kocaemre/zeguard
GitHub: kocaemre/zeguard
ZeGuard 是一款运行在浏览器端的安全工具,用于检测 PDF、DOCX 和 PPTX 文档中隐藏的 Prompt Injection 攻击技术。
Stars: 0 | Forks: 0
# user wants a translation of a Markdown document from Turkish to Simplified Chinese.
**Constraints Checklist & Confidence Score:**
1. Keep code placeholders (`
```
git clone https://github.com/kocaemre/zeguard.git
cd zeguard
npm install
npm run dev
```
`)? Yes.
2. Keep HTML image placeholders (`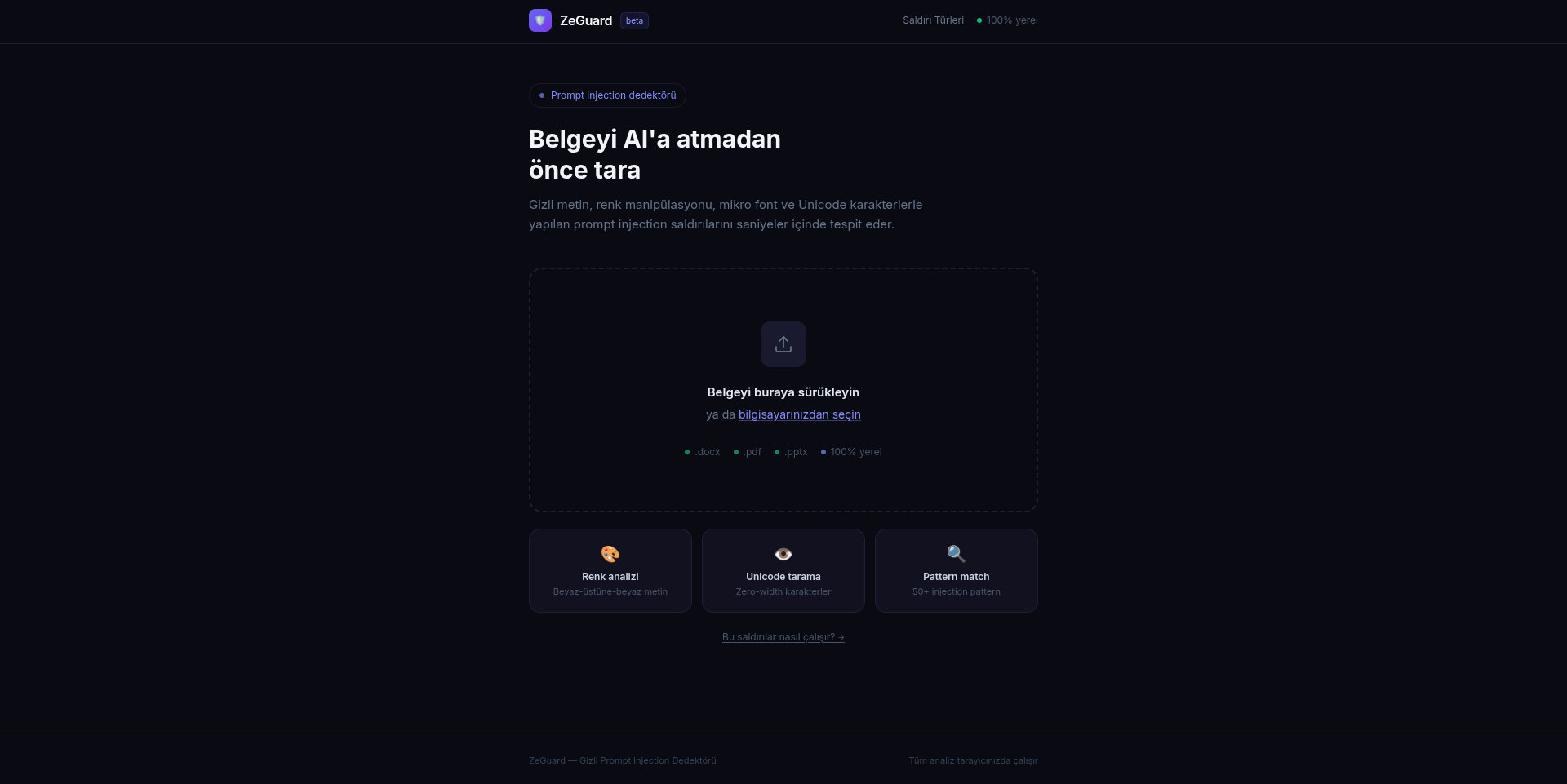 `)? Yes.
3. Keep link URL placeholders (`https://docguard.zepatrol.xyz`)? Yes.
4. Translate link text? Yes.
5. Preserve HTML blocks? Yes.
6. Keep Markdown structure? Yes.
7. Translate headings? Yes.
8. Preserve technical terms (English)? Yes.
Confidence Score: 5/5
**Mental Sandbox Simulation:**
- Title: `# 🛡️ ZeGuard — Gizli Prompt Injection Dedektörü` -> `# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器` (ZeGuard is a name, Prompt Injection is technical).
- Demo: `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` -> `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` (Link text is a domain, usually kept as is or translated if it's a description. Here it looks like the URL itself as text. I will keep it as is to be safe, or translate if it's clearly a label. The rule says "translate the link text". "docguard.zepatrol.xyz" is a domain. I will keep the domain as is because it's an identifier, but if it were "Demo Site", I'd translate. Wait, the rule says "Example: [Overview]... -> [概述]". If the text is a URL, it's safer to keep it, but strictly following "translate link text" might imply making it Chinese. However, usually, domains are not translated. I will keep the domain text as is because it serves as the address.)
