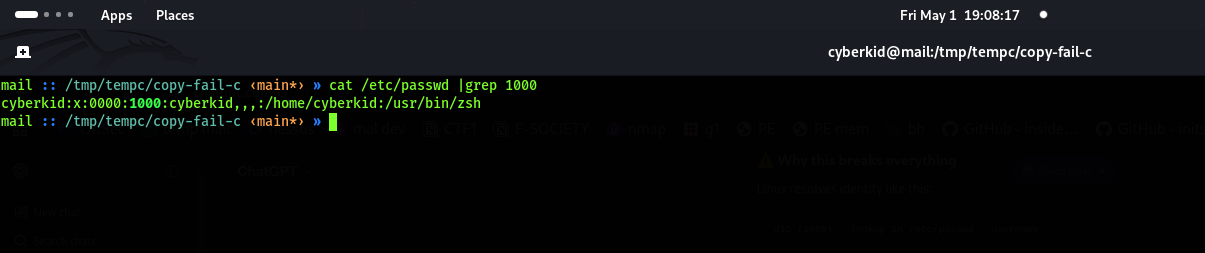 The id changed from 1000 to 0000
## 意外造成损害如何恢复
The id changed from 1000 to 0000
## 意外造成损害如何恢复
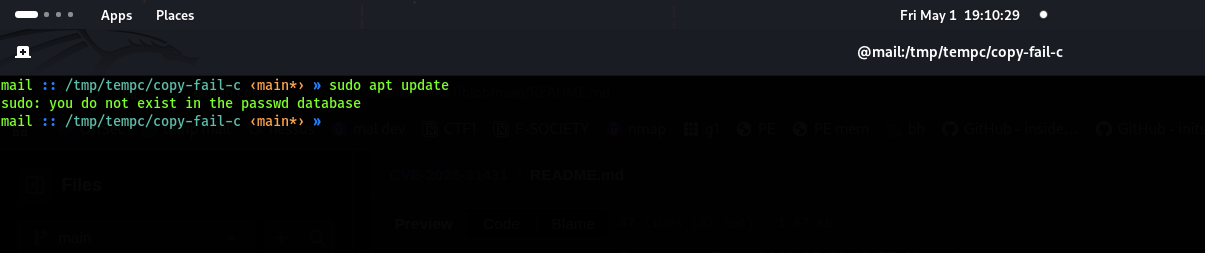
 We cant operate some system commands
We cant operate some system commands
 Go as root using sudo su or use ./exploit then search the user you run the exploit
Go as root using sudo su or use ./exploit then search the user you run the exploit
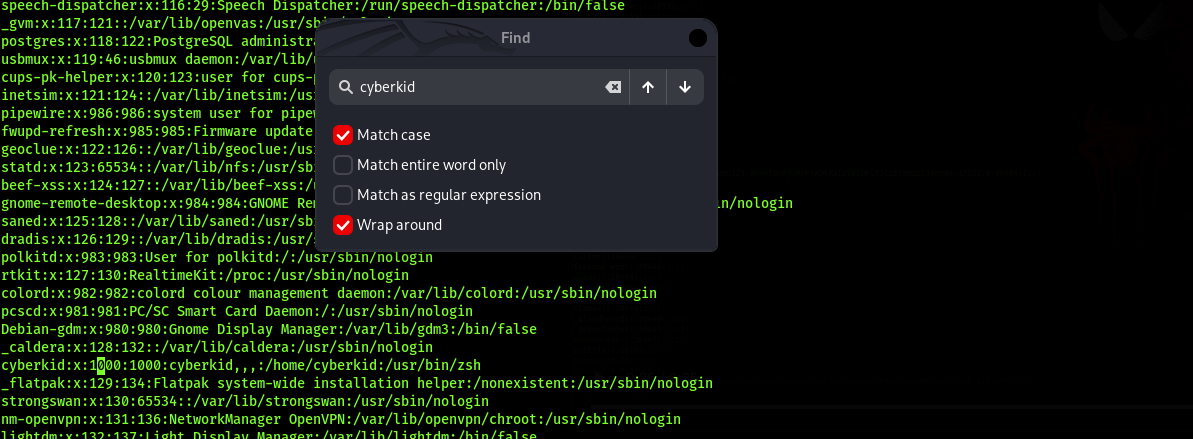 Replace the 0000 to 1000
Replace the 0000 to 1000
 Here you have back your user
## 需要立即采取的行动:
1. 临时缓解措施 – (检查 algif_aead 是否正在使用)
运行:
```
lsmod | grep algif_aead
```
无输出(未在使用)→ 运行以下禁用命令
```
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/disable-algif-aead.conf
sudo rmmod algif_aead 2>/dev/null || true
```
2. 永久修复(在执行前仔细评估业务兼容性)
Debian/Ubuntu: sudo apt update && sudo apt upgrade -y
CentOS/RHEL/Rocky/Alma: sudo dnf update -y
补丁:https://git.kernel.org/stable/c/a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5
Here you have back your user
## 需要立即采取的行动:
1. 临时缓解措施 – (检查 algif_aead 是否正在使用)
