alialsartawi7-sketch/ghosttrace
GitHub: alialsartawi7-sketch/ghosttrace
一款本地运行的模块化 OSINT 与攻击面分析平台,聚合多款安全工具并提供风险评分与报告生成。
Stars: 4 | Forks: 0


-orange?logo=linux&logoColor=white)





```
██████╗ ██╗ ██╗ ██████╗ ███████╗████████╗████████╗██████╗ █████╗ ██████╗███████╗
██╔════╝ ██║ ██║██╔═══██╗██╔════╝╚══██╔══╝╚══██╔══╝██╔══██╗██╔══██╗██╔════╝██╔════╝
██║ ███╗███████║██║ ██║███████╗ ██║ ██║ ██████╔╝███████║██║ █████╗
██║ ██║██╔══██║██║ ██║╚════██║ ██║ ██║ ██╔══██╗██╔══██║██║ ██╔══╝
╚██████╔╝██║ ██║╚██████╔╝███████║ ██║ ██║ ██║ ██║██║ ██║╚██████╗███████╗
╚═════╝ ╚═╝ ╚═╝ ╚═════╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ╚═════╝╚══════╝
v5.0 by Alsartawi
```
**OSINT made simple — from beginner to professional.**
GhostTrace is a modular OSINT intelligence platform that wraps 9 Linux tools into a single web interface with real-time streaming, active reconnaissance, risk scoring, attack path analysis, and professional PDF reports. No cloud dependencies. No telemetry. Runs entirely on your machine.
"⭐ If you find this useful, a star helps a lot!"
"🐛 Found a bug? Open an issue — I actively fix them."
## ⚡ 什么使 GhostTrace 不同
- 🔍 **9 integrated tools** — not just wrappers, full intelligence pipeline
- 🛡️ **Active Recon** — DNS validation, HTTP probing, port scanning, attack surface detection
- 📊 **Risk Scoring Engine** — 0-100 dynamic scoring with actionable reasons
- 🗺️ **Attack Path Generator** — 5 rules that map real exploitation paths
- 🧠 **Smart Confidence** — scores based on result quality, not just source
- 📄 **Professional Reports** — PDF with all 9 result types, risk assessment, confidence bars
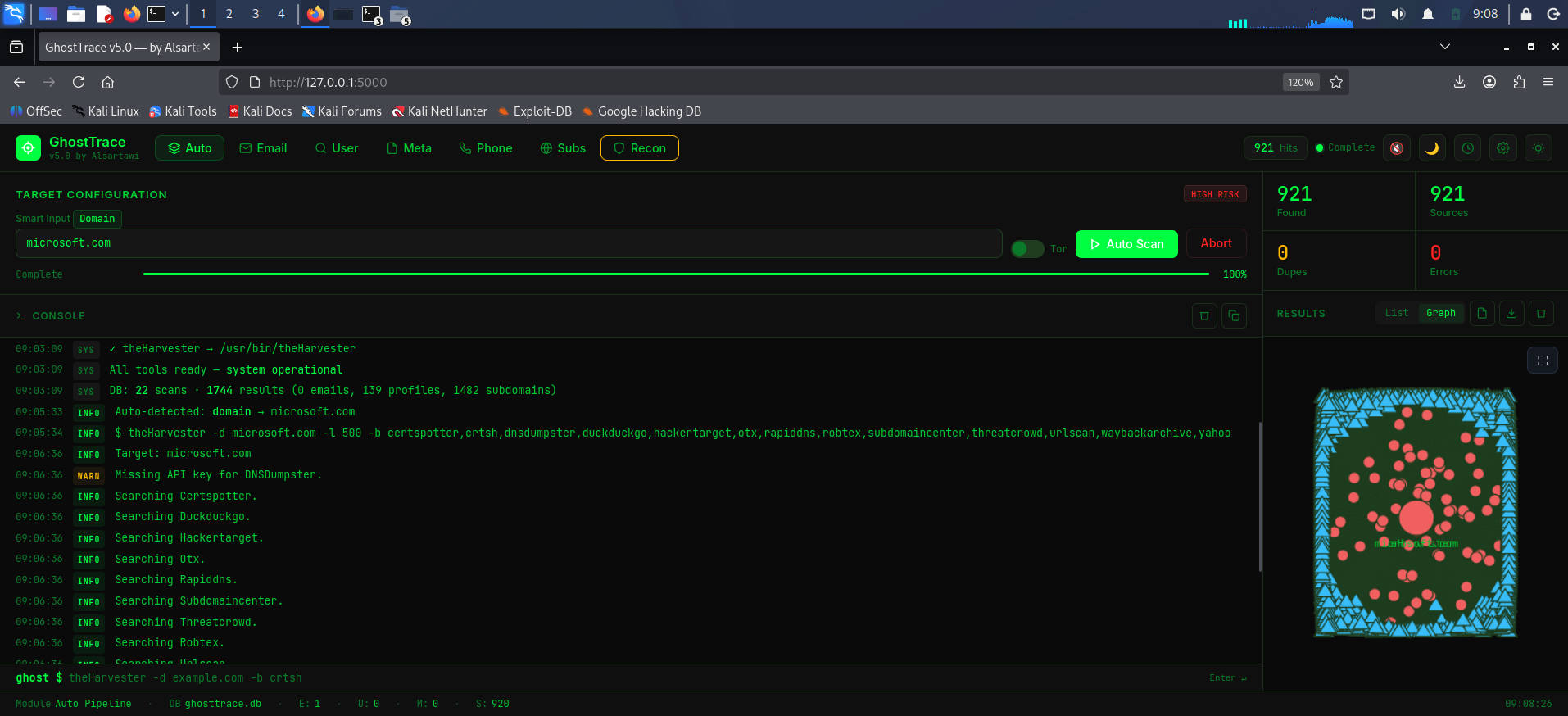
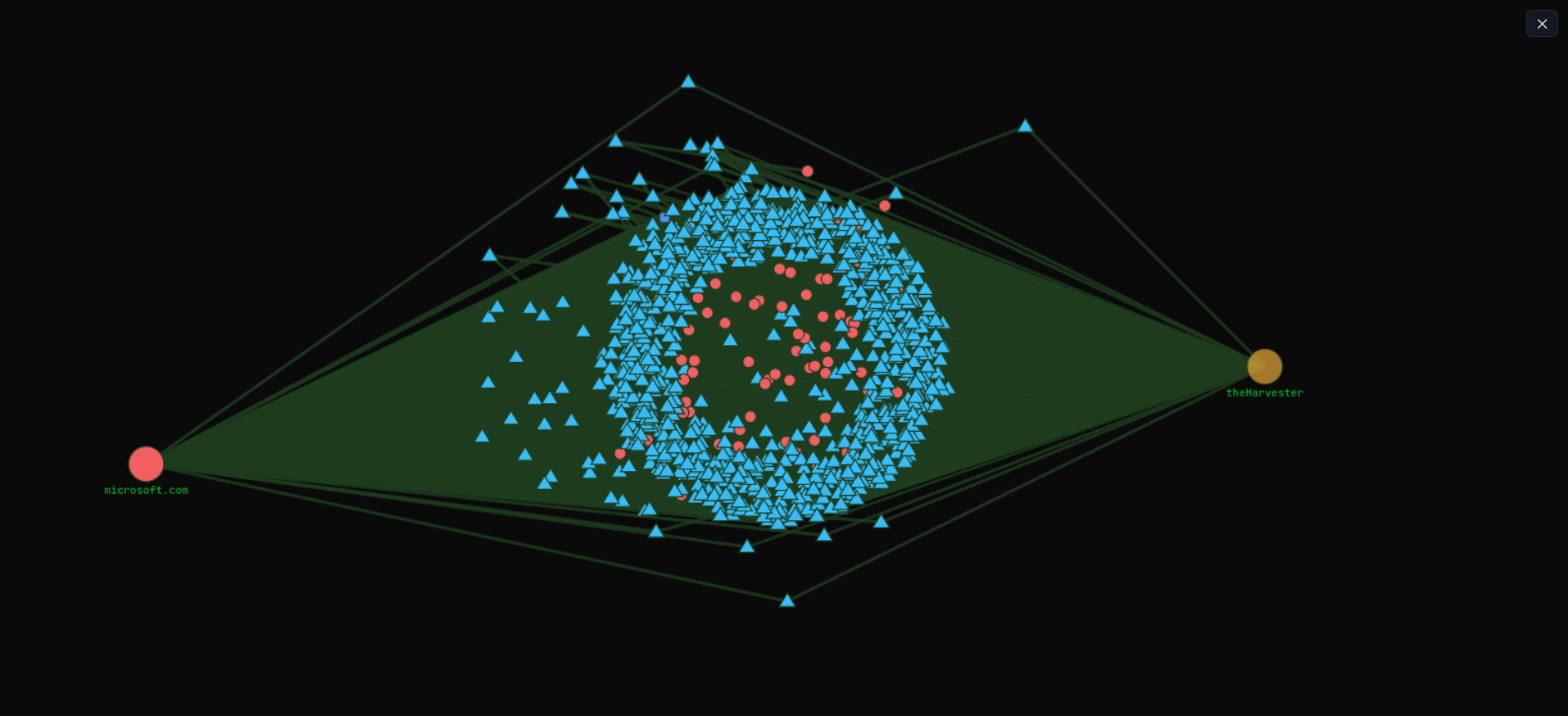
- 🌐 **Interactive Graph** — clustered force layout with shapes, legend, PNG export
- 🔐 **Authentication** — bcrypt password protection with session management
- 🎨 **12 Premium Themes** — including Royal Gold and Midnight Silver
- 🔄 **Cross-Scan Diff** — compare two scans to detect new exposures
