jeet-ganguly/birdy-edwards
GitHub: jeet-ganguly/birdy-edwards
一个基于本地大模型的 Facebook SOCMINT 工具,解决数据隐私与离线分析需求。
Stars: 2 | Forks: 0

# BIRDY-EDWARDS
### *Infiltrate & Expose*
[](https://python.org)
[](https://flask.palletsprojects.com)
[](https://ollama.com)
[](https://docker.com)
[]()
[]()
**AI-powered Facebook SOCMINT platform — 100% local, zero cloud dependency.**
[Installation](#installation) · [Troubleshooting](#troubleshooting) · [Disclaimer](#️-disclaimer) . [Contributing](#contributing)
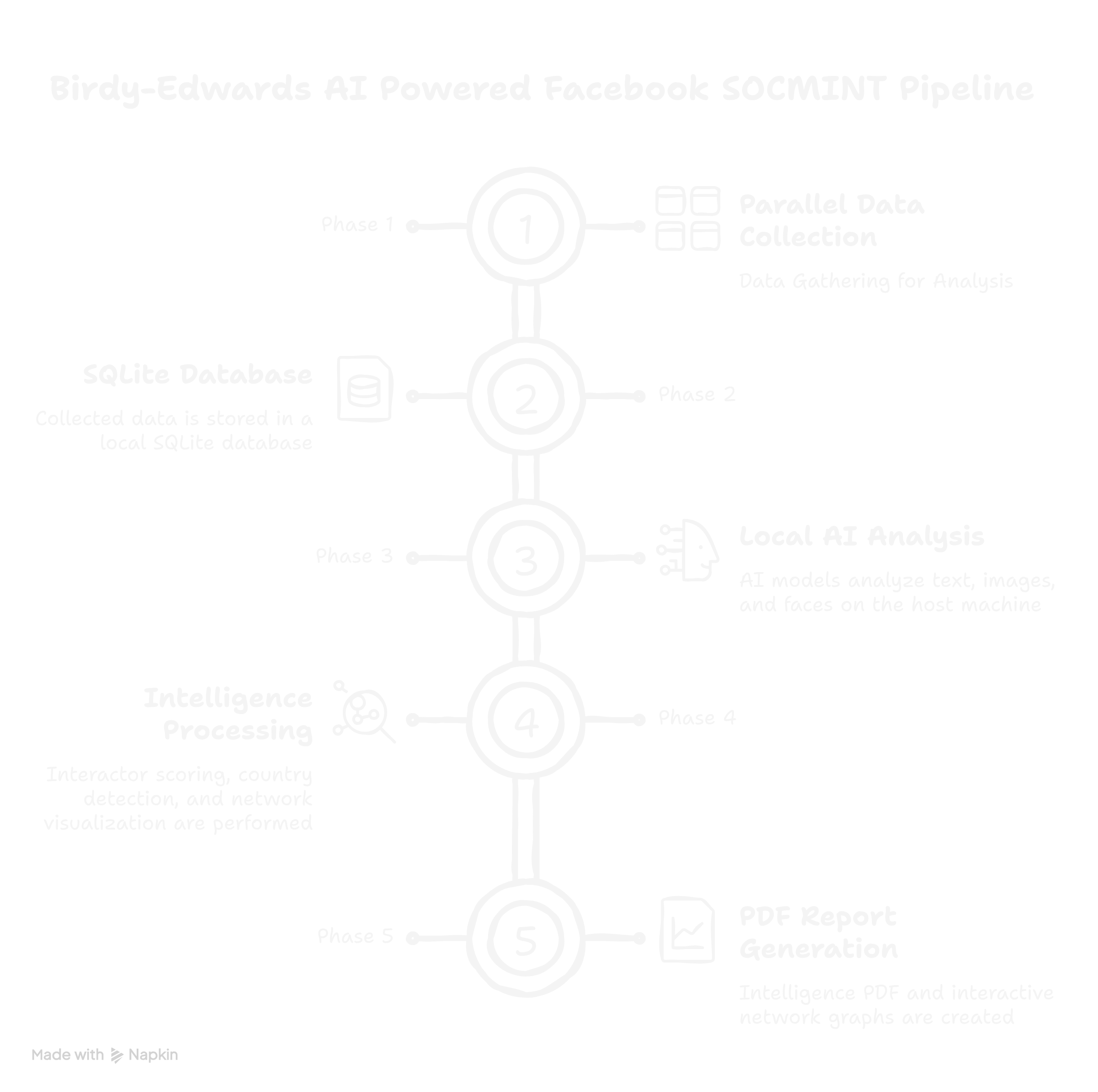
