ninoseki/mitaka
GitHub: ninoseki/mitaka
一款浏览器扩展,支持选中 IOC 威胁指标并自动反混淆,右键即可跳转至 65+ 个安全情报平台进行查询或扫描。
Stars: 1733 | Forks: 175
# 三鹰
[](https://github.com/ninoseki/mitaka/actions?query=workflow%3A%22Node.js+CI%22)
[](https://www.codefactor.io/repository/github/ninoseki/mitaka)
[](https://coveralls.io/github/ninoseki/mitaka)
Mitaka 是一款浏览器扩展,旨在让您的 OSINT(开源情报)搜索与扫描更加轻松。
- 主要特性:
- 自动 IoC(威胁指标)选择与反混淆。
- 例如:将 `example[.]com` 转换为 `example.com`,将 `test[at]example.com` 转换为 `test@example.com`,将 `hxxp://example.com` 转换为 `http://example.com` 等。
- 支持 65+ 种服务。
## 安装
 [
[ ][link-cws] [
][link-cws] [ ][link-cws]
][link-cws]
 [
[ ][link-amo] [
][link-amo] [ ][link-amo]
## 功能
### 支持的 IoC(威胁指标)
| 名称 | 描述 | 例如 |
| :-------- | :-------------------------- | :------------------------------------------- |
| ANS | ASN | `AS13335` |
| BTC | BTC 地址 | `1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa` |
| CVE | CVE 编号 | `CVE-2018-11776` |
| Domain | 域名 | `github.com` |
| Email | 电子邮件地址 | `test@test.com` |
| ETH | 以太坊地址 | `0x32be343b94f860124dc4fee278fdcbd38c102d88` |
| GaPubID | Google Adsense 发布者 ID | `pub-9383614236930773` |
| GaTrackID | Google Analytics 跟踪 ID | `UA-67609351-1` |
| Hash | MD5, SHA1, SHA256 | `44d88612fea8a8f36de82e1278abb02f` |
| IP | IPv4 地址 | `8.8.8.8` |
| URL | URL | `https://github.com` |
### 支持的搜索引擎
| 名称 | URL | 支持的类型 |
| :------------------- | :------------------------------------- | :------------------------- |
| AbuseIPDB | https://www.abuseipdb.com | IP |
| AnyRun | https://app.any.run | Hash |
| archive.org | https://archive.org | URL |
| Blockchain.com | https://www.blockchain.com | BTC |
| BlockCypher | https://live.blockcypher.com | BTC |
| Censys | https://censys.io | IP, domain, ASN, email |
| Checkphish | https://checkphish.ai | IP, domain |
| Coalition | https://ess.coalitioninc.com | CVE |
| crt.sh | https://crt.sh | Domain |
| CVE | https://cve.org | CVE |
| DNS Coffee | https://dns.coffee | Domain |
| DNSlytics | https://dnslytics.com | IP, domain |
| DomainTools | https://www.domaintools.com | IP, domain |
| EmailRep | https://emailrep.io | Email |
| FileScan.IO | https://filescan.io | Hash |
| FortiGuard | https://fortiguard.com | IP, URL, CVE |
| Google Safe Browsing | https://transparencyreport.google.com | Domain, URL |
| GreyNoise | https://viz.greynoise.io | IP, domain, ASN, CVE |
| Host.io | https://host.io | Domain |
| Hurricane Electric | https://bgp.he.net/ | IP, domain, ASN |
| HybridAnalysis | https://www.hybrid-analysis.com | IP, domain, hash |
| Intezer | https://analyze.intezer.com | Hash |
| IPinfo | https://ipinfo.io | IP, ASN |
| IPIP | https://en.ipip.net | IP, ASN |
| Joe Sandbox | https://www.joesandbox.com | Hash |
| Maltiverse | https://www.maltiverse.com | Domain, hash |
| MalwareBazaar | https://bazaar.abuse.ch | Hash |
| NVD | https://nvd.nist.gov | CVE |
