mostafaahmedaly2003/SOC-monitoring-lab
GitHub: mostafaahmedaly2003/SOC-monitoring-lab
一个集成的 SOC 迷你实验室,通过 Snort、Wazuh、T-Pot 与 Shuffle SOAR 实现秒级检测与自动响应。
Stars: 3 | Forks: 3
# SOC Mini-Lab: Snort + Wazuh + T-Pot + Shuffle SOAR








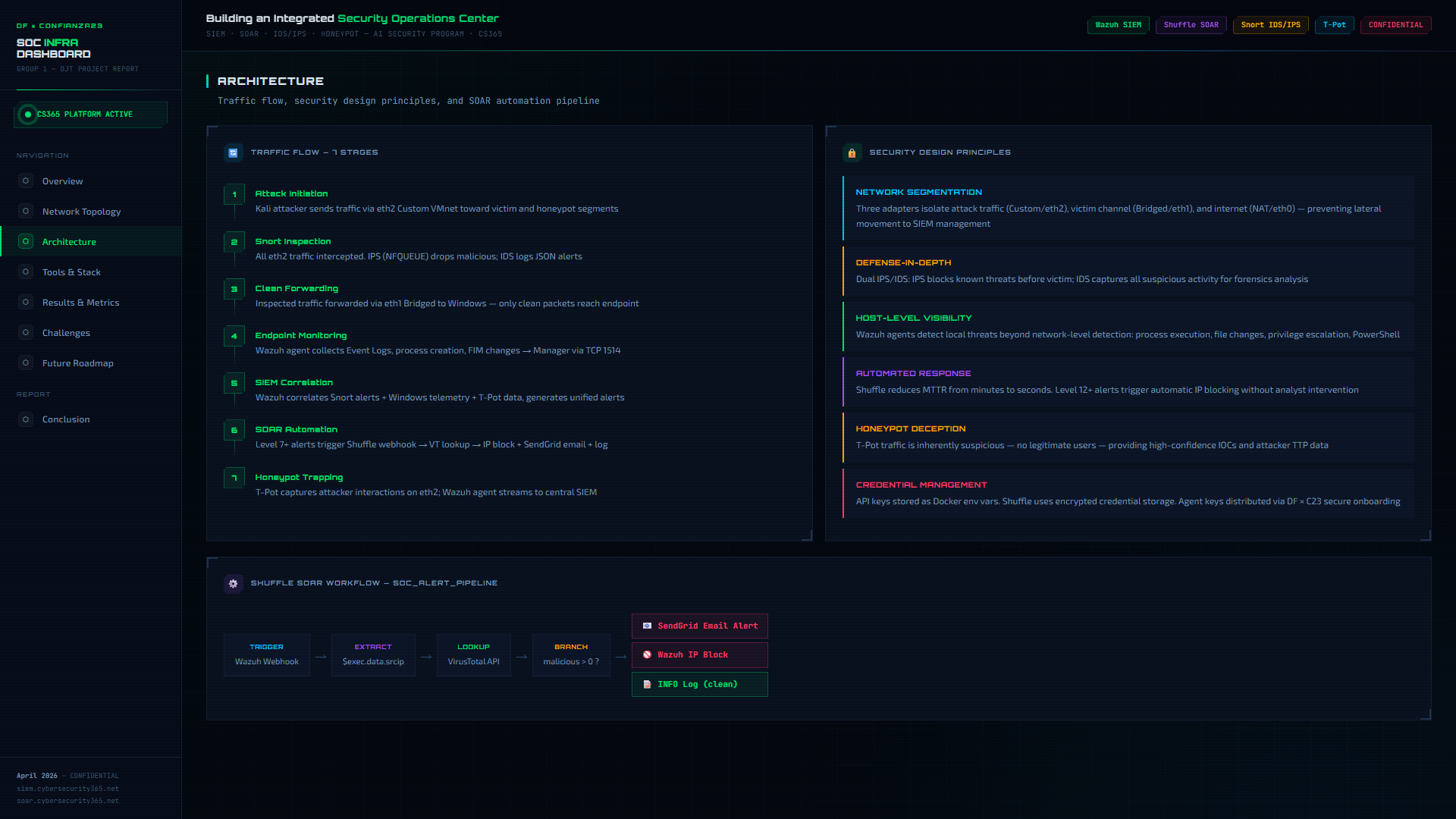
## 架构概述
```
flowchart TB
subgraph INTERNET["INTERNET"]
NET[("WAN")]
end
subgraph KALI["KALI LINUX — Gateway + Attacker"]
ETH0["eth0: NAT\n192.168.61.128"]
SNORT["Snort 3.12.1.0\nIPS: NFQUEUE drop\nIDS: alert_fast.txt"]
WAGENT1["Wazuh Agent"]
SHUFFLE["Shuffle SOAR\n:3443"]
end
subgraph INTERNAL["INTERNAL LAN — 192.168.1.0/24"]
WIN["Windows 10\n192.168.1.32\nWazuh Agent + Sysmon"]
WAZUH["Wazuh Server\n192.168.1.33\nManager + Indexer + Dashboard"]
TPOT["T-Pot Honeypot\n192.168.1.34\nWazuh Agent"]
end
subgraph EXTERNAL["EXTERNAL SERVICES"]
VT["VirusTotal API"]
SG["SendGrid Email"]
end
NET -->|NAT| ETH0
ETH0 --> SNORT
SNORT -->|"clean traffic"| WIN
SNORT -->|"attack traffic"| TPOT
SNORT -->|"alerts"| WAGENT1
WAGENT1 -->|TCP 1514| WAZUH
WIN -->|"events"| WAZUH
TPOT -->|"honeypot logs"| WAZUH
WAZUH -->|"webhook L10+"| SHUFFLE
SHUFFLE --> VT
SHUFFLE --> SG
style KALI fill:#1a1a2e,stroke:#00ff41,color:#00ff41
style INTERNAL fill:#0d1117,stroke:#58a6ff,color:#58a6ff
style SNORT fill:#ff4444,stroke:#ff4444,color:#fff
style WAZUH fill:#0066cc,stroke:#0066cc,color:#fff
style TPOT fill:#ff8800,stroke:#ff8800,color:#fff
style SHUFFLE fill:#9933ff,stroke:#9933ff,color:#fff
```
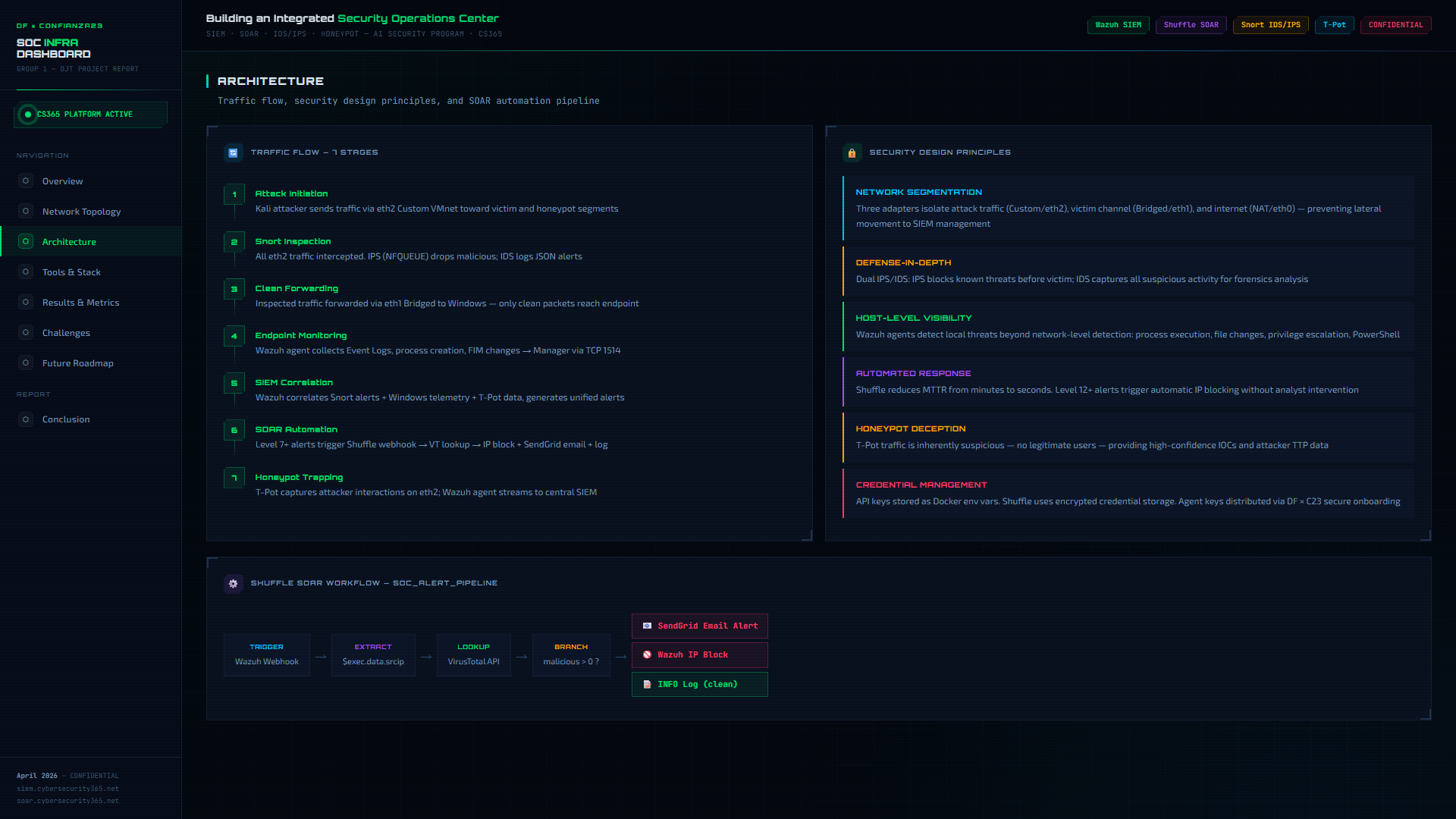 **Full architecture details:** [`architecture/README.md`](architecture/README.md)
## 网络拓扑
### IP 分配
| Machine | Interface | IP Address | Network | Role |
|:--------|:----------|:-----------|:--------|:-----|
| Kali Linux | eth0 | `192.168.61.128` | NAT | Internet egress |
| Kali Linux | eth1 | `192.168.1.31` | Bridged | Internal LAN |
| Kali Linux | eth2 | `10.94.117.59` | Bridged | Snort inspection |
| Windows 10 | eth0 | `192.168.1.32` | Bridged | Victim + Wazuh agent |
| Wazuh Server | eth0 | `192.168.1.33` | Bridged | SIEM manager |
| T-Pot | eth0 | `192.168.1.34` | Bridged | Honeypot |
| Shuffle SOAR | Docker | `10.94.117.58:3443` | — | SOAR engine |
### 网络分段
| Segment | CIDR | Purpose |
|:--------|:-----|:--------|
| NAT | `192.168.61.0/24` | Internet access for Kali only |
| Internal LAN | `192.168.1.0/24` | All agents to Wazuh manager |
| Management | `10.94.117.0/24` | Snort interface + Shuffle |
### 流量流向
```
sequenceDiagram
participant K as Kali (Attacker)
participant S as Snort IPS/IDS
participant W as Windows (Victim)
participant T as T-Pot (Honeypot)
participant M as Wazuh Manager
participant SH as Shuffle SOAR
participant VT as VirusTotal
participant E as SendGrid Email
K->>S: Attack traffic (eth2)
S--xK: IPS: DROP malicious packets
S->>W: Clean traffic forwarded (eth1)
S->>M: IDS alerts via Wazuh agent
W->>M: Endpoint events (Sysmon/Security)
