amanpiyush/Offensive-Security-Resources-Bug-Hunt
GitHub: amanpiyush/Offensive-Security-Resources-Bug-Hunt
一个面向进攻安全与漏洞赏金的学习与实践资源聚合库,解决如何系统化构建侦察、测试与报告能力的问题。
Stars: 0 | Forks: 0
# 🏴☠️ 网络安全 / 进攻安全 / 漏洞赏金资源
## 📌 目录
* [🗺️ 学习路线](#️-roadmap)
* [📄 漏洞报告](#-bug-reports)
* [📚 书籍](#-books)
* [✅ 检查清单](#-checklist)
* [🧪 学习平台](#-learning-platforms)
* [🎯 漏洞赏金平台](#-bug-bounty-platforms)
* [🛠️ 侦察工具](#️-recon-tools)
* [🧠 博客与学习](#-blogs--learning)
* [⚙️ 方法论](#️-methodology)
* [📅 日常计划](#-daily-routine)
* [🧩 心态](#-mindset)
* [🚀 最后说明](#-final-note)
## 🗺️ 学习路线
### 🔹 网络安全学习指南
👉 [https://www.itshahirx.com/](https://www.itshahirx.com/roadmap)
### 🔹 AI 红队路线图
👉 [https://www.itshahirx.com/ai/roadmap](https://www.itshahirx.com/ai/roadmap)
## 📄 漏洞报告
### 🔹 HackerOne 报告(真实漏洞)
👉 [https://github.com/reddelexc/hackerone-reports](https://github.com/reddelexc/hackerone-reports)
### 🔹 10,000+ 已披露报告
👉 [https://github.com/shreyaschavhan/10000-h1-disclosed-reports](https://github.com/shreyaschavhan/10000-h1-disclosed-reports)
**为什么这很重要:**
* 学习真实黑客思维
* 理解漏洞利用链
* 改进报告撰写
* 发现高影响漏洞
## 📚 书籍
### 🔹 漏洞赏金书籍合集
👉 [https://github.com/akr3ch/BugBountyBooks](https://github.com/akr3ch/BugBountyBooks)
**重点领域:**
* Web 应用安全
* 网络与协议
* 漏洞利用技术
* 真实案例研究
## ✅ 检查清单
### 🔹 漏洞检查清单
👉 [https://github.com/Az0x7/vulnerability-Checklist](https://github.com/Az0x7/vulnerability-Checklist)
**用于:**
* 避免遗漏常见漏洞
* 遵循结构化测试
* 建立专业工作流程
## 🧪 学习平台
* 🔗 [https://portswigger.net/web-security](https://portswigger.net/web-security)
* 🔗 [https://www.hackthebox.com/](https://www.hackthebox.com/)
* 🔗 [https://tryhackme.com/](https://tryhackme.com/)
* 🔗 [https://pentesterlab.com/](https://pentesterlab.com/)
* 🔗 [https://www.root-me.org/](https://www.root-me.org/)
## 🎯 漏洞赏金平台
* 🔗 [https://www.hackerone.com/](https://www.hackerone.com/)
* 🔗 [https://www.bugcrowd.com/](https://www.bugcrowd.com/)
* 🔗 [https://www.intigriti.com/](https://www.intigriti.com/)
* 🔗 [https://www.yeswehack.com/](https://www.yeswehack.com/)