- 📝 **Scan Notes & History** — SQLite-backed with load, notes, delete
## 🧰 集成工具 (9)
| # | Tool | Tab | What It Finds |
|---|------|-----|---------------|
| 1 | **theHarvester** | Email / Subs | Emails, subdomains, IPs from 13 free sources |
| 2 | **Maigret** | Username | Social media profiles across 2500+ sites |
| 3 | **Sherlock** | Username | Username search across 400+ sites |
| 4 | **ExifTool** | Metadata | Hidden metadata in files (author, GPS, software) |
| 5 | **PhoneInfoga** | Phone | Phone number carrier, country, format info |
| 6 | **Whois** | Auto/CLI | Domain registration, registrar, expiry, nameservers |
| 7 | **dig** | DNS | MX, TXT (SPF/DKIM/DMARC), NS, SOA, A records |
| 8 | **openssl** | SSL | Certificate SANs (hidden subdomains), issuer, expiry |
| 9 | **Google Dorks** | Dorks | 28 targeted queries for sensitive files, admin panels, leaks |
## 🎛️ 10 个扫描模块
| Module | Input | Tool Used | Example |
|--------|-------|-----------|---------|
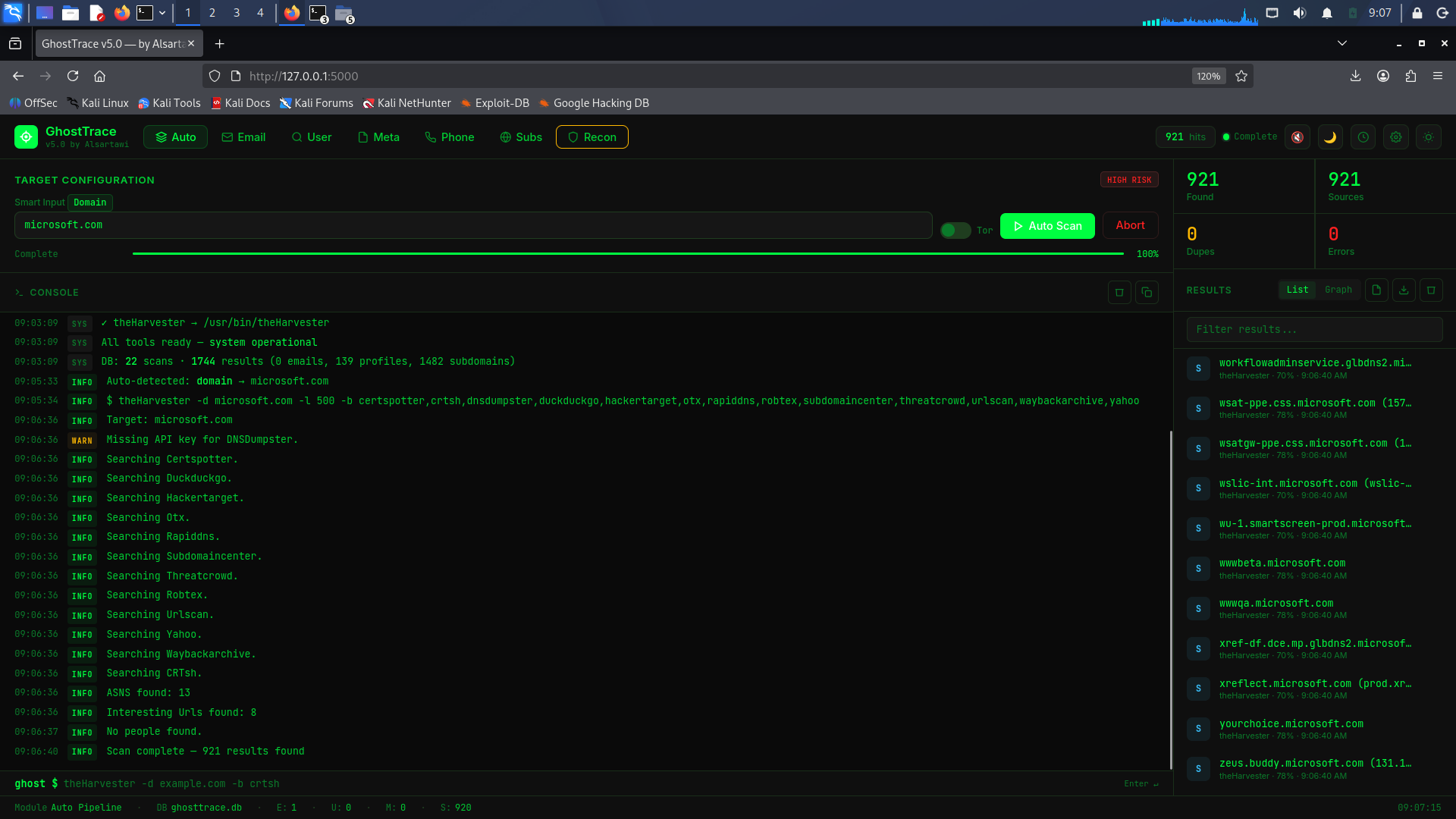
| **Auto** | Anything | Auto-detects type | `microsoft.com` → theHarvester |
| **Email** | Domain | theHarvester | `example.com` |
| **Username** | Username | Maigret / Sherlock | `johndoe` |
| **Metadata** | File path | ExifTool | `/home/kali/photo.jpg` |
| **Phone** | Phone number | PhoneInfoga | `+1234567890` |
| **Subdomain** | Domain | theHarvester | `google.com` |
| **DNS** | Domain | dig | `example.com` → MX, TXT, NS, SOA |
| **SSL** | Domain | openssl | `example.com` → SANs, issuer, expiry |
| **Dorks** | Domain | Generator | `example.com` → 28 Google dork queries |
| **Recon** | Domain | Built-in | DNS resolve → HTTP probe → Ports → Risk |
## 🛡️ 主动侦察管道
After passive OSINT, GhostTrace validates and enriches results:
```
📡 DNS Resolution → Remove dead domains, validate alive hosts
🌐 HTTP Probing → Status codes, technology detection, security headers
🔌 Port Scanning → Top 25 common ports (SSH, RDP, MySQL, Redis...)