T->>M: Honeypot hits via Wazuh agent
M->>SH: Level 10+ alert webhook
SH->>VT: IP reputation lookup
VT-->>SH: Malicious score
SH->>E: Alert email notification
SH->>M: IP block (active response)
```
**Full topology details:** [`topology/README.md`](topology/README.md)
## 工具与技术栈
| Tool | Version | Purpose | License |
|:-----|:--------|:--------|:--------|
| Kali Linux | 2025.4 | Attacker + gateway + Docker host | GPL |
| Snort | 3.12.1.0 | Network IDS/IPS (NFQUEUE inline) | GPL-2.0 |
| Wazuh | 4.14.4 OVA | SIEM: Manager + Indexer + Dashboard | GPL-2.0 |
| Windows 10 | 10.0.17763 | Victim endpoint | Proprietary |
| Sysmon | v15 | Enhanced Windows event logging | Free |
| T-Pot | 24.04 HIVE | Multi-honeypot platform | Apache-2.0 |
| Shuffle SOAR | Latest | Automated incident response | GPL-3.0 |
| VirusTotal API | v3 | IP reputation lookups | Free tier |
| SendGrid | v3 API | Email notifications | Free tier |
| VMware Workstation | Pro | Kali + Windows virtualization | Proprietary |
| VirtualBox | Latest | Wazuh + T-Pot virtualization | GPL-2.0 |
| Docker | Latest | Shuffle containers | Apache-2.0 |
| iptables/NFQUEUE | Kernel | Inline packet routing to Snort | GPL |
### 功能对比
| Capability | Traditional SOC | This Lab |
|:-----------|:----------------|:---------|
| Detection method | Manual log review | Automated IDS/IPS + SIEM correlation |
| Response time | Minutes to hours | **< 15 seconds** |
| Threat intel | Manual IOC lookup | Automated VirusTotal enrichment |
| Alerting | Email on schedule | Real-time webhook + email |
| Honeypot integration | Separate system | Unified in SIEM pipeline |
| Incident response | Manual playbooks | SOAR-automated workflows |
## 检测流水线
```
flowchart LR
subgraph ATTACK["ATTACK"]
A1["Nmap SYN Scan"]
A2["Hydra SSH Brute"]
A3["ICMP Sweep"]
A4["Honeypot Probe"]
end
subgraph DETECT["DETECT"]
D1["Snort IDS\nalert_fast.txt"]
D2["Snort IPS\nNFQUEUE DROP"]
D3["Sysmon\nWindows Events"]
D4["T-Pot\nJSON Logs"]
end
subgraph CORRELATE["CORRELATE"]
C1["Wazuh Manager\n192.168.1.33"]
end
subgraph RESPOND["RESPOND"]
R1["Shuffle SOAR"]
R2["VirusTotal API"]
R3["SendGrid Email"]
R4["IP Block"]
end
A1 --> D1 & D2
A2 --> D1 & D2
A3 --> D1 & D2
A4 --> D4
D1 --> C1
D3 --> C1
D4 --> C1
C1 -->|"Level 10+"| R1
R1 --> R2
R2 --> R3
R2 --> R4
style ATTACK fill:#ff4444,stroke:#ff4444,color:#fff
style DETECT fill:#ff8800,stroke:#ff8800,color:#fff
style CORRELATE fill:#0066cc,stroke:#0066cc,color:#fff
style RESPOND fill:#00cc44,stroke:#00cc44,color:#fff
```
### 自定义 Snort 规则
| SID | Type | Rule | Threshold |
|:----|:-----|:-----|:----------|
| 1000001 | IDS | ICMP Ping Sweep | 5 pings / 2 sec |
| 1000002 | IDS | Nmap SYN Port Scan | 20 SYN / 1 sec |
| 1000003 | IDS | SSH Brute Force | 5 attempts / 60 sec |
| 1000004 | IDS | HTTP Non-Standard Port (C2) | per packet |
| 1000005 | **IPS** | **Aggressive Port Scan** | **30 SYN / 5 sec** |
