rudrasingh-007/Aegis-SOC
GitHub: rudrasingh-007/Aegis-SOC
一款端到端自动化 SOC L1/L2 告警分流系统,集成双源威胁情报富化、杀伤链检测、统计异常分析和响应剧本,帮助安全团队高效处理安全告警。
Stars: 0 | Forks: 0
```
█████╗ ███████╗ ██████╗ ██╗███████╗ ███████╗ ██████╗ ██████╗
██╔══██╗██╔════╝██╔════╝ ██║██╔════╝ ██╔════╝██╔═══██╗██╔════╝
███████║█████╗ ██║ ███╗██║███████╗ ███████╗██║ ██║██║
██╔══██║██╔══╝ ██║ ██║██║╚════██║ ╚════██║██║ ██║██║
██║ ██║███████╗╚██████╔╝██║███████║ ███████║╚██████╔╝╚██████╗
╚═╝ ╚═╝╚══════╝ ╚═════╝ ╚═╝╚══════╝ ╚══════╝ ╚═════╝ ╚═════╝
```
```
SYSTEM : Automated L1 SOC Triage System
VERSION : 5.0
STATUS : ACTIVE
CLEARANCE : OPEN SOURCE
```
## Aegis-SOC 查询真实的威胁情报 API,并自动标记已确认的恶意 IP。
它能检测具有关联性的告警中的杀伤链攻击序列。
它在单一流水线中模拟并自动化 L1 和 L2 SOC 分流的核心环节——从告警摄取、调查到响应。
## 概述
Aegis-SOC 是一款模块化的开源 SOC 自动化工具,旨在端到端地自动化 L1 SOC 分流。该系统会生成或接收告警,通过基于规则的分类引擎进行处理,并针对 AbuseIPDB 和 VirusTotal 执行双源情报富化。告警会经过动态的威胁情报重新分类(由 AbuseIPDB 和 VirusTotal 的分数驱动严重性等级提升),随后流入统计异常检测器;该检测器利用持久的 SQLite 历史基线进行 Z 分数计算。系统会对关联告警进行分析,以识别快速时间窗口攻击和已知的杀伤链序列,从而揭示多向量攻击活动。该平台支持针对严重事件的自动化电子邮件通知、结构化的 JSON 和控制台报告生成、带有影响评估和隔离建议的 L2 自动化调查引擎,以及一系列响应剧本。误报会被记录用于系统调优,同时配备具有基于会话身份验证的安全 Flask 仪表板,为操作员提供受控的访问权限和可视化界面。
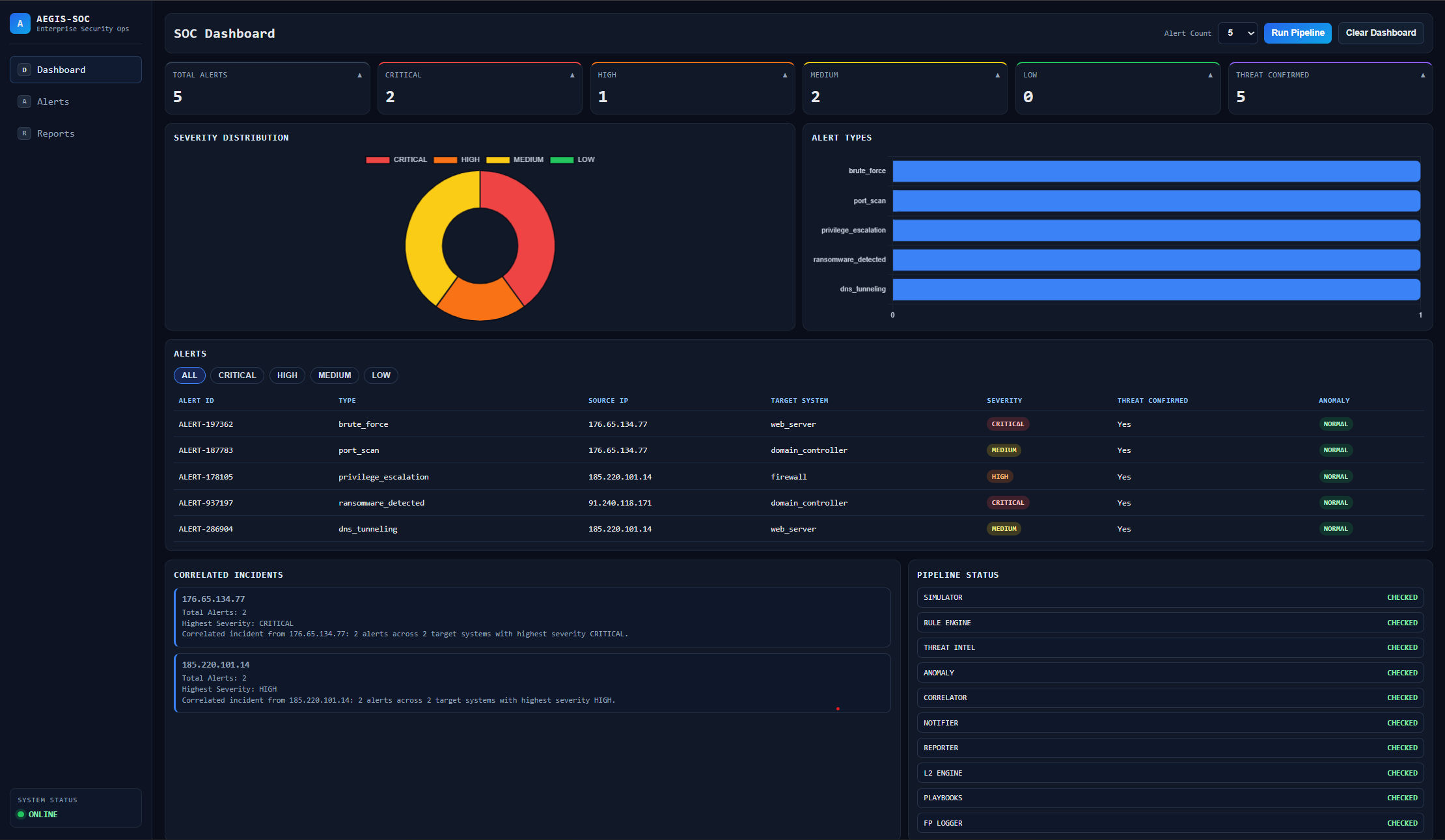
## 仪表板预览
## 
## 功能特性
```
[+] Realistic Alert Simulation 10 attack vectors across 5 target systems
[+] Rule Based Classification LOW / MEDIUM / HIGH / CRITICAL severity engine
[+] Dual Source Threat Intel AbuseIPDB + VirusTotal cross-validation
[+] Email Notifications Real-time CRITICAL alert dispatch via Gmail SMTP
[+] Structured Report Generation Console + JSON incident reports per alert
[+] False Positive Tracking Persistent FP registry for rule tuning
[+] L2 Investigation Engine Automated deep analysis with isolation recommendations
[+] Alert Correlation Multi-vector attack detection by source IP grouping
[+] Wazuh SIEM Integration Wazuh compatible ingestion layer for live connectivity
[+] Automated Response Playbooks Step-by-step incident response for 6 attack types
[+] Anomaly Detection Engine Z-score based statistical anomaly detection