| OOCPR | https://data.occrp.org | Email |
| ONYPHE | https://www.onyphe.io | IP |
| OpenTIP | https://opentip.kaspersky.com | Hash |
| OTX | https://otx.alienvault.com | IP, domain, CVE, URL, hash |
| Pulsedive | https://pulsedive.com | IP, domain, URL, hash |
| Radar | https://radar.cloudflare.com | IP, domain |
| Robtex | https://www.robtex.com | IP, domain |
| Scumware | https://www.scumware.org | IP, domain, hash (MD5) |
| SecurityTrails | https://securitytrails.com | IP, domain |
| Shodan | https://www.shodan.io | IP, domain, ASN |
| Sploitus | https://sploitus.com | CVE |
| Talos | https://talosintelligence.com | IP, domain |
| ThreatBook | https://threatbook.io | IP, domain |
| ThreatConnect | https://app.threatconnect.com | IP, domain, email |
| ThreatMiner | https://www.threatminer.org | IP, domain, hash |
| TIP | https://threatintelligenceplatform.com | IP, domain |
| Triage | https://tria.ge | Hash, URL |
| URLhaus | https://urlhaus.abuse.ch | IP, domain |
| urlscan.io | https://urlscan.io | IP, domain, ASN, URL |
| URLVoid | https://www.urlvoid.com | Domain |
| ViewDNS | https://viewdns.info | IP, domain, email |
| VirusTotal | https://www.virustotal.com | IP, domain, URL, hash |
| VMRay | https://www.vmray.com | Hash |
| Vulmon | https://vulmon.com | CVE |
| WebCheck | https://web-check.xyz | Domain |
| X-Force Exchange | https://exchange.xforce.ibmcloud.com | IP, domain, hash |
| ZoomEye | https://www.zoomeye.ai | IP |
### 支持的扫描引擎
| 名称 | url | 支持的类型 |
| :------------- | :------------------------------ | :-------------- |
| Browserling | https://www.browserling.com | URL |
| HybridAnalysis | https://www.hybrid-analysis.com | URL |
| urlscan.io | https://urlscan.io | IP, domain, URL |
| VirusTotal | https://www.virustotal.com | URL |
## 如何使用
- [使用 Mitaka 在浏览器中进行 OSINT 以识别恶意软件、可疑网站、可疑邮件等](https://null-byte.wonderhowto.com/how-to/use-mitaka-perform-browser-osint-identify-malware-sketchy-sites-shady-emails-more-0216352/)
**注意:** 请在选项中设置您的 API 密钥,以启用 HybridAnalysis、urlscan.io 和 VirusTotal 扫描。
## 选项
您可以根据自己的偏好,在选项页面启用或禁用搜索引擎。

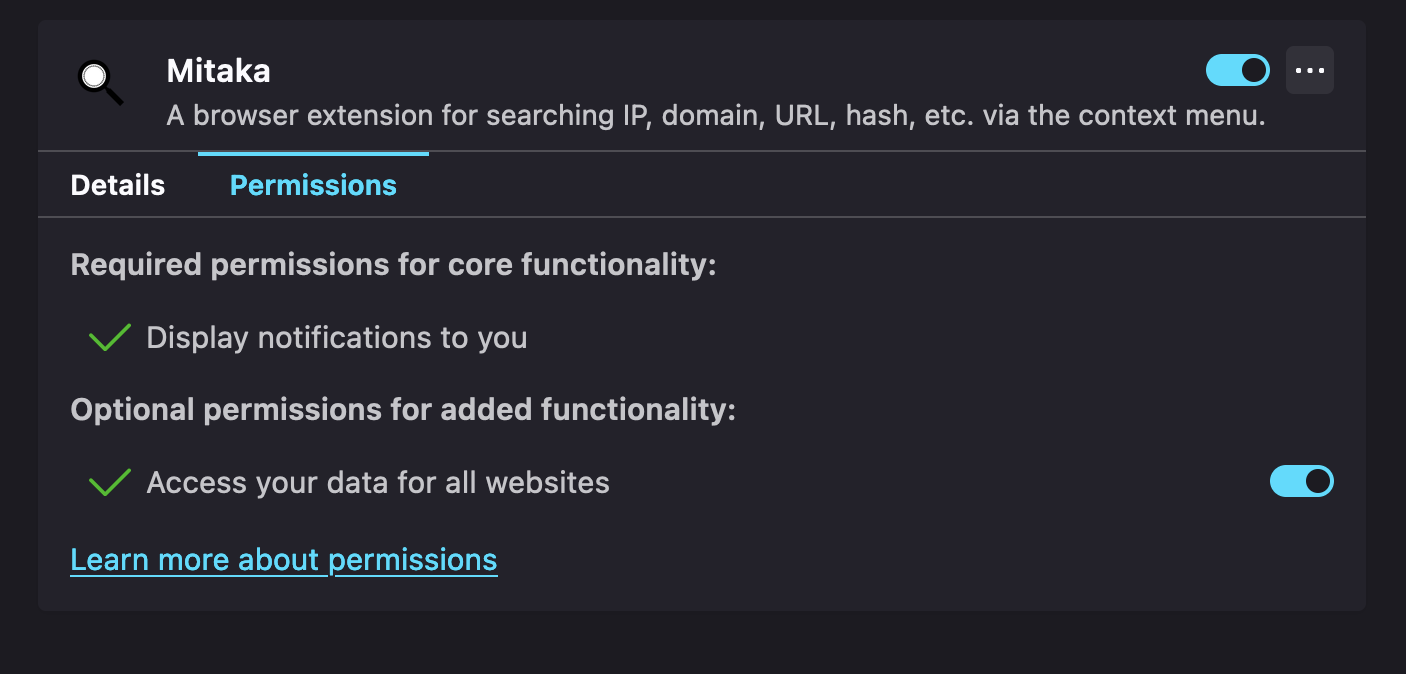
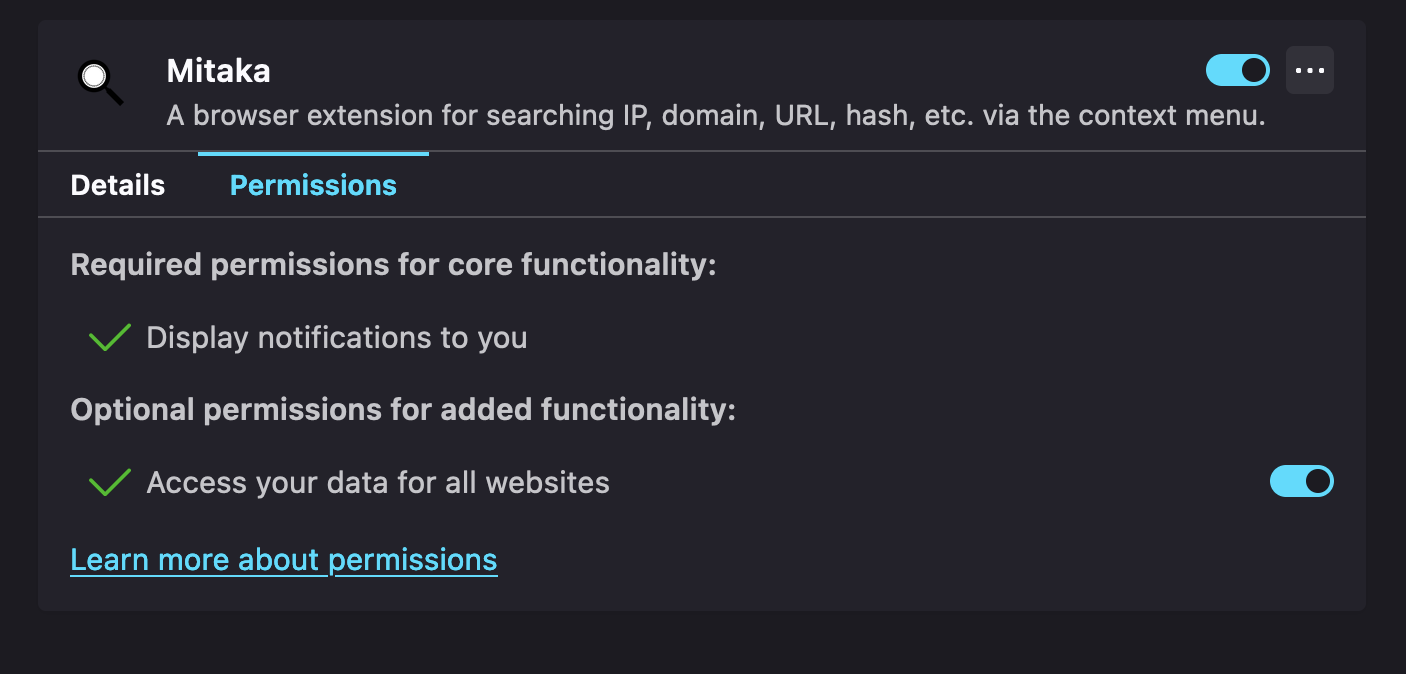
## 权限
### Firefox
请允许“访问所有网站的数据”权限。否则此扩展将无法工作。
][link-amo]
## 功能
### 支持的 IoC(威胁指标)
| 名称 | 描述 | 例如 |
| :-------- | :-------------------------- | :------------------------------------------- |
| ANS | ASN | `AS13335` |
| BTC | BTC 地址 | `1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa` |
| CVE | CVE 编号 | `CVE-2018-11776` |
| Domain | 域名 | `github.com` |
| Email | 电子邮件地址 | `test@test.com` |
| ETH | 以太坊地址 | `0x32be343b94f860124dc4fee278fdcbd38c102d88` |
| GaPubID | Google Adsense 发布者 ID | `pub-9383614236930773` |
| GaTrackID | Google Analytics 跟踪 ID | `UA-67609351-1` |
| Hash | MD5, SHA1, SHA256 | `44d88612fea8a8f36de82e1278abb02f` |
| IP | IPv4 地址 | `8.8.8.8` |
