MdRafiuzzamanSowrov/Malware_Scanner
GitHub: MdRafiuzzamanSowrov/Malware_Scanner
基于 YARA 规则的静态恶意软件扫描器,提供 PE 分析、熵值检测和风险评分,支持 CLI、REST API 和 Web 仪表盘多种使用方式。
Stars: 1 | Forks: 0
# 🛡️ 恶意软件扫描器 v2.0
**基于 YARA 的静态恶意软件扫描器 + 仪表盘 | PE 分析 | 熵值检测 | 风险评分 | CLI + API**
[](https://www.python.org/)
[](LICENSE)
## ✨ 功能
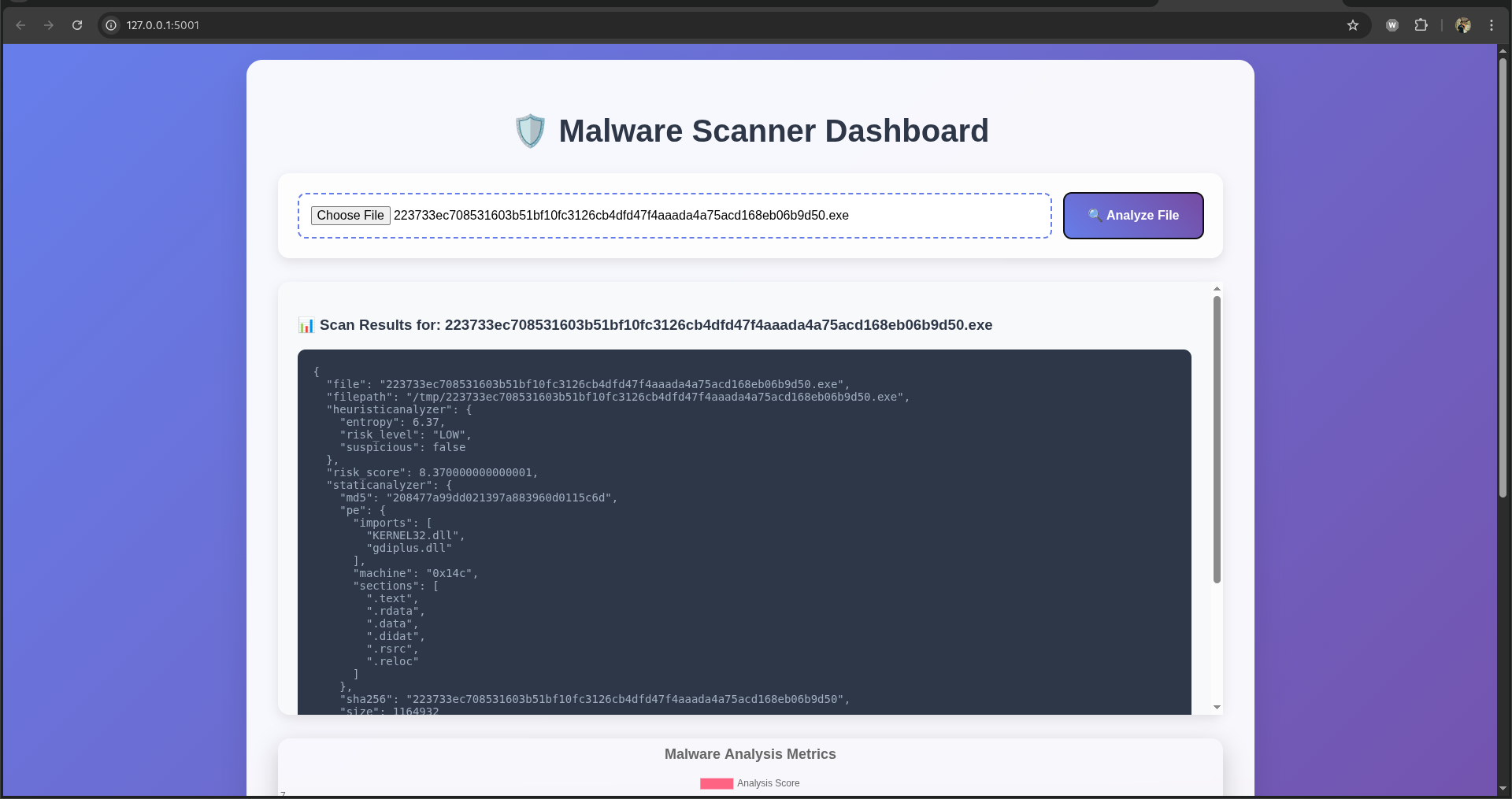
- **🔍 静态分析**: PE 解析,哈希值 (MD5/SHA256),导入表/节
- **🛡️ YARA 规则**: 基于特征的检测
- **📊 启发式检测**: 熵值分析(加壳恶意软件检测)
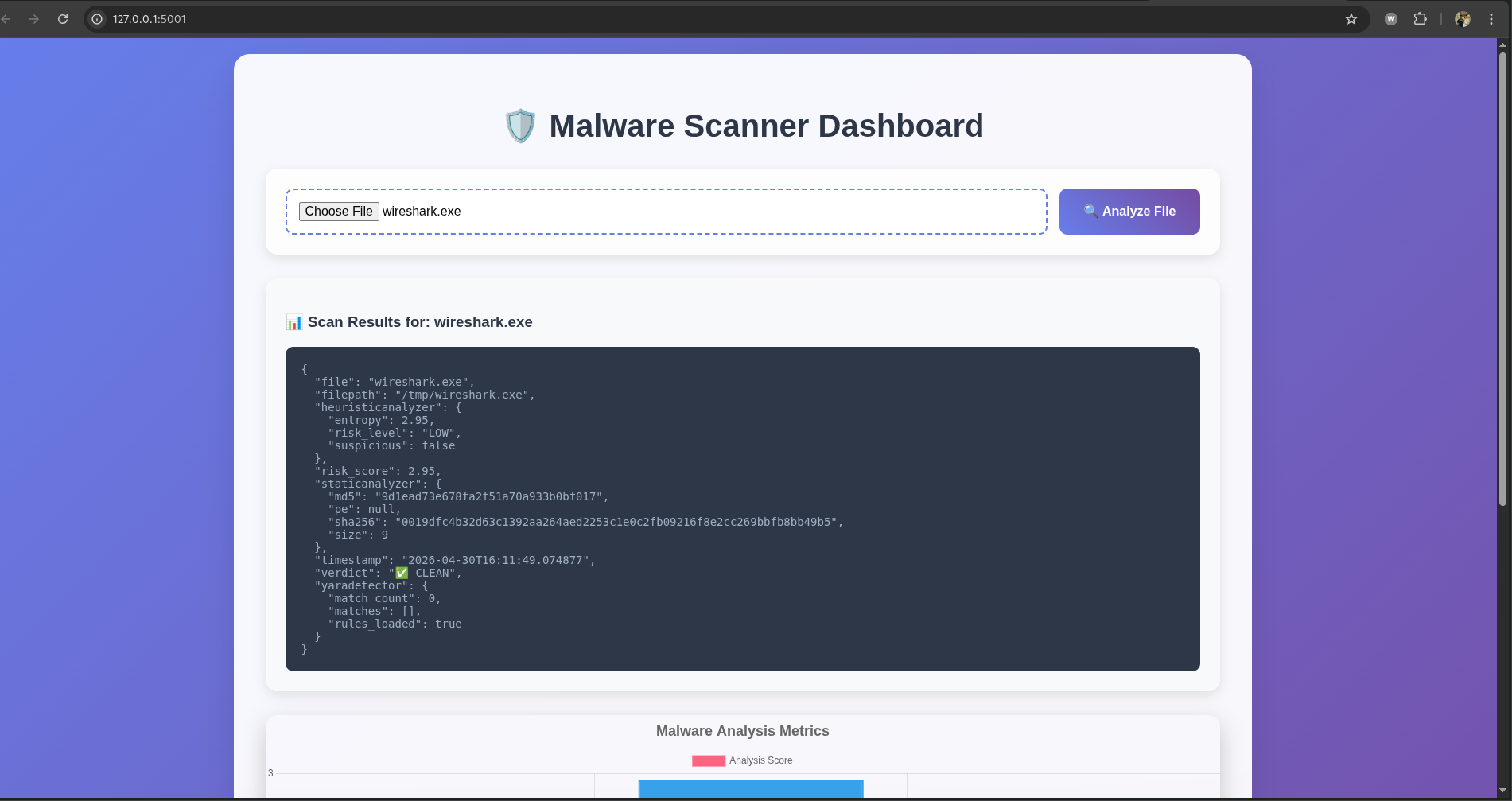