🎯 Attack Surface → Admin panels, login pages, API endpoints
📊 Risk Scoring → 0-100 dynamic score with explanations
🗺️ Attack Paths → 5 rules: Brute Force, Admin Panel, API, Legacy, Chained
```
### 风险评分
Every host gets a dynamic risk score based on:
| Factor | Points | Example |
|--------|--------|---------|
| Alive host | +10 | Base score for reachable targets |
| RDP exposed | +25 | Port 3389 open |
| Admin panel found | +20 | `/admin` returns 200/401/403 |
| Missing HSTS | +10 | No Strict-Transport-Security header |
| Staging/dev exposed | +18 | `staging.example.com` publicly accessible |
| WordPress detected | +10 | Known vulnerability history |
### 攻击路径规则
| Rule | Trigger | Severity |
|------|---------|----------|
| Brute Force Candidate | Login page + SSH/FTP/RDP open | HIGH |
| Admin Panel Exposed | Any admin panel found | CRITICAL (score≥65) |
| API Enumeration | API endpoint detected | HIGH |
| Legacy Service | FTP (21) or Telnet (23) open | CRITICAL |
| Chained Risk | Score≥65 + 3 contributing factors | CRITICAL |
## 🧠 智能置信度系统
Unlike tools that give static confidence, GhostTrace scores each result individually:
| Result | Old Score | Smart Score | Why |
|--------|-----------|-------------|-----|
| `Personal email pattern (firstname.lastname)` | 72% | **90%** | Personal email (firstname.lastname) |
| `Generic service alias` | 72% | **60%** | Generic alias |
| `Vulnerable admin subdomain detected` | 70% | **90%** | Admin subdomain + DNS resolved |
| `No IP confirmation on staging environmentg` | 70% | **60%** | No IP confirmation |
| `Loopback address - Filtered noise` | 70% | **15%** | Private IP — noise |
| `Broad wildcard entry` | 70% | **20%** | Wildcard entry |
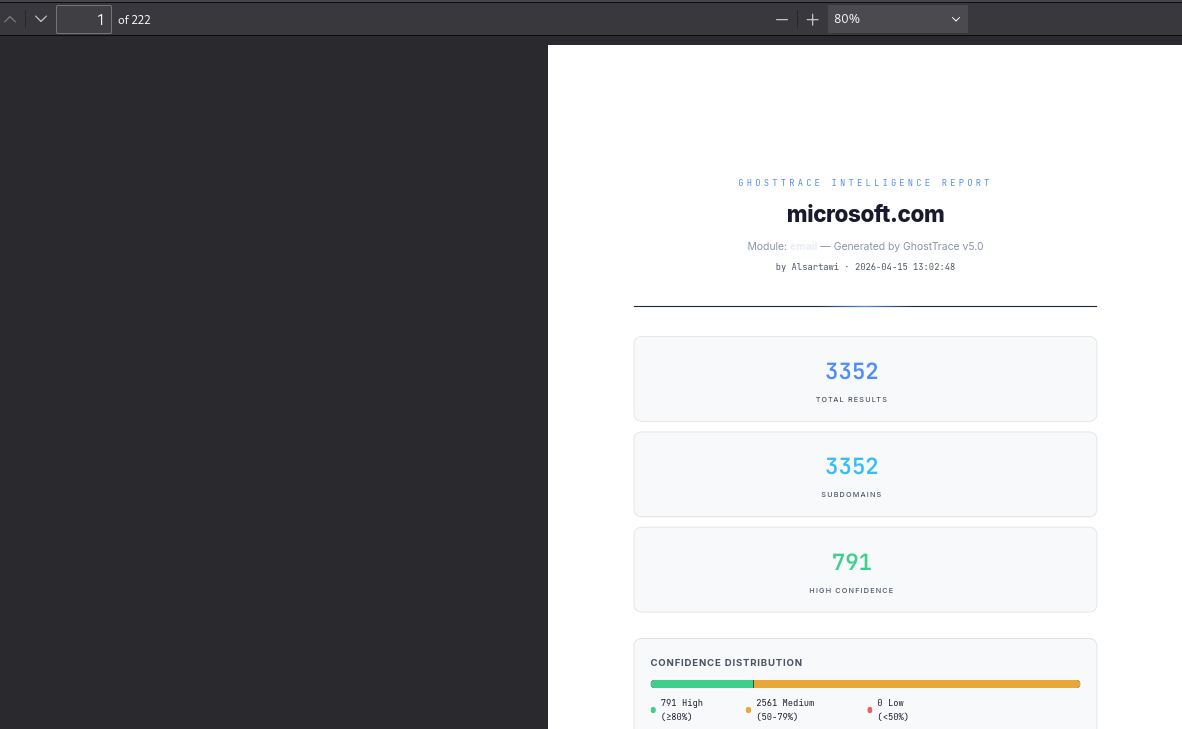
## 📄 专业 PDF 报告
Reports include **all 9 result types** with:
- 📊 Stat cards (dynamic — only show categories with results)
- 📈 Confidence distribution bar (high/medium/low)
- 📝 Executive summary (auto-generated)
- 🛡️ Risk Assessment section (if recon was performed)
- 🗺️ Attack paths with severity and steps
- ⚠️ Recommendations
## ✨ 附加功能
| Feature | Description |
|---------|-------------|
| 🔐 **Authentication** | bcrypt password with `--setup`, session-based |
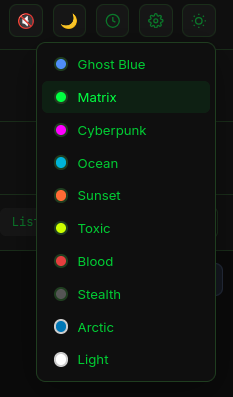
| 🎨 **12 Premium Themes** | Ghost Blue, Matrix, Cyberpunk, Ocean, Sunset, Toxic, Blood, Stealth, Arctic, Light, **Royal Gold**, **Midnight Silver** |
| 🌙 **Dark/Light Toggle** | Quick toggle button in navbar |
| 📋 **Copy Button** | Hover any result → click ⎘ to copy |
| 📝 **Scan Notes** Add notes to any scan from History |
| 🗑️ **Delete Scans** | Remove old scans from History with one click |
| 🔄 **Cross-Scan Diff** | Compare two scans: added/removed/unchanged |
| 🌐 **Interactive Graph** | Clustered force layout, shapes per type, legend, click highlight, PNG export |
| ⛶ **Fullscreen Graph** | Dedicated fullscreen mode with proper resizing |
| 🔎 **Result Search** | Filter results in real-time |
| 💾 **Scan History** | SQLite-backed — load, search, delete past scans |
| 🔌 **Tor Integration** | One toggle — routes traffic through Tor |
| 📦 **Export** | JSON, CSV, TXT, HTML, PDF |
| 🖥️ **CLI Mode** | Direct commands in the terminal bar |
## 🧪 质量保证
GhostTrace is continuously tested and verified:
| Category | Details |
|----------|---------|
| ✅ **6 Test Files** | validators, harvester, correlator, risk_engine, recon, new_tools |
| ✅ **CI/CD Pipeline** | GitHub Actions auto-runs tests on every push (Python 3.10, 3.11, 3.12) |
| ✅ **Linting** | flake8 checks for syntax errors and undefined names |
| ✅ **API Documentation** | Full reference at [`docs/API.md`](docs/API.md) — all 29 endpoints, schemas, cURL examples |
Run tests locally:
```
pytest tests/ -v
```
## 架构
```
GhostTrace v5.0
┌──────────┐ ┌────────────┐ ┌──────────────┐ ┌──────────┐
│ Web UI │───→│ Validators │───→│ Tool Adapters │───→│ Execution│