| URL | URL | `https://github.com` |
### 支持的搜索引擎
| 名称 | URL | 支持的类型 |
| :------------------- | :------------------------------------- | :------------------------- |
| AbuseIPDB | https://www.abuseipdb.com | IP |
| AnyRun | https://app.any.run | Hash |
| archive.org | https://archive.org | URL |
| Blockchain.com | https://www.blockchain.com | BTC |
| BlockCypher | https://live.blockcypher.com | BTC |
| Censys | https://censys.io | IP, domain, ASN, email |
| Checkphish | https://checkphish.ai | IP, domain |
| Coalition | https://ess.coalitioninc.com | CVE |
| crt.sh | https://crt.sh | Domain |
| CVE | https://cve.org | CVE |
| DNS Coffee | https://dns.coffee | Domain |
| DNSlytics | https://dnslytics.com | IP, domain |
| DomainTools | https://www.domaintools.com | IP, domain |
| EmailRep | https://emailrep.io | Email |
| FileScan.IO | https://filescan.io | Hash |
| FortiGuard | https://fortiguard.com | IP, URL, CVE |
| Google Safe Browsing | https://transparencyreport.google.com | Domain, URL |
| GreyNoise | https://viz.greynoise.io | IP, domain, ASN, CVE |
| Host.io | https://host.io | Domain |
| Hurricane Electric | https://bgp.he.net/ | IP, domain, ASN |
| HybridAnalysis | https://www.hybrid-analysis.com | IP, domain, hash |
| Intezer | https://analyze.intezer.com | Hash |
| IPinfo | https://ipinfo.io | IP, ASN |
| IPIP | https://en.ipip.net | IP, ASN |
| Joe Sandbox | https://www.joesandbox.com | Hash |
| Maltiverse | https://www.maltiverse.com | Domain, hash |
| MalwareBazaar | https://bazaar.abuse.ch | Hash |
| NVD | https://nvd.nist.gov | CVE |
| OOCPR | https://data.occrp.org | Email |
| ONYPHE | https://www.onyphe.io | IP |
| OpenTIP | https://opentip.kaspersky.com | Hash |
| OTX | https://otx.alienvault.com | IP, domain, CVE, URL, hash |
| Pulsedive | https://pulsedive.com | IP, domain, URL, hash |
| Radar | https://radar.cloudflare.com | IP, domain |
| Robtex | https://www.robtex.com | IP, domain |
| Scumware | https://www.scumware.org | IP, domain, hash (MD5) |
| SecurityTrails | https://securitytrails.com | IP, domain |
| Shodan | https://www.shodan.io | IP, domain, ASN |
| Sploitus | https://sploitus.com | CVE |
| Talos | https://talosintelligence.com | IP, domain |
| ThreatBook | https://threatbook.io | IP, domain |
| ThreatConnect | https://app.threatconnect.com | IP, domain, email |
| ThreatMiner | https://www.threatminer.org | IP, domain, hash |
| TIP | https://threatintelligenceplatform.com | IP, domain |
| Triage | https://tria.ge | Hash, URL |
| URLhaus | https://urlhaus.abuse.ch | IP, domain |
| urlscan.io | https://urlscan.io | IP, domain, ASN, URL |
| URLVoid | https://www.urlvoid.com | Domain |
| ViewDNS | https://viewdns.info | IP, domain, email |
| VirusTotal | https://www.virustotal.com | IP, domain, URL, hash |
| VMRay | https://www.vmray.com | Hash |