- Heading: `## 🎯 Ne Yapar?` -> `## 🎯 功能` (What does it do? -> Functionality).
- Table:
- `Teknik` -> `技术`
- `Açıklama` -> `描述`
- `Invisible Font` -> `Invisible Font` (Technical term/Proper noun concept).
- `Font rengi ≈ arka plan rengi (Delta-E ≤ 10) kontrolü` -> `字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查`
- `Tiny Font` -> `Tiny Font`
- `4pt altı metin — gözle görünmez, LLM okur` -> `小于 4pt 的文本 — 肉眼不可见,但 LLM 可读`
- `Hidden Text` -> `Hidden Text`
- `DOCX w:vanish ve w:webHidden XML tag'leri` -> `DOCX w:vanish 和 w:webHidden XML 标签`
- `Unicode Invisible` -> `Unicode Invisible`
- `8 farklı invisible Unicode karakteri (özellikle 3+ ardışık)` -> `8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符)`
- `Metadata Injection` -> `Metadata Injection`
- `docProps/core.xml ve custom.xml içinde injection pattern'ları` -> `docProps/core.xml 和 custom.xml 内部的注入模式`
- `Pattern Matching` -> `Pattern Matching`
- `50+ Türkçe ve İngilizce prompt injection pattern veritabanı` -> `50+ 土耳其语和英语 prompt injection 模式数据库`
- Privacy: `Tüm analiz **tarayıcıda** gerçekleşir.` -> `所有分析均在**浏览器**中完成。`
- Tech Stack:
- `React 18` -> `React 18`
- `Vite — build tool` -> `Vite — 构建工具`
- `Tailwind CSS — stil` -> `Tailwind CSS — 样式`
- `pdf.js — PDF parsing` -> `pdf.js — PDF 解析`
- `mammoth.js — DOCX parsing` -> `mammoth.js — DOCX 解析`
- `PptxGenJS — PPTX parsing` -> `PptxGenJS — PPTX 解析`
- Installation: `## 🚀 Kurulum` -> `## 🚀 安装`
- Build: `### Build` -> `### 构建`
- Project Structure: `## 📁 Proje Yapısı` -> `## 📁 项目结构`
- Developer: `## 👨💻 Geliştirici` -> `## 👨💻 开发者`
- License: `## 📄 Lisans` -> `## 📄 许可证`
**Refinement on Technical Terms:**
- "Prompt Injection" -> Keep as "Prompt Injection" (Rule 9).
