CyberEnthusiastic/mitre-attack-detection-rules
GitHub: CyberEnthusiastic/mitre-attack-detection-rules
一个基于 Python 的 MITRE ATT&CK 检测规则库与可视化工具,解决跨平台规则导出与覆盖分析问题。
Stars: 0 | Forks: 0
# MITRE ATT&CK 检测规则库
[](./LICENSE)
[](https://www.python.org/downloads/)
[](https://attack.mitre.org/)
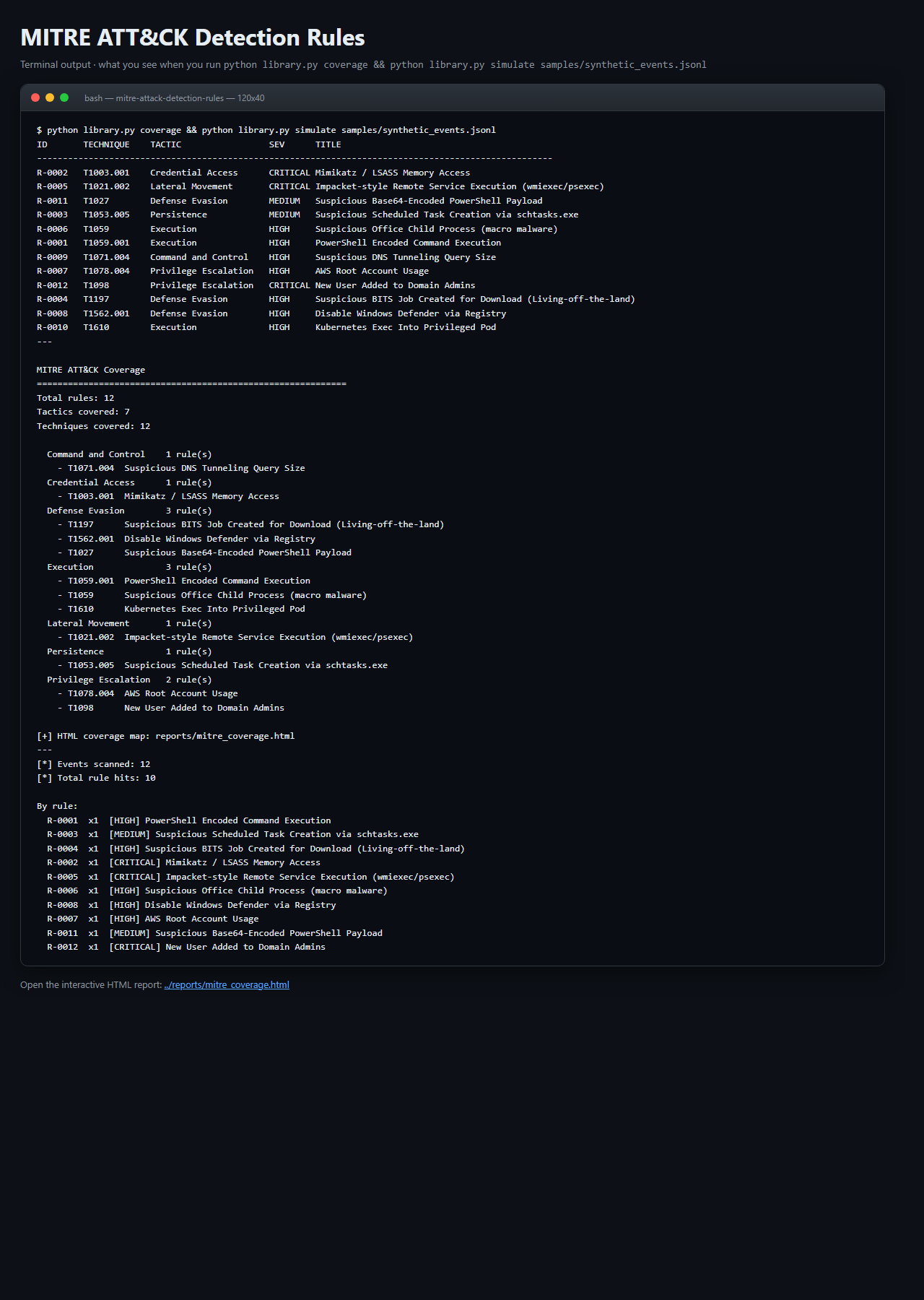
## 功能概述(终端输出截图)
```
ID TECHNIQUE TACTIC SEV TITLE
----------------------------------------------------------------------------------------------------
R-0002 T1003.001 Credential Access CRITICAL Mimikatz / LSASS Memory Access
R-0005 T1021.002 Lateral Movement CRITICAL Impacket-style Remote Service Execution
R-0001 T1059.001 Execution HIGH PowerShell Encoded Command Execution
R-0012 T1098 Privilege Escalation CRITICAL New User Added to Domain Admins
R-0007 T1078.004 Privilege Escalation HIGH AWS Root Account Usage
...
