xdrew87/PhantomTrace
GitHub: xdrew87/PhantomTrace
一款面向合法 OSINT 研究的 Python 模块化 CLI 框架,用于聚合多源公开情报并生成可导出报告。
Stars: 0 | Forks: 0
# 🔍 PhantomTrace




🌐 **[osintintelligence.xyz/phantomtrace](https://osintintelligence.xyz/phantomtrace.php)** — Official page & Pro version
**PhantomTrace** is a professional, modular OSINT (Open Source Intelligence) CLI framework for gathering publicly available intelligence on individuals and digital assets. Built with Python and Rich for a clean, production-grade experience.
## 截图
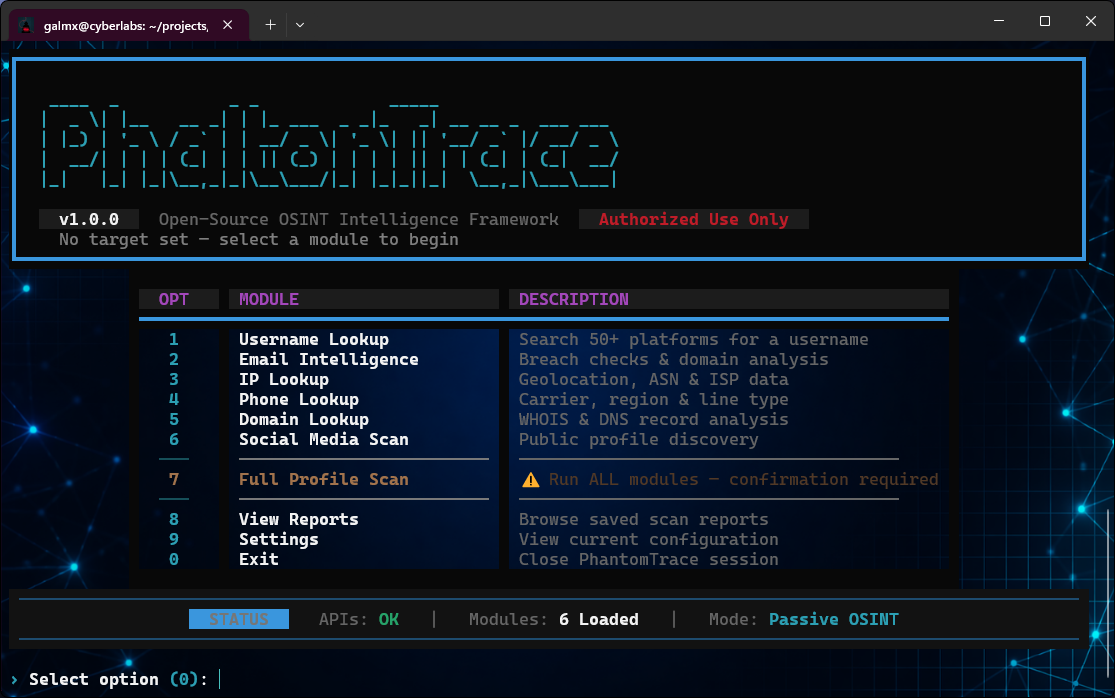
### 主菜单
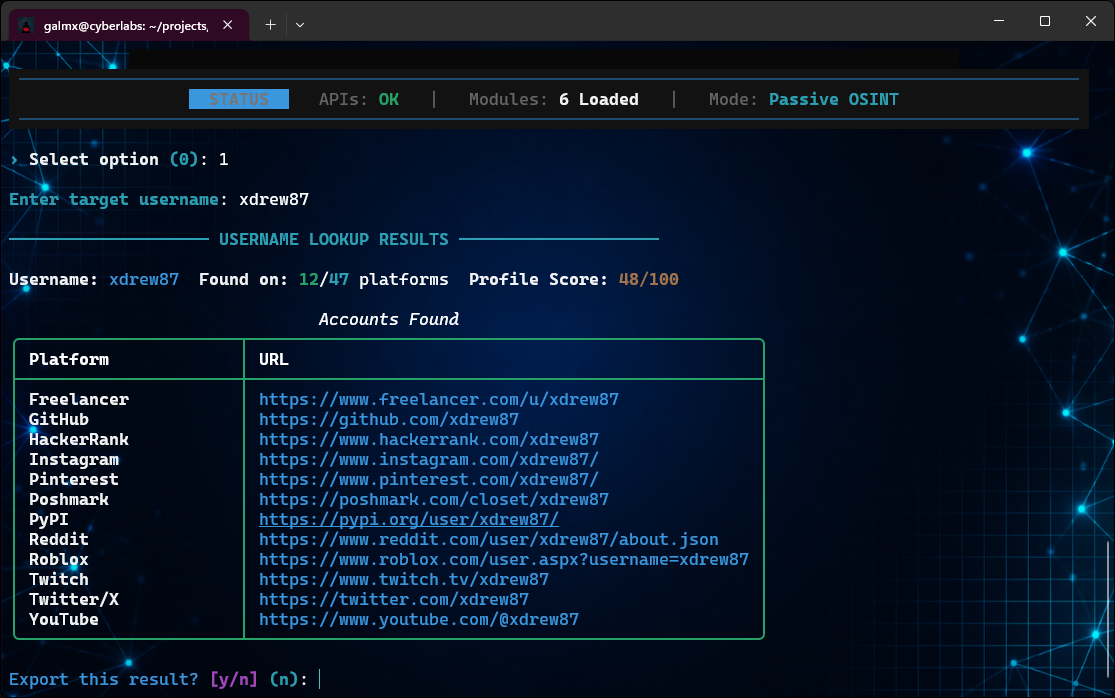
### 用户名查找
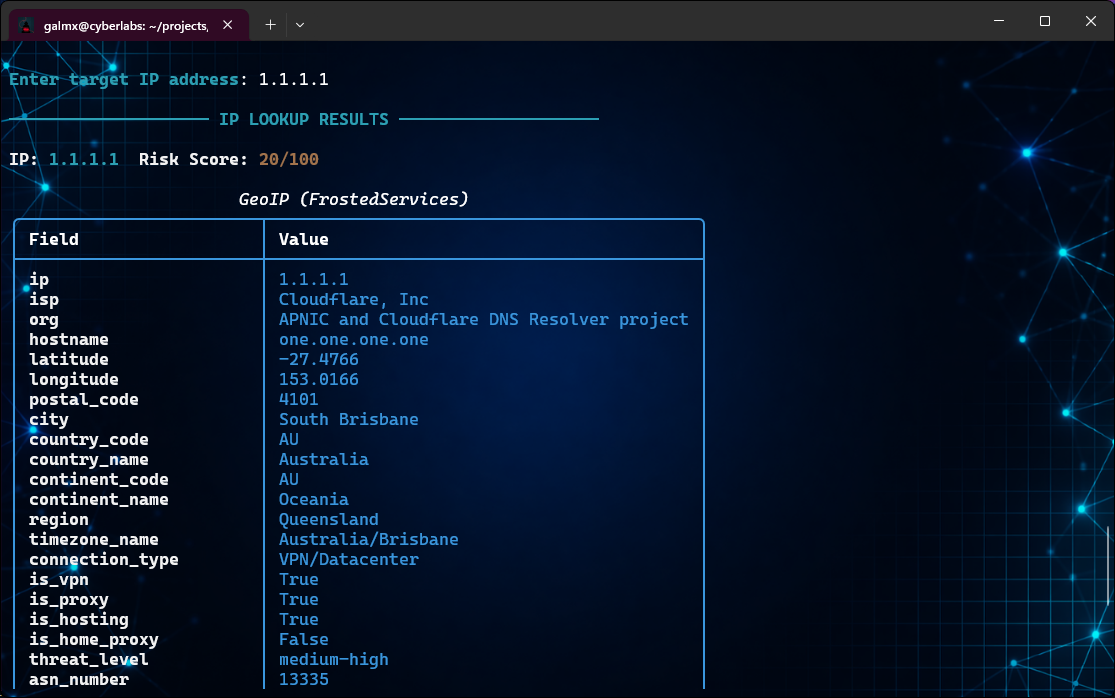
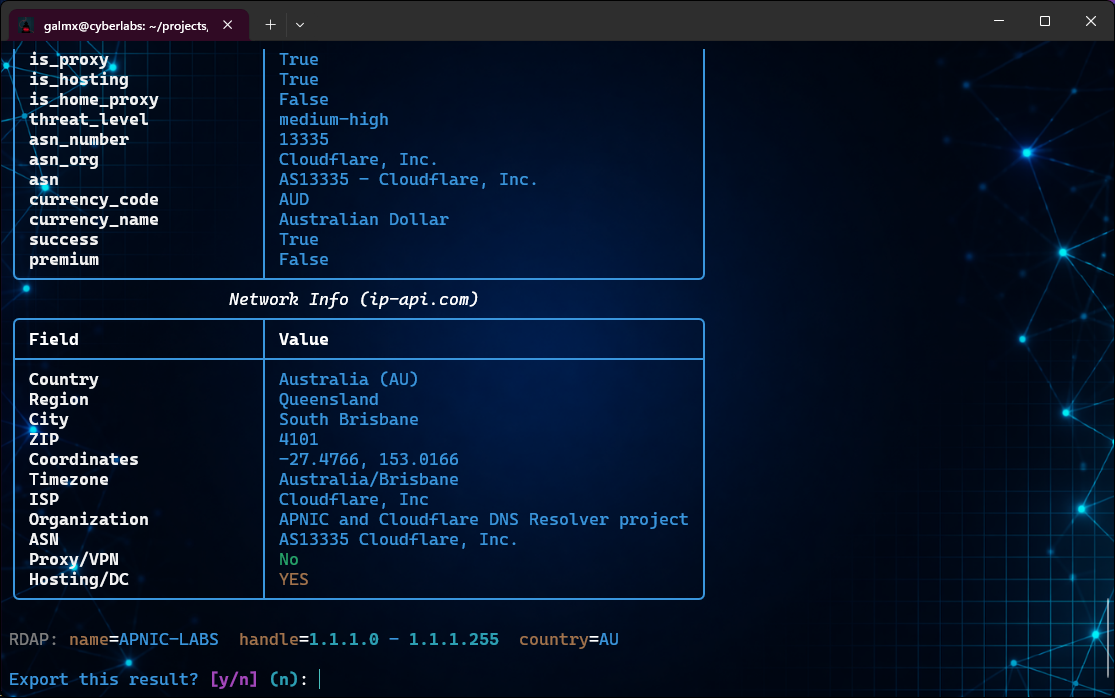