| 1000006 | IDS | RDP Brute Force | 5 attempts / 30 sec |
| 1000007 | **IPS** | **ICMP Flood** | **50 pings / 1 sec** |
| 1000008 | IDS | FTP Login Attempt | per packet |
| 100009 | IDS | DNS Amplification | dsize > 512 |
**Detection rules, decoders, and rule IDs:** [`detection-pipeline/README.md`](detection-pipeline/README.md)
## 自动化工作流
### Shuffle SOAR — 告警 enrichment 流水线
```
flowchart TD
A["Wazuh Alert\nLevel >= 10"] -->|webhook| B["Shuffle\nWebhook Trigger"]
B --> C["Extract src_ip\n(regex parse)"]
C --> D["VirusTotal\nIP Lookup"]
D --> E{"Malicious\nscore > 0?"}
E -->|YES| F["SendGrid\nAlert Email"]
E -->|YES| G["Wazuh\nIP Block"]
E -->|NO| H["Log: Benign\n(INFO level)"]
style A fill:#0066cc,stroke:#0066cc,color:#fff
style E fill:#ff8800,stroke:#ff8800,color:#fff
style F fill:#00cc44,stroke:#00cc44,color:#fff
style G fill:#ff4444,stroke:#ff4444,color:#fff
style H fill:#666,stroke:#666,color:#fff
```
**Trigger condition:** Wazuh alert level >= 10
**Average response time:** < 15 seconds from detection to email
**Full workflow documentation:** [`automation-workflows/shuffle-lab1.md`](automation-workflows/shuffle-lab1.md)
## 性能结果
| Metric | Result | Rating |
|:-------|:-------|:-------|
| Snort to Wazuh latency | 1-3 seconds | Excellent |
| Wazuh to Shuffle latency | 2-5 seconds | Good |
| End-to-end (attack to block) | **5-15 seconds** | Excellent |
| VirusTotal API response | 1-3 seconds | Free Tier |
| T-Pot capture rate | 100% | Excellent |
| Email delivery (SendGrid) | 3-10 seconds | Good |
| Dashboard query time | 1-2 seconds | Good |
### 验证的攻击场景
| # | Attack | Tool | IPS Response | IDS Alert | SOAR Action | Status |
|:--|:-------|:-----|:-------------|:----------|:------------|:-------|
| 1 | Port scan | `nmap -sS` | Blocked after 30 SYN/5s | Rule 1000002 | Email sent | PASS |
| 2 | SSH brute force | `hydra` | Blocked after 5 attempts | Rule 1000003 | IP blocked | PASS |
| 3 | ICMP sweep | `ping -c` | Blocked after 50/s | Rule 1000001 | Logged | PASS |
| 4 | Malicious IP probe | `curl` | N/A | Wazuh alert | VT score > 0 - email | PASS |
| 5 | Honeypot SSH | `ssh` to T-Pot | N/A | Rule 200002 | Dashboard alert | PASS |
| 6 | FIM change | File edit on Win | N/A | Sysmon EID 1 | Dashboard alert | PASS |
## 安装指南
Follow these guides in order:
| Step | Guide | Time |
|:-----|:------|:-----|
| 0 | [External Accounts Setup](installation/00-accounts-setup.md) | 15 min |
| 1 | [Kali Environment Setup](installation/01-kali-setup.md) | 20 min |
| 2 | [Snort IDS/IPS Configuration](installation/02-snort-ids-ips.md) | 30 min |
| 3 | [Wazuh Agent on Kali](installation/03-wazuh-agent-kali.md) | 20 min |
| 4 | [Windows Agent + Sysmon](installation/04-windows-agent-sysmon.md) | 25 min |
| 5 | [T-Pot Honeypot](installation/05-tpot-honeypot.md) | 60 min |
| 6 | [Shuffle SOAR Workflow](installation/06-shuffle-soar.md) | 30 min |