| Vulmon | https://vulmon.com | CVE |
| WebCheck | https://web-check.xyz | Domain |
| X-Force Exchange | https://exchange.xforce.ibmcloud.com | IP, domain, hash |
| ZoomEye | https://www.zoomeye.ai | IP |
### 支持的扫描引擎
| 名称 | url | 支持的类型 |
| :------------- | :------------------------------ | :-------------- |
| Browserling | https://www.browserling.com | URL |
| HybridAnalysis | https://www.hybrid-analysis.com | URL |
| urlscan.io | https://urlscan.io | IP, domain, URL |
| VirusTotal | https://www.virustotal.com | URL |
## 如何使用
- [使用 Mitaka 在浏览器中进行 OSINT 以识别恶意软件、可疑网站、可疑邮件等](https://null-byte.wonderhowto.com/how-to/use-mitaka-perform-browser-osint-identify-malware-sketchy-sites-shady-emails-more-0216352/)
**注意:** 请在选项中设置您的 API 密钥,以启用 HybridAnalysis、urlscan.io 和 VirusTotal 扫描。
## 选项
您可以根据自己的偏好,在选项页面启用或禁用搜索引擎。

## 权限
### Firefox
请允许“访问所有网站的数据”权限。否则此扩展将无法工作。
 ## 隐私政策
- [扩展的隐私政策](https://ninoseki.github.io/chrome-webstore/privacy-policy/)
## 常见问题
- 问:没有显示上下文菜单(右键菜单)。
- 答:有时上下文菜单需要一段时间才会出现。或者在刷新上下文菜单时出现了问题。这种小故障可以通过稍等片刻来解决。请在选择后深呼吸一下,然后点击右键。
## 替代品或类似工具
- [CrowdScrape](https://chrome.google.com/webstore/detail/crowdscrape/jjplaeklnlddpkbbdbnogmppffokemej)
- [Gotanda](https://github.com/HASH1da1/Gotanda)
- [SOC Multi-tool](https://github.com/zdhenard42/SOC-Multitool)
- [Sputnik](https://github.com/mitchmoser/sputnik)
- [ThreatConnect Integrated Chrome Extension](https://chrome.google.com/webstore/detail/threatconnect-integrated/lblgcphpihpadjdpjgjnnoikjdjcnkbh)
- [ThreatPinch Lookup](https://github.com/cloudtracer/ThreatPinchLookup)
- [VTchromizer](https://chrome.google.com/webstore/detail/vtchromizer/efbjojhplkelaegfbieplglfidafgoka)
## 工作原理
```
flowchart LR
CS[Content Script] --> |1 - Send Selection| BSW[Background Service Worker]
BSW --> |2 - Create Context Menus| CS
CS --> |3 - Click Context Menu| BSW
BSW --> |4 - Search/Scan| T[New Tab]
```
## 贡献
阅读[贡献指南](contributing.md)并加入[贡献者](https://github.com/ninoseki/mitaka/graphs/contributors)的行列。
## 隐私政策
- [扩展的隐私政策](https://ninoseki.github.io/chrome-webstore/privacy-policy/)
## 常见问题
- 问:没有显示上下文菜单(右键菜单)。
- 答:有时上下文菜单需要一段时间才会出现。或者在刷新上下文菜单时出现了问题。这种小故障可以通过稍等片刻来解决。请在选择后深呼吸一下,然后点击右键。
## 替代品或类似工具
- [CrowdScrape](https://chrome.google.com/webstore/detail/crowdscrape/jjplaeklnlddpkbbdbnogmppffokemej)
- [Gotanda](https://github.com/HASH1da1/Gotanda)
- [SOC Multi-tool](https://github.com/zdhenard42/SOC-Multitool)
- [Sputnik](https://github.com/mitchmoser/sputnik)
- [ThreatConnect Integrated Chrome Extension](https://chrome.google.com/webstore/detail/threatconnect-integrated/lblgcphpihpadjdpjgjnnoikjdjcnkbh)
- [ThreatPinch Lookup](https://github.com/cloudtracer/ThreatPinchLookup)
- [VTchromizer](https://chrome.google.com/webstore/detail/vtchromizer/efbjojhplkelaegfbieplglfidafgoka)
## 工作原理
```
flowchart LR
CS[Content Script] --> |1 - Send Selection| BSW[Background Service Worker]