### IP 查找结果
### HTML 报告导出
## 功能
- **Username Lookup** — Search 50+ platforms for username presence
- **Email Intelligence** — Breach detection (HIBP), MX records, domain analysis
- **IP Lookup** — Geolocation via FrostedServices GeoIP + ip-api.com, ASN, ISP, proxy/VPN detection
- **Phone Lookup** — Carrier, region, line type via `phonenumbers` + optional NumVerify
- **Domain Lookup** — WHOIS, DNS (A/MX/NS/TXT/SOA/CNAME), HTTP headers
- **Social Media Scan** — Public profile discovery across 15 major platforms
- **Full Profile Scan** — Run all modules against a single target
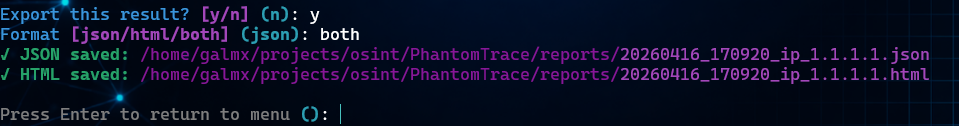
- **Report Export** — JSON and styled HTML reports saved locally
- **Scoring System** — Risk/profile completeness scores per module
- **Activity Logging** — All sessions logged to `logs/`
## 安装
```
git clone https://github.com/xdrew87/PhantomTrace.git
cd PhantomTrace
pip install -r requirements.txt
cp config/.env.example config/.env
# 编辑 config/.env 并添加可选的 API 密钥
python main.py
```
## 配置
The tool works **without any API keys** — keys unlock additional data sources.
Copy `config/.env.example` to `config/.env` and optionally add keys:
| Variable | Service | Notes |
|---|---|---|
| `HIBP_API_KEY` | HaveIBeenPwned | Email breach lookup |
| `NUMVERIFY_API_KEY` | NumVerify | Enhanced phone data |
| `HUNTER_API_KEY` | Hunter.io | Email verification |
IP geolocation uses the built-in [FrostedServices GeoIP API](https://frostedservices.xyz/api/geoip/) — no key needed.