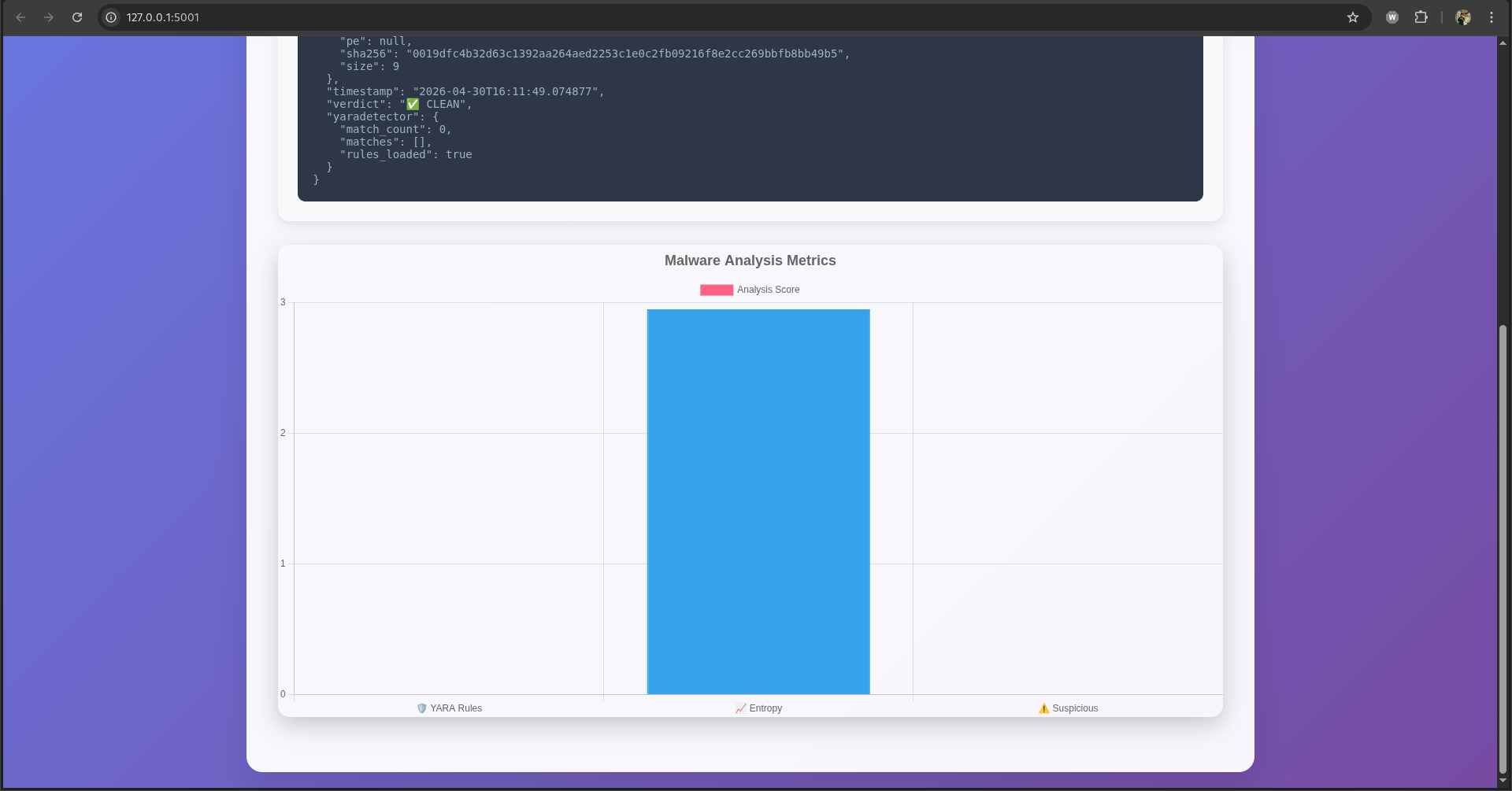
- **🌐 Web 仪表盘**: 精美的 Chart.js 可视化图表
- **⚡ REST API**: 用于自动化集成的 `/scan` 端点
- **💻 CLI 接口**: `python main.py file.exe`
- **🎯 风险评分**: 智能的 0-10 恶意软件评分
- **📱 响应式 UI**: 适配桌面端与移动端