│ 10 tabs │ │ whitelist │ │ 9 tools │ │ Engine │
└──────────┘ └────────────┘ └──────────────┘ └────┬─────┘
↑ │
│ SSE ┌────────────┐ ┌──────────────┐ subprocess
│←─────────│ Scanner │←───│ Parser │←───────┘
│ └─────┬──────┘ └──────────────┘
│ │
│ ┌─────↓──────┐ ┌──────────────┐
│ │ Correlator │───→│ SQLite DB │
│ │ + Scorer │ │ WAL mode │
│ └─────┬──────┘ └──────────────┘
│ │
│ ┌─────↓──────┐ ┌──────────────┐
│ │ Active Recon│───→│ Risk Engine │
│ │ DNS+HTTP+ │ │ Score 0-100 │
│ │ Ports+Attack│ │ Attack Paths │
│ └────────────┘ └──────────────┘
```
**Project Structure (35+ files):**
```
ghosttrace/
├── .github/
│ └── workflows/
│ └── test.yml # CI/CD — auto tests on every push
├── docs/
│ └── API.md # Full REST API documentation
├── app.py # Flask entry + authentication
├── config.py # Centralized config
├── core/
│ ├── engine.py # Sandboxed subprocess execution
│ ├── scanner.py # Scan orchestrator + CLI + abort
│ └── differ.py # Cross-scan diff comparison
├── tools/
│ ├── base.py # ToolAdapter abstract interface
│ ├── harvester.py # theHarvester (smart confidence, API keys)
│ ├── sherlock_tool.py # Sherlock adapter
│ ├── maigret_tool.py # Maigret (false positive filter, Tor)
│ ├── exiftool.py # ExifTool adapter
│ ├── phoneinfoga_tool.py # PhoneInfoga adapter
│ ├── whois_tool.py # Whois lookup adapter
│ ├── dns_records.py # DNS records via dig
│ ├── ssl_cert.py # SSL certificate SANs extraction
│ ├── google_dorks.py # Google dork generator (28 queries)
│ └── registry.py # Plugin registry (9 tools)
├── api/
│ ├── routes.py # 4 Blueprints, 29 endpoints
│ └── recon_routes.py # Active recon pipeline
├── database/
│ └── manager.py # SQLite WAL + migrations + notes
├── intelligence/
│ └── correlator.py # Entity linking + smart scoring
├── recon/
│ ├── __init__.py # DNS, HTTP, Port, AttackSurface, DataQuality
│ └── risk_engine.py # RiskScorer + AttackPathGenerator
├── reports/
│ └── html_report.py # Professional reports (9 types + risk)
├── utils/
│ ├── validators.py # Whitelist per-tool regex validation
│ ├── security.py # Rate limiter + output sanitizer
│ └── logger.py # Rotating file logger
├── templates/
│ └── index.html # Single-page dashboard (12 themes)
├── tests/ # 6 test files
│ ├── test_validators.py
│ ├── test_harvester.py
│ ├── test_correlator.py
│ ├── test_risk_engine.py
│ ├── test_recon.py # NEW — DNSResolver, DataQuality, AttackSurface
│ └── test_new_tools.py # NEW — DNS, SSL, Dorks, Whois, Phone, Differ
├── build.sh
├── requirements.txt
└── LICENSE
```
## 安装
**Target:** Kali Linux 2025+ / Ubuntu 22.04+
### 1. 克隆并安装 Python 依赖
```
git clone https://github.com/alialsartawi7-sketch/ghosttrace.git
cd ghosttrace
pip install -r requirements.txt --break-system-packages
```
### 2. 安装 OSINT 工具
```
# 必需
sudo apt update
sudo apt install -y pkg-config libcairo2-dev python3-dev build-essential
sudo apt install theharvester exiftool -y
pip install sherlock-project maigret --break-system-packages
# PhoneInfoga
wget https://github.com/sundowndev/phoneinfoga/releases/latest/download/phoneinfoga_Linux_x86_64.tar.gz -O /tmp/phoneinfoga.tar.gz
tar xzf /tmp/phoneinfoga.tar.gz -C /tmp/
sudo mv /tmp/phoneinfoga /usr/local/bin/
# 可选 — 用于 PDF 报告
pip install weasyprint --break-system-packages
# 可选 — 用于 Tor 路由
sudo apt install tor -y
sudo service tor start
```
### 3. 验证工具
```
theHarvester -h
sherlock --version
maigret --version
exiftool -ver
phoneinfoga version
dig -v
openssl version
```
### 4. 设置密码(推荐)
```
python3 app.py --setup
```
## 用法
```
python3 app.py
# 打开 http://127.0.0.1:5000
```
### Tor
| Tool | Tor Method |
|------|-----------|
| Maigret | `--tor-proxy socks5://127.0.0.1:9050` |
| Sherlock | `--tor` |
| theHarvester | `proxychains4 -q` wrapper |
| ExifTool | N/A (local file processing) |
### CLI 模式
```
ghost $ maigret johndoe --site Instagram --site GitHub
