CyberGriffith/ADBOY
GitHub: CyberGriffith/ADBOY
一款专注于 Active Directory 攻击路径分析与权限提升检测的工具,整合 LDAP 扫描与 BloodHound 数据解析能力。
Stars: 3 | Forks: 0
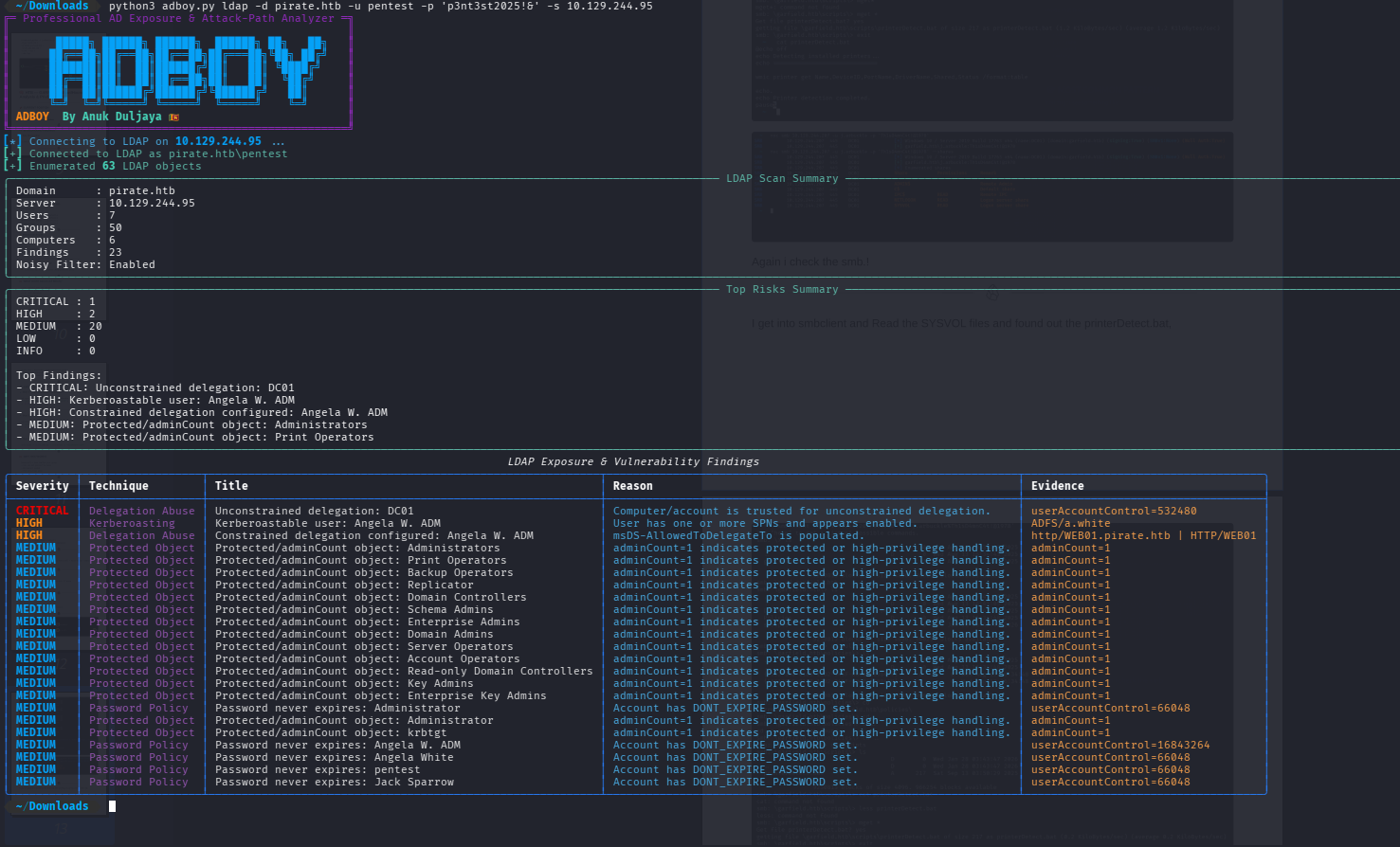
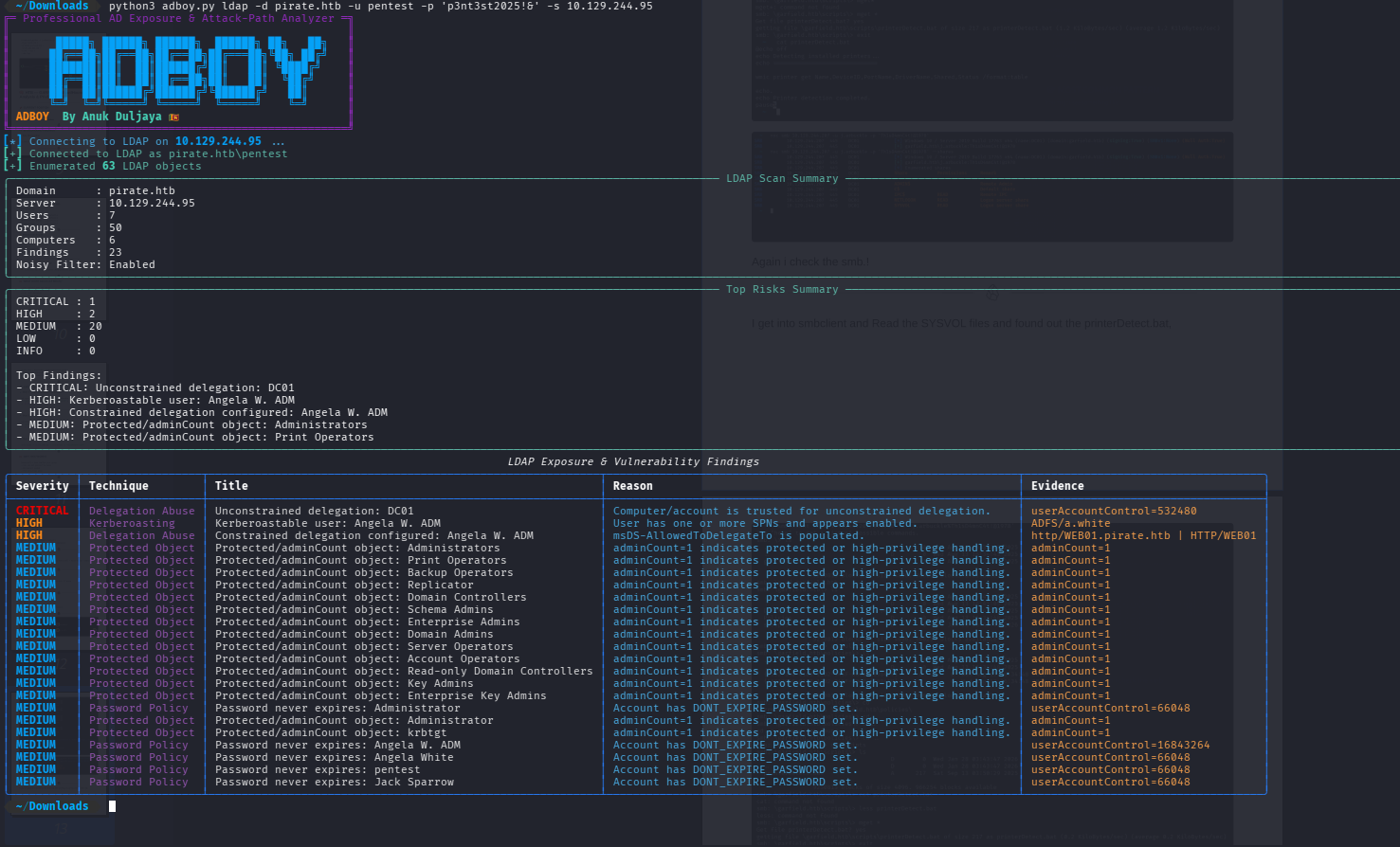
# 🔥 ADBOY — Active Directory Attack Path Analyzer
### By Anuk Duljaya 🇱🇰
ADBOY is a pro toofessional Active Directory enumeration and attack-path analysis tool designed to identify privilege escalation paths in AD environments.