BSW --> |2 - Create Context Menus| CS
CS --> |3 - Click Context Menu| BSW
BSW --> |4 - Search/Scan| T[New Tab]
```
## 贡献
阅读[贡献指南](contributing.md)并加入[贡献者](https://github.com/ninoseki/mitaka/graphs/contributors)的行列。
 ][link-cws] [
][link-cws] [ ][link-cws]
][link-cws]
 ][link-amo] [
][link-amo] [ ][link-amo]
## 功能
### 支持的 IoC(威胁指标)
| 名称 | 描述 | 例如 |
| :-------- | :-------------------------- | :------------------------------------------- |
| ANS | ASN | `AS13335` |
| BTC | BTC 地址 | `1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa` |
| CVE | CVE 编号 | `CVE-2018-11776` |
| Domain | 域名 | `github.com` |
| Email | 电子邮件地址 | `test@test.com` |
| ETH | 以太坊地址 | `0x32be343b94f860124dc4fee278fdcbd38c102d88` |
| GaPubID | Google Adsense 发布者 ID | `pub-9383614236930773` |
| GaTrackID | Google Analytics 跟踪 ID | `UA-67609351-1` |
| Hash | MD5, SHA1, SHA256 | `44d88612fea8a8f36de82e1278abb02f` |
| IP | IPv4 地址 | `8.8.8.8` |
| URL | URL | `https://github.com` |
### 支持的搜索引擎
| 名称 | URL | 支持的类型 |
| :------------------- | :------------------------------------- | :------------------------- |
| AbuseIPDB | https://www.abuseipdb.com | IP |
| AnyRun | https://app.any.run | Hash |
| archive.org | https://archive.org | URL |
| Blockchain.com | https://www.blockchain.com | BTC |
| BlockCypher | https://live.blockcypher.com | BTC |
| Censys | https://censys.io | IP, domain, ASN, email |
| Checkphish | https://checkphish.ai | IP, domain |
| Coalition | https://ess.coalitioninc.com | CVE |
| crt.sh | https://crt.sh | Domain |
| CVE | https://cve.org | CVE |
| DNS Coffee | https://dns.coffee | Domain |
| DNSlytics | https://dnslytics.com | IP, domain |
| DomainTools | https://www.domaintools.com | IP, domain |
| EmailRep | https://emailrep.io | Email |
| FileScan.IO | https://filescan.io | Hash |
| FortiGuard | https://fortiguard.com | IP, URL, CVE |
| Google Safe Browsing | https://transparencyreport.google.com | Domain, URL |
| GreyNoise | https://viz.greynoise.io | IP, domain, ASN, CVE |
| Host.io | https://host.io | Domain |
| Hurricane Electric | https://bgp.he.net/ | IP, domain, ASN |
| HybridAnalysis | https://www.hybrid-analysis.com | IP, domain, hash |
| Intezer | https://analyze.intezer.com | Hash |
| IPinfo | https://ipinfo.io | IP, ASN |
| IPIP | https://en.ipip.net | IP, ASN |
| Joe Sandbox | https://www.joesandbox.com | Hash |
| Maltiverse | https://www.maltiverse.com | Domain, hash |
| MalwareBazaar | https://bazaar.abuse.ch | Hash |
| NVD | https://nvd.nist.gov | CVE |
| OOCPR | https://data.occrp.org | Email |
| ONYPHE | https://www.onyphe.io | IP |
| OpenTIP | https://opentip.kaspersky.com | Hash |
| OTX | https://otx.alienvault.com | IP, domain, CVE, URL, hash |
| Pulsedive | https://pulsedive.com | IP, domain, URL, hash |
| Radar | https://radar.cloudflare.com | IP, domain |
