toyin-soc-analyst/soc-brute-force-detection-splunk
GitHub: toyin-soc-analyst/soc-brute-force-detection-splunk
该项目展示了如何利用Splunk分析Windows事件日志,从而检测和调查账户暴力破解攻击。
Stars: 1 | Forks: 0
## 📌 场景
某公司的安全团队注意到一个用户账户上存在多次失败的登录尝试。作为 SOC 分析师,我的任务是利用 Splunk 调查潜在的暴力破解攻击活动。
## 🎯 目标
- 检测可疑的登录行为
- 分析身份验证日志
- 识别攻击模式
- 提出缓解策略
## 🛠️ 使用的工具
- Splunk (SIEM)
- Windows 事件日志
- MITRE ATT&CK 框架
## 🔍 调查步骤
### 1. 日志收集
收集 Windows 事件日志并将其导入 Splunk。
### 2. 搜索查询
使用 Splunk 识别多次失败的登录尝试:
```
index=wineventlog EventCode=4625
| stats count by Account_Name, Source_Network_Address
| sort - count
3. Detection
Identified repeated failed login attempts from a single IP address targeting multiple accounts.
4. Analysis
High volume of failed logins within short time frame
Same IP attempting access across accounts
Pattern consistent with brute-force attack
🚨 Findings