## 📱 截图
### 仪表盘
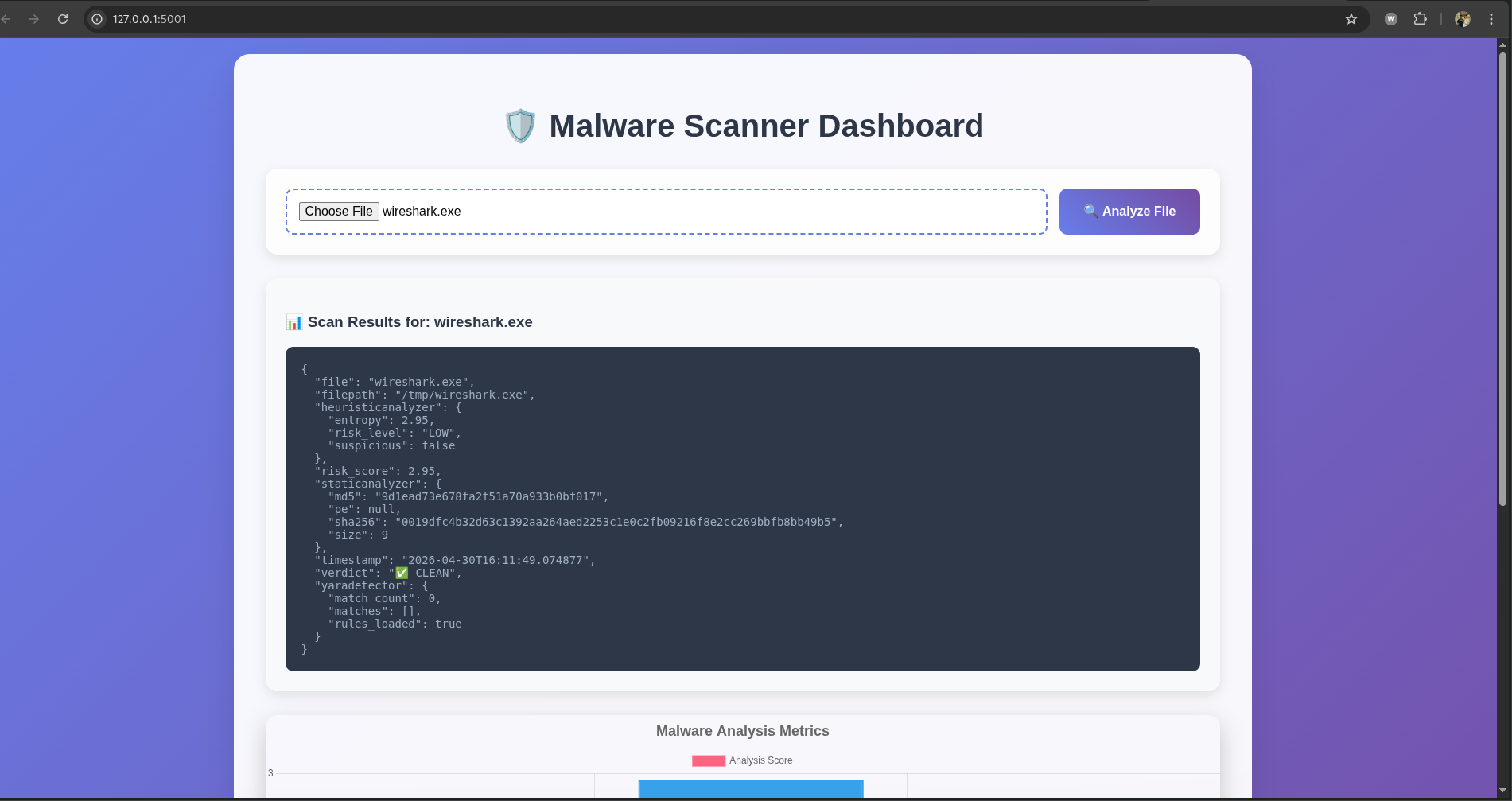
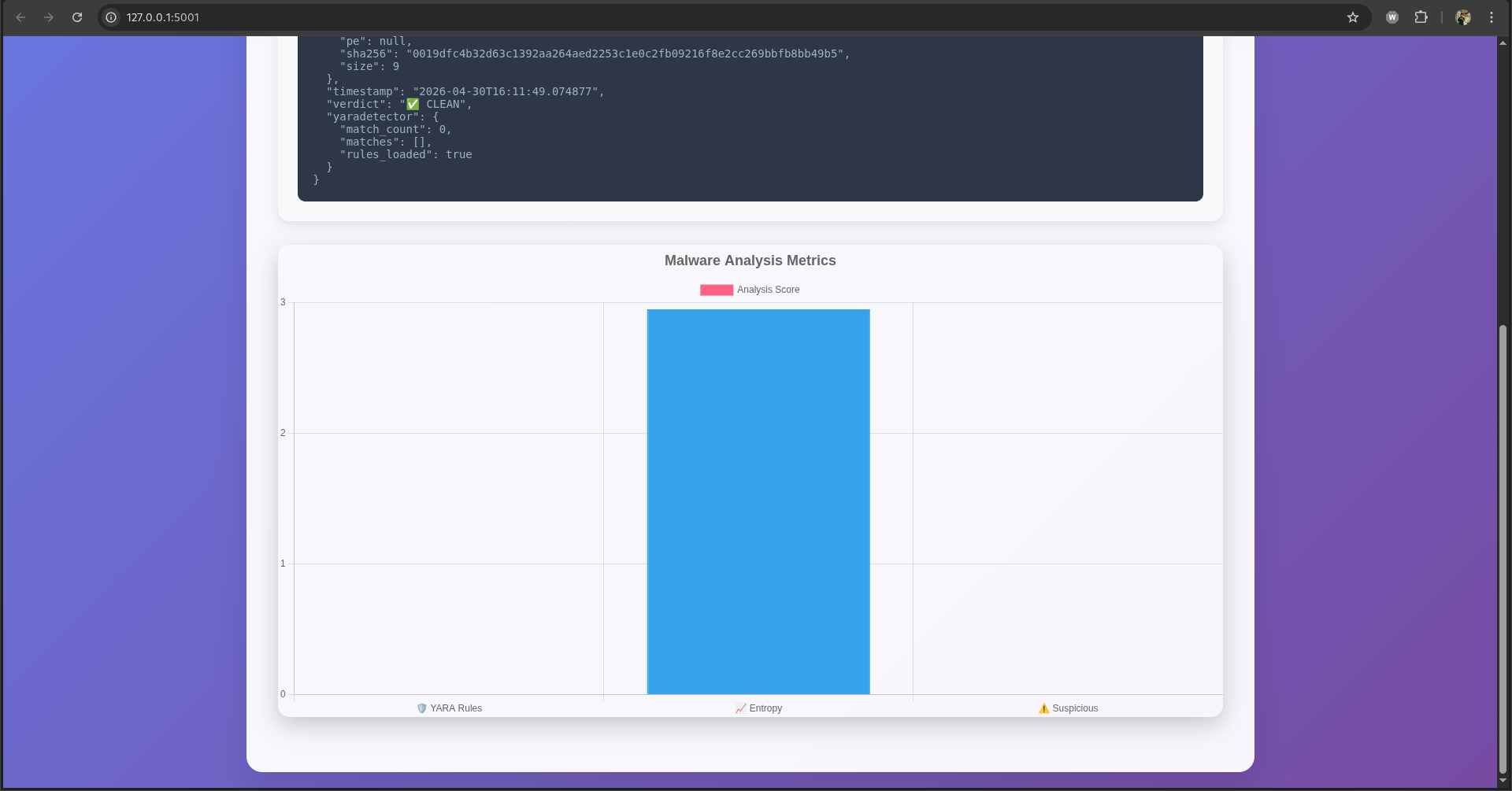
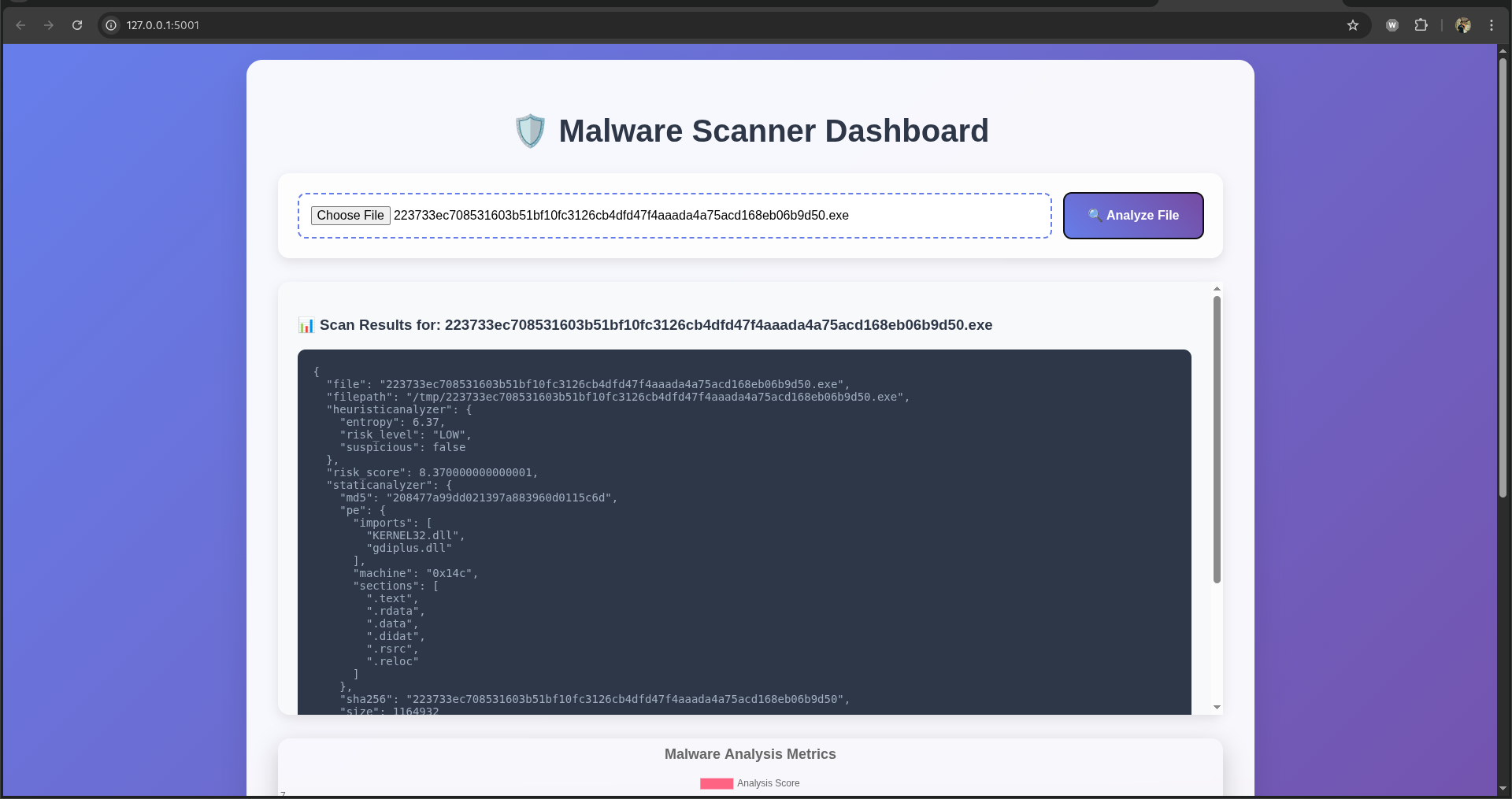
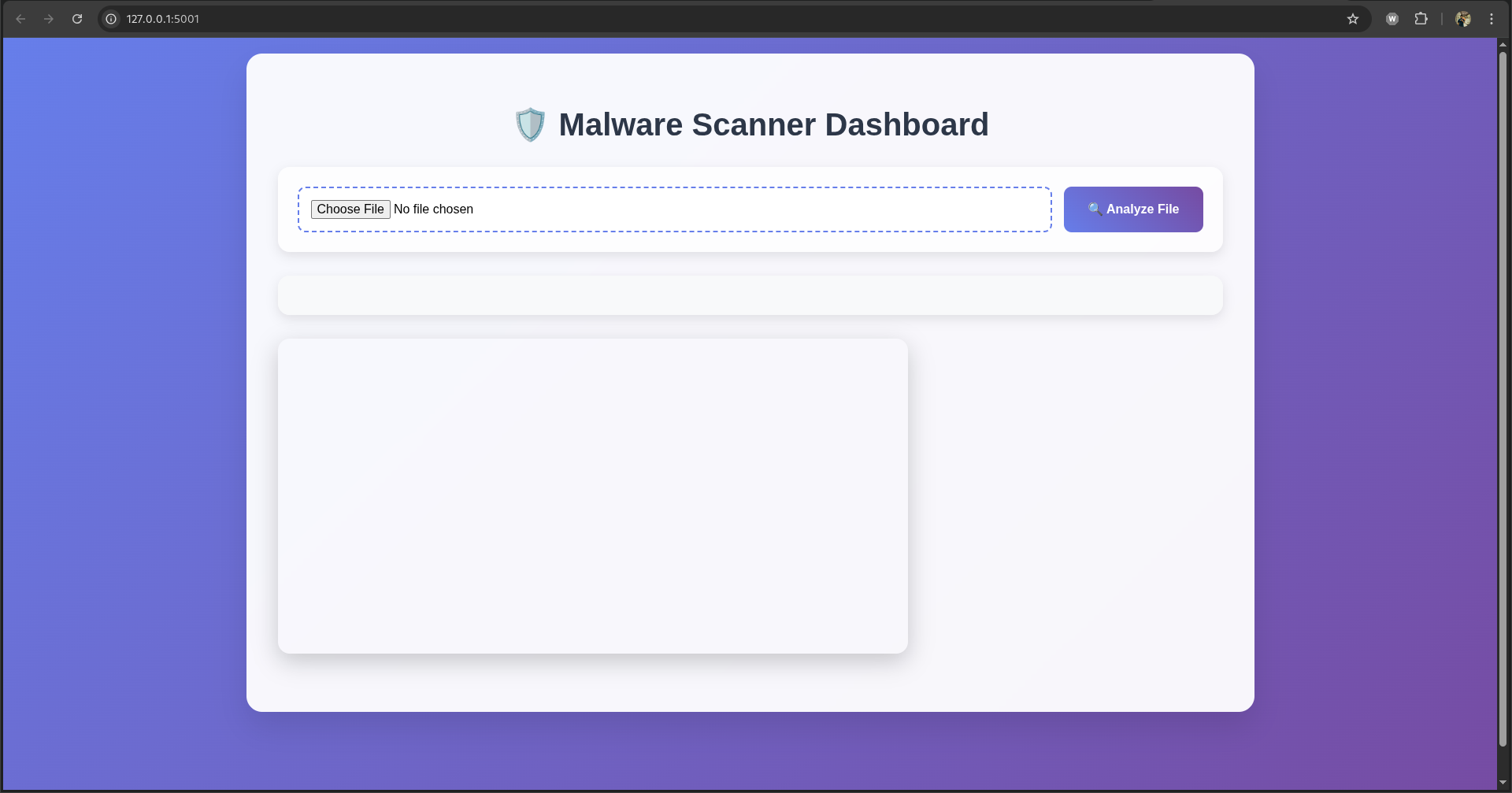 ### 正常文件分析
### 正常文件分析
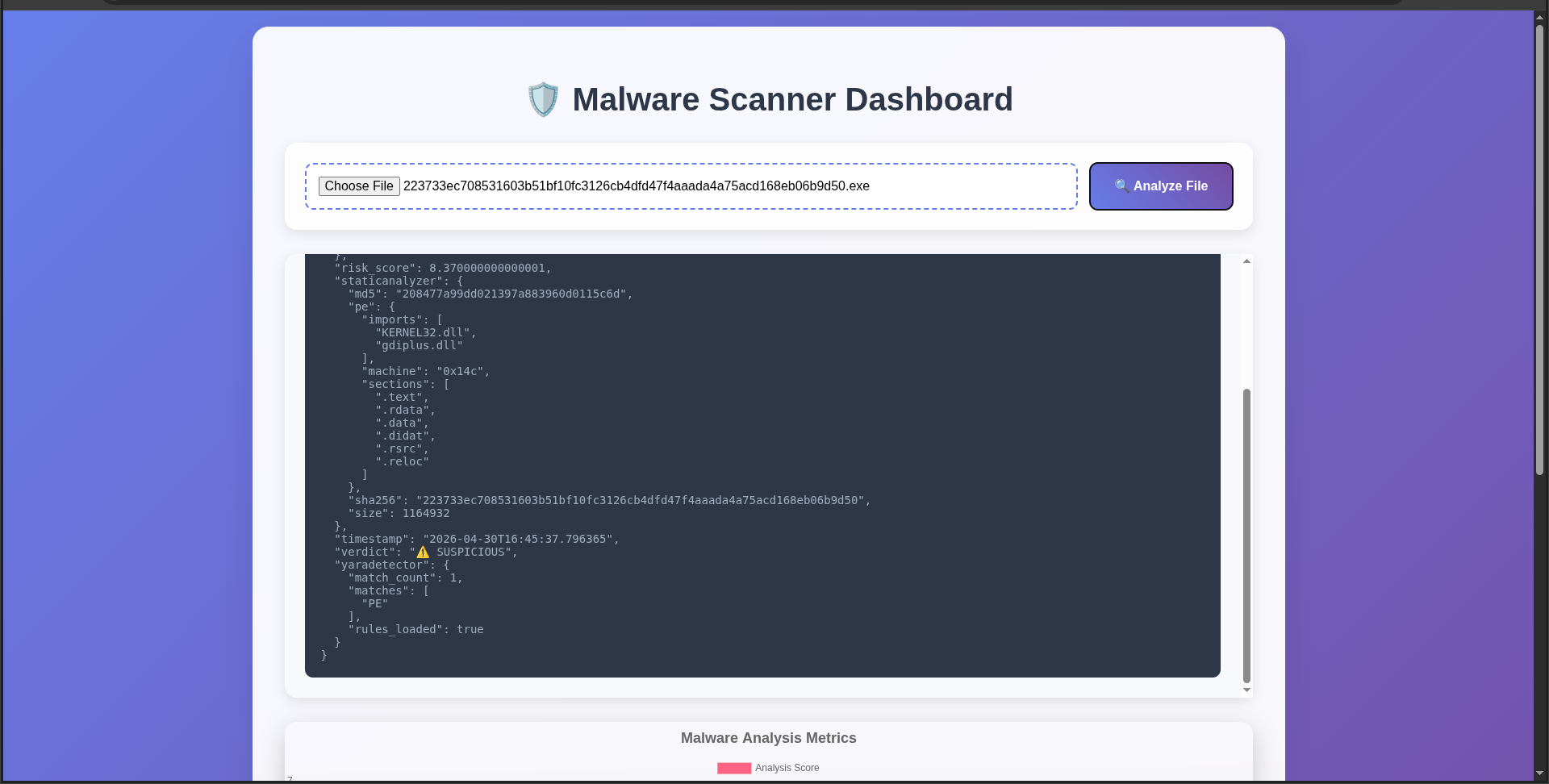
