Oyedibu/Hybrid-SOC-Home-Lab-Network-Security-Implementation
GitHub: Oyedibu/Hybrid-SOC-Home-Lab-Network-Security-Implementation
通过pfSense和Hyper-V构建多分段虚拟网络环境,为恶意软件分析和钓鱼调查提供安全的隔离测试区域,防止威胁横向移动至管理网络。
Stars: 0 | Forks: 0
# 混合SOC家庭实验室网络安全实施
本项目涉及使用 pfSense 和 Hyper V 进行多分段虚拟网络环境的架构设计和部署。核心目标是建立一个安全的"测试"区域,用于恶意软件和网络钓鱼分析,并与管理网络进行逻辑隔离,以防止横向移动。
# 网络架构
```
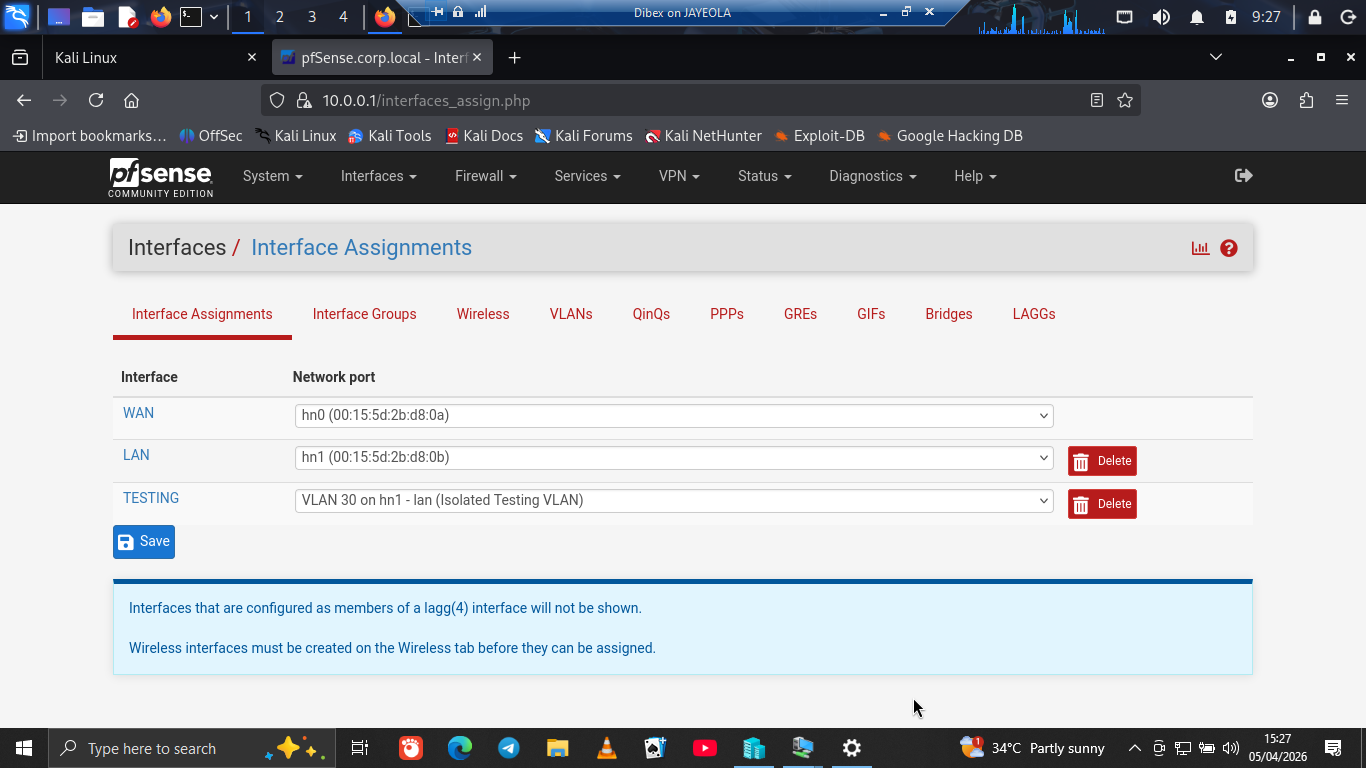
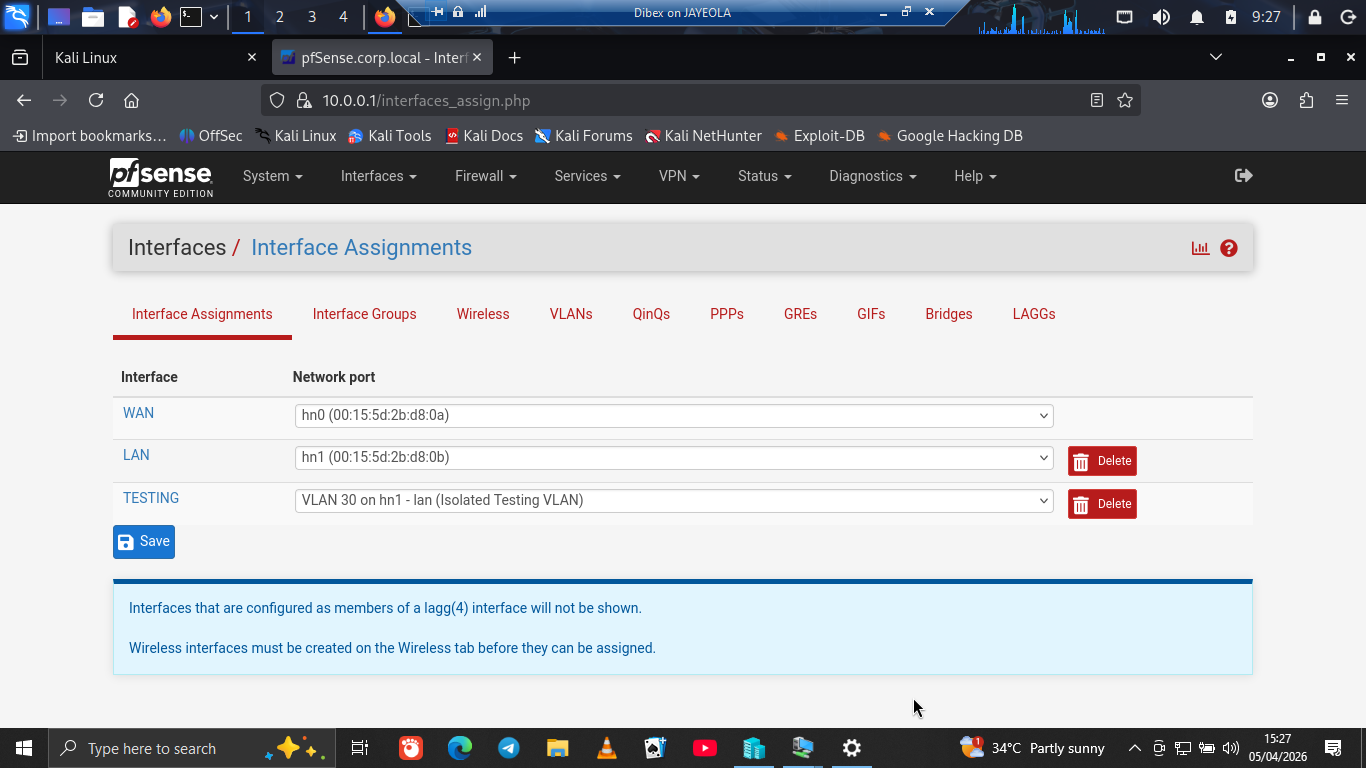
The environment is divided into three distinct security zones:
. WAN Interface: Connects to the physical internet gateway
. LAN(Management) Segment: Dedicated to the KALI Linux attack and monitoring machine (10.0.0.102)