$ python library.py simulate samples/synthetic_events.jsonl
[*] Events scanned: 12
[*] Total rule hits: 10
R-0002 x1 [CRITICAL] Mimikatz / LSASS Memory Access
R-0012 x1 [CRITICAL] New User Added to Domain Admins
R-0005 x1 [CRITICAL] Impacket-style Remote Service Execution
...
```
并打开一个交互式的 MITRE ATT&CK 覆盖热力图:每个战术一列,按严重程度着色,每个规则对应可点击的方块。
## 截图(本地运行,零配置)
**终端输出** - 与命令行看到的一模一样:
**交互式 HTML 仪表板** - 在任意浏览器中打开,支持暗色模式、可过滤:
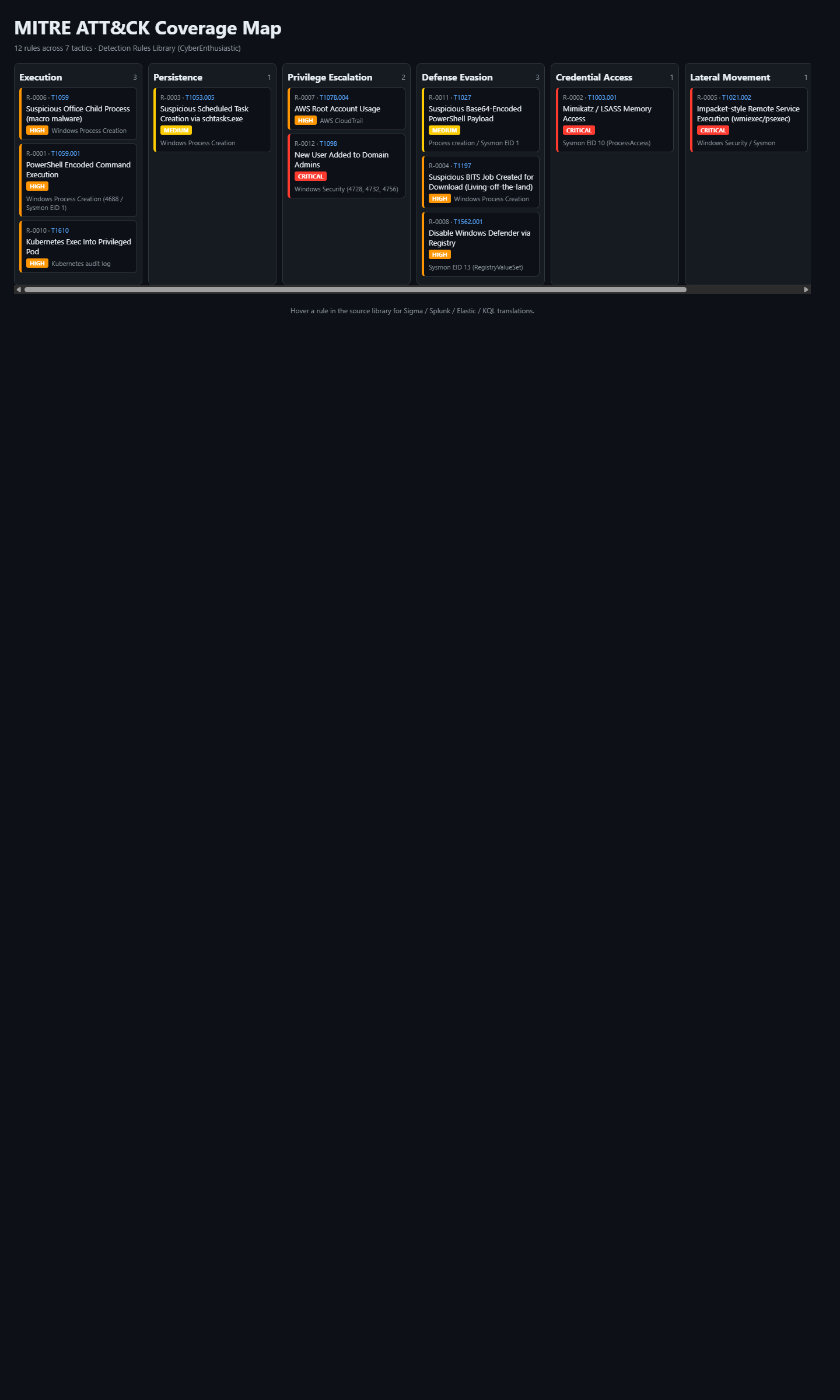
这两张截图均从针对捆绑的 `samples/` 目录的本地真实运行中捕获。使用以下快速入门命令即可复现。
## 为何选择此库
| | **本库** | SigmaHQ | Splunk ES CU | Elastic Detection Rules | Sentinel 内容中心 |
|---|---|---|---|---|---|
| **价格** | 免费(MIT) | 免费(OSS) | $$$$ 授权 | 免费(OSS) | 付费内容 |
| **单一事实来源** | 是(Python) | YAML | SPL | EQL/KQL | KQL |
| **导出 Sigma** | 是 | 原生支持 | 否 | 否 | 否 |
| **导出 Splunk SPL** | 是 | 通过转换器 | 原生支持 | 否 | 否 |
| **导出 Elastic EQL/KQL** | 是 | 通过转换器 | 否 | 原生支持 | 否 |
| **导出 Sentinel KQL** | 是 | 通过转换器 | 否 | 否 | 原生支持 |
| **内置 ATT&CK 覆盖热力图** | 是 | 外部 Navigator | Splunk Navigator | 通过 Navigator | 通过 Navigator |
| **规则测试模拟器** | 内置 | 无 | 无 | 通过测试框架 | 无 |
| **零运行时依赖** | 是 | 是 | Splunk 服务器 | Elastic 服务器 | Azure |
## 60 秒快速入门
```
# 克隆
git clone https://github.com/CyberEnthusiastic/mitre-attack-detection-rules.git
cd mitre-attack-detection-rules
# 列出所有规则
python library.py list
# 显示完整规则详情(所有查询语言)
python library.py show T1003.001
# 查看 ATT&CK 覆盖热力图
python library.py coverage
open reports/mitre_coverage.html
# 导出为您的 SIEM 格式
python library.py export sigma out/sigma/
python library.py export splunk out/splunk/
python library.py export elastic out/elastic/
python library.py export kql out/sentinel/