运行:
```
lsmod | grep algif_aead
```
无输出(未在使用)→ 运行以下禁用命令
```
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/disable-algif-aead.conf
sudo rmmod algif_aead 2>/dev/null || true
```
2. 永久修复(在执行前仔细评估业务兼容性)
Debian/Ubuntu: sudo apt update && sudo apt upgrade -y
CentOS/RHEL/Rocky/Alma: sudo dnf update -y
补丁:https://git.kernel.org/stable/c/a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5
 ## CopyFail 标准二进制文件
在
## CopyFail 标准二进制文件
在 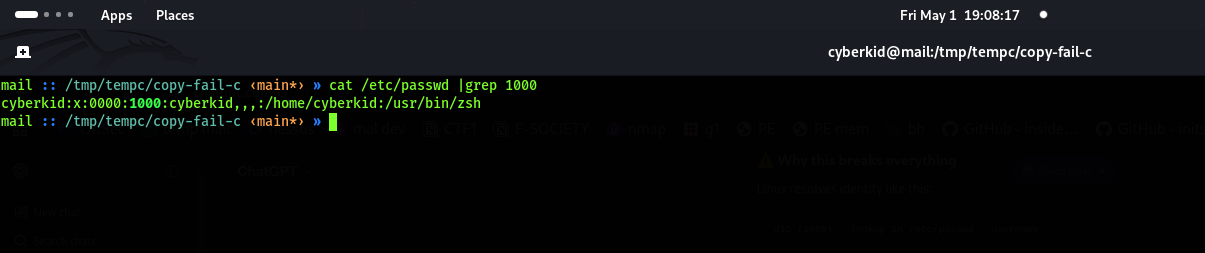 The id changed from 1000 to 0000
## 意外造成损害如何恢复
The id changed from 1000 to 0000
## 意外造成损害如何恢复
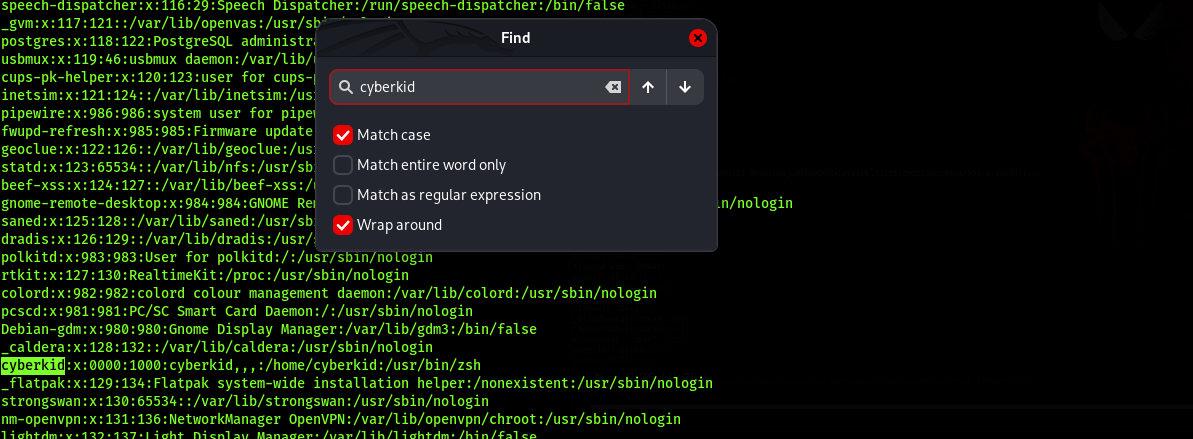 We cant operate some system commands
We cant operate some system commands
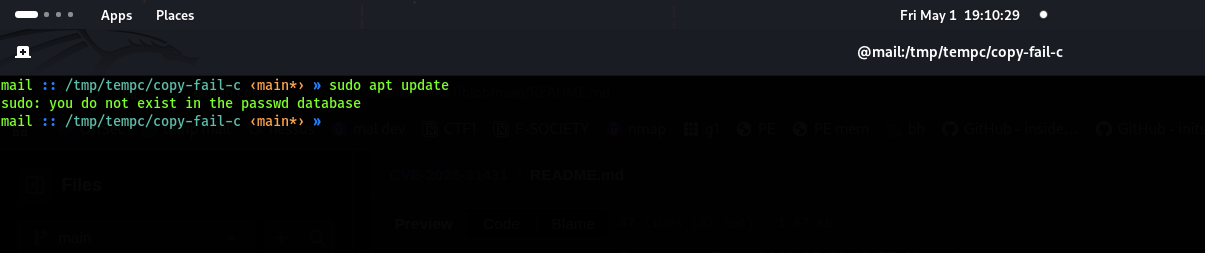 Go as root using sudo su or use ./exploit then search the user you run the exploit
Go as root using sudo su or use ./exploit then search the user you run the exploit
 Replace the 0000 to 1000
Replace the 0000 to 1000
 Here you have back your user
## 需要立即采取的行动:
1. 临时缓解措施 – (检查 algif_aead 是否正在使用)
运行:
```