| Robtex | https://www.robtex.com | IP, domain |
| Scumware | https://www.scumware.org | IP, domain, hash (MD5) |
| SecurityTrails | https://securitytrails.com | IP, domain |
| Shodan | https://www.shodan.io | IP, domain, ASN |
| Sploitus | https://sploitus.com | CVE |
| Talos | https://talosintelligence.com | IP, domain |
| ThreatBook | https://threatbook.io | IP, domain |
| ThreatConnect | https://app.threatconnect.com | IP, domain, email |
| ThreatMiner | https://www.threatminer.org | IP, domain, hash |
| TIP | https://threatintelligenceplatform.com | IP, domain |
| Triage | https://tria.ge | Hash, URL |
| URLhaus | https://urlhaus.abuse.ch | IP, domain |
| urlscan.io | https://urlscan.io | IP, domain, ASN, URL |
| URLVoid | https://www.urlvoid.com | Domain |
| ViewDNS | https://viewdns.info | IP, domain, email |
| VirusTotal | https://www.virustotal.com | IP, domain, URL, hash |
| VMRay | https://www.vmray.com | Hash |
| Vulmon | https://vulmon.com | CVE |
| WebCheck | https://web-check.xyz | Domain |
| X-Force Exchange | https://exchange.xforce.ibmcloud.com | IP, domain, hash |
| ZoomEye | https://www.zoomeye.ai | IP |
### 支持的扫描引擎
| 名称 | url | 支持的类型 |
| :------------- | :------------------------------ | :-------------- |
| Browserling | https://www.browserling.com | URL |
| HybridAnalysis | https://www.hybrid-analysis.com | URL |
| urlscan.io | https://urlscan.io | IP, domain, URL |
| VirusTotal | https://www.virustotal.com | URL |
## 如何使用
- [使用 Mitaka 在浏览器中进行 OSINT 以识别恶意软件、可疑网站、可疑邮件等](https://null-byte.wonderhowto.com/how-to/use-mitaka-perform-browser-osint-identify-malware-sketchy-sites-shady-emails-more-0216352/)
**注意:** 请在选项中设置您的 API 密钥,以启用 HybridAnalysis、urlscan.io 和 VirusTotal 扫描。
## 选项
您可以根据自己的偏好,在选项页面启用或禁用搜索引擎。

## 权限
### Firefox
请允许“访问所有网站的数据”权限。否则此扩展将无法工作。
][link-amo]
## 功能
### 支持的 IoC(威胁指标)
| 名称 | 描述 | 例如 |
| :-------- | :-------------------------- | :------------------------------------------- |
| ANS | ASN | `AS13335` |
| BTC | BTC 地址 | `1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa` |
| CVE | CVE 编号 | `CVE-2018-11776` |
| Domain | 域名 | `github.com` |
| Email | 电子邮件地址 | `test@test.com` |
| ETH | 以太坊地址 | `0x32be343b94f860124dc4fee278fdcbd38c102d88` |
| GaPubID | Google Adsense 发布者 ID | `pub-9383614236930773` |
| GaTrackID | Google Analytics 跟踪 ID | `UA-67609351-1` |
| Hash | MD5, SHA1, SHA256 | `44d88612fea8a8f36de82e1278abb02f` |
| IP | IPv4 地址 | `8.8.8.8` |
| URL | URL | `https://github.com` |
### 支持的搜索引擎
| 名称 | URL | 支持的类型 |
| :------------------- | :------------------------------------- | :------------------------- |
| AbuseIPDB | https://www.abuseipdb.com | IP |
| AnyRun | https://app.any.run | Hash |
| archive.org | https://archive.org | URL |
| Blockchain.com | https://www.blockchain.com | BTC |
| BlockCypher | https://live.blockcypher.com | BTC |