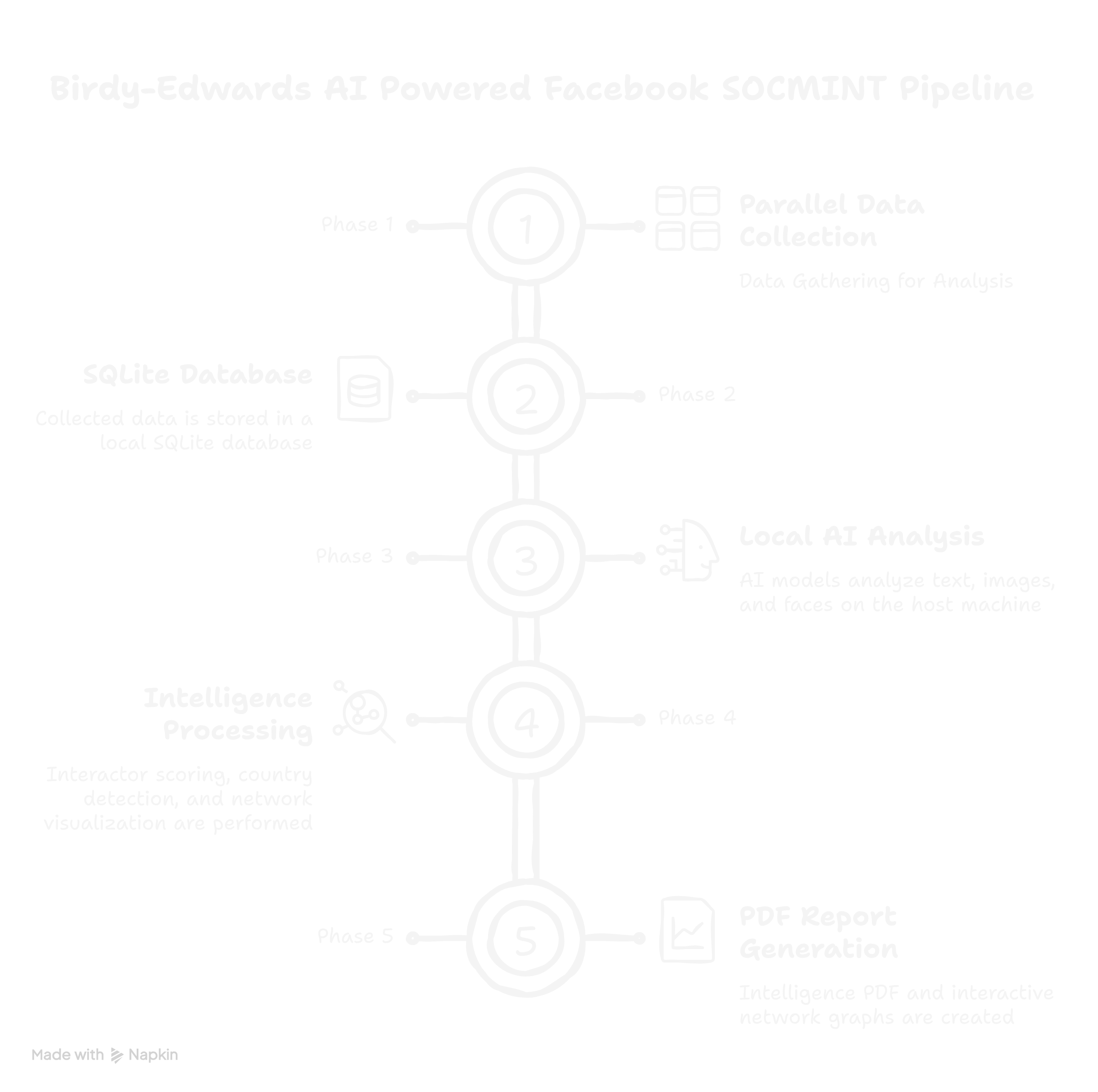
## 架构
## 功能
- 🔍 **Profile collection** — Automated data gathering of posts, photos, reels, and about data
- 🧠 **Interaction intelligence** — AI sentiment, stance, emotion, and language analysis per interaction
- 📊 **Actor scoring** — Weighted composite score with 5-tier classification system
- 🌍 **Country detection** — LLM identifies country of origin from profile signals
- 👤 **Face intelligence** — Face detection, 128D encoding, and identity clustering across all images. It uses HOG model.