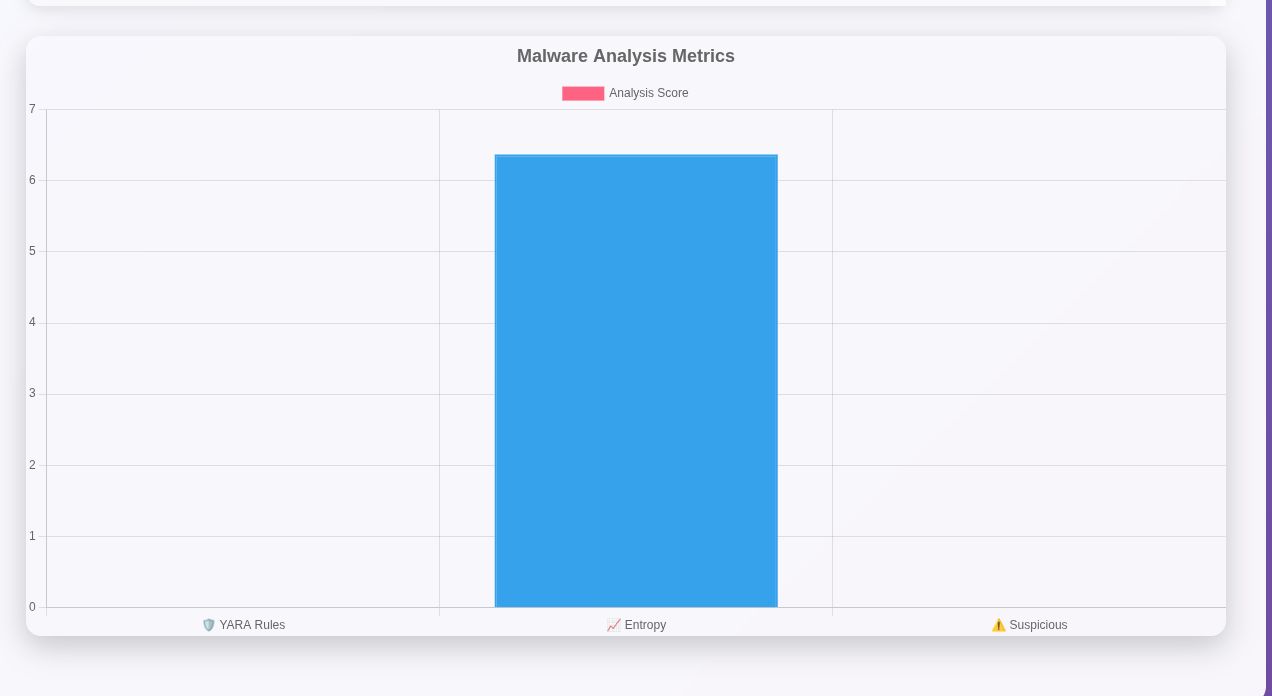
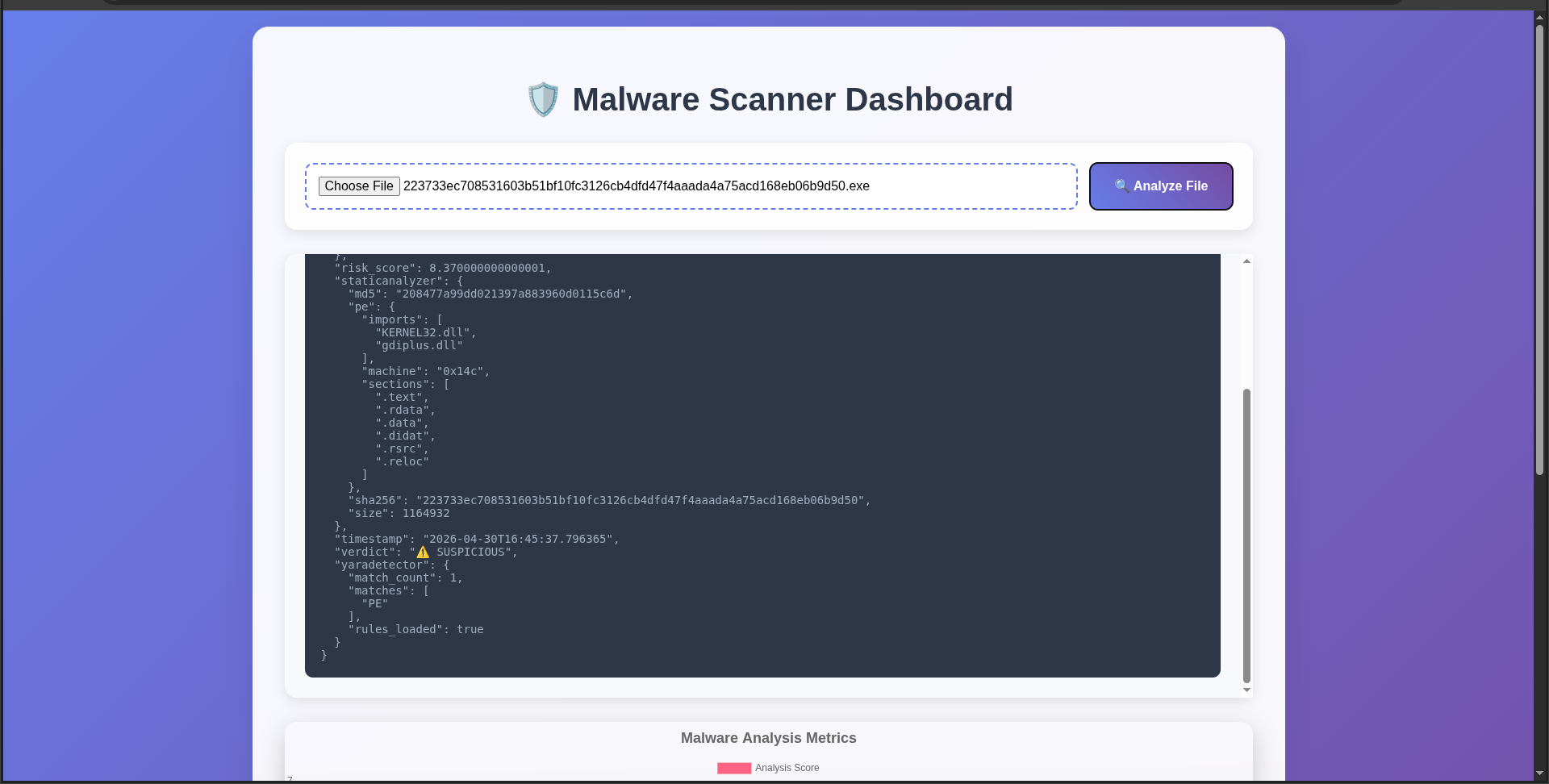
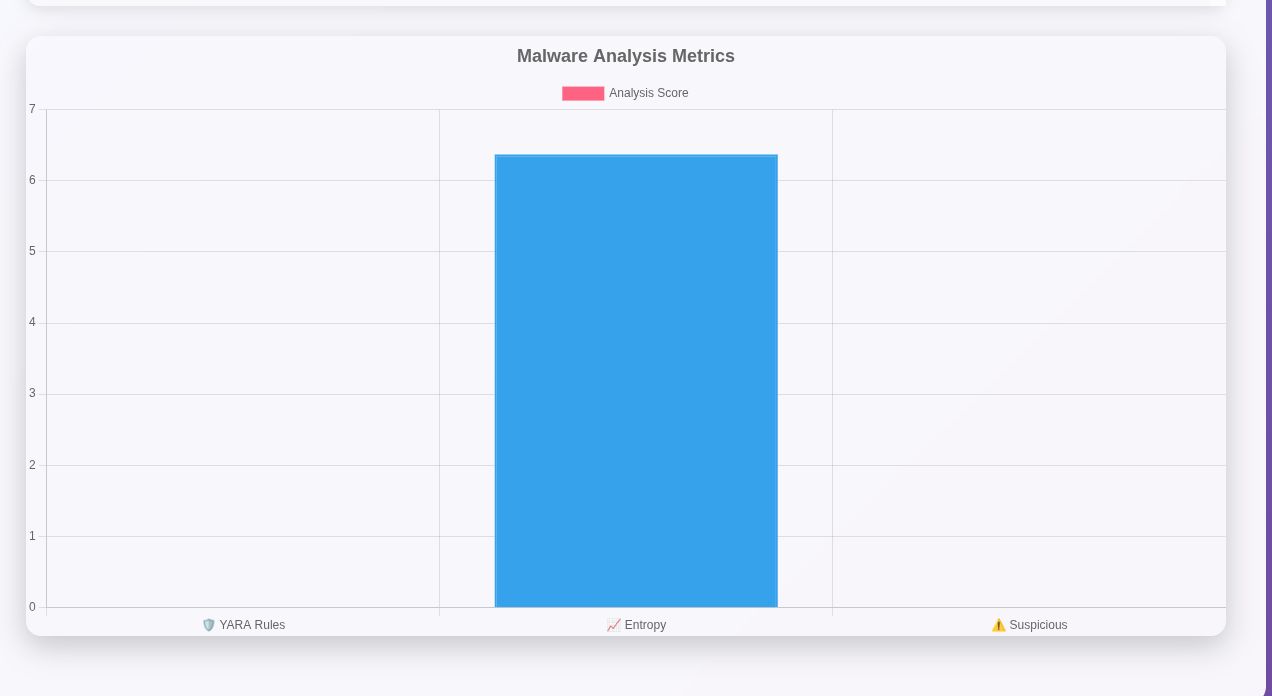
 ### 恶意软件检测
### 恶意软件检测
 ## 🚀 快速入门
```
# Clone 与设置
git clone https://github.com/[YOUR_USERNAME]/Malware_Scanner.git
cd Malware_Scanner
python3 -m venv venv
source venv/bin/activate # Linux/Mac
# 安装
pip install flask pefile yara-python
# 运行 Dashboard
python main.py --dashboard
```
💻 使用示例
Web 仪表盘
```
Visit http://localhost:5001
Upload .exe file
Instant analysis + charts!
