DerrickLongkai/EdgeGuard-Honeypot
GitHub: DerrickLongkai/EdgeGuard-Honeypot
一款基于Cowrie蜜罐的实时威胁情报可视化平台,解决SSH/Telnet攻击的地理与行为分析问题。
Stars: 0 | Forks: 0
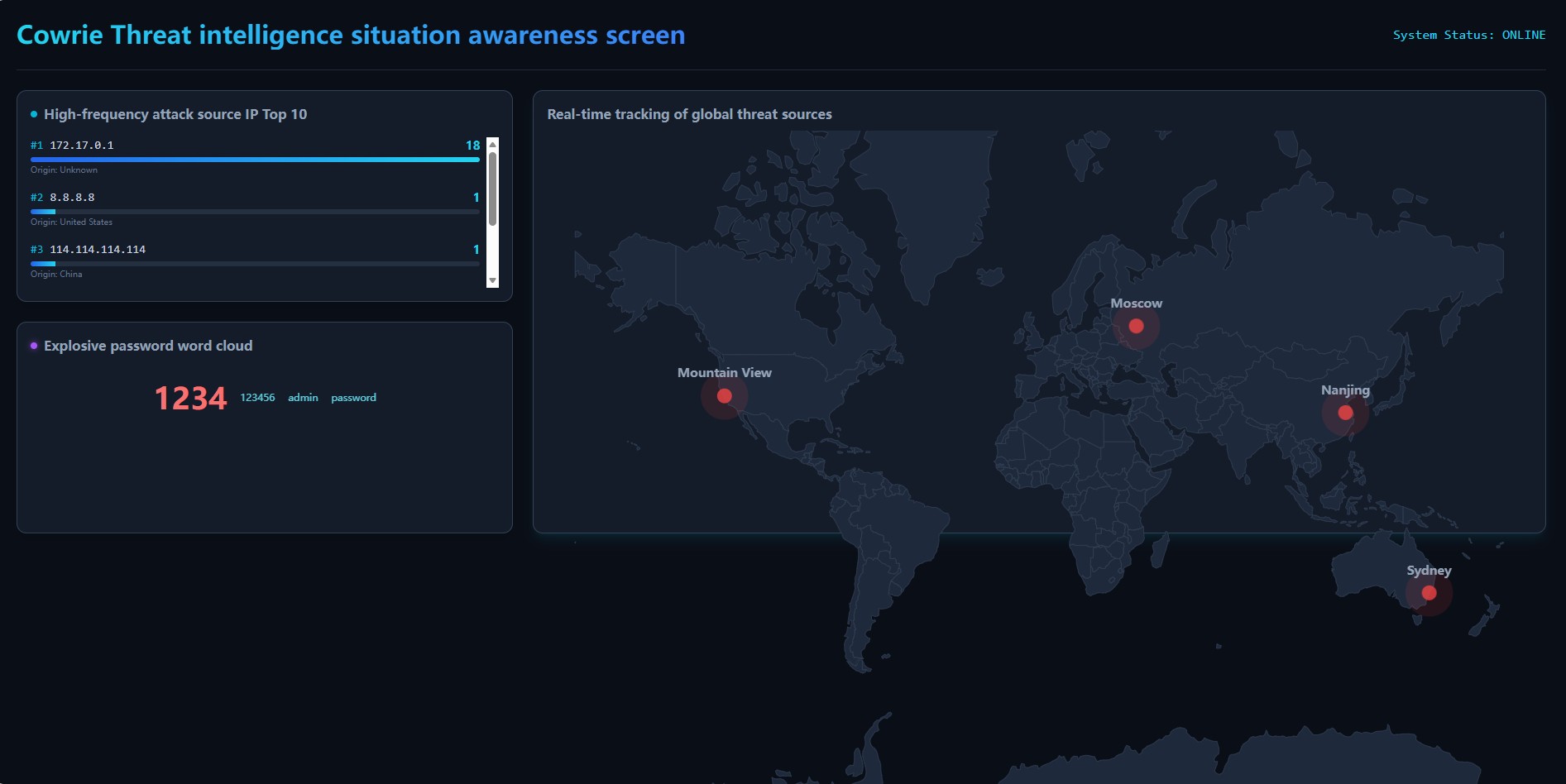
# EdgeGuard: Threat Intelligence Situation Awareness Platform




A full-stack, real-time threat intelligence dashboard designed to visualize SSH/Telnet brute-force attacks captured by a Cowrie honeypot.
## Key Features
* **Real-Time Global Tracking:** Maps attacker IP addresses to geographic coordinates using the MaxMind GeoLite2 engine.
* **Threat Analytics:** Identifies high-frequency attack source IPs dynamically.
* **Credential Intelligence:** Visualizes explosive password attempts (weak credentials) via a dynamic word cloud.
* **Automated Data Pipeline:** A robust Python daemon that parses honeypot logs, enriches them with GeoIP data, and stores them in MySQL.
## Architecture
1. **Sensor:** Cowrie Honeypot intercepts unauthorized access attempts.
2. **ETL Engine:** Python script extracts telemetry, resolves IP geolocation, and persists data to a MySQL relational database.
3. **Backend API:** Lightweight Flask REST API serves threat intelligence to the frontend.
4. **Frontend Dashboard:** React.js + Vite application utilizing `react-simple-maps` for interactive threat visualization.
## Dashboard Preview
## How to start
### 1. Database Setup
Execute the SQL schema to initialize the `attacks` table:
CREATE DATABASE edgeguard;
USE edgeguard;
CREATE TABLE attacks (
id INT AUTO_INCREMENT PRIMARY KEY,
src_ip VARCHAR(50) NOT NULL,
username VARCHAR(100),
password VARCHAR(255),
country VARCHAR(100),
city VARCHAR(100),
latitude DECIMAL(10, 6),
longitude DECIMAL(11, 6),
timestamp DATETIME DEFAULT CURRENT_TIMESTAMP
);
### 2. Backend Environment (Flask API)
Navigate to the backend directory, set up the Python virtual environment, install dependencies, and start the server:
cd backend
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
python3 app.py
### 3. frontend Environment (React Dashboard)
cd frontend
npm install --legacy-peer-deps
npm run dev
标签:EdgeGuard, ETL, Flask, GeoIP, HTTP/HTTPS抓包, IP 追踪, JavaCC, Python 守护进程, React, SSH 攻击, Syscalls, Telnet 攻击, Vite, 全栈, 前端可视化, 地图可视化, 地理定位, 威胁情报, 安全运营, 密码爆破, 开发者工具, 态势感知, 扫描框架, 数据管道, 日志解析, 网络调试, 自动化, 自定义脚本, 蜜罐, 证书伪造, 证书利用, 词云, 软件工程, 逆向工具, 高频攻击