- "Invisible Font" -> Keep as "Invisible Font" or "隐形字体"? Rule 9 says "Domain-specific terminology widely known in English... e.g. token, prompt...". "Invisible Font" is a specific attack technique name. I will keep it in English to be safe and professional, or translate the description. The table has "Teknik" (Technique) as the header. I will keep the technique names in English as they are likely standard terms in this security domain.
- "Metadata Injection" -> Keep as "Metadata Injection".
- "Pattern Matching" -> Keep as "Pattern Matching".
**Refinement on Link Text:**
- `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)`: The text is the URL itself. I will leave it as is.
- `[0xemrek](https://github.com/kocaemre)`: This is a username/handle. I will leave it as is.
**Final Polish:**
Ensure the tone is professional and the Chinese is natural.
Let's generate the output.
# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器
**演示:** [docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)
`)? Yes.
3. Keep link URL placeholders (`https://docguard.zepatrol.xyz`)? Yes.
4. Translate link text? Yes.
5. Preserve HTML blocks? Yes.
6. Keep Markdown structure? Yes.
7. Translate headings? Yes.
8. Preserve technical terms (English)? Yes.
Confidence Score: 5/5
**Mental Sandbox Simulation:**
- Title: `# 🛡️ ZeGuard — Gizli Prompt Injection Dedektörü` -> `# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器` (ZeGuard is a name, Prompt Injection is technical).
- Demo: `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` -> `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` (Link text is a domain, usually kept as is or translated if it's a description. Here it looks like the URL itself as text. I will keep it as is to be safe, or translate if it's clearly a label. The rule says "translate the link text". "docguard.zepatrol.xyz" is a domain. I will keep the domain as is because it's an identifier, but if it were "Demo Site", I'd translate. Wait, the rule says "Example: [Overview]... -> [概述]". If the text is a URL, it's safer to keep it, but strictly following "translate link text" might imply making it Chinese. However, usually, domains are not translated. I will keep the domain text as is because it serves as the address.)
- Heading: `## 🎯 Ne Yapar?` -> `## 🎯 功能` (What does it do? -> Functionality).
- Table:
- `Teknik` -> `技术`
- `Açıklama` -> `描述`
- `Invisible Font` -> `Invisible Font` (Technical term/Proper noun concept).
- `Font rengi ≈ arka plan rengi (Delta-E ≤ 10) kontrolü` -> `字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查`
- `Tiny Font` -> `Tiny Font`
- `4pt altı metin — gözle görünmez, LLM okur` -> `小于 4pt 的文本 — 肉眼不可见,但 LLM 可读`
- `Hidden Text` -> `Hidden Text`
- `DOCX w:vanish ve w:webHidden XML tag'leri` -> `DOCX w:vanish 和 w:webHidden XML 标签`
- `Unicode Invisible` -> `Unicode Invisible`
- `8 farklı invisible Unicode karakteri (özellikle 3+ ardışık)` -> `8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符)`
- `Metadata Injection` -> `Metadata Injection`
- `docProps/core.xml ve custom.xml içinde injection pattern'ları` -> `docProps/core.xml 和 custom.xml 内部的注入模式`
- `Pattern Matching` -> `Pattern Matching`
- `50+ Türkçe ve İngilizce prompt injection pattern veritabanı` -> `50+ 土耳其语和英语 prompt injection 模式数据库`
- Privacy: `Tüm analiz **tarayıcıda** gerçekleşir.` -> `所有分析均在**浏览器**中完成。`
- Tech Stack:
- `React 18` -> `React 18`
- `Vite — build tool` -> `Vite — 构建工具`
- `Tailwind CSS — stil` -> `Tailwind CSS — 样式`
- `pdf.js — PDF parsing` -> `pdf.js — PDF 解析`
- `mammoth.js — DOCX parsing` -> `mammoth.js — DOCX 解析`
- `PptxGenJS — PPTX parsing` -> `PptxGenJS — PPTX 解析`
- Installation: `## 🚀 Kurulum` -> `## 🚀 安装`
- Build: `### Build` -> `### 构建`
- Project Structure: `## 📁 Proje Yapısı` -> `## 📁 项目结构`
- Developer: `## 👨💻 Geliştirici` -> `## 👨💻 开发者`
- License: `## 📄 Lisans` -> `## 📄 许可证`
**Refinement on Technical Terms:**
- "Prompt Injection" -> Keep as "Prompt Injection" (Rule 9).