. Testing(Isolated) Segment: A dedicated VLAN for victim machines and malware execution (10.0.30.100)
```
 # 安全策略与实施
```
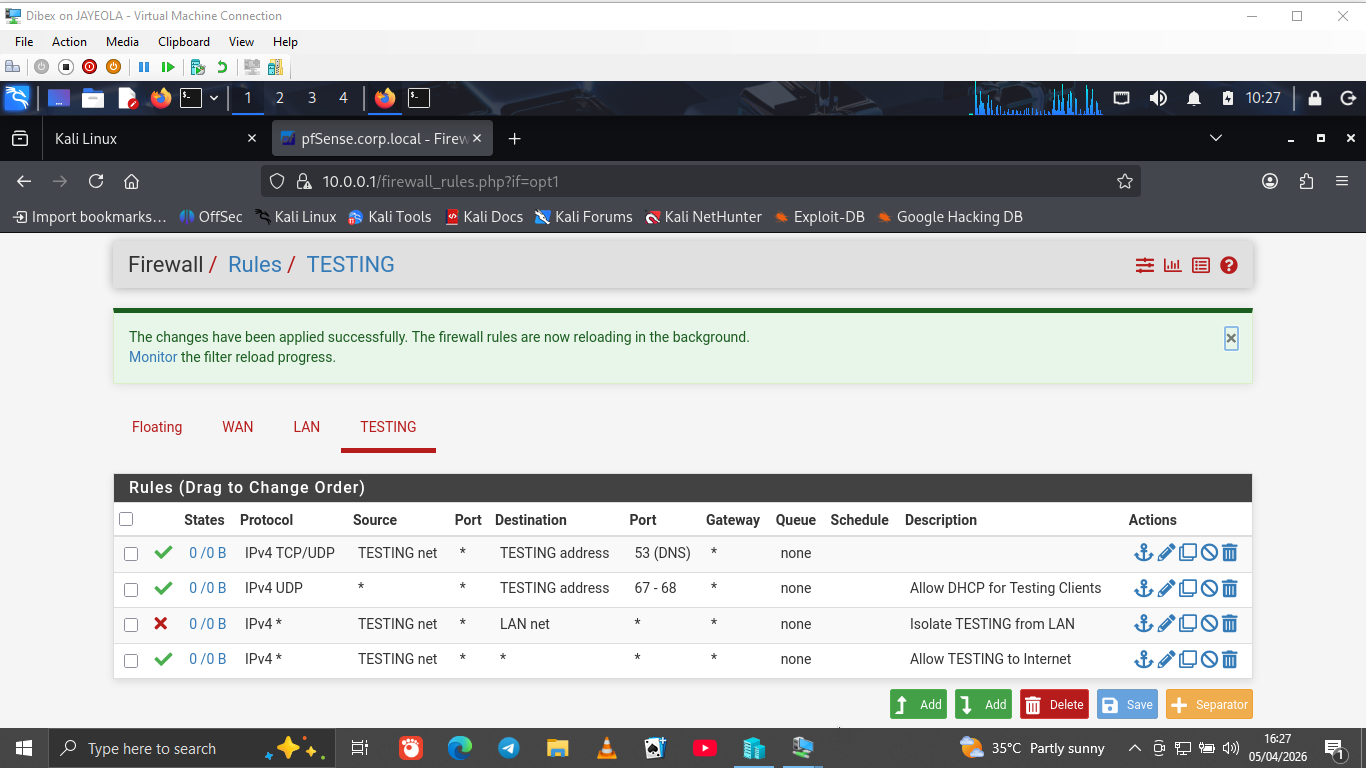
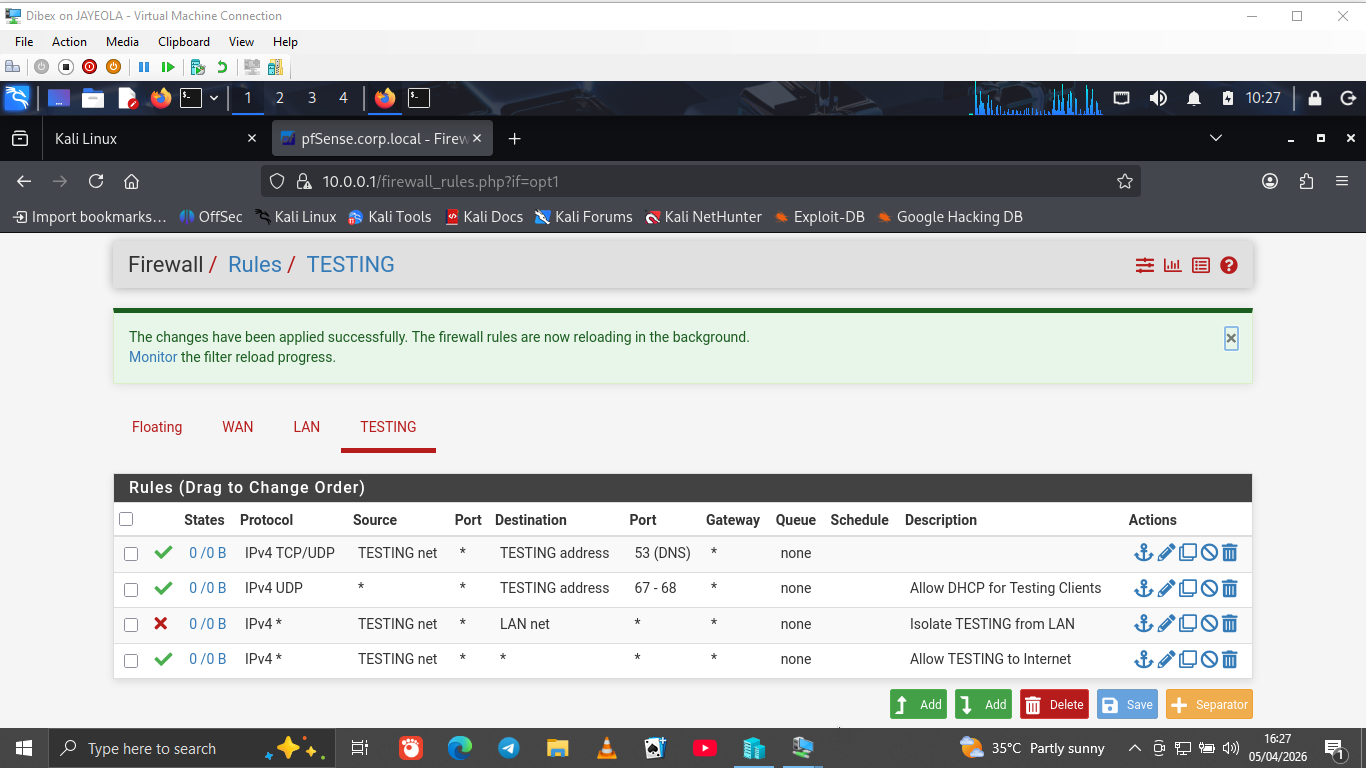
Using pfSense, I implemented a Zero-Trust egress policy for the Testing segment.