- 🕸️ **Network graphs** — Interactive HTML graphs including force-directed and co-interactors relationship matrix
- 📄 **PDF reports** — Professional intelligence report with limited ammount of charts
- 🤖 **Local AI** — Ollama powered, gemma3:4b/12b/27b and other models(mention in web panel), runs on GPU or CPU
- 🐳 **Docker ready** — One command deployment on Linux and Windows
## 文档
Full usage guides for both investigation modes are available on the project website:
- [Click Here](https://jeet-ganguly.github.io/profile/edwards.html)
[](https://jeet-ganguly.github.io/profile/edwards.html)
## ⚠️ 免责声明
## 系统要求
| Component | Minimum | Recommended |
|---|---|---|
| OS | Ubuntu 24.04 LTS / Windows 10+ | Ubuntu 24.04 LTS |
| RAM | 8 GB | 16 GB |
| Storage | 20 GB free | 40 GB free |
| Docker | Docker Desktop / Engine | Latest stable |
| Ollama | Latest | Latest |
## 安装
### 先决条件
**Step 1 — Install Docker**
- **Linux:** https://docs.docker.com/engine/install/ubuntu/
- **Windows:** https://docs.docker.com/desktop/install/windows-install/
**Step 2 — Install Ollama**
- **Linux:**
```
curl -fsSL https://ollama.com/install.sh | sh
```
- **Windows:** Download installer from https://ollama.com/download
**Step 3 — Start Ollama bound to all interfaces**
- **Linux:**
```
OLLAMA_HOST=0.0.0.0:11434 ollama serve
```
To make this permanent:
```
sudo systemctl edit ollama
```
Add:
```
[Service]
Environment="OLLAMA_HOST=0.0.0.0:11434"
```
```
sudo systemctl daemon-reload && sudo systemctl restart ollama
```
- **Windows:** Ollama listens on all interfaces by default — no extra configuration needed. If no then,
```
$env:OLLAMA_HOST="0.0.0.0"
ollama serve
```
### 快速开始
**Step 1 — Clone the repository**
```
git clone https://github.com/jeet-ganguly/birdy-edwards.git
cd birdy-edwards
```
**Step 2 — Create required files and directories**
- **Linux:**
```
mkdir -p app/reports app/face_data app/post_screenshots app/status
touch app/fb_cookies.pkl app/socmint.db app/socmint_manual.db app/.ollama_model
```
- **Windows (PowerShell):**
```
New-Item -ItemType Directory app/reports, app/face_data, app/post_screenshots, app/status
New-Item -ItemType File app/fb_cookies.pkl, app/socmint.db, app/socmint_manual.db, app/.ollama_model
```
**Step 3 — Build the Docker image**
```
docker compose build
```
**Step 4 — Start the container**
```
docker compose up -d
docker compose logs -f
```
**Step 5 — Open the web UI**
```
http://localhost:5000
```
### 拉取 AI 模型
Pull a model on your host machine:
```
ollama pull gemma3:4b
```
Or use the **AI Model panel** in the web UI — select a model and click **Apply & Pull**.
| RAM | Recommended Model |
|---|---|
| 8 GB | gemma3:4b |
| 16 GB | gemma3:12b |
| 32 GB | gemma3:27b |
### 导入会话 Cookie
BIRDY-EDWARDS requires a valid Facebook session. Use the **Cookie-Editor** browser extension — works on all platforms, no Selenium required.