| 7 | [End-to-End Verification](installation/07-verification.md) | 15 min |
### 先决条件
- VMware Workstation Pro (any recent version)
- VirtualBox (latest)
- Kali Linux VM with 3 network adapters configured
- Minimum **16 GB RAM** on host machine (8 GB for T-Pot alone)
## 截图与演示
## 项目结构
```
SOC-Lab/
|
|-- README.md # You are here
|-- architecture/
| +-- README.md # Component interaction + data flow
|-- topology/
| +-- README.md # Network design + traffic flow
|-- installation/
| |-- 00-accounts-setup.md # VirusTotal + SendGrid accounts
| |-- 01-kali-setup.md # Kali network configuration
| |-- 02-snort-ids-ips.md # Snort full setup guide
| |-- 03-wazuh-agent-kali.md # Wazuh agent on Kali
| |-- 04-windows-agent-sysmon.md # Windows agent + Sysmon
| |-- 05-tpot-honeypot.md # T-Pot install guide
| |-- 06-shuffle-soar.md # Shuffle workflow build
| +-- 07-verification.md # End-to-end test checklist
|-- configurations/
| |-- snort.lua # Snort 3 main config
| |-- local.rules # Custom IDS/IPS detection rules
| |-- ossec-kali-agent.conf # Wazuh agent config (Kali)
| |-- ossec-windows-snippet.xml # Windows agent localfile blocks
| |-- tpot-decoder.xml # Custom T-Pot Wazuh decoder
| +-- tpot-rules.xml # Custom T-Pot Wazuh rules
|-- detection-pipeline/
| +-- README.md # Alert pipeline + rule reference
|-- automation-workflows/
| +-- shuffle-lab1.md # SOAR workflow documentation
|-- screenshots/
| +-- README.md # Screenshot guide + placeholders
|-- scripts/
| |-- setup-nfqueue.sh # iptables NFQUEUE setup
| +-- verify-lab.sh # Full lab health check
|-- troubleshooting/
| +-- README.md # Common errors + fixes
+-- references/
+-- README.md # All links + citations
```
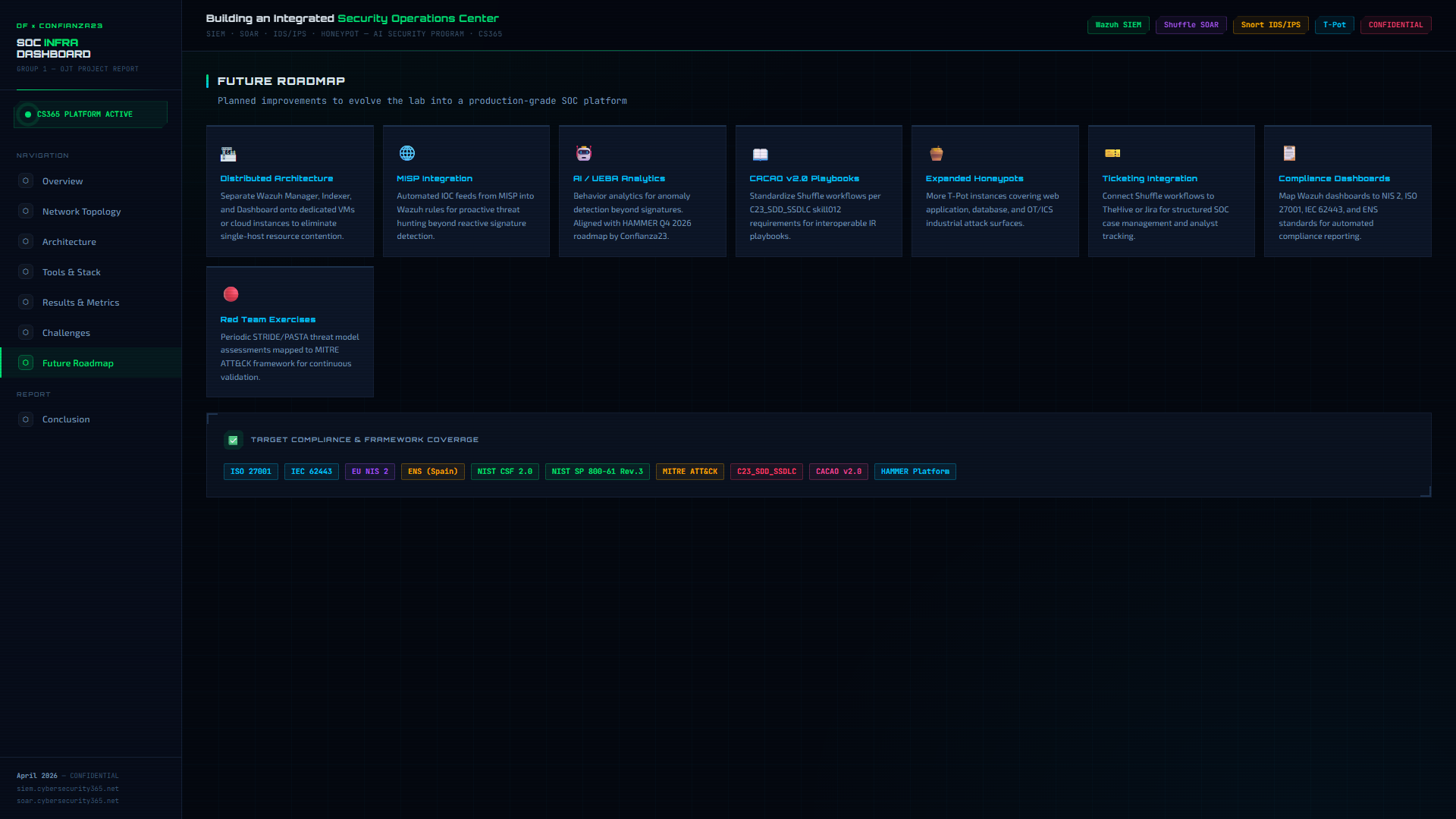
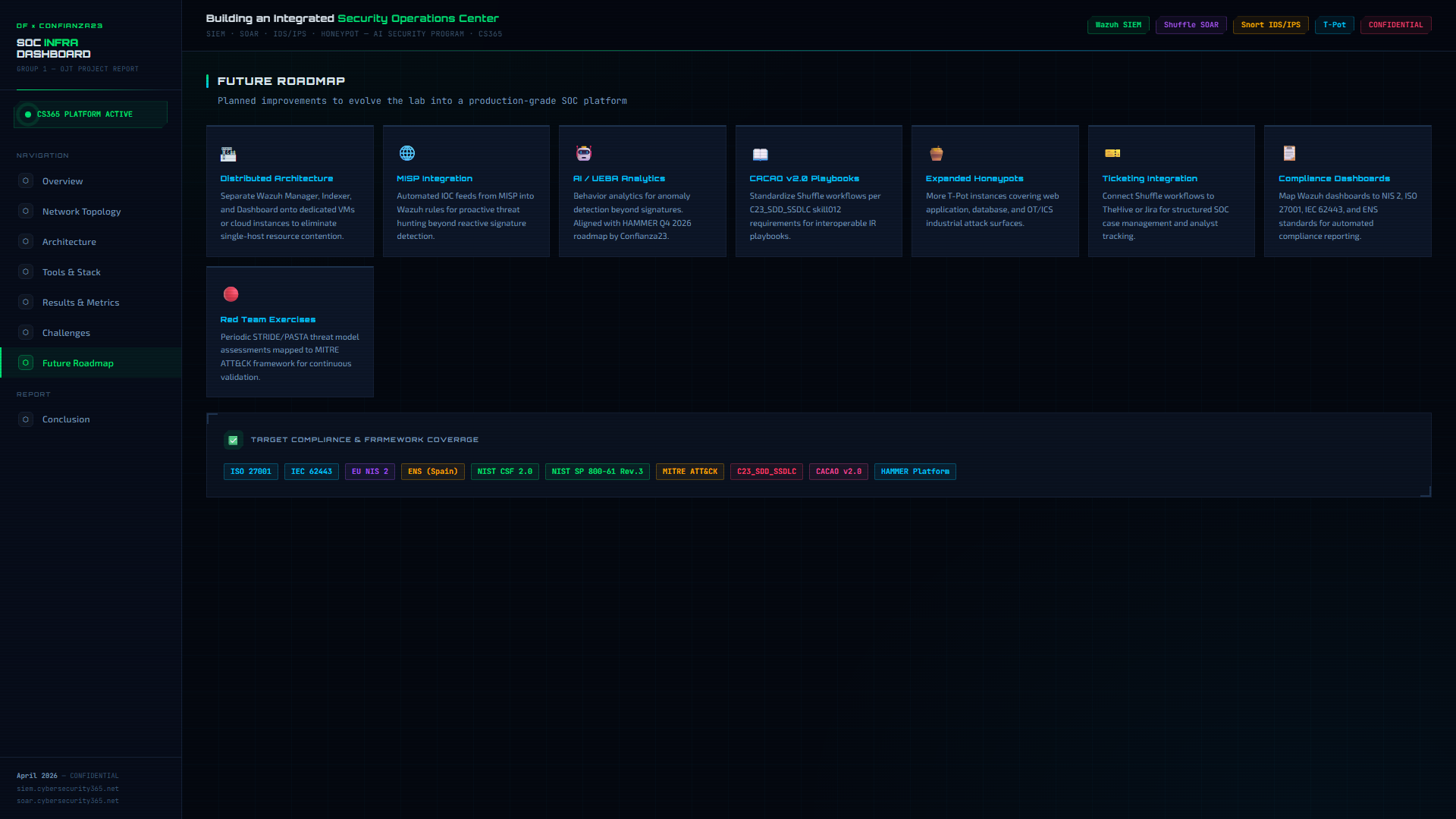
## 未来路线图
- [ ] **Distributed architecture** — separate Wazuh components onto dedicated VMs/cloud
- [ ] **MISP integration** — automated IOC feeds for proactive threat hunting
- [ ] **AI/UEBA** — behavior analytics for anomaly detection beyond signatures
- [ ] **CACAO v2.0 playbooks** — standardize Shuffle workflows
- [ ] **Expanded honeypots** — additional T-Pot instances (web, DB, OT/ICS)
- [ ] **Ticketing integration** — connect Shuffle to TheHive or Jira
- [ ] **Compliance dashboards** — map Wazuh to NIS 2, ISO 27001, IEC 62443
- [ ] **MITRE ATT&CK mapping** — tag detection rules with ATT&CK technique IDs
- [ ] **HA/clustering** — eliminate single point of failure
- [ ] **Automated rule feeds** — CI/CD for Snort + Wazuh rule deployment
**Full architecture details:** [`architecture/README.md`](architecture/README.md)
## 网络拓扑
### IP 分配
| Machine | Interface | IP Address | Network | Role |
|:--------|:----------|:-----------|:--------|:-----|
| Kali Linux | eth0 | `192.168.61.128` | NAT | Internet egress |
| Kali Linux | eth1 | `192.168.1.31` | Bridged | Internal LAN |
| Kali Linux | eth2 | `10.94.117.59` | Bridged | Snort inspection |