[+] Live SOC Dashboard Flask web dashboard with charts, alerts table, and pipeline control
[+] Auth Log Ingestion Parse real Linux auth.log files into alerts
[+] Dashboard File Upload Upload real log files through the browser UI
[+] Threat Intel Reclassification Severity upgraded dynamically based on AbuseIPDB and VirusTotal scores
[+] Kill-Chain Sequence Detection Identifies known attack chains across correlated alerts
[+] Time-Window Correlation Flags rapid multi-alert attacks within 60 second windows
[+] SQLite Historical Baseline Persistent alert history for statistically meaningful anomaly detection
[+] Dashboard Authentication Session-based login with environment configured credentials
[+] 43 Automated Unit Tests 43 automated unit tests across core modules
```
## 威胁流水线
```
[SIMULATOR/WAZUH] → [RULE ENGINE] → [THREAT INTEL] → [RECLASSIFIER] → [ANOMALY DETECTOR] → [CORRELATOR] → [NOTIFIER] → [REPORTER] → [L2 ENGINE] → [PLAYBOOKS] → [FP LOGGER]
```
## 流水线架构
```
INPUT LAYER
├── Alert Simulator → 10 attack vectors, synthetic alerts
└── Wazuh Ingestor → SIEM compatible ingestion
PROCESSING LAYER
├── Rule Engine → Severity classification (LOW/MED/HIGH/CRIT)
├── Threat Intel → AbuseIPDB + VirusTotal enrichment
├── Anomaly Detector → Z-score statistical analysis
└── Alert Correlator → Multi-vector attack grouping
OUTPUT LAYER
├── Email Notifier → CRITICAL alert dispatch
├── Report Generator → JSON + Console incident reports
├── L2 Investigator → Impact assessment + isolation rec.
├── Response Playbooks → Step-by-step incident response
└── FP Logger → False positive registry
```
| 阶段 | 模块 | 功能 |
|---|---|---|
| 01 | 告警模拟器 / Wazuh 接入器 | 生成或接收安全告警 |
| 02 | 规则引擎 | 分类严重性 —— 低 / 中 / 高 / 严重 |
| 03 | 威胁情报 | 通过 AbuseIPDB + VirusTotal 进行双源情报富化 |
| 03b | 威胁情报重分类 | 根据 AbuseIPDB 和 VirusTotal 分数提升严重性 |
| 04 | 告警关联器 | 按源 IP 对相关告警进行分组 |
| 05 | 邮件通知器 | 为严重事件派发安全分析师通知 |
| 06 | 报告生成器 | 输出结构化的控制台 + JSON 事件报告 |
| 07 | L2 调查引擎 | 针对严重告警进行深度自动化分析 |
| 08 | 误报记录器 | 维护持久化的误报记录 |
## 严重性矩阵
```
CRITICAL [████████████] Immediate escalation. Isolate affected system.