ghost $ theHarvester -d example.com -b crtsh -l 100
ghost $ whois example.com
ghost $ dig example.com MX
```
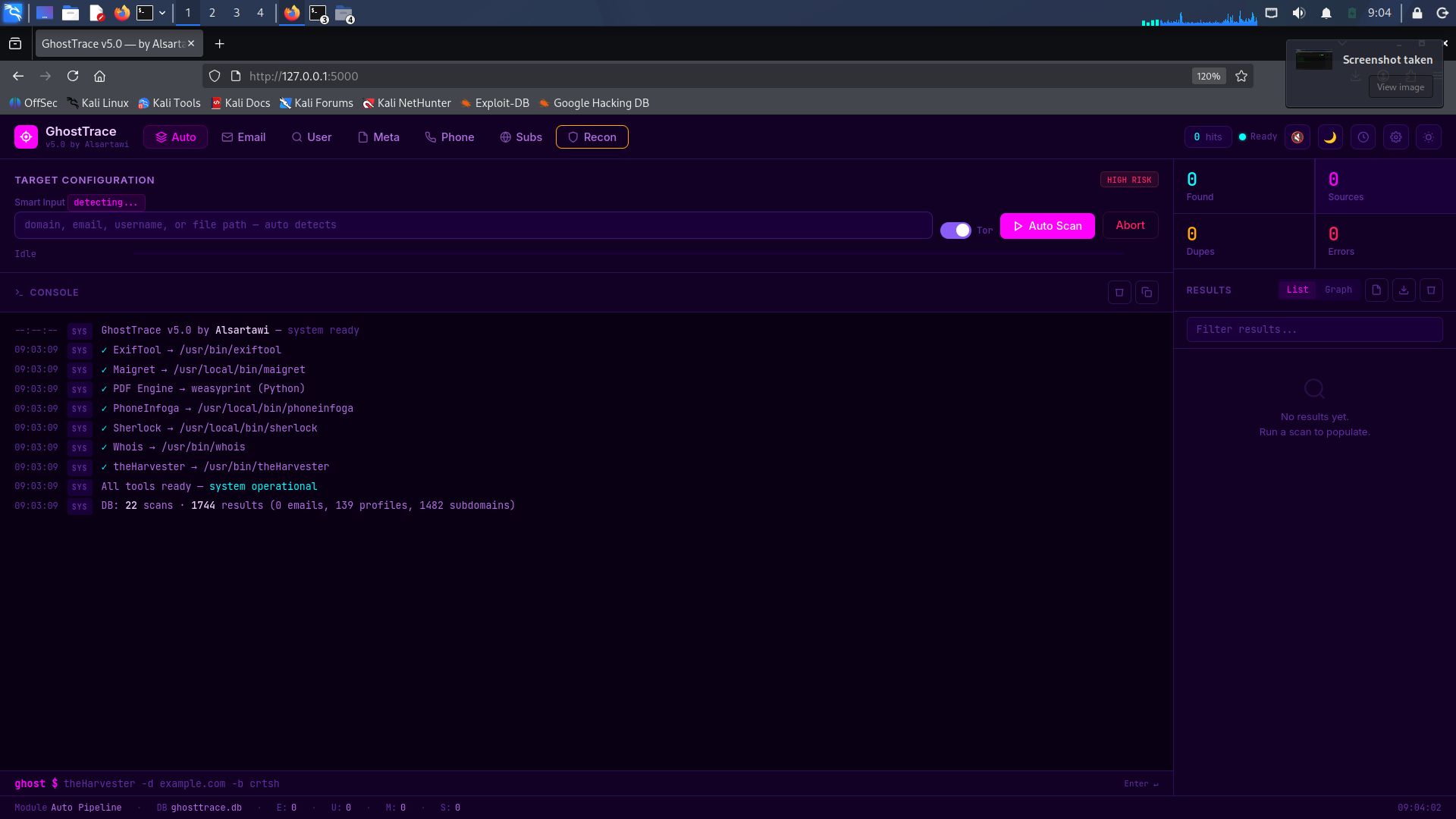
## 📸 截图
**The themes:**



-orange?logo=linux&logoColor=white)





```
██████╗ ██╗ ██╗ ██████╗ ███████╗████████╗████████╗██████╗ █████╗ ██████╗███████╗
██╔════╝ ██║ ██║██╔═══██╗██╔════╝╚══██╔══╝╚══██╔══╝██╔══██╗██╔══██╗██╔════╝██╔════╝
██║ ███╗███████║██║ ██║███████╗ ██║ ██║ ██████╔╝███████║██║ █████╗
██║ ██║██╔══██║██║ ██║╚════██║ ██║ ██║ ██╔══██╗██╔══██║██║ ██╔══╝
╚██████╔╝██║ ██║╚██████╔╝███████║ ██║ ██║ ██║ ██║██║ ██║╚██████╗███████╗
╚═════╝ ╚═╝ ╚═╝ ╚═════╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ╚═════╝╚══════╝
v5.0 by Alsartawi
```
**OSINT made simple — from beginner to professional.**
GhostTrace is a modular OSINT intelligence platform that wraps 9 Linux tools into a single web interface with real-time streaming, active reconnaissance, risk scoring, attack path analysis, and professional PDF reports. No cloud dependencies. No telemetry. Runs entirely on your machine.
"⭐ If you find this useful, a star helps a lot!"
"🐛 Found a bug? Open an issue — I actively fix them."
## ⚡ 什么使 GhostTrace 不同
- 🔍 **9 integrated tools** — not just wrappers, full intelligence pipeline
- 🛡️ **Active Recon** — DNS validation, HTTP probing, port scanning, attack surface detection
- 📊 **Risk Scoring Engine** — 0-100 dynamic scoring with actionable reasons
- 🗺️ **Attack Path Generator** — 5 rules that map real exploitation paths
- 🧠 **Smart Confidence** — scores based on result quality, not just source
- 📄 **Professional Reports** — PDF with all 9 result types, risk assessment, confidence bars
- 🌐 **Interactive Graph** — clustered force layout with shapes, legend, PNG export
- 🔐 **Authentication** — bcrypt password protection with session management
- 🎨 **12 Premium Themes** — including Royal Gold and Midnight Silver
- 🔄 **Cross-Scan Diff** — compare two scans to detect new exposures
- 📝 **Scan Notes & History** — SQLite-backed with load, notes, delete
## 🧰 集成工具 (9)
| # | Tool | Tab | What It Finds |
|---|------|-----|---------------|
| 1 | **theHarvester** | Email / Subs | Emails, subdomains, IPs from 13 free sources |
| 2 | **Maigret** | Username | Social media profiles across 2500+ sites |
| 3 | **Sherlock** | Username | Username search across 400+ sites |
| 4 | **ExifTool** | Metadata | Hidden metadata in files (author, GPS, software) |
| 5 | **PhoneInfoga** | Phone | Phone number carrier, country, format info |
| 6 | **Whois** | Auto/CLI | Domain registration, registrar, expiry, nameservers |
| 7 | **dig** | DNS | MX, TXT (SPF/DKIM/DMARC), NS, SOA, A records |
| 8 | **openssl** | SSL | Certificate SANs (hidden subdomains), issuer, expiry |
| 9 | **Google Dorks** | Dorks | 28 targeted queries for sensitive files, admin panels, leaks |
## 🎛️ 10 个扫描模块
| Module | Input | Tool Used | Example |
|--------|-------|-----------|---------|
| **Auto** | Anything | Auto-detects type | `microsoft.com` → theHarvester |
| **Email** | Domain | theHarvester | `example.com` |
| **Username** | Username | Maigret / Sherlock | `johndoe` |
| **Metadata** | File path | ExifTool | `/home/kali/photo.jpg` |
| **Phone** | Phone number | PhoneInfoga | `+1234567890` |
| **Subdomain** | Domain | theHarvester | `google.com` |
| **DNS** | Domain | dig | `example.com` → MX, TXT, NS, SOA |
| **SSL** | Domain | openssl | `example.com` → SANs, issuer, expiry |
| **Dorks** | Domain | Generator | `example.com` → 28 Google dork queries |
| **Recon** | Domain | Built-in | DNS resolve → HTTP probe → Ports → Risk |
## 🛡️ 主动侦察管道
After passive OSINT, GhostTrace validates and enriches results:
```
📡 DNS Resolution → Remove dead domains, validate alive hosts
🌐 HTTP Probing → Status codes, technology detection, security headers
🔌 Port Scanning → Top 25 common ports (SSH, RDP, MySQL, Redis...)