| Windows 10 | eth0 | `192.168.1.32` | Bridged | Victim + Wazuh agent |
| Wazuh Server | eth0 | `192.168.1.33` | Bridged | SIEM manager |
| T-Pot | eth0 | `192.168.1.34` | Bridged | Honeypot |
| Shuffle SOAR | Docker | `10.94.117.58:3443` | — | SOAR engine |
### 网络分段
| Segment | CIDR | Purpose |
|:--------|:-----|:--------|
| NAT | `192.168.61.0/24` | Internet access for Kali only |
| Internal LAN | `192.168.1.0/24` | All agents to Wazuh manager |
| Management | `10.94.117.0/24` | Snort interface + Shuffle |
### 流量流向
```
sequenceDiagram
participant K as Kali (Attacker)
participant S as Snort IPS/IDS
participant W as Windows (Victim)
participant T as T-Pot (Honeypot)
participant M as Wazuh Manager
participant SH as Shuffle SOAR
participant VT as VirusTotal
participant E as SendGrid Email
K->>S: Attack traffic (eth2)
S--xK: IPS: DROP malicious packets
S->>W: Clean traffic forwarded (eth1)
S->>M: IDS alerts via Wazuh agent
W->>M: Endpoint events (Sysmon/Security)
T->>M: Honeypot hits via Wazuh agent
M->>SH: Level 10+ alert webhook
SH->>VT: IP reputation lookup
VT-->>SH: Malicious score
SH->>E: Alert email notification
SH->>M: IP block (active response)
```
**Full topology details:** [`topology/README.md`](topology/README.md)
## 工具与技术栈
| Tool | Version | Purpose | License |
|:-----|:--------|:--------|:--------|
| Kali Linux | 2025.4 | Attacker + gateway + Docker host | GPL |
| Snort | 3.12.1.0 | Network IDS/IPS (NFQUEUE inline) | GPL-2.0 |
| Wazuh | 4.14.4 OVA | SIEM: Manager + Indexer + Dashboard | GPL-2.0 |
| Windows 10 | 10.0.17763 | Victim endpoint | Proprietary |
| Sysmon | v15 | Enhanced Windows event logging | Free |
| T-Pot | 24.04 HIVE | Multi-honeypot platform | Apache-2.0 |
| Shuffle SOAR | Latest | Automated incident response | GPL-3.0 |
| VirusTotal API | v3 | IP reputation lookups | Free tier |
| SendGrid | v3 API | Email notifications | Free tier |
| VMware Workstation | Pro | Kali + Windows virtualization | Proprietary |
| VirtualBox | Latest | Wazuh + T-Pot virtualization | GPL-2.0 |
| Docker | Latest | Shuffle containers | Apache-2.0 |
| iptables/NFQUEUE | Kernel | Inline packet routing to Snort | GPL |
### 功能对比
| Capability | Traditional SOC | This Lab |
|:-----------|:----------------|:---------|
| Detection method | Manual log review | Automated IDS/IPS + SIEM correlation |
| Response time | Minutes to hours | **< 15 seconds** |
| Threat intel | Manual IOC lookup | Automated VirusTotal enrichment |
| Alerting | Email on schedule | Real-time webhook + email |
| Honeypot integration | Separate system | Unified in SIEM pipeline |
| Incident response | Manual playbooks | SOAR-automated workflows |
## 检测流水线
```
flowchart LR
subgraph ATTACK["ATTACK"]
A1["Nmap SYN Scan"]
A2["Hydra SSH Brute"]
A3["ICMP Sweep"]
A4["Honeypot Probe"]
end
subgraph DETECT["DETECT"]
D1["Snort IDS\nalert_fast.txt"]