- "Invisible Font" -> Keep as "Invisible Font" or "隐形字体"? Rule 9 says "Domain-specific terminology widely known in English... e.g. token, prompt...". "Invisible Font" is a specific attack technique name. I will keep it in English to be safe and professional, or translate the description. The table has "Teknik" (Technique) as the header. I will keep the technique names in English as they are likely standard terms in this security domain.
- "Metadata Injection" -> Keep as "Metadata Injection".
- "Pattern Matching" -> Keep as "Pattern Matching".
**Refinement on Link Text:**
- `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)`: The text is the URL itself. I will leave it as is.
- `[0xemrek](https://github.com/kocaemre)`: This is a username/handle. I will leave it as is.
**Final Polish:**
Ensure the tone is professional and the Chinese is natural.
Let's generate the output.
# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器
**演示:** [docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)
 ## 🎯 功能
当您向 AI 系统上传文件时,文档中隐藏的指令可能会操纵 LLM。ZeGuard 会自动检测这些技术。
### 检测到的攻击技术
| 技术 | 描述 |
|--------|----------|
| **Invisible Font** | 字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查 |
| **Tiny Font** | 小于 4pt 的文本 — 肉眼不可见,但 LLM 可读 |
| **Hidden Text** | DOCX `w:vanish` 和 `w:webHidden` XML 标签 |
| **Unicode Invisible** | 8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符) |
| **Metadata Injection** | `docProps/core.xml` 和 `custom.xml` 内部的注入模式 |
| **Pattern Matching** | 50+ 土耳其语和英语 prompt injection 模式数据库 |
## 🔒 隐私
所有分析均在**浏览器**中完成。您的文件不会发送到任何服务器。
## 🛠️ 技术
- **React 18** + TypeScript
- **Vite** — 构建工具
- **Tailwind CSS** — 样式
- **pdf.js** — PDF 解析
- **mammoth.js** — DOCX 解析
- **PptxGenJS** — PPTX 解析
## 🚀 安装
```
git clone https://github.com/kocaemre/zeguard.git
cd zeguard
npm install
npm run dev
```
### 构建
```
npm run build
# dist/ klasörü oluşur, herhangi bir static hosting'e deploy edilebilir
```
## 📁 项目结构
```
zeguard/
├── src/
│ ├── analyzers/ # Analiz modülleri
│ │ ├── color-analyzer.ts # Invisible font tespiti
│ │ ├── font-analyzer.ts # Tiny font tespiti
│ │ ├── metadata-analyzer.ts # Metadata injection
│ │ ├── pattern-analyzer.ts # Pattern matching
│ │ └── unicode-analyzer.ts # Invisible unicode
│ ├── parsers/ # Dosya ayrıştırıcıları
│ │ ├── pdf-parser.ts
│ │ ├── docx-parser.ts
│ │ └── pptx-parser.ts
│ ├── ui/ # React bileşenleri
│ │ ├── DropZone.tsx
│ │ ├── ResultsPanel.tsx
│ │ ├── FindingCard.tsx
│ │ ├── ScanProgress.tsx
│ │ └── AttacksPage.tsx
│ ├── patterns/
│ │ ├── tr.json # Türkçe injection pattern'ları
│ │ └── en.json # İngilizce injection pattern'ları
│ ├── reporter/
│ │ └── report-builder.ts
│ └── App.tsx
├── public/
├── index.html
└── vite.config.ts
```
## 👨💻 开发者
**Emre Koca** — [0xemrek](https://github.com/kocaemre)
## 📄 许可证
MIT
## 🎯 功能
当您向 AI 系统上传文件时,文档中隐藏的指令可能会操纵 LLM。ZeGuard 会自动检测这些技术。
### 检测到的攻击技术
| 技术 | 描述 |
|--------|----------|