.Rule 1: Explicitly allow DNS and DHCP for client connectivity.
.Rule 2: Block all traffic from the Testing segment to the Management LAN
.Rule 3: Allow Restricted internet access for threat research
```
# 安全策略与实施
```
Using pfSense, I implemented a Zero-Trust egress policy for the Testing segment.
.Rule 1: Explicitly allow DNS and DHCP for client connectivity.
.Rule 2: Block all traffic from the Testing segment to the Management LAN
.Rule 3: Allow Restricted internet access for threat research
```
 # 技术挑战与故障排除
```
During the deployment , a routing conflict occured where the management machine(Kali) retained legacy IP configuration leading to a "Destination Host Unreachable" error.
. Issue: Conflict between the 192.168.100.10 legacy static IP and the new 10.0.0.102 DHCP lease
. Resolution: Performed a network interface flush and renewed the DHCP lease to restore WAN connectivity
```
# 取证验证(Wireshark分析)
```
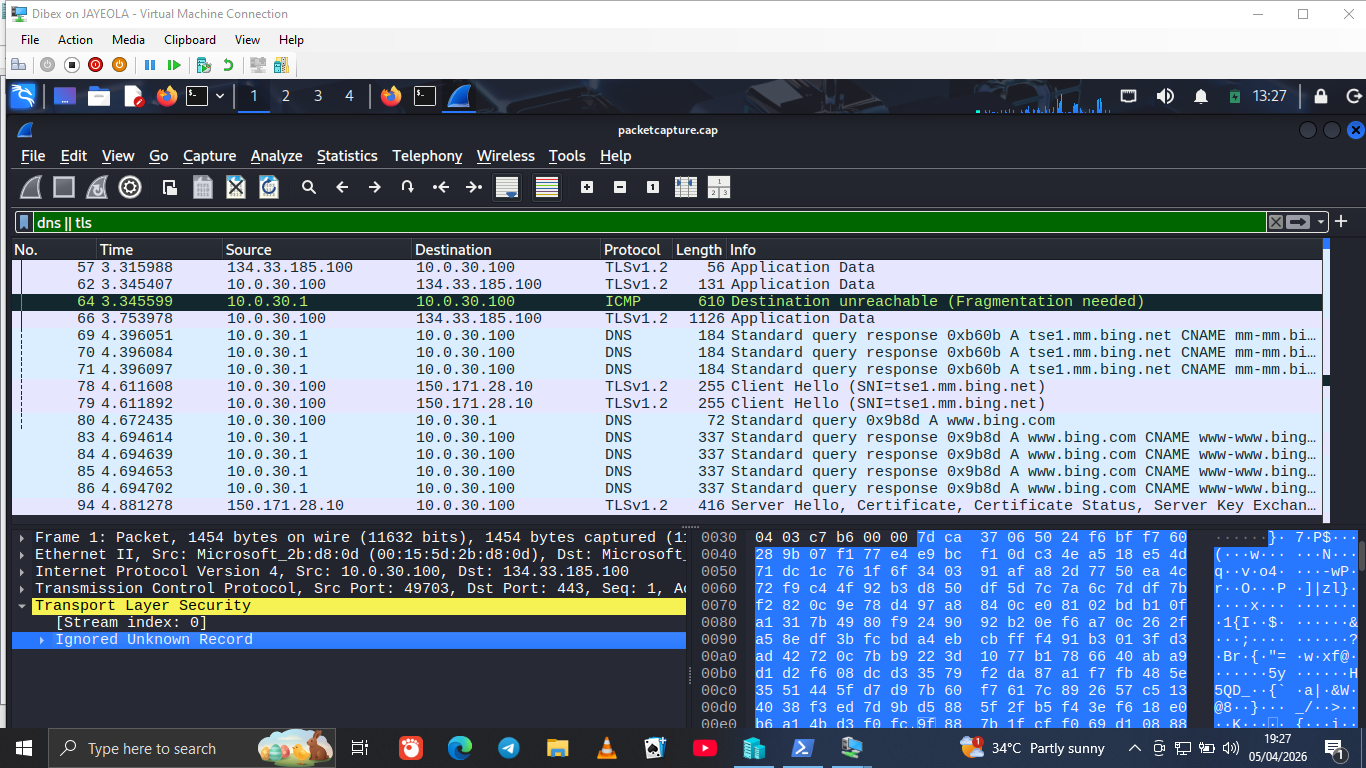
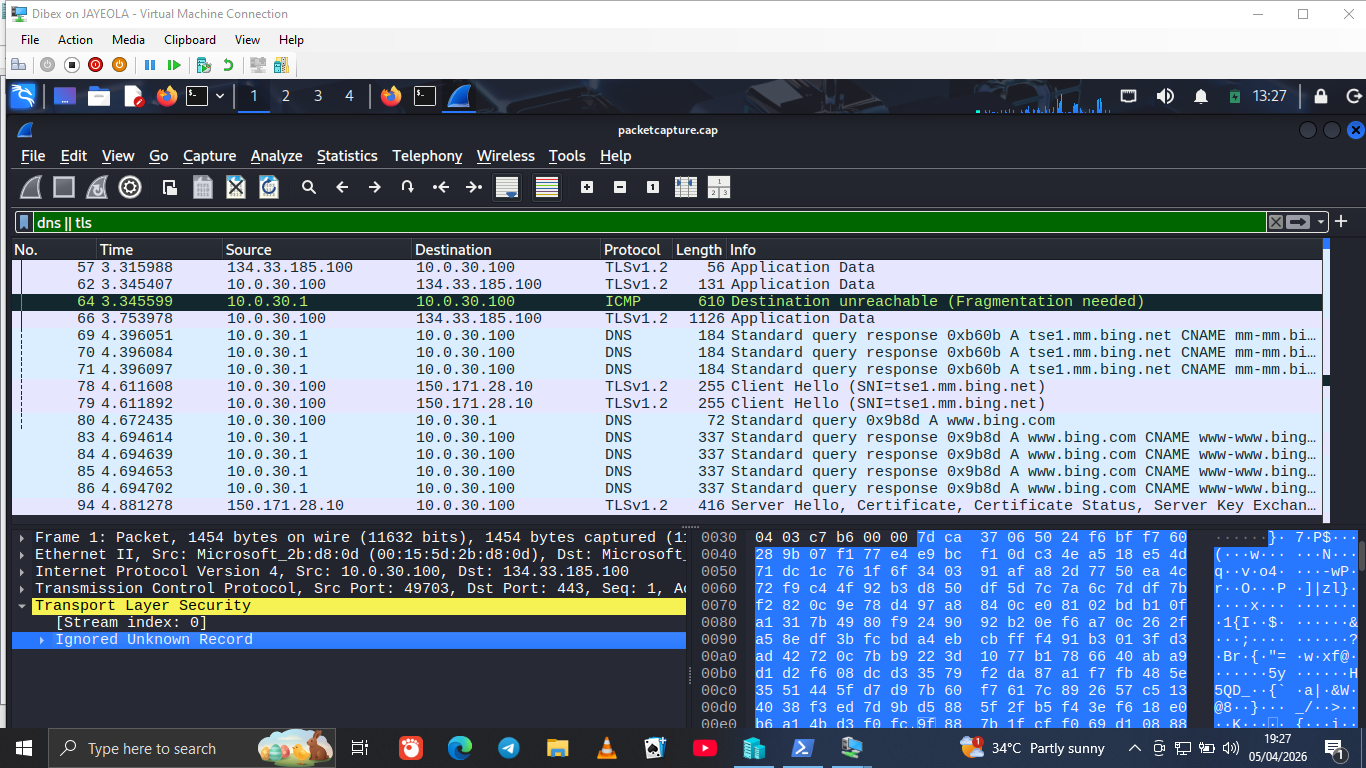
To verify the integrity of the security boundary, I conducted a deep packet inspection on the traffic crossing gateway.