D2["Snort IPS\nNFQUEUE DROP"]
D3["Sysmon\nWindows Events"]
D4["T-Pot\nJSON Logs"]
end
subgraph CORRELATE["CORRELATE"]
C1["Wazuh Manager\n192.168.1.33"]
end
subgraph RESPOND["RESPOND"]
R1["Shuffle SOAR"]
R2["VirusTotal API"]
R3["SendGrid Email"]
R4["IP Block"]
end
A1 --> D1 & D2
A2 --> D1 & D2
A3 --> D1 & D2
A4 --> D4
D1 --> C1
D3 --> C1
D4 --> C1
C1 -->|"Level 10+"| R1
R1 --> R2
R2 --> R3
R2 --> R4
style ATTACK fill:#ff4444,stroke:#ff4444,color:#fff
style DETECT fill:#ff8800,stroke:#ff8800,color:#fff
style CORRELATE fill:#0066cc,stroke:#0066cc,color:#fff
style RESPOND fill:#00cc44,stroke:#00cc44,color:#fff
```
### 自定义 Snort 规则
| SID | Type | Rule | Threshold |
|:----|:-----|:-----|:----------|
| 1000001 | IDS | ICMP Ping Sweep | 5 pings / 2 sec |
| 1000002 | IDS | Nmap SYN Port Scan | 20 SYN / 1 sec |
| 1000003 | IDS | SSH Brute Force | 5 attempts / 60 sec |
| 1000004 | IDS | HTTP Non-Standard Port (C2) | per packet |
| 1000005 | **IPS** | **Aggressive Port Scan** | **30 SYN / 5 sec** |
| 1000006 | IDS | RDP Brute Force | 5 attempts / 30 sec |
| 1000007 | **IPS** | **ICMP Flood** | **50 pings / 1 sec** |
| 1000008 | IDS | FTP Login Attempt | per packet |
| 100009 | IDS | DNS Amplification | dsize > 512 |
**Detection rules, decoders, and rule IDs:** [`detection-pipeline/README.md`](detection-pipeline/README.md)
## 自动化工作流
### Shuffle SOAR — 告警 enrichment 流水线
```
flowchart TD
A["Wazuh Alert\nLevel >= 10"] -->|webhook| B["Shuffle\nWebhook Trigger"]
B --> C["Extract src_ip\n(regex parse)"]
C --> D["VirusTotal\nIP Lookup"]
D --> E{"Malicious\nscore > 0?"}
E -->|YES| F["SendGrid\nAlert Email"]
E -->|YES| G["Wazuh\nIP Block"]
E -->|NO| H["Log: Benign\n(INFO level)"]
style A fill:#0066cc,stroke:#0066cc,color:#fff
style E fill:#ff8800,stroke:#ff8800,color:#fff
style F fill:#00cc44,stroke:#00cc44,color:#fff
style G fill:#ff4444,stroke:#ff4444,color:#fff
style H fill:#666,stroke:#666,color:#fff
```
**Trigger condition:** Wazuh alert level >= 10
**Average response time:** < 15 seconds from detection to email
**Full workflow documentation:** [`automation-workflows/shuffle-lab1.md`](automation-workflows/shuffle-lab1.md)
## 性能结果
| Metric | Result | Rating |
|:-------|:-------|:-------|
| Snort to Wazuh latency | 1-3 seconds | Excellent |
| Wazuh to Shuffle latency | 2-5 seconds | Good |
| End-to-end (attack to block) | **5-15 seconds** | Excellent |
| VirusTotal API response | 1-3 seconds | Free Tier |
| T-Pot capture rate | 100% | Excellent |
| Email delivery (SendGrid) | 3-10 seconds | Good |
| Dashboard query time | 1-2 seconds | Good |
### 验证的攻击场景
| # | Attack | Tool | IPS Response | IDS Alert | SOAR Action | Status |
|:--|:-------|:-----|:-------------|:----------|:------------|:-------|
| 1 | Port scan | `nmap -sS` | Blocked after 30 SYN/5s | Rule 1000002 | Email sent | PASS |
| 2 | SSH brute force | `hydra` | Blocked after 5 attempts | Rule 1000003 | IP blocked | PASS |