## 用法
```
python main.py
```
Select modules from the interactive menu. Results are displayed in formatted tables and optionally exported to `reports/`.
## 项目结构
```
PhantomTrace/
├── main.py # Entry point & CLI menu
├── modules/ # OSINT modules (one per data type)
│ ├── username_lookup.py
│ ├── email_intel.py
│ ├── ip_lookup.py
│ ├── phone_lookup.py
│ ├── domain_lookup.py
│ └── social_media.py
├── utils/ # Helpers: API, logging, formatting, reporting
├── config/ # Settings & API key configuration
├── reports/ # Exported reports (JSON & HTML)
└── logs/ # Activity logs
```
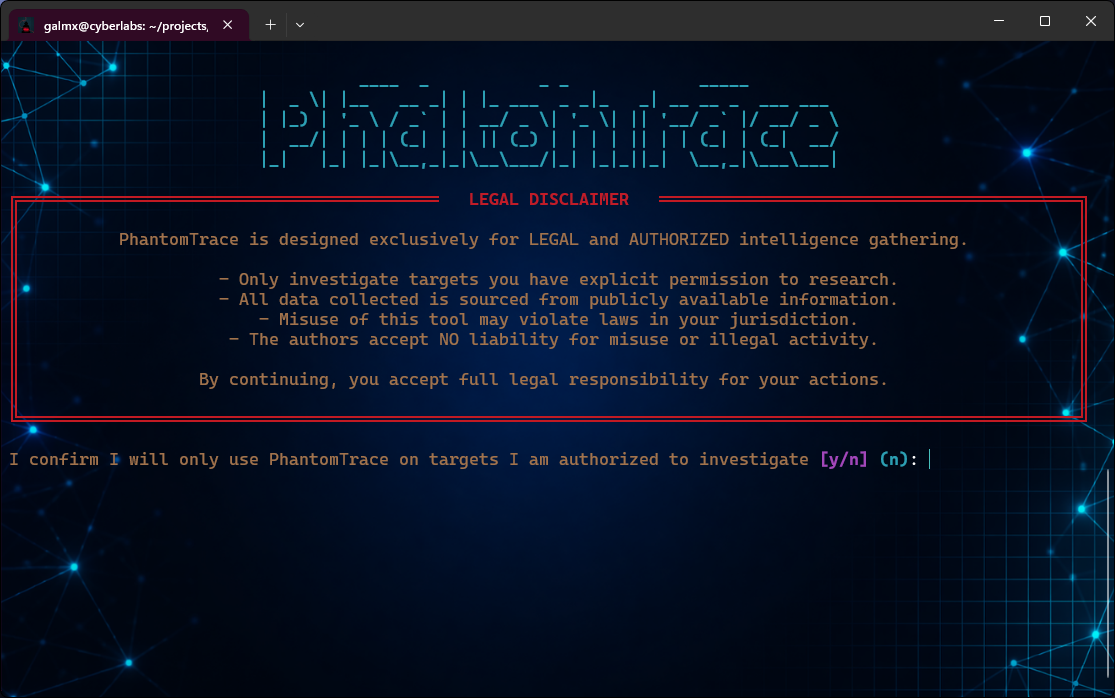
## 免责声明
PhantomTrace is intended for **legal OSINT research only** — penetration testers, security researchers, journalists, and investigators with proper authorization. The authors accept no liability for misuse.
## 许可证
MIT — see [LICENSE](LICENSE)
标签:ASN, Atomic Red Team, DNS, ESC4, ETW劫持, HIBP, HTML报告, HTTP头, IP查询, JSON, OSINT, Python, Rich, SEO, VPN检测, WHOIS, 代理检测, 公开资料, 区域, 反取证, 反射式DLL注入, 地理位置, 威胁情报, 安全评估, 开发者工具, 情报收集, 手机号查询, 报告导出, 数据泄露检测, 无后门, 日志记录, 模块化框架, 漏洞研究, 生产级, 用户名查找, 社交媒体, 社交网络扫描, 运营商, 逆向工具, 邮箱查询, 风险评分