. Validation: Wireshark captures successfully identified ICMP Destination Unreachable packets when the Victim VM attempted to ping the Management gateway.
. Result: This confirm that the firewall is sucessfully dropping unauthorized lateral movement attempts.
```
# 技术挑战与故障排除
```
During the deployment , a routing conflict occured where the management machine(Kali) retained legacy IP configuration leading to a "Destination Host Unreachable" error.
. Issue: Conflict between the 192.168.100.10 legacy static IP and the new 10.0.0.102 DHCP lease
. Resolution: Performed a network interface flush and renewed the DHCP lease to restore WAN connectivity
```
# 取证验证(Wireshark分析)
```
To verify the integrity of the security boundary, I conducted a deep packet inspection on the traffic crossing gateway.
. Validation: Wireshark captures successfully identified ICMP Destination Unreachable packets when the Victim VM attempted to ping the Management gateway.
. Result: This confirm that the firewall is sucessfully dropping unauthorized lateral movement attempts.
```
 # 邮件安全与网络钓鱼调查
```
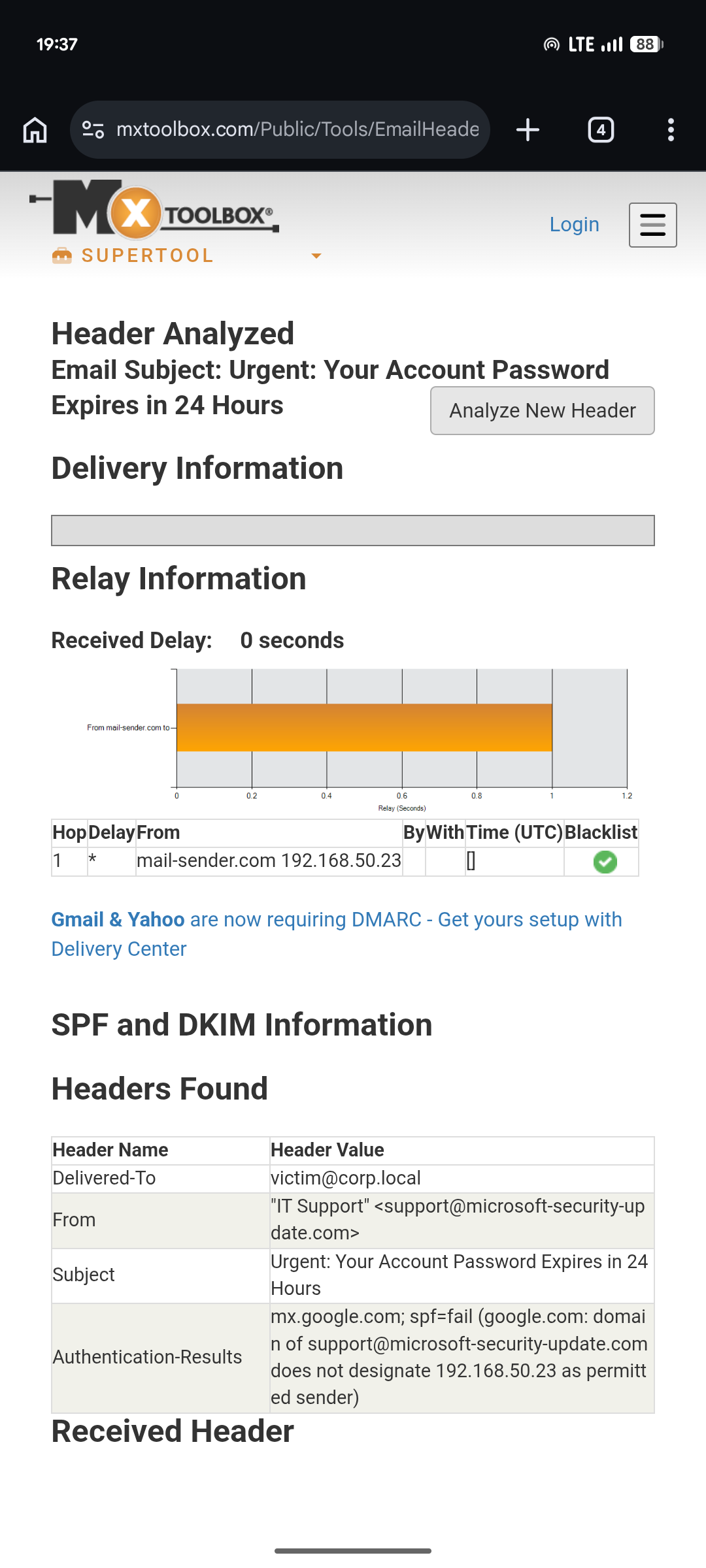
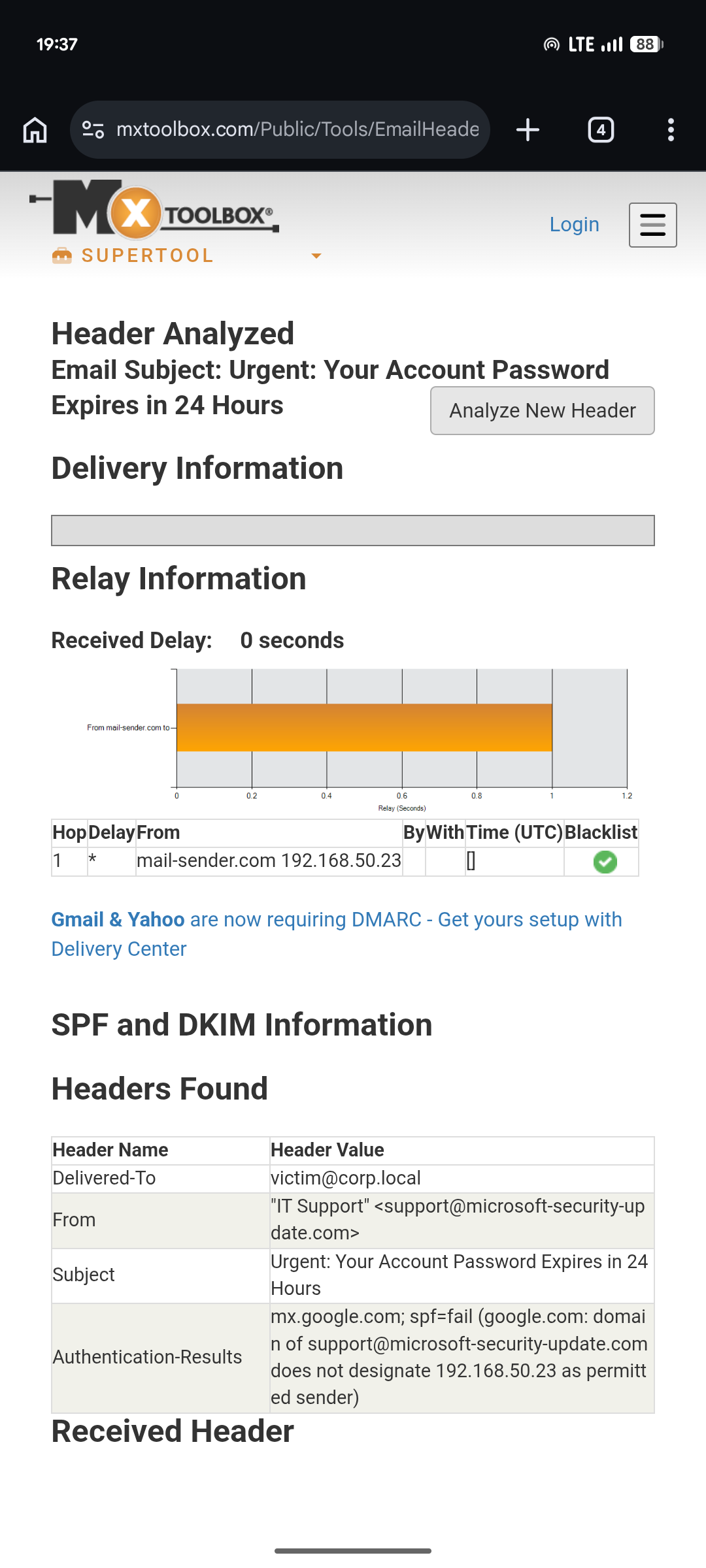
I used the lab also to serve as a sandbox for email header forensics.
. Investigation: Analyzed a spoofed "IT support" email using MXToolbox
. Findings: Identified as SPF Failure, indicating the source IP was unauthorized to send on behalf of the domain.
```
# 邮件安全与网络钓鱼调查
```
I used the lab also to serve as a sandbox for email header forensics.
. Investigation: Analyzed a spoofed "IT support" email using MXToolbox
. Findings: Identified as SPF Failure, indicating the source IP was unauthorized to send on behalf of the domain.