Suspicious IP: 192.168.1.100
Attack Type: Brute Force Attempt
Target: Multiple user accounts
Risk Level: High
🛡️ Recommendations
Block the malicious IP address
Enable Multi-Factor Authentication (MFA)
Implement account lockout policies
Monitor login attempts continuously
## 📸 Evidence
## 📸 Evidence
📚 Skills Demonstrated
SIEM Log Analysis
Threat Detection
Incident Investigation
Security Monitoring
MITRE ATT&CK Mapping
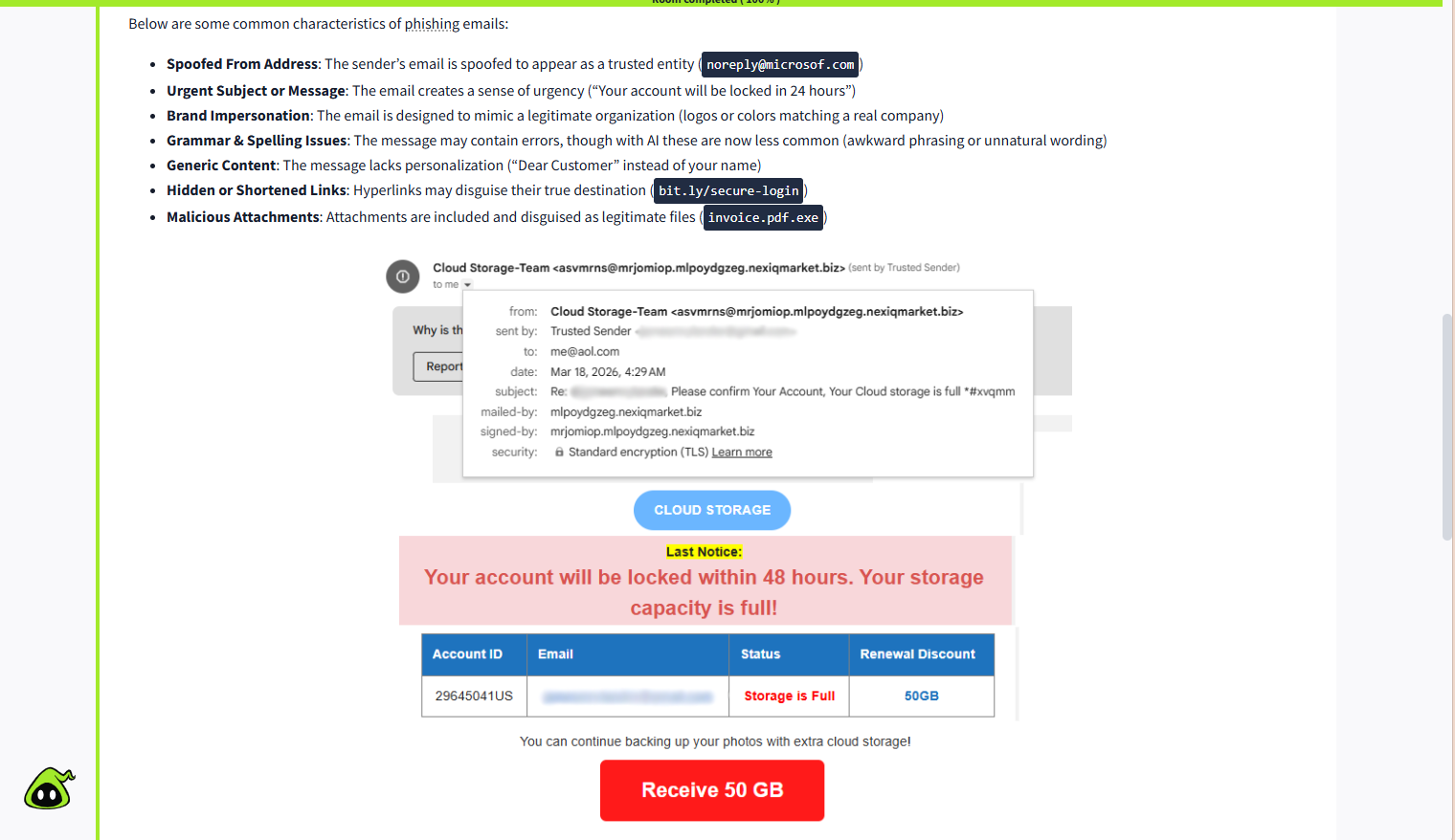
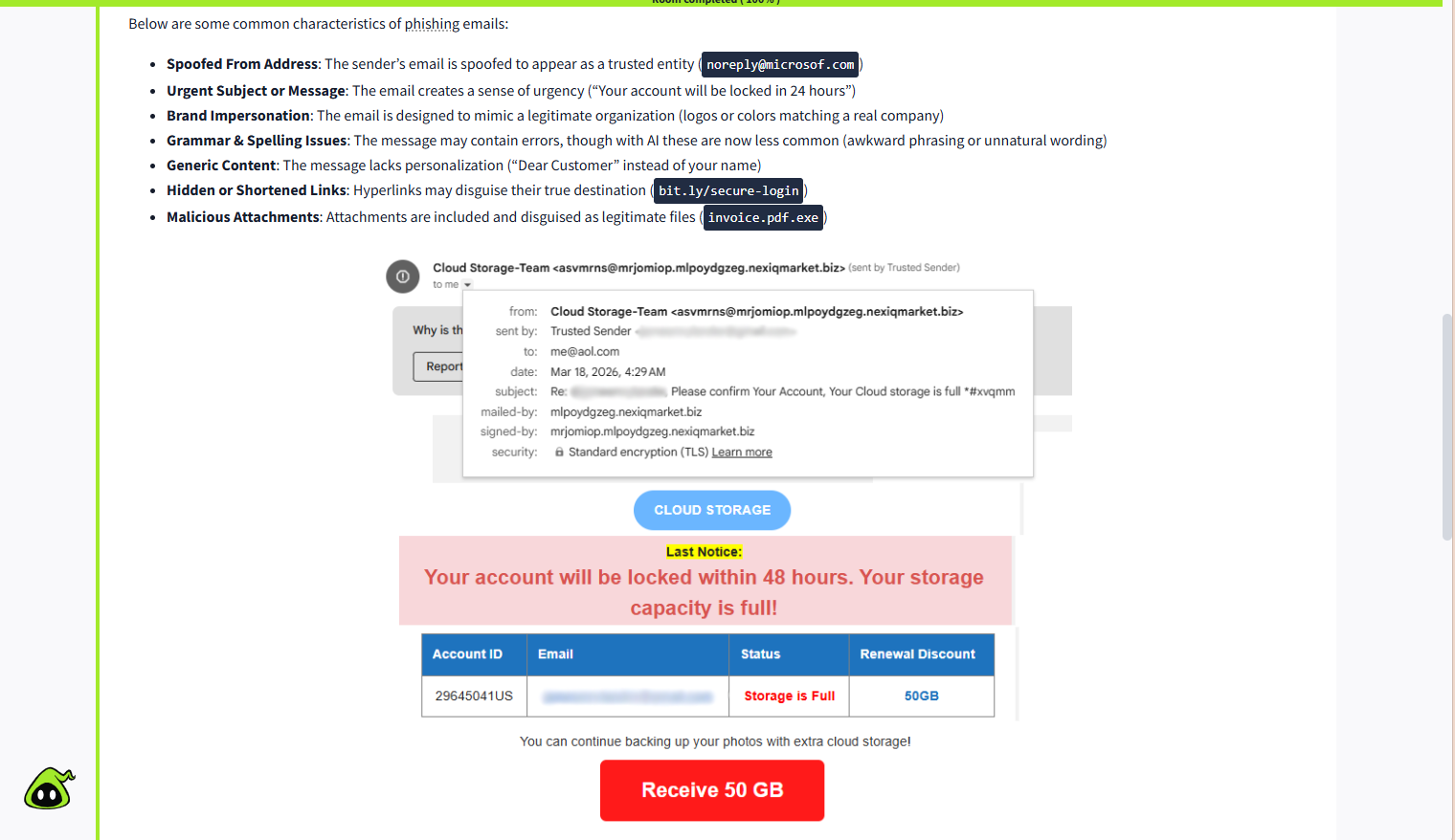
## 🚨 Findings
- Attack Type: Credential Harvesting
- Malicious Domain: bit.ly/secure-login
- Spoofed Email: noreply@microsoft.com
- Technique: Social Engineering
- Risk Level: High
```
标签:AMSI绕过, BurpSuite集成, IP封禁, MFA, PoC, Windows日志, 事件调查, 凭据填充, 多因素认证, 威胁检测, 子域枚举, 安全运营中心, 暴力破解, 深度包检测, 登录失败, 红队行动, 网络安全, 网络安全分析, 网络映射, 账户锁定策略, 隐私保护