🎯 Attack Surface → Admin panels, login pages, API endpoints
📊 Risk Scoring → 0-100 dynamic score with explanations
🗺️ Attack Paths → 5 rules: Brute Force, Admin Panel, API, Legacy, Chained
```
### 风险评分
Every host gets a dynamic risk score based on:
| Factor | Points | Example |
|--------|--------|---------|
| Alive host | +10 | Base score for reachable targets |
| RDP exposed | +25 | Port 3389 open |
| Admin panel found | +20 | `/admin` returns 200/401/403 |
| Missing HSTS | +10 | No Strict-Transport-Security header |
| Staging/dev exposed | +18 | `staging.example.com` publicly accessible |
| WordPress detected | +10 | Known vulnerability history |
### 攻击路径规则
| Rule | Trigger | Severity |
|------|---------|----------|
| Brute Force Candidate | Login page + SSH/FTP/RDP open | HIGH |
| Admin Panel Exposed | Any admin panel found | CRITICAL (score≥65) |
| API Enumeration | API endpoint detected | HIGH |
| Legacy Service | FTP (21) or Telnet (23) open | CRITICAL |
| Chained Risk | Score≥65 + 3 contributing factors | CRITICAL |
## 🧠 智能置信度系统
Unlike tools that give static confidence, GhostTrace scores each result individually:
| Result | Old Score | Smart Score | Why |
|--------|-----------|-------------|-----|
| `Personal email pattern (firstname.lastname)` | 72% | **90%** | Personal email (firstname.lastname) |
| `Generic service alias` | 72% | **60%** | Generic alias |
| `Vulnerable admin subdomain detected` | 70% | **90%** | Admin subdomain + DNS resolved |
| `No IP confirmation on staging environmentg` | 70% | **60%** | No IP confirmation |
| `Loopback address - Filtered noise` | 70% | **15%** | Private IP — noise |
| `Broad wildcard entry` | 70% | **20%** | Wildcard entry |
## 📄 专业 PDF 报告
Reports include **all 9 result types** with:
- 📊 Stat cards (dynamic — only show categories with results)
- 📈 Confidence distribution bar (high/medium/low)
- 📝 Executive summary (auto-generated)
- 🛡️ Risk Assessment section (if recon was performed)
- 🗺️ Attack paths with severity and steps
- ⚠️ Recommendations
## ✨ 附加功能
| Feature | Description |
|---------|-------------|
| 🔐 **Authentication** | bcrypt password with `--setup`, session-based |
| 🎨 **12 Premium Themes** | Ghost Blue, Matrix, Cyberpunk, Ocean, Sunset, Toxic, Blood, Stealth, Arctic, Light, **Royal Gold**, **Midnight Silver** |
| 🌙 **Dark/Light Toggle** | Quick toggle button in navbar |
| 📋 **Copy Button** | Hover any result → click ⎘ to copy |
| 📝 **Scan Notes** Add notes to any scan from History |
| 🗑️ **Delete Scans** | Remove old scans from History with one click |
| 🔄 **Cross-Scan Diff** | Compare two scans: added/removed/unchanged |
| 🌐 **Interactive Graph** | Clustered force layout, shapes per type, legend, click highlight, PNG export |
| ⛶ **Fullscreen Graph** | Dedicated fullscreen mode with proper resizing |
| 🔎 **Result Search** | Filter results in real-time |
| 💾 **Scan History** | SQLite-backed — load, search, delete past scans |
| 🔌 **Tor Integration** | One toggle — routes traffic through Tor |
| 📦 **Export** | JSON, CSV, TXT, HTML, PDF |
| 🖥️ **CLI Mode** | Direct commands in the terminal bar |
## 🧪 质量保证
GhostTrace is continuously tested and verified:
| Category | Details |
|----------|---------|
| ✅ **6 Test Files** | validators, harvester, correlator, risk_engine, recon, new_tools |
| ✅ **CI/CD Pipeline** | GitHub Actions auto-runs tests on every push (Python 3.10, 3.11, 3.12) |
| ✅ **Linting** | flake8 checks for syntax errors and undefined names |
| ✅ **API Documentation** | Full reference at [`docs/API.md`](docs/API.md) — all 29 endpoints, schemas, cURL examples |