| **Invisible Font** | 字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查 |
| **Tiny Font** | 小于 4pt 的文本 — 肉眼不可见,但 LLM 可读 |
| **Hidden Text** | DOCX `w:vanish` 和 `w:webHidden` XML 标签 |
| **Unicode Invisible** | 8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符) |
| **Metadata Injection** | `docProps/core.xml` 和 `custom.xml` 内部的注入模式 |
| **Pattern Matching** | 50+ 土耳其语和英语 prompt injection 模式数据库 |
## 🔒 隐私
所有分析均在**浏览器**中完成。您的文件不会发送到任何服务器。
## 🛠️ 技术
- **React 18** + TypeScript
- **Vite** — 构建工具
- **Tailwind CSS** — 样式
- **pdf.js** — PDF 解析
- **mammoth.js** — DOCX 解析
- **PptxGenJS** — PPTX 解析
## 🚀 安装
```
git clone https://github.com/kocaemre/zeguard.git
cd zeguard
npm install
npm run dev
```
### 构建
```
npm run build
# dist/ klasörü oluşur, herhangi bir static hosting'e deploy edilebilir
```
## 📁 项目结构
```
zeguard/
├── src/
│ ├── analyzers/ # Analiz modülleri
│ │ ├── color-analyzer.ts # Invisible font tespiti
│ │ ├── font-analyzer.ts # Tiny font tespiti
│ │ ├── metadata-analyzer.ts # Metadata injection
│ │ ├── pattern-analyzer.ts # Pattern matching
│ │ └── unicode-analyzer.ts # Invisible unicode
│ ├── parsers/ # Dosya ayrıştırıcıları
│ │ ├── pdf-parser.ts
│ │ ├── docx-parser.ts
│ │ └── pptx-parser.ts
│ ├── ui/ # React bileşenleri
│ │ ├── DropZone.tsx
│ │ ├── ResultsPanel.tsx
│ │ ├── FindingCard.tsx
│ │ ├── ScanProgress.tsx
│ │ └── AttacksPage.tsx
│ ├── patterns/
│ │ ├── tr.json # Türkçe injection pattern'ları
│ │ └── en.json # İngilizce injection pattern'ları
│ ├── reporter/
│ │ └── report-builder.ts
│ └── App.tsx
├── public/
├── index.html
└── vite.config.ts
```
## 👨💻 开发者
**Emre Koca** — [0xemrek](https://github.com/kocaemre)
## 📄 许可证
MIT
 `)? Yes.
3. Keep link URL placeholders (`https://docguard.zepatrol.xyz`)? Yes.
4. Translate link text? Yes.
5. Preserve HTML blocks? Yes.
6. Keep Markdown structure? Yes.
7. Translate headings? Yes.
8. Preserve technical terms (English)? Yes.
Confidence Score: 5/5
**Mental Sandbox Simulation:**
- Title: `# 🛡️ ZeGuard — Gizli Prompt Injection Dedektörü` -> `# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器` (ZeGuard is a name, Prompt Injection is technical).
- Demo: `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` -> `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` (Link text is a domain, usually kept as is or translated if it's a description. Here it looks like the URL itself as text. I will keep it as is to be safe, or translate if it's clearly a label. The rule says "translate the link text". "docguard.zepatrol.xyz" is a domain. I will keep the domain as is because it's an identifier, but if it were "Demo Site", I'd translate. Wait, the rule says "Example: [Overview]... -> [概述]". If the text is a URL, it's safer to keep it, but strictly following "translate link text" might imply making it Chinese. However, usually, domains are not translated. I will keep the domain text as is because it serves as the address.)