1. Install Cookie-Editor → [Chrome](https://chrome.google.com/webstore/detail/cookie-editor/hlkenndednhfkekhgcdicdfddnkalmdm) · [Firefox](https://addons.mozilla.org/en-US/firefox/addon/cookie-editor/)
2. Log into your **dedicated investigation account** on Facebook
3. Click Cookie-Editor while on facebook.com
4. Click **Export → Export as JSON**
5. Go to `http://localhost:5000/tools/import-cookies` and paste
## 故障排除
**Ollama not reachable from Docker**
```
docker exec -it birdy-edwards curl http://host.docker.internal:11434/api/tags
```
If it fails, restart Ollama with `OLLAMA_HOST=0.0.0.0:11434 ollama serve`
**DB error: no such table or other DB related error**
Start a new investigation — schema is created automatically on first use. If you stop process/program during analysis delete that investigation and then start new investigation.
**Cookies expired**
Go to `http://localhost:5000/tools/import-cookies` and re-import fresh cookies.
**Port 5000 already in use**
Change in `docker-compose.yml`: `"5001:5000"` then access at `http://localhost:5001`
**Out of memory during build**
Increase Docker Desktop memory to 8 GB+ via Settings → Resources → Memory
- Features that bypass platform security controls
- Changes that introduce cloud dependencies
- Code that stores or transmits investigation data externally
## 致谢
- Inspired by [Sherlock](https://github.com/sherlock-project/sherlock)
- Inspired by the OSINT and threat intelligence research community
- [SeleniumBase](https://github.com/seleniumbase/SeleniumBase) — Undetected Chrome automation
- [Ollama](https://ollama.com) — Local LLM inference engine
- [face_recognition](https://github.com/ageitgey/face_recognition) — Face detection and encoding library
- [pyvis](https://github.com/WestHealth/pyvis) — Interactive network graph visualization
- [reportlab](https://www.reportlab.com) — PDF generation
- [pytesseract](https://github.com/madmaze/pytesseract) — OCR engine wrapper
**BIRDY-EDWARDS** · Infiltrate & Expose ·
标签:AI风险缓解, Docker, Flask, HOG特征, LLM评估, Ollama, PDF生成, Python, SEO: Facebook情报, SEO: 本地LLM, SEO: 社交图谱分析, SEO: 自动化情报, SOCMINT, Webhook, 个人数据收集, 五级分类, 交互智能, 人脸检测, 人脸编码, 关系矩阵, 力导向图, 加权评分, 可扩展分析, 国家检测, 威胁报告, 安全防御评估, 情感分析, 情绪分析, 无后门, 本地AI推理, 照片收集, 目标画像, 社交媒体情报, 社交网络分析, 立场分析, 线下情报, 网络图谱, 自动化情报收集, 行为画像, 视频收集, 语言分析, 请求拦截, 逆向工具, 零云依赖
 # BIRDY-EDWARDS
### *Infiltrate & Expose*
[](https://python.org)
[](https://flask.palletsprojects.com)
[](https://ollama.com)
[](https://docker.com)
[]()
[]()
**AI-powered Facebook SOCMINT platform — 100% local, zero cloud dependency.**
[Installation](#installation) · [Troubleshooting](#troubleshooting) · [Disclaimer](#️-disclaimer) . [Contributing](#contributing)
# BIRDY-EDWARDS
### *Infiltrate & Expose*
[](https://python.org)
[](https://flask.palletsprojects.com)
[](https://ollama.com)
[](https://docker.com)
[]()
[]()
**AI-powered Facebook SOCMINT platform — 100% local, zero cloud dependency.**
[Installation](#installation) · [Troubleshooting](#troubleshooting) · [Disclaimer](#️-disclaimer) . [Contributing](#contributing)