## 🛠️ 侦察工具
* **Amass**
* **Subfinder**
* **httpx**
* **Nuclei**
* **ffuf**
* **Burp Suite**
**学习:**
* 子域名枚举
* 资产发现
* 模糊测试
* 自动化工作流
## 🧠 博客与学习
### 🔹 Shreyas Chavhan
👉 [https://shreyaschavhan.notion.site/Shreyas-Chavhan-Blog-3921d456a8e344adb7c779d4258b8c17](https://shreyaschavhan.notion.site/Shreyas-Chavhan-Blog-3921d456a8e344adb7c779d4258b8c17)
### 🔹 Shahir (itshahirx)
👉 [https://www.itshahirx.com/](https://www.itshahirx.com/)
### 🔹 NahamSec
👉 [https://www.nahamsec.com/](https://www.nahamsec.com/)
👉 [https://www.youtube.com/@NahamSec](https://www.youtube.com/@NahamSec)
**学习:**
* 漏洞赏金工作流程
* 侦察策略
* 真实世界心态
### 🔹 Intigriti 博客
👉 [https://blog.intigriti.com/](https://blog.intigriti.com/)
### 🔹 HackerOne Hacktivity
👉 [https://hackerone.com/hacktivity](https://hackerone.com/hacktivity)
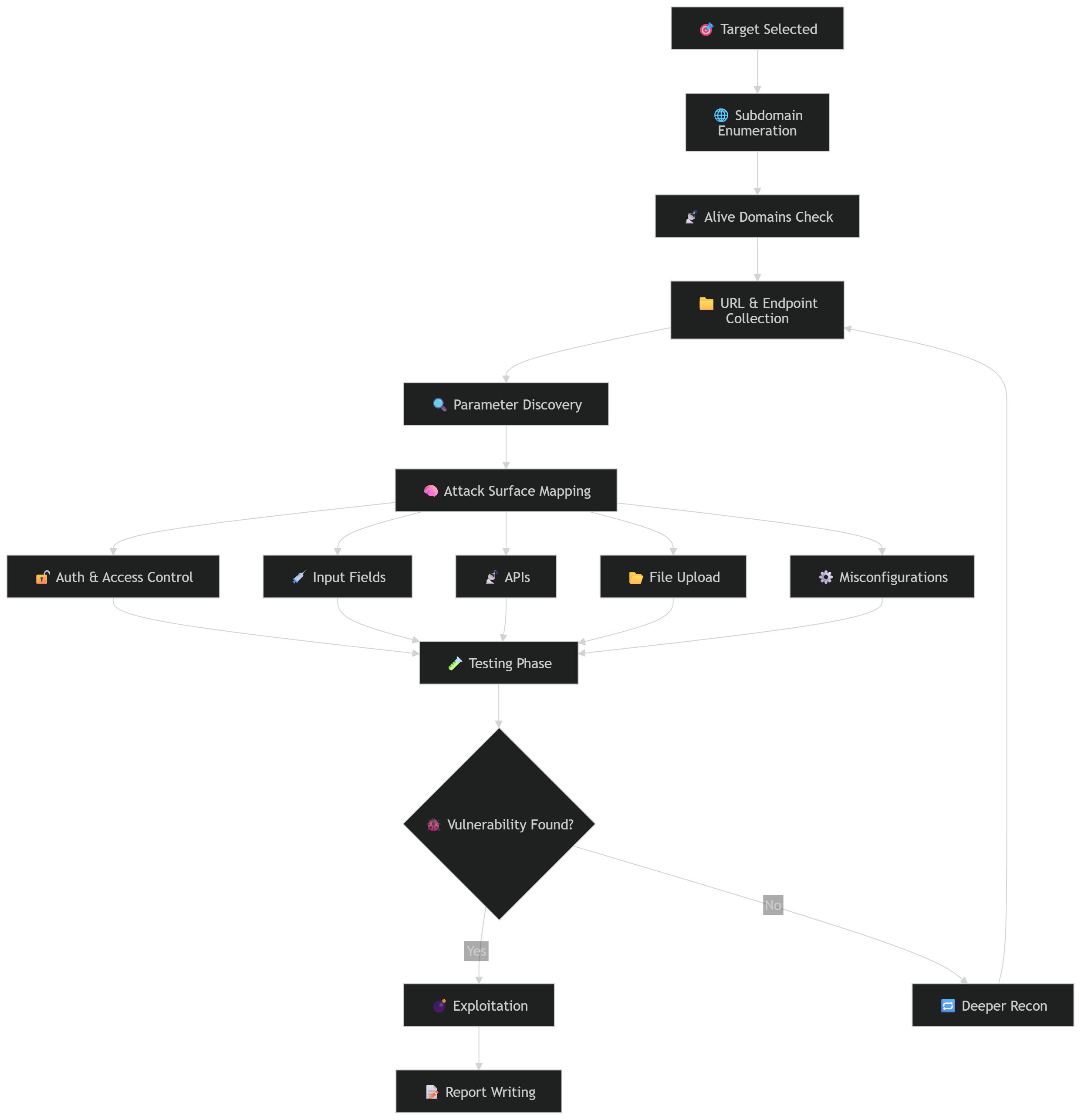
## ⚙️ 方法论
```
1. Recon → Find attack surface
2. Mapping → Understand application
3. Testing → Manual + Automated
4. Exploitation → Chain vulnerabilities
5. Reporting → Clear & impactful
```
**黄金法则:**
## 📅 日常计划
```
Daily Plan:
- 1–2 hrs → Fundamentals
- 1–2 hrs → Labs / Practice
- 1 hr → Bug Reports
- 1–2 hrs → Real Hunting
```
**每周目标:**
* 找到 ≥ 1 个有效漏洞
* 改进侦察流程
## 🧩 心态
* 坚持 > 动机
* 练习 > 理论
* 深度 > 随机学习
## 🚀 最后说明
```
> This repo is your base
> Skills come from execution
> Start hunting. Stay consistent
```
## 🏁 进阶资源(可选)
### ⚠️ Wiz 漏洞赏金大师班
👉 [https://www.wiz.io/bug-bounty-masterclass](https://www.wiz.io/bug-bounty-masterclass)
### ✅ 推荐替代方案
* 🔗 [https://www.nahamsec.com/](https://www.nahamsec.com/)
* 🔗 [https://www.youtube.com/@NahamSec](https://www.youtube.com/@NahamSec)
* 🔗 [https://hackerone.com/hacktivity](https://hackerone.com/hacktivity)
* 🔗 [https://blog.intigriti.com/](https://blog.intigriti.com/)
**这些提供:**
* 真实世界技术
* 高级侦察流程
* 实际漏洞利用
标签:Bug Bounty, C2框架, Web安全, 侦察工具, 可自定义解析器, 安全书籍, 安全学习资源, 安全社区, 安全课程, 实战训练, 攻击链, 数据展示, 漏洞报告, 红队, 红队平台, 网络安全, 蓝队分析, 进攻安全, 防御加固, 隐私保护, 黑客技术