```
 # 展示的技能
```
. Network Micro-segmentation
. Firewall Rule Configuration(pfSense)
. Packet Analysis & Forensic Validation (Wireshark)
. Virtual infrastructure management (Hyper V)
```
# 使用的工具
```
. Hypervisor: Hyper-V
. Firewall/Router: pfSense
. Operating System: Kali Linux, Windows 10
. Analysis Tools: Wireshark
```
# 展示的技能
```
. Network Micro-segmentation
. Firewall Rule Configuration(pfSense)
. Packet Analysis & Forensic Validation (Wireshark)
. Virtual infrastructure management (Hyper V)
```
# 使用的工具
```
. Hypervisor: Hyper-V
. Firewall/Router: pfSense
. Operating System: Kali Linux, Windows 10
. Analysis Tools: Wireshark
```
 # 安全策略与实施
```
Using pfSense, I implemented a Zero-Trust egress policy for the Testing segment.
.Rule 1: Explicitly allow DNS and DHCP for client connectivity.
.Rule 2: Block all traffic from the Testing segment to the Management LAN
.Rule 3: Allow Restricted internet access for threat research
```
# 安全策略与实施
```
Using pfSense, I implemented a Zero-Trust egress policy for the Testing segment.
.Rule 1: Explicitly allow DNS and DHCP for client connectivity.
.Rule 2: Block all traffic from the Testing segment to the Management LAN
.Rule 3: Allow Restricted internet access for threat research
```
 # 技术挑战与故障排除
```
During the deployment , a routing conflict occured where the management machine(Kali) retained legacy IP configuration leading to a "Destination Host Unreachable" error.
. Issue: Conflict between the 192.168.100.10 legacy static IP and the new 10.0.0.102 DHCP lease
. Resolution: Performed a network interface flush and renewed the DHCP lease to restore WAN connectivity
```
# 取证验证(Wireshark分析)
```
To verify the integrity of the security boundary, I conducted a deep packet inspection on the traffic crossing gateway.
. Validation: Wireshark captures successfully identified ICMP Destination Unreachable packets when the Victim VM attempted to ping the Management gateway.
. Result: This confirm that the firewall is sucessfully dropping unauthorized lateral movement attempts.
```
# 技术挑战与故障排除
```
During the deployment , a routing conflict occured where the management machine(Kali) retained legacy IP configuration leading to a "Destination Host Unreachable" error.
. Issue: Conflict between the 192.168.100.10 legacy static IP and the new 10.0.0.102 DHCP lease
. Resolution: Performed a network interface flush and renewed the DHCP lease to restore WAN connectivity
```
# 取证验证(Wireshark分析)
```
To verify the integrity of the security boundary, I conducted a deep packet inspection on the traffic crossing gateway.
. Validation: Wireshark captures successfully identified ICMP Destination Unreachable packets when the Victim VM attempted to ping the Management gateway.
. Result: This confirm that the firewall is sucessfully dropping unauthorized lateral movement attempts.
```
 # 邮件安全与网络钓鱼调查
```
I used the lab also to serve as a sandbox for email header forensics.
. Investigation: Analyzed a spoofed "IT support" email using MXToolbox
. Findings: Identified as SPF Failure, indicating the source IP was unauthorized to send on behalf of the domain.
```
# 邮件安全与网络钓鱼调查
```
I used the lab also to serve as a sandbox for email header forensics.
. Investigation: Analyzed a spoofed "IT support" email using MXToolbox
. Findings: Identified as SPF Failure, indicating the source IP was unauthorized to send on behalf of the domain.
```
 # 展示的技能
```
. Network Micro-segmentation
. Firewall Rule Configuration(pfSense)
. Packet Analysis & Forensic Validation (Wireshark)
. Virtual infrastructure management (Hyper V)
```
# 使用的工具
```
. Hypervisor: Hyper-V
. Firewall/Router: pfSense
. Operating System: Kali Linux, Windows 10
. Analysis Tools: Wireshark
```
# 展示的技能
```
. Network Micro-segmentation
. Firewall Rule Configuration(pfSense)
. Packet Analysis & Forensic Validation (Wireshark)
. Virtual infrastructure management (Hyper V)
```
# 使用的工具
```
. Hypervisor: Hyper-V
. Firewall/Router: pfSense
. Operating System: Kali Linux, Windows 10
. Analysis Tools: Wireshark
```
标签:DAST, DHCP, DNS, Hyper-V, ICMP, pfSense, VLAN, Wireshark, 句柄查看, 安全边界, 安全运营中心, 家庭实验室, 恶意软件分析, 横向移动防护, 流量监控, 网络分段, 网络安全, 网络映射, 网络架构设计, 网络钓鱼分析, 虚拟化, 防火墙策略, 隐私保护, 隔离网络, 零信任架构