HIGH [████████░░░░] Investigate immediately. Review related logs.
MEDIUM [████░░░░░░░░] Monitor closely. Cross-reference threat intel.
LOW [██░░░░░░░░░░] Likely false positive. Log and discard.
```
## 涵盖的攻击向量
```
failed_login brute_force malware_detected
port_scan suspicious_connection ransomware_detected
privilege_escalation ddos_attack unauthorized_wifi_access
dns_tunneling
```
## 系统结构
```
Aegis-SOC/
│
├── main.py # Pipeline entry point
├── config/
│ └── config.py # Central configuration
├── simulator/
│ └── alert_simulator.py # Alert simulation module
├── engine/
│ └── rule_engine.py # Rule based classification engine
├── storage/
│ └── history_store.py # SQLite historical alert persistence
├── log_parser/
│ └── auth_log_parser.py # Linux auth.log parser
├── sample_logs/
│ └── auth.log # Sample auth.log for testing
├── enrichment/
│ └── threat_intel.py # AbuseIPDB + VirusTotal enrichment
├── notifier/
│ └── email_notifier.py # Critical alert notifications
├── reporter/
│ └── report_generator.py # Incident report generation
├── logger/
│ └── false_positive_logger.py # False positive registry
├── l2_investigator/
│ └── l2_engine.py # L2 automated investigation engine
├── correlator/
│ └── alert_correlator.py # Multi-vector alert correlation
├── integrations/
│ └── wazuh_ingestor.py # Wazuh SIEM ingestion layer
├── l2_reports/ # L2 investigation reports
├── correlation_reports/ # Correlation reports
├── anomaly/
│ └── anomaly_detector.py # Z-score based anomaly detection
├── playbooks/
│ └── response_playbooks.py # Automated incident response playbooks
├── dashboard/
│ ├── app.py # Flask dashboard server
│ └── templates/
│ └── index.html # SOC dashboard UI
├── reports/ # Generated incident reports
├── requirements.txt # Dependencies
└── README.md # Documentation
```
## 部署说明
**要求**
- Python 3.x
- AbuseIPDB API 密钥 — [abuseipdb.com](https://abuseipdb.com)
- VirusTotal API 密钥 — [virustotal.com](https://virustotal.com)
- 启用了应用专用密码的 Gmail 帐户
**安装**
```
git clone https://github.com/yourusername/Aegis-SOC.git
cd Aegis-SOC
pip install -r requirements.txt
```
**环境配置**
在根目录下创建一个 `.env` 文件:
```
ABUSEIPDB_API_KEY=your_abuseipdb_key
VIRUSTOTAL_API_KEY=your_virustotal_key
EMAIL_SENDER=your_gmail@gmail.com
EMAIL_PASSWORD=your_gmail_app_password
EMAIL_RECEIVER=your_gmail@gmail.com
DASHBOARD_USERNAME=your_dashboard_username
DASHBOARD_PASSWORD=your_dashboard_password
FLASK_SECRET_KEY=your_secret_key
```
**执行**
```
python main.py
```
**运行仪表板**
```
python -m dashboard.app
```
```然后在浏览器中打开``` http://localhost:5000```。```
```要注销:点击侧边栏中的注销按钮或在浏览器中访问``` http://localhost:5000/logout```。```
**上传真实日志**
```
Upload a Linux auth.log file through the dashboard UI to process real log data instead of simulated alerts.
```
## 测试
运行所有 43 个单元测试:
```
python -m pytest tests/ -v
```
## 路线图
```
[COMPLETE] V1 — Core triage pipeline
[COMPLETE] V2 — Dual threat intel, email alerts, FP tracking
[COMPLETE] V3 — L2 automation, Wazuh SIEM integration, alert correlation
[COMPLETE] V4 — Dashboard UI, anomaly detection, response playbooks
[COMPLETE] V5 — Kill-chain detection, threat intel reclassification, SQLite baseline, dashboard auth, 43 unit tests
[PLANNED] V6 — ML based detection, live SIEM feed, multi-user support
```
## 许可证
MIT 许可证 — 可免费使用、修改和分发。
```
[ AEGIS-SOC ] — AUTOMATED THREAT TRIAGE — OPEN SOURCE
```
标签:AbuseIPDB, Ask搜索, auth.log, Flask仪表盘, IP 地址批量处理, L1/L2安全分析师, Python, SOC工具, SOC自动化, SQLite, VirusTotal, Web安全, Z-score异常检测, 告警分类, 基于规则分类, 威胁情报, 威胁情报富化, 安全规则引擎, 安全运营中心, 开发者工具, 异常检测, 恶意IP检测, 无后门, 日志接入, 杀伤链检测, 漏洞发现, 网络安全, 网络映射, 自动化分诊, 自动化调查, 蓝队分析, 身份验证日志, 逆向工具, 隐私保护