- Heading: `## 🎯 Ne Yapar?` -> `## 🎯 功能` (What does it do? -> Functionality).
- Table:
- `Teknik` -> `技术`
- `Açıklama` -> `描述`
- `Invisible Font` -> `Invisible Font` (Technical term/Proper noun concept).
- `Font rengi ≈ arka plan rengi (Delta-E ≤ 10) kontrolü` -> `字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查`
- `Tiny Font` -> `Tiny Font`
- `4pt altı metin — gözle görünmez, LLM okur` -> `小于 4pt 的文本 — 肉眼不可见,但 LLM 可读`
- `Hidden Text` -> `Hidden Text`
- `DOCX w:vanish ve w:webHidden XML tag'leri` -> `DOCX w:vanish 和 w:webHidden XML 标签`
- `Unicode Invisible` -> `Unicode Invisible`
- `8 farklı invisible Unicode karakteri (özellikle 3+ ardışık)` -> `8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符)`
- `Metadata Injection` -> `Metadata Injection`
- `docProps/core.xml ve custom.xml içinde injection pattern'ları` -> `docProps/core.xml 和 custom.xml 内部的注入模式`
- `Pattern Matching` -> `Pattern Matching`
- `50+ Türkçe ve İngilizce prompt injection pattern veritabanı` -> `50+ 土耳其语和英语 prompt injection 模式数据库`
- Privacy: `Tüm analiz **tarayıcıda** gerçekleşir.` -> `所有分析均在**浏览器**中完成。`
- Tech Stack:
- `React 18` -> `React 18`
- `Vite — build tool` -> `Vite — 构建工具`
- `Tailwind CSS — stil` -> `Tailwind CSS — 样式`
- `pdf.js — PDF parsing` -> `pdf.js — PDF 解析`
- `mammoth.js — DOCX parsing` -> `mammoth.js — DOCX 解析`
- `PptxGenJS — PPTX parsing` -> `PptxGenJS — PPTX 解析`
- Installation: `## 🚀 Kurulum` -> `## 🚀 安装`
- Build: `### Build` -> `### 构建`
- Project Structure: `## 📁 Proje Yapısı` -> `## 📁 项目结构`
- Developer: `## 👨💻 Geliştirici` -> `## 👨💻 开发者`
- License: `## 📄 Lisans` -> `## 📄 许可证`
**Refinement on Technical Terms:**
- "Prompt Injection" -> Keep as "Prompt Injection" (Rule 9).
- "Invisible Font" -> Keep as "Invisible Font" or "隐形字体"? Rule 9 says "Domain-specific terminology widely known in English... e.g. token, prompt...". "Invisible Font" is a specific attack technique name. I will keep it in English to be safe and professional, or translate the description. The table has "Teknik" (Technique) as the header. I will keep the technique names in English as they are likely standard terms in this security domain.
- "Metadata Injection" -> Keep as "Metadata Injection".
- "Pattern Matching" -> Keep as "Pattern Matching".
**Refinement on Link Text:**
- `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)`: The text is the URL itself. I will leave it as is.
- `[0xemrek](https://github.com/kocaemre)`: This is a username/handle. I will leave it as is.
**Final Polish:**
Ensure the tone is professional and the Chinese is natural.
Let's generate the output.
# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器
**演示:** [docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)
`)? Yes.
3. Keep link URL placeholders (`https://docguard.zepatrol.xyz`)? Yes.
4. Translate link text? Yes.
5. Preserve HTML blocks? Yes.
6. Keep Markdown structure? Yes.
7. Translate headings? Yes.
8. Preserve technical terms (English)? Yes.
Confidence Score: 5/5
**Mental Sandbox Simulation:**
- Title: `# 🛡️ ZeGuard — Gizli Prompt Injection Dedektörü` -> `# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器` (ZeGuard is a name, Prompt Injection is technical).