| 3 | ICMP sweep | `ping -c` | Blocked after 50/s | Rule 1000001 | Logged | PASS |
| 4 | Malicious IP probe | `curl` | N/A | Wazuh alert | VT score > 0 - email | PASS |
| 5 | Honeypot SSH | `ssh` to T-Pot | N/A | Rule 200002 | Dashboard alert | PASS |
| 6 | FIM change | File edit on Win | N/A | Sysmon EID 1 | Dashboard alert | PASS |
## 安装指南
Follow these guides in order:
| Step | Guide | Time |
|:-----|:------|:-----|
| 0 | [External Accounts Setup](installation/00-accounts-setup.md) | 15 min |
| 1 | [Kali Environment Setup](installation/01-kali-setup.md) | 20 min |
| 2 | [Snort IDS/IPS Configuration](installation/02-snort-ids-ips.md) | 30 min |
| 3 | [Wazuh Agent on Kali](installation/03-wazuh-agent-kali.md) | 20 min |
| 4 | [Windows Agent + Sysmon](installation/04-windows-agent-sysmon.md) | 25 min |
| 5 | [T-Pot Honeypot](installation/05-tpot-honeypot.md) | 60 min |
| 6 | [Shuffle SOAR Workflow](installation/06-shuffle-soar.md) | 30 min |
| 7 | [End-to-End Verification](installation/07-verification.md) | 15 min |
### 先决条件
- VMware Workstation Pro (any recent version)
- VirtualBox (latest)
- Kali Linux VM with 3 network adapters configured
- Minimum **16 GB RAM** on host machine (8 GB for T-Pot alone)
## 截图与演示
## 项目结构
```
SOC-Lab/
|
|-- README.md # You are here
|-- architecture/
| +-- README.md # Component interaction + data flow
|-- topology/
| +-- README.md # Network design + traffic flow
|-- installation/
| |-- 00-accounts-setup.md # VirusTotal + SendGrid accounts
| |-- 01-kali-setup.md # Kali network configuration
| |-- 02-snort-ids-ips.md # Snort full setup guide
| |-- 03-wazuh-agent-kali.md # Wazuh agent on Kali
| |-- 04-windows-agent-sysmon.md # Windows agent + Sysmon
| |-- 05-tpot-honeypot.md # T-Pot install guide
| |-- 06-shuffle-soar.md # Shuffle workflow build
| +-- 07-verification.md # End-to-end test checklist
|-- configurations/
| |-- snort.lua # Snort 3 main config
| |-- local.rules # Custom IDS/IPS detection rules
| |-- ossec-kali-agent.conf # Wazuh agent config (Kali)
| |-- ossec-windows-snippet.xml # Windows agent localfile blocks
| |-- tpot-decoder.xml # Custom T-Pot Wazuh decoder
| +-- tpot-rules.xml # Custom T-Pot Wazuh rules
|-- detection-pipeline/
| +-- README.md # Alert pipeline + rule reference
|-- automation-workflows/
| +-- shuffle-lab1.md # SOAR workflow documentation
|-- screenshots/
| +-- README.md # Screenshot guide + placeholders
|-- scripts/
| |-- setup-nfqueue.sh # iptables NFQUEUE setup
| +-- verify-lab.sh # Full lab health check
|-- troubleshooting/
| +-- README.md # Common errors + fixes
+-- references/
+-- README.md # All links + citations
```
## 未来路线图
- [ ] **Distributed architecture** — separate Wazuh components onto dedicated VMs/cloud
- [ ] **MISP integration** — automated IOC feeds for proactive threat hunting