| Censys | https://censys.io | IP, domain, ASN, email |
| Checkphish | https://checkphish.ai | IP, domain |
| Coalition | https://ess.coalitioninc.com | CVE |
| crt.sh | https://crt.sh | Domain |
| CVE | https://cve.org | CVE |
| DNS Coffee | https://dns.coffee | Domain |
| DNSlytics | https://dnslytics.com | IP, domain |
| DomainTools | https://www.domaintools.com | IP, domain |
| EmailRep | https://emailrep.io | Email |
| FileScan.IO | https://filescan.io | Hash |
| FortiGuard | https://fortiguard.com | IP, URL, CVE |
| Google Safe Browsing | https://transparencyreport.google.com | Domain, URL |
| GreyNoise | https://viz.greynoise.io | IP, domain, ASN, CVE |
| Host.io | https://host.io | Domain |
| Hurricane Electric | https://bgp.he.net/ | IP, domain, ASN |
| HybridAnalysis | https://www.hybrid-analysis.com | IP, domain, hash |
| Intezer | https://analyze.intezer.com | Hash |
| IPinfo | https://ipinfo.io | IP, ASN |
| IPIP | https://en.ipip.net | IP, ASN |
| Joe Sandbox | https://www.joesandbox.com | Hash |
| Maltiverse | https://www.maltiverse.com | Domain, hash |
| MalwareBazaar | https://bazaar.abuse.ch | Hash |
| NVD | https://nvd.nist.gov | CVE |
| OOCPR | https://data.occrp.org | Email |
| ONYPHE | https://www.onyphe.io | IP |
| OpenTIP | https://opentip.kaspersky.com | Hash |
| OTX | https://otx.alienvault.com | IP, domain, CVE, URL, hash |
| Pulsedive | https://pulsedive.com | IP, domain, URL, hash |
| Radar | https://radar.cloudflare.com | IP, domain |
| Robtex | https://www.robtex.com | IP, domain |
| Scumware | https://www.scumware.org | IP, domain, hash (MD5) |
| SecurityTrails | https://securitytrails.com | IP, domain |
| Shodan | https://www.shodan.io | IP, domain, ASN |
| Sploitus | https://sploitus.com | CVE |
| Talos | https://talosintelligence.com | IP, domain |
| ThreatBook | https://threatbook.io | IP, domain |
| ThreatConnect | https://app.threatconnect.com | IP, domain, email |
| ThreatMiner | https://www.threatminer.org | IP, domain, hash |
| TIP | https://threatintelligenceplatform.com | IP, domain |
| Triage | https://tria.ge | Hash, URL |
| URLhaus | https://urlhaus.abuse.ch | IP, domain |
| urlscan.io | https://urlscan.io | IP, domain, ASN, URL |
| URLVoid | https://www.urlvoid.com | Domain |
| ViewDNS | https://viewdns.info | IP, domain, email |
| VirusTotal | https://www.virustotal.com | IP, domain, URL, hash |
| VMRay | https://www.vmray.com | Hash |
| Vulmon | https://vulmon.com | CVE |
| WebCheck | https://web-check.xyz | Domain |
| X-Force Exchange | https://exchange.xforce.ibmcloud.com | IP, domain, hash |
| ZoomEye | https://www.zoomeye.ai | IP |
### 支持的扫描引擎
| 名称 | url | 支持的类型 |
| :------------- | :------------------------------ | :-------------- |
| Browserling | https://www.browserling.com | URL |
| HybridAnalysis | https://www.hybrid-analysis.com | URL |