 ## 🚀 Features
* 🔍 LDAP vulnerability scanning
* 🧠 BloodHound JSON parsing
* ⚠️ Detection of dangerous ACL edges
* 🔗 Privilege path identification
* 🎨 Colorized professional output
* 📊 Top risk summary
* 📁 JSON export for reporting
## 🧪 Supported Attack Detection
* Kerberoasting
* AS-REP Roasting
* ACL Abuse (GenericAll, WriteDACL, etc.)
* Shadow Credentials (AddKeyCredentialLink)
* Delegation Abuse
* Privileged Group Paths
## ⚙️ Installation
```
git clone https://github.com/CyberGriffith/ADBOY.git
cd ADBOY
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
```
## 🧠 Usage
### LDAP Scan
```
python3 adboy.py ldap -d domain.local -u user -p pass -s
## 🚀 Features
* 🔍 LDAP vulnerability scanning
* 🧠 BloodHound JSON parsing
* ⚠️ Detection of dangerous ACL edges
* 🔗 Privilege path identification
* 🎨 Colorized professional output
* 📊 Top risk summary
* 📁 JSON export for reporting
## 🧪 Supported Attack Detection
* Kerberoasting
* AS-REP Roasting
* ACL Abuse (GenericAll, WriteDACL, etc.)
* Shadow Credentials (AddKeyCredentialLink)
* Delegation Abuse
* Privileged Group Paths
## ⚙️ Installation
```
git clone https://github.com/CyberGriffith/ADBOY.git
cd ADBOY
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
```
## 🧠 Usage
### LDAP Scan
```
python3 adboy.py ldap -d domain.local -u user -p pass -s
```
### BloodHound Analysis
```
python3 adboy.py bh --bh-dir ./bloodhound --start 'USER@DOMAIN.LOCAL'
```
## 🧾 Example Output
```
CRITICAL: PENTEST -> GenericAll -> ENTERPRISE ADMINS
→ Full domain compromise path detected
```
## ⚠️ Disclaimer
This tool is intended for:
* Educational purposes
* Authorized penetration testing
* CTF environments (Hack The Box, TryHackMe)
## 👨💻 Author
**Anuk Duljaya**
Cybersecurity Student | AD Exploitation Enthusiast
 ## 🚀 Features
* 🔍 LDAP vulnerability scanning
* 🧠 BloodHound JSON parsing
* ⚠️ Detection of dangerous ACL edges
* 🔗 Privilege path identification
* 🎨 Colorized professional output
* 📊 Top risk summary
* 📁 JSON export for reporting
## 🧪 Supported Attack Detection
* Kerberoasting
* AS-REP Roasting
* ACL Abuse (GenericAll, WriteDACL, etc.)
* Shadow Credentials (AddKeyCredentialLink)
* Delegation Abuse
* Privileged Group Paths
## ⚙️ Installation
```
git clone https://github.com/CyberGriffith/ADBOY.git
cd ADBOY
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
```
## 🧠 Usage
### LDAP Scan
```
python3 adboy.py ldap -d domain.local -u user -p pass -s
## 🚀 Features
* 🔍 LDAP vulnerability scanning
* 🧠 BloodHound JSON parsing
* ⚠️ Detection of dangerous ACL edges
* 🔗 Privilege path identification
* 🎨 Colorized professional output
* 📊 Top risk summary
* 📁 JSON export for reporting
## 🧪 Supported Attack Detection
* Kerberoasting
* AS-REP Roasting
* ACL Abuse (GenericAll, WriteDACL, etc.)
* Shadow Credentials (AddKeyCredentialLink)
* Delegation Abuse
* Privileged Group Paths
## ⚙️ Installation
```
git clone https://github.com/CyberGriffith/ADBOY.git
cd ADBOY
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
```
## 🧠 Usage
### LDAP Scan
```
python3 adboy.py ldap -d domain.local -u user -p pass -s 标签:ACL滥用, Active Directory, AD安全, AS-REP Roasting, BloodHound, Checkov, CTF工具, Kerberoasting, LDAP扫描, Modbus, Plaso, StruQ, 协议分析, 域名枚举, 委派滥用, 报告导出, 攻击路径分析, 权限提升, 权限路径识别, 漏洞搜索, 网络安全, 逆向工具, 隐私保护