```
CLI
```
python main.py suspicious.exe
python main.py --dir /path/to/folder
```
API
```
curl -F "file=@sample.exe" http://localhost:5001/scan
```
🧪 安全测试文件
# EICAR 测试(安全)
```
curl -o eicar_test https://secure.eicar.org/eicar.com.txt
python main.py eicar_test
```
📊 示例输出
```
{
"verdict": "🚨 MALWARE",
"risk_score": 10,
"yaradetector": {
"match_count": 2,
"matches": ["PE", "LargeFile"]
},
"heuristicanalyzer": {
"entropy": 7.99,
"suspicious": true
}
}
```
🛠️ 架构
```
main.py (Flask + CLI)
├── StaticAnalyzer (PE + Hashes)
├── YaraDetector (Signatures)
├── HeuristicAnalyzer (Entropy)
├── rules.yar (Detection rules)
└── dashboard.html (Chart.js UI)
```
📈 风险评分
```
Risk = YARA(2pts) + Entropy(1pt) + Size(1pt) + Heuristics(3pts)
10+ = 🚨 MALWARE | 6-9 = ⚠️ SUSPICIOUS | <6 = ✅ CLEAN
```
🏁 生产部署
# Gunicorn
```
pip install gunicorn
gunicorn -w 4 -b 0.0.0.0:5001 main:app
```
# Docker
```
docker build -t malware-scanner .
docker run -p 5001:5001 malware-scanner
```
📚 包含的 YARA 规则
```
✅ PE Executable Detection
✅ Large File Detection (>8MB)
✅ Process Injection APIs
✅ Anti-Debug Detection
```
```
Fork repository
Add YARA rules
Test with python main.py test.exe
Submit PR!
```
📄 许可证
MIT 许可证 - 可免费商用!
👤 Md.Rafiuzzaman Sowrov
Md.Rafiuzzaman Sowrov - 恶意软件安全研究员
⭐ 如果有帮助,请给个 Star! ⭐
🛡️ 远离恶意软件,保持安全! 🛡️
## 🚀 快速入门
```
# Clone 与设置
git clone https://github.com/[YOUR_USERNAME]/Malware_Scanner.git
cd Malware_Scanner
python3 -m venv venv
source venv/bin/activate # Linux/Mac
# 安装
pip install flask pefile yara-python
# 运行 Dashboard
python main.py --dashboard
```
💻 使用示例
Web 仪表盘
```
Visit http://localhost:5001
Upload .exe file
Instant analysis + charts!
```
CLI
```
python main.py suspicious.exe
python main.py --dir /path/to/folder
```
API
```
curl -F "file=@sample.exe" http://localhost:5001/scan
```
🧪 安全测试文件
# EICAR 测试(安全)
```
curl -o eicar_test https://secure.eicar.org/eicar.com.txt
python main.py eicar_test
```
📊 示例输出
```
{
"verdict": "🚨 MALWARE",
"risk_score": 10,
"yaradetector": {
"match_count": 2,
"matches": ["PE", "LargeFile"]
},
"heuristicanalyzer": {
"entropy": 7.99,
"suspicious": true
}
}
```
🛠️ 架构
```
main.py (Flask + CLI)
├── StaticAnalyzer (PE + Hashes)
├── YaraDetector (Signatures)
├── HeuristicAnalyzer (Entropy)
├── rules.yar (Detection rules)
└── dashboard.html (Chart.js UI)
```
📈 风险评分
```
Risk = YARA(2pts) + Entropy(1pt) + Size(1pt) + Heuristics(3pts)
10+ = 🚨 MALWARE | 6-9 = ⚠️ SUSPICIOUS | <6 = ✅ CLEAN
```
🏁 生产部署
# Gunicorn
```
pip install gunicorn
gunicorn -w 4 -b 0.0.0.0:5001 main:app
```
# Docker
```
docker build -t malware-scanner .
docker run -p 5001:5001 malware-scanner
```
📚 包含的 YARA 规则
```
✅ PE Executable Detection
✅ Large File Detection (>8MB)
✅ Process Injection APIs
✅ Anti-Debug Detection
```
```
Fork repository
Add YARA rules
Test with python main.py test.exe
Submit PR!
```
📄 许可证
MIT 许可证 - 可免费商用!
👤 Md.Rafiuzzaman Sowrov
Md.Rafiuzzaman Sowrov - 恶意软件安全研究员
⭐ 如果有帮助,请给个 Star! ⭐
🛡️ 远离恶意软件,保持安全! 🛡️
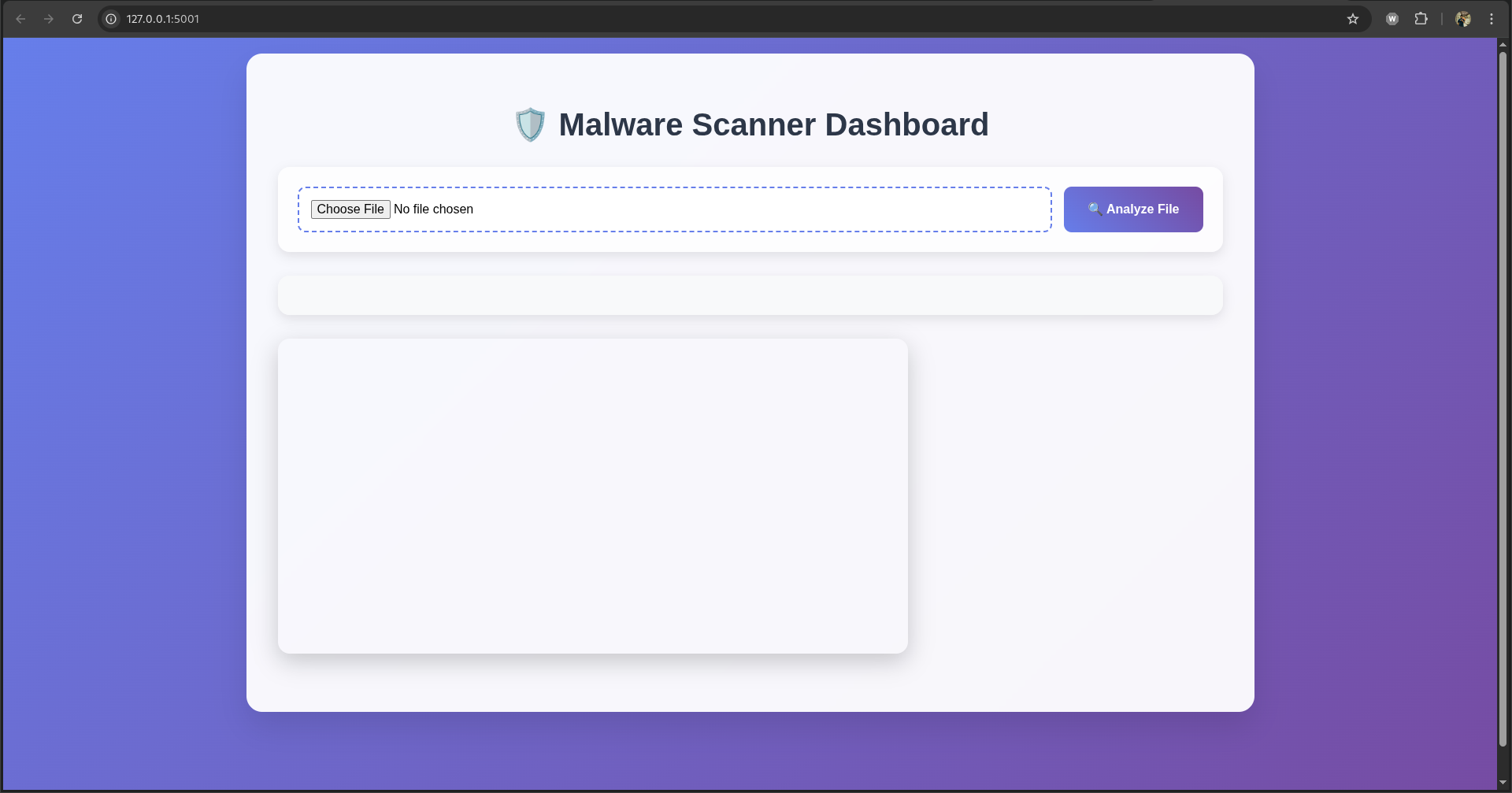 ### 正常文件分析
### 正常文件分析
 ### 恶意软件检测
### 恶意软件检测
 ## 🚀 快速入门
```
# Clone 与设置
git clone https://github.com/[YOUR_USERNAME]/Malware_Scanner.git
cd Malware_Scanner
python3 -m venv venv
source venv/bin/activate # Linux/Mac
# 安装
pip install flask pefile yara-python