- Demo: `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` -> `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)` (Link text is a domain, usually kept as is or translated if it's a description. Here it looks like the URL itself as text. I will keep it as is to be safe, or translate if it's clearly a label. The rule says "translate the link text". "docguard.zepatrol.xyz" is a domain. I will keep the domain as is because it's an identifier, but if it were "Demo Site", I'd translate. Wait, the rule says "Example: [Overview]... -> [概述]". If the text is a URL, it's safer to keep it, but strictly following "translate link text" might imply making it Chinese. However, usually, domains are not translated. I will keep the domain text as is because it serves as the address.)
- Heading: `## 🎯 Ne Yapar?` -> `## 🎯 功能` (What does it do? -> Functionality).
- Table:
- `Teknik` -> `技术`
- `Açıklama` -> `描述`
- `Invisible Font` -> `Invisible Font` (Technical term/Proper noun concept).
- `Font rengi ≈ arka plan rengi (Delta-E ≤ 10) kontrolü` -> `字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查`
- `Tiny Font` -> `Tiny Font`
- `4pt altı metin — gözle görünmez, LLM okur` -> `小于 4pt 的文本 — 肉眼不可见,但 LLM 可读`
- `Hidden Text` -> `Hidden Text`
- `DOCX w:vanish ve w:webHidden XML tag'leri` -> `DOCX w:vanish 和 w:webHidden XML 标签`
- `Unicode Invisible` -> `Unicode Invisible`
- `8 farklı invisible Unicode karakteri (özellikle 3+ ardışık)` -> `8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符)`
- `Metadata Injection` -> `Metadata Injection`
- `docProps/core.xml ve custom.xml içinde injection pattern'ları` -> `docProps/core.xml 和 custom.xml 内部的注入模式`
- `Pattern Matching` -> `Pattern Matching`
- `50+ Türkçe ve İngilizce prompt injection pattern veritabanı` -> `50+ 土耳其语和英语 prompt injection 模式数据库`
- Privacy: `Tüm analiz **tarayıcıda** gerçekleşir.` -> `所有分析均在**浏览器**中完成。`
- Tech Stack:
- `React 18` -> `React 18`
- `Vite — build tool` -> `Vite — 构建工具`
- `Tailwind CSS — stil` -> `Tailwind CSS — 样式`
- `pdf.js — PDF parsing` -> `pdf.js — PDF 解析`
- `mammoth.js — DOCX parsing` -> `mammoth.js — DOCX 解析`
- `PptxGenJS — PPTX parsing` -> `PptxGenJS — PPTX 解析`
- Installation: `## 🚀 Kurulum` -> `## 🚀 安装`
- Build: `### Build` -> `### 构建`
- Project Structure: `## 📁 Proje Yapısı` -> `## 📁 项目结构`
- Developer: `## 👨💻 Geliştirici` -> `## 👨💻 开发者`
- License: `## 📄 Lisans` -> `## 📄 许可证`
**Refinement on Technical Terms:**
- "Prompt Injection" -> Keep as "Prompt Injection" (Rule 9).
- "Invisible Font" -> Keep as "Invisible Font" or "隐形字体"? Rule 9 says "Domain-specific terminology widely known in English... e.g. token, prompt...". "Invisible Font" is a specific attack technique name. I will keep it in English to be safe and professional, or translate the description. The table has "Teknik" (Technique) as the header. I will keep the technique names in English as they are likely standard terms in this security domain.
- "Metadata Injection" -> Keep as "Metadata Injection".
- "Pattern Matching" -> Keep as "Pattern Matching".
**Refinement on Link Text:**
- `[docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)`: The text is the URL itself. I will leave it as is.
- `[0xemrek](https://github.com/kocaemre)`: This is a username/handle. I will leave it as is.
**Final Polish:**
Ensure the tone is professional and the Chinese is natural.