Run tests locally:
```
pytest tests/ -v
```
## 架构
```
GhostTrace v5.0
┌──────────┐ ┌────────────┐ ┌──────────────┐ ┌──────────┐
│ Web UI │───→│ Validators │───→│ Tool Adapters │───→│ Execution│
│ 10 tabs │ │ whitelist │ │ 9 tools │ │ Engine │
└──────────┘ └────────────┘ └──────────────┘ └────┬─────┘
↑ │
│ SSE ┌────────────┐ ┌──────────────┐ subprocess
│←─────────│ Scanner │←───│ Parser │←───────┘
│ └─────┬──────┘ └──────────────┘
│ │
│ ┌─────↓──────┐ ┌──────────────┐
│ │ Correlator │───→│ SQLite DB │
│ │ + Scorer │ │ WAL mode │
│ └─────┬──────┘ └──────────────┘
│ │
│ ┌─────↓──────┐ ┌──────────────┐
│ │ Active Recon│───→│ Risk Engine │
│ │ DNS+HTTP+ │ │ Score 0-100 │
│ │ Ports+Attack│ │ Attack Paths │
│ └────────────┘ └──────────────┘
```
**Project Structure (35+ files):**
```
ghosttrace/
├── .github/
│ └── workflows/
│ └── test.yml # CI/CD — auto tests on every push
├── docs/
│ └── API.md # Full REST API documentation
├── app.py # Flask entry + authentication
├── config.py # Centralized config
├── core/
│ ├── engine.py # Sandboxed subprocess execution
│ ├── scanner.py # Scan orchestrator + CLI + abort
│ └── differ.py # Cross-scan diff comparison
├── tools/
│ ├── base.py # ToolAdapter abstract interface
│ ├── harvester.py # theHarvester (smart confidence, API keys)
│ ├── sherlock_tool.py # Sherlock adapter
│ ├── maigret_tool.py # Maigret (false positive filter, Tor)
│ ├── exiftool.py # ExifTool adapter
│ ├── phoneinfoga_tool.py # PhoneInfoga adapter
│ ├── whois_tool.py # Whois lookup adapter
│ ├── dns_records.py # DNS records via dig
│ ├── ssl_cert.py # SSL certificate SANs extraction
│ ├── google_dorks.py # Google dork generator (28 queries)
│ └── registry.py # Plugin registry (9 tools)
├── api/
│ ├── routes.py # 4 Blueprints, 29 endpoints
│ └── recon_routes.py # Active recon pipeline
├── database/
│ └── manager.py # SQLite WAL + migrations + notes
├── intelligence/
│ └── correlator.py # Entity linking + smart scoring
├── recon/
│ ├── __init__.py # DNS, HTTP, Port, AttackSurface, DataQuality
│ └── risk_engine.py # RiskScorer + AttackPathGenerator
├── reports/
│ └── html_report.py # Professional reports (9 types + risk)
├── utils/
│ ├── validators.py # Whitelist per-tool regex validation
│ ├── security.py # Rate limiter + output sanitizer
│ └── logger.py # Rotating file logger
├── templates/
│ └── index.html # Single-page dashboard (12 themes)
├── tests/ # 6 test files
│ ├── test_validators.py
│ ├── test_harvester.py
│ ├── test_correlator.py
│ ├── test_risk_engine.py
│ ├── test_recon.py # NEW — DNSResolver, DataQuality, AttackSurface
│ └── test_new_tools.py # NEW — DNS, SSL, Dorks, Whois, Phone, Differ
├── build.sh
├── requirements.txt
└── LICENSE
```
## 安装
**Target:** Kali Linux 2025+ / Ubuntu 22.04+
### 1. 克隆并安装 Python 依赖
```
git clone https://github.com/alialsartawi7-sketch/ghosttrace.git
cd ghosttrace
pip install -r requirements.txt --break-system-packages
```
### 2. 安装 OSINT 工具
```
# 必需
sudo apt update
sudo apt install -y pkg-config libcairo2-dev python3-dev build-essential
sudo apt install theharvester exiftool -y
pip install sherlock-project maigret --break-system-packages
# PhoneInfoga
wget https://github.com/sundowndev/phoneinfoga/releases/latest/download/phoneinfoga_Linux_x86_64.tar.gz -O /tmp/phoneinfoga.tar.gz
tar xzf /tmp/phoneinfoga.tar.gz -C /tmp/
sudo mv /tmp/phoneinfoga /usr/local/bin/
# 可选 — 用于 PDF 报告
pip install weasyprint --break-system-packages
# 可选 — 用于 Tor 路由
sudo apt install tor -y
sudo service tor start
```
### 3. 验证工具
```
theHarvester -h
sherlock --version
maigret --version
exiftool -ver
phoneinfoga version