- [ ] **AI/UEBA** — behavior analytics for anomaly detection beyond signatures
- [ ] **CACAO v2.0 playbooks** — standardize Shuffle workflows
- [ ] **Expanded honeypots** — additional T-Pot instances (web, DB, OT/ICS)
- [ ] **Ticketing integration** — connect Shuffle to TheHive or Jira
- [ ] **Compliance dashboards** — map Wazuh to NIS 2, ISO 27001, IEC 62443
- [ ] **MITRE ATT&CK mapping** — tag detection rules with ATT&CK technique IDs
- [ ] **HA/clustering** — eliminate single point of failure
- [ ] **Automated rule feeds** — CI/CD for Snort + Wazuh rule deployment
 ## 参考
| Resource | URL |
|:---------|:----|
| Wazuh Documentation | https://documentation.wazuh.com |
| Snort 3 Documentation | https://docs.snort.org |
| Shuffle SOAR | https://shuffler.io/docs |
| T-Pot GitHub | https://github.com/telekom-security/tpotce |
| VirusTotal API v3 | https://developers.virustotal.com/reference |
| NIST CSF 2.0 | https://www.nist.gov/cyberframework |
| MITRE ATT&CK | https://attack.mitre.org |
| NIST SP 800-61 Rev. 3 | https://csrc.nist.gov/publications/detail/sp/800-61/rev-3/final |
Full references: [`references/README.md`](references/README.md)
## 参考
| Resource | URL |
|:---------|:----|
| Wazuh Documentation | https://documentation.wazuh.com |
| Snort 3 Documentation | https://docs.snort.org |
| Shuffle SOAR | https://shuffler.io/docs |
| T-Pot GitHub | https://github.com/telekom-security/tpotce |
| VirusTotal API v3 | https://developers.virustotal.com/reference |
| NIST CSF 2.0 | https://www.nist.gov/cyberframework |
| MITRE ATT&CK | https://attack.mitre.org |
| NIST SP 800-61 Rev. 3 | https://csrc.nist.gov/publications/detail/sp/800-61/rev-3/final |
Full references: [`references/README.md`](references/README.md)
SOC Mini-Lab — Integrated Security Operations Center
## 目录 - [Highlights](#-highlights) - [Architecture Overview](#-architecture-overview) - [Network Topology](#-network-topology) - [Tools Used](#-tools--technology-stack) - [Detection Pipeline](#-detection-pipeline) - [Automation Workflow](#-automation-workflow) - [Performance Results](#-performance-results) - [Installation](#-installation-guide) - [Screenshots](#-screenshots--demo) - [Project Structure](#-project-structure) - [Future Improvements](#-future-roadmap) - [References](#-references) ## 亮点
5Core ComponentsWazuh • Snort • Shuffle • T-Pot • Sysmon |
<15sAttack to BlockEnd-to-end automated response |
3Active AgentsKali + Windows + T-Pot |
6/6Tests Passed100% detection rate |
View Architecture Dashboard Screenshot
View Future Roadmap Dashboard
Built as a SOC prototype. Open-source tools, production-representative architecture.
Security Framework: NIST Cybersecurity Framework 2.0 — Detect, Respond, Recover
标签:5-15秒, FTP漏洞扫描, GPL-2.0, NIST CSF, Shuffle SOAR, Snort IDS, Snort IPS, SOC 工具栈, T-Pot 蜜罐, Wazuh SIEM, 全场景 SOC, 后端开发, 告警响应, 安全可视化, 安全演练, 安全编排, 安全运营, 扫描框架, 攻击场景, 检测与阻断, 流量监控, 自动化响应, 蜜罐诱捕, 请求拦截, 迷你实验室