lsmod | grep algif_aead
```
无输出(未在使用)→ 运行以下禁用命令
```
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/disable-algif-aead.conf
sudo rmmod algif_aead 2>/dev/null || true
```
2. 永久修复(在执行前仔细评估业务兼容性)
Debian/Ubuntu: sudo apt update && sudo apt upgrade -y
CentOS/RHEL/Rocky/Alma: sudo dnf update -y
补丁:https://git.kernel.org/stable/c/a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5
Here you have back your user
## 需要立即采取的行动:
1. 临时缓解措施 – (检查 algif_aead 是否正在使用)
运行:
```
lsmod | grep algif_aead
```
无输出(未在使用)→ 运行以下禁用命令
```
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/disable-algif-aead.conf
sudo rmmod algif_aead 2>/dev/null || true
```
2. 永久修复(在执行前仔细评估业务兼容性)
Debian/Ubuntu: sudo apt update && sudo apt upgrade -y
CentOS/RHEL/Rocky/Alma: sudo dnf update -y
补丁:https://git.kernel.org/stable/c/a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5标签:CopyFail, CSV导出, CVE-2026-31431, ELF可执行文件, Exploit, Linux漏洞利用, LPE, Maven, Offensive Security, Root权限, UID修改, Web报告查看器, x86-64, 协议分析, 安全渗透, 攻击脚本, 数据展示, 本地提权, 权限提升, 漏洞复现, 漏洞验证, 系统提权, 红队, 网络安全, 隐私保护, 静态编译