dig -v
openssl version
```
### 4. 设置密码(推荐)
```
python3 app.py --setup
```
## 用法
```
python3 app.py
# 打开 http://127.0.0.1:5000
```
### Tor
| Tool | Tor Method |
|------|-----------|
| Maigret | `--tor-proxy socks5://127.0.0.1:9050` |
| Sherlock | `--tor` |
| theHarvester | `proxychains4 -q` wrapper |
| ExifTool | N/A (local file processing) |
### CLI 模式
```
ghost $ maigret johndoe --site Instagram --site GitHub
ghost $ theHarvester -d example.com -b crtsh -l 100
ghost $ whois example.com
ghost $ dig example.com MX
```
## 📸 截图
**The themes:**
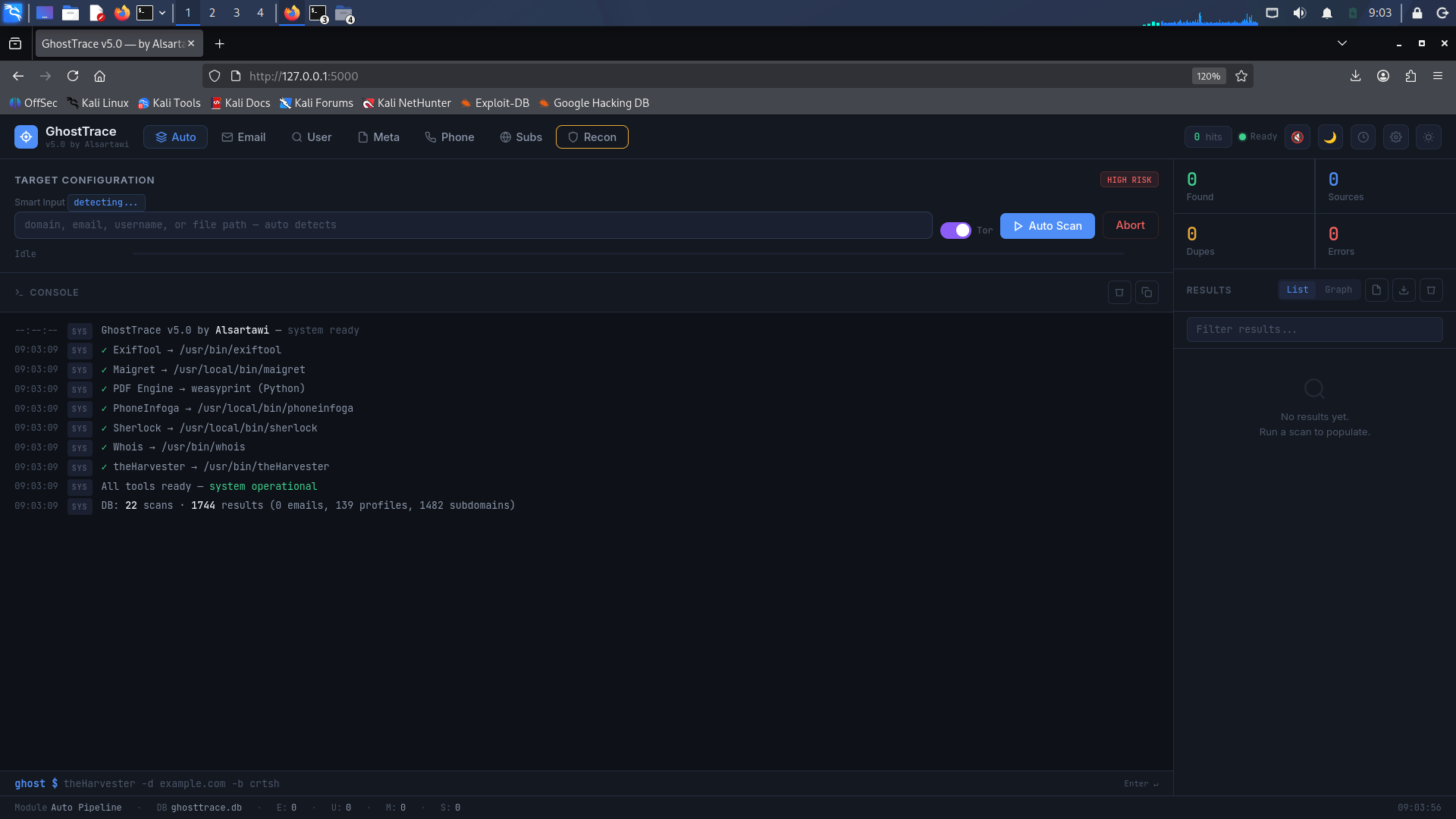
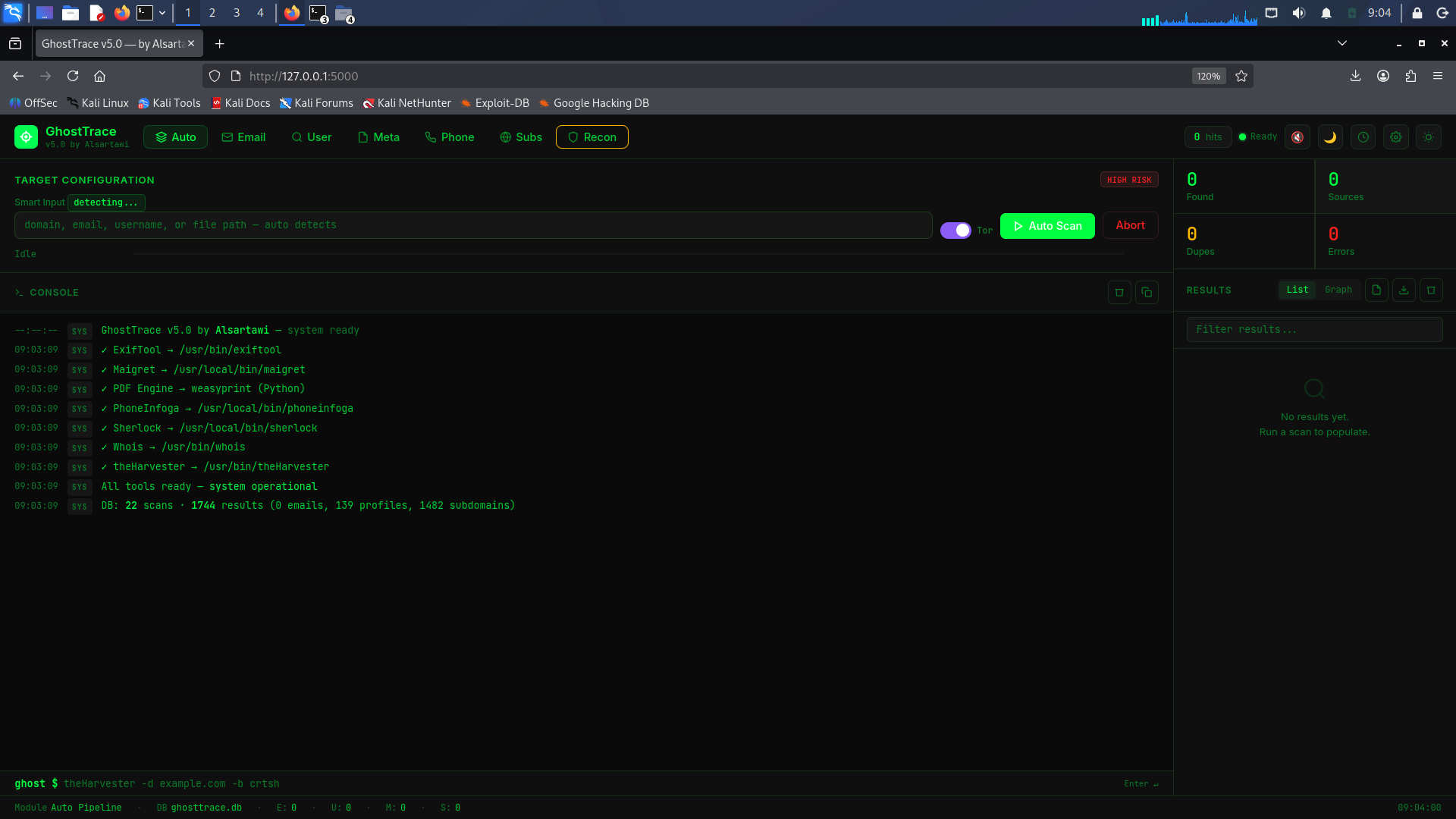
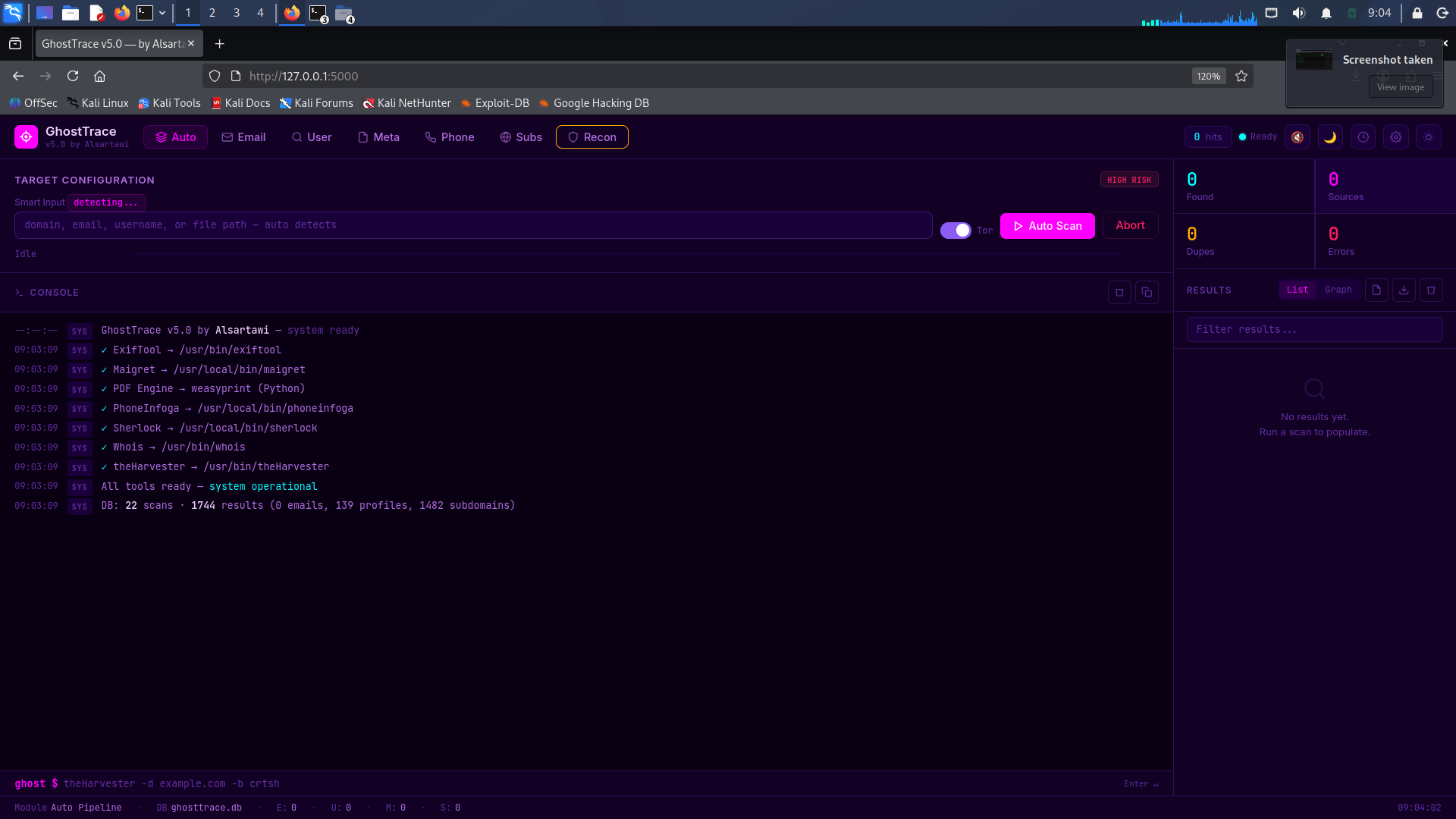 All themes — try it 😉
All themes — try it 😉
 **The scans:**
**The scans:**
 **The Graph:**
**The Graph:**
 **The PDF Reports:**
**The PDF Reports:**
 ## 安全模型
| Layer | Implementation |
|-------|---------------|
| Authentication | bcrypt password hashing, session-based auth |
| Input validation | Per-field regex: domain, email, username, filepath, phone |
| CLI validation | **Whitelist** regex per tool (not a blacklist) |
| Path traversal | Blocks `..`, `/etc/shadow`, `/root`, `.ssh` |
| Output sanitization | Strips ANSI codes + control characters |
| Rate limiting | 20 scans per 60 seconds |
| Process isolation | `os.setsid` + process group kill on timeout/abort |
## 已知限制
- Instagram/Facebook block automated checks (Cloudflare) — even with Tor
- Maigret + Tor on all 2500+ sites is slow — use `--site` targeting
- Google Dorks generates queries only — user must search manually
- PhoneInfoga requires separate installation from GitHub releases
- PDF requires `weasyprint` (recommended) or `wkhtmltopdf`
- Linux only — Windows not supported
## 免责声明
GhostTrace is intended for **authorized security research, penetration testing, and educational purposes only**.
The author assumes no liability for misuse. Always obtain proper authorization before performing OSINT operations on targets you do not own.
**Use responsibly. Respect privacy. Follow your country's laws.**
## 许可证
MIT License — see [LICENSE](LICENSE)
**Built with ❤️ by Alsartawi**
## 安全模型
| Layer | Implementation |
|-------|---------------|
| Authentication | bcrypt password hashing, session-based auth |
| Input validation | Per-field regex: domain, email, username, filepath, phone |
| CLI validation | **Whitelist** regex per tool (not a blacklist) |
| Path traversal | Blocks `..`, `/etc/shadow`, `/root`, `.ssh` |
| Output sanitization | Strips ANSI codes + control characters |
| Rate limiting | 20 scans per 60 seconds |
| Process isolation | `os.setsid` + process group kill on timeout/abort |
## 已知限制
- Instagram/Facebook block automated checks (Cloudflare) — even with Tor
- Maigret + Tor on all 2500+ sites is slow — use `--site` targeting
- Google Dorks generates queries only — user must search manually
- PhoneInfoga requires separate installation from GitHub releases
- PDF requires `weasyprint` (recommended) or `wkhtmltopdf`
- Linux only — Windows not supported
## 免责声明
GhostTrace is intended for **authorized security research, penetration testing, and educational purposes only**.
The author assumes no liability for misuse. Always obtain proper authorization before performing OSINT operations on targets you do not own.
**Use responsibly. Respect privacy. Follow your country's laws.**
## 许可证
MIT License — see [LICENSE](LICENSE)
**Built with ❤️ by Alsartawi**标签:AES-256, API, API路由, ESC4, GitHub Actions, OSINT, Python, Python 3.10, 单元测试, 威胁建模, 安全测试工具, 平台, 攻击路径, 攻击面分析, 无后门, 模块化, 测试, 漏洞评估, 网络安全, 网络调试, 自动化, 自动笔记, 调试工具, 逆向工具, 隐私保护, 风险评分