# 针对合成事件测试规则(离线)
python library.py simulate samples/synthetic_events.jsonl
```
### 替代方案:一键安装器
```
./install.sh # Linux/Mac/WSL/Git Bash
.\install.ps1 # Windows PowerShell
```
## 包含内容(12 条 curated 规则,扩展至 40+)
| ID | 标题 | 战术 | 技术 | 严重度 |
|----|-------|--------|-----------|-----|
| R-0001 | PowerShell 编码命令执行 | Execution | T1059.001 | HIGH |
| R-0002 | Mimikatz / LSASS 内存访问 | Credential Access | T1003.001 | CRITICAL |
| R-0003 | 可疑的计划任务创建 | Persistence | T1053.005 | MEDIUM |
| R-0004 | 可疑的 BITS 任务用于下载 | Defense Evasion | T1197 | HIGH |
| R-0005 | Impacket 风格的远程服务执行 | Lateral Movement | T1021.002 | CRITICAL |
| R-0006 | 可疑的 Office 子进程 | Execution | T1059 | HIGH |
| R-0007 | AWS 根账户使用 | Privilege Escalation | T1078.004 | HIGH |
| R-0008 | 通过注册表禁用 Defender | Defense Evasion | T1562.001 | HIGH |
| R-0009 | DNS 隧道(长查询) | C2 | T1071.004 | HIGH |
| R-0010 | Kubernetes 提权进入特权 Pod | Execution | T1610 | HIGH |
| R-0011 | Base64 编码的 PowerShell 载荷 | Defense Evasion | T1027 | MEDIUM |
| R-0012 | 新增用户至域管理员 | Privilege Escalation | T1098 | CRITICAL |
每条规则均附带 **四个即用查询**:
- Sigma YAML(适用于 Sigma 兼容引擎)
- Splunk SPL
- Elastic KQL/EQL
- Microsoft Sentinel KQL
以及元数据:数据源、引用、严重度、置信度、ATT&CK 战术 + 技术。
## 跨 SIEM 示例:`python library.py show T1003.001`
```
R-0002 Mimikatz / LSASS Memory Access
------------------------------------------
Tactic : Credential Access
Technique : T1003.001 (OS Credential Dumping: LSASS Memory)
Severity : CRITICAL Confidence: 0.95
Data source: Sysmon EID 10 (ProcessAccess)
--- Sigma ---
{ "detection": { "selection": { "EventID": 10, ... } } }
--- Splunk SPL ---
sourcetype=sysmon EventCode=10 TargetImage="*\lsass.exe" ...