# 运行 Dashboard
python main.py --dashboard
```
💻 使用示例
Web 仪表盘
```
Visit http://localhost:5001
Upload .exe file
Instant analysis + charts!
```
CLI
```
python main.py suspicious.exe
python main.py --dir /path/to/folder
```
API
```
curl -F "file=@sample.exe" http://localhost:5001/scan
```
🧪 安全测试文件
# EICAR 测试(安全)
```
curl -o eicar_test https://secure.eicar.org/eicar.com.txt
python main.py eicar_test
```
📊 示例输出
```
{
"verdict": "🚨 MALWARE",
"risk_score": 10,
"yaradetector": {
"match_count": 2,
"matches": ["PE", "LargeFile"]
},
"heuristicanalyzer": {
"entropy": 7.99,
"suspicious": true
}
}
```
🛠️ 架构
```
main.py (Flask + CLI)
├── StaticAnalyzer (PE + Hashes)
├── YaraDetector (Signatures)
├── HeuristicAnalyzer (Entropy)
├── rules.yar (Detection rules)
└── dashboard.html (Chart.js UI)
```
📈 风险评分
```
Risk = YARA(2pts) + Entropy(1pt) + Size(1pt) + Heuristics(3pts)
10+ = 🚨 MALWARE | 6-9 = ⚠️ SUSPICIOUS | <6 = ✅ CLEAN
```
🏁 生产部署
# Gunicorn
```
pip install gunicorn
gunicorn -w 4 -b 0.0.0.0:5001 main:app
```
# Docker
```
docker build -t malware-scanner .
docker run -p 5001:5001 malware-scanner
```
📚 包含的 YARA 规则
```
✅ PE Executable Detection
✅ Large File Detection (>8MB)
✅ Process Injection APIs
✅ Anti-Debug Detection
```
```
Fork repository
Add YARA rules
Test with python main.py test.exe
Submit PR!
```
📄 许可证
MIT 许可证 - 可免费商用!
👤 Md.Rafiuzzaman Sowrov
Md.Rafiuzzaman Sowrov - 恶意软件安全研究员
⭐ 如果有帮助,请给个 Star! ⭐
🛡️ 远离恶意软件,保持安全! 🛡️
## 🚀 快速入门
```
# Clone 与设置
git clone https://github.com/[YOUR_USERNAME]/Malware_Scanner.git
cd Malware_Scanner
python3 -m venv venv
source venv/bin/activate # Linux/Mac
# 安装
pip install flask pefile yara-python
# 运行 Dashboard
python main.py --dashboard
```
💻 使用示例
Web 仪表盘
```
Visit http://localhost:5001
Upload .exe file
Instant analysis + charts!
```
CLI
```
python main.py suspicious.exe
python main.py --dir /path/to/folder
```
API
```
curl -F "file=@sample.exe" http://localhost:5001/scan
```
🧪 安全测试文件
# EICAR 测试(安全)
```
curl -o eicar_test https://secure.eicar.org/eicar.com.txt
python main.py eicar_test
```
📊 示例输出
```
{
"verdict": "🚨 MALWARE",
"risk_score": 10,
"yaradetector": {
"match_count": 2,
"matches": ["PE", "LargeFile"]
},
"heuristicanalyzer": {
"entropy": 7.99,
"suspicious": true
}
}
```
🛠️ 架构
```
main.py (Flask + CLI)
├── StaticAnalyzer (PE + Hashes)
├── YaraDetector (Signatures)
├── HeuristicAnalyzer (Entropy)
├── rules.yar (Detection rules)
└── dashboard.html (Chart.js UI)
```
📈 风险评分
```
Risk = YARA(2pts) + Entropy(1pt) + Size(1pt) + Heuristics(3pts)
10+ = 🚨 MALWARE | 6-9 = ⚠️ SUSPICIOUS | <6 = ✅ CLEAN
```
🏁 生产部署
# Gunicorn
```
pip install gunicorn
gunicorn -w 4 -b 0.0.0.0:5001 main:app
```
# Docker
```
docker build -t malware-scanner .
docker run -p 5001:5001 malware-scanner
```
📚 包含的 YARA 规则
```
✅ PE Executable Detection
✅ Large File Detection (>8MB)
✅ Process Injection APIs
✅ Anti-Debug Detection
```
```
Fork repository
Add YARA rules
Test with python main.py test.exe
Submit PR!
```
📄 许可证
MIT 许可证 - 可免费商用!
👤 Md.Rafiuzzaman Sowrov
Md.Rafiuzzaman Sowrov - 恶意软件安全研究员
⭐ 如果有帮助,请给个 Star! ⭐
🛡️ 远离恶意软件,保持安全! 🛡️标签:Chart.js, DNS信息、DNS暴力破解, DNS 反向解析, Flask, pefile, PE文件分析, Python, REST API, Web仪表盘, YARA规则, 云安全监控, 可视化面板, 威胁分析, 开发者评论分析, 恶意软件扫描器, 文件哈希, 无后门, 熵值检测, 签名检测, 网络信息收集, 网络安全, 自动化侦查工具, 请求拦截, 逆向工具, 隐私保护, 静态分析