| urlscan.io | https://urlscan.io | IP, domain, URL |
| VirusTotal | https://www.virustotal.com | URL |
## 如何使用
- [使用 Mitaka 在浏览器中进行 OSINT 以识别恶意软件、可疑网站、可疑邮件等](https://null-byte.wonderhowto.com/how-to/use-mitaka-perform-browser-osint-identify-malware-sketchy-sites-shady-emails-more-0216352/)
**注意:** 请在选项中设置您的 API 密钥,以启用 HybridAnalysis、urlscan.io 和 VirusTotal 扫描。
## 选项
您可以根据自己的偏好,在选项页面启用或禁用搜索引擎。

## 权限
### Firefox
请允许“访问所有网站的数据”权限。否则此扩展将无法工作。
 ## 隐私政策
- [扩展的隐私政策](https://ninoseki.github.io/chrome-webstore/privacy-policy/)
## 常见问题
- 问:没有显示上下文菜单(右键菜单)。
- 答:有时上下文菜单需要一段时间才会出现。或者在刷新上下文菜单时出现了问题。这种小故障可以通过稍等片刻来解决。请在选择后深呼吸一下,然后点击右键。
## 替代品或类似工具
- [CrowdScrape](https://chrome.google.com/webstore/detail/crowdscrape/jjplaeklnlddpkbbdbnogmppffokemej)
- [Gotanda](https://github.com/HASH1da1/Gotanda)
- [SOC Multi-tool](https://github.com/zdhenard42/SOC-Multitool)
- [Sputnik](https://github.com/mitchmoser/sputnik)
- [ThreatConnect Integrated Chrome Extension](https://chrome.google.com/webstore/detail/threatconnect-integrated/lblgcphpihpadjdpjgjnnoikjdjcnkbh)
- [ThreatPinch Lookup](https://github.com/cloudtracer/ThreatPinchLookup)
- [VTchromizer](https://chrome.google.com/webstore/detail/vtchromizer/efbjojhplkelaegfbieplglfidafgoka)
## 工作原理
```
flowchart LR
CS[Content Script] --> |1 - Send Selection| BSW[Background Service Worker]
BSW --> |2 - Create Context Menus| CS
CS --> |3 - Click Context Menu| BSW
BSW --> |4 - Search/Scan| T[New Tab]
```
## 贡献
阅读[贡献指南](contributing.md)并加入[贡献者](https://github.com/ninoseki/mitaka/graphs/contributors)的行列。
## 隐私政策
- [扩展的隐私政策](https://ninoseki.github.io/chrome-webstore/privacy-policy/)
## 常见问题
- 问:没有显示上下文菜单(右键菜单)。
- 答:有时上下文菜单需要一段时间才会出现。或者在刷新上下文菜单时出现了问题。这种小故障可以通过稍等片刻来解决。请在选择后深呼吸一下,然后点击右键。
## 替代品或类似工具
- [CrowdScrape](https://chrome.google.com/webstore/detail/crowdscrape/jjplaeklnlddpkbbdbnogmppffokemej)
- [Gotanda](https://github.com/HASH1da1/Gotanda)
- [SOC Multi-tool](https://github.com/zdhenard42/SOC-Multitool)
- [Sputnik](https://github.com/mitchmoser/sputnik)
- [ThreatConnect Integrated Chrome Extension](https://chrome.google.com/webstore/detail/threatconnect-integrated/lblgcphpihpadjdpjgjnnoikjdjcnkbh)
- [ThreatPinch Lookup](https://github.com/cloudtracer/ThreatPinchLookup)
- [VTchromizer](https://chrome.google.com/webstore/detail/vtchromizer/efbjojhplkelaegfbieplglfidafgoka)
## 工作原理
```
flowchart LR
CS[Content Script] --> |1 - Send Selection| BSW[Background Service Worker]
BSW --> |2 - Create Context Menus| CS
CS --> |3 - Click Context Menu| BSW
BSW --> |4 - Search/Scan| T[New Tab]
```
## 贡献
阅读[贡献指南](contributing.md)并加入[贡献者](https://github.com/ninoseki/mitaka/graphs/contributors)的行列。
标签:CTF工具, CVE漏洞, ESC4, Firefox插件, IoC提取, IP查询, OSINT, Refanging, Sigma 规则, 哈希检测, 域名分析, 威胁情报, 开发者工具, 情报搜集, 插件, 数据可视化, 文本识别, 浏览器扩展, 漏洞搜索, 网络安全, 网络调试, 自动化, 自动化攻击, 自动化攻击, 自动识别, 隐私保护