--- Elastic (KQL/EQL) ---
event.code:"10" AND winlog.event_data.TargetImage:"*\\lsass.exe" ...
--- Microsoft Sentinel (KQL) ---
DeviceEvents | where ActionType == "OpenProcessApiCall" ...
```
## 规则测试模拟器(离线)
`simulate` 子命令在 JSONL 事件日志上运行规则 - 适用于回归测试检测、回顾事件或验证威胁狩猎数据集。
```
python library.py simulate samples/synthetic_events.jsonl
```
它针对每条规则的 Sigma `selection` 块评估每个事件并统计命中次数。实际生产环境的匹配应通过 SigmaHQ 的 `pySigma` 进行完整覆盖,但此离线匹配器可捕获约 70% 的 Sigma 检测模式。
## 导出格式
```
python library.py export sigma out/sigma/ # one .yml per rule
python library.py export splunk out/splunk/ # one .txt per rule (SPL)
python library.py export elastic out/elastic/ # one .txt per rule (KQL/EQL)
python library.py export kql out/sentinel/ # one .txt per rule (Sentinel KQL)
python library.py export json out/json/ # one .json per rule (full doc)
```
## ATT&CK 覆盖热力图
```
python library.py coverage
start reports/mitre_coverage.html
```
HTML 视图按战术列(侦察 -> 影响)布局每条规则,按严重程度着色,快速回答“我们的缺口在哪里?”
## 扩展本库
在 `library.py` 中向 `RULES` 添加一个字典:
```
{
"id": "R-0013",
"title": "Cobalt Strike Named Pipe",
"tactic": "Command and Control",
"technique": "T1071.001",
"severity": "CRITICAL",
"confidence": 0.90,
"data_source": "Sysmon EID 17 (PipeCreated)",
"references": ["https://attack.mitre.org/techniques/T1071/001/"],
"sigma": { "detection": { "selection": {
"EventID": 17, "PipeName|re": "\\\\\\\\.\\\\pipe\\\\MSSE-.*"
}, "condition": "selection" } },
"splunk": "sourcetype=sysmon EventCode=17 PipeName=\"\\\\\\\\.\\\\pipe\\\\MSSE-*\"",
"elastic": "event.code:\"17\" AND winlog.event_data.PipeName:/\\\\\\\\\\\\\\\\\\.\\\\\\\\pipe\\\\\\\\MSSE-.*/",
"kql": "DeviceEvents | where ActionType == \"NamedPipeEvent\" and PipeName startswith \"\\\\\\\\.\\\\pipe\\\\MSSE-\"",
},
```
## 项目结构
```
mitre-attack-detection-rules/
|-- library.py # rule library + CLI (list/search/show/export/coverage/simulate)
|-- report_generator.py # ATT&CK coverage HTML heatmap
|-- samples/
| `-- synthetic_events.jsonl # toy event log to exercise the simulator
|-- reports/ # output (gitignored)
|-- out/ # export destination (gitignored)
|-- Dockerfile
|-- install.sh / install.ps1
|-- requirements.txt # empty - pure stdlib
|-- README.md
`-- LICENSE / NOTICE / SECURITY.md / CONTRIBUTING.md
```
## 路线图
- [ ] 完整覆盖 40+ 条规则,涵盖每个 ATT&CK 战术
- [ ] pySigma 集成,实现全保真检测转换
- [ ] ATT&CK Navigator JSON 层导出
- [ ] 规则联动(多事件关联)
- [ ] 与 MISP / OpenCTI 威胁情报源集成
## 许可证
MIT。参见 [LICENSE](./LICENSE) 和 [NOTICE](./NOTICE)。
## 安全
负责任披露策略:参见 [SECURITY.md](./SECURITY.md)。
由 **[Mohith Vasamsetti (CyberEnthusiastic)](https://github.com/CyberEnthusiastic)** 构建,作为 [AI Security Projects](https://github.com/CyberEnthusiastic?tab=repositories) 套件的一部分。
标签:ATT&CK技术, AWS, Cloudflare, DPI, Elasticsearch, MITRE ATT&CK, MITRE框架, Python, Sentinel, Sigma规则, URL发现, 交互式仪表盘, 内存访问, 凭证访问, 协议分析, 域管理员, 多模态安全, 威胁情报, 安全检测, 安全运营, 导出, 开发者工具, 执行, 扫描框架, 文档结构分析, 无后门, 权限提升, 检测规则, 横向移动, 热图, 目标导入, 编程规范, 网络资产发现, 覆盖率热力图, 请求拦截, 远程服务执行, 逆向工具