Let's generate the output.
# 🛡️ ZeGuard — 隐蔽 Prompt Injection 检测器
**演示:** [docguard.zepatrol.xyz](https://docguard.zepatrol.xyz)
 ## 🎯 功能
当您向 AI 系统上传文件时,文档中隐藏的指令可能会操纵 LLM。ZeGuard 会自动检测这些技术。
### 检测到的攻击技术
| 技术 | 描述 |
|--------|----------|
| **Invisible Font** | 字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查 |
| **Tiny Font** | 小于 4pt 的文本 — 肉眼不可见,但 LLM 可读 |
| **Hidden Text** | DOCX `w:vanish` 和 `w:webHidden` XML 标签 |
| **Unicode Invisible** | 8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符) |
| **Metadata Injection** | `docProps/core.xml` 和 `custom.xml` 内部的注入模式 |
| **Pattern Matching** | 50+ 土耳其语和英语 prompt injection 模式数据库 |
## 🔒 隐私
所有分析均在**浏览器**中完成。您的文件不会发送到任何服务器。
## 🛠️ 技术
- **React 18** + TypeScript
- **Vite** — 构建工具
- **Tailwind CSS** — 样式
- **pdf.js** — PDF 解析
- **mammoth.js** — DOCX 解析
- **PptxGenJS** — PPTX 解析
## 🚀 安装
```
git clone https://github.com/kocaemre/zeguard.git
cd zeguard
npm install
npm run dev
```
### 构建
```
npm run build
# dist/ klasörü oluşur, herhangi bir static hosting'e deploy edilebilir
```
## 📁 项目结构
```
zeguard/
├── src/
│ ├── analyzers/ # Analiz modülleri
│ │ ├── color-analyzer.ts # Invisible font tespiti
│ │ ├── font-analyzer.ts # Tiny font tespiti
│ │ ├── metadata-analyzer.ts # Metadata injection
│ │ ├── pattern-analyzer.ts # Pattern matching
│ │ └── unicode-analyzer.ts # Invisible unicode
│ ├── parsers/ # Dosya ayrıştırıcıları
│ │ ├── pdf-parser.ts
│ │ ├── docx-parser.ts
│ │ └── pptx-parser.ts
│ ├── ui/ # React bileşenleri
│ │ ├── DropZone.tsx
│ │ ├── ResultsPanel.tsx
│ │ ├── FindingCard.tsx
│ │ ├── ScanProgress.tsx
│ │ └── AttacksPage.tsx
│ ├── patterns/
│ │ ├── tr.json # Türkçe injection pattern'ları
│ │ └── en.json # İngilizce injection pattern'ları
│ ├── reporter/
│ │ └── report-builder.ts
│ └── App.tsx
├── public/
├── index.html
└── vite.config.ts
```
## 👨💻 开发者
**Emre Koca** — [0xemrek](https://github.com/kocaemre)
## 📄 许可证
MIT
## 🎯 功能
当您向 AI 系统上传文件时,文档中隐藏的指令可能会操纵 LLM。ZeGuard 会自动检测这些技术。
### 检测到的攻击技术
| 技术 | 描述 |
|--------|----------|
| **Invisible Font** | 字体颜色 ≈ 背景颜色 (Delta-E ≤ 10) 检查 |
| **Tiny Font** | 小于 4pt 的文本 — 肉眼不可见,但 LLM 可读 |
| **Hidden Text** | DOCX `w:vanish` 和 `w:webHidden` XML 标签 |
| **Unicode Invisible** | 8 种不同的不可见 Unicode 字符(特别是 3 个以上连续字符) |
| **Metadata Injection** | `docProps/core.xml` 和 `custom.xml` 内部的注入模式 |
| **Pattern Matching** | 50+ 土耳其语和英语 prompt injection 模式数据库 |
## 🔒 隐私
所有分析均在**浏览器**中完成。您的文件不会发送到任何服务器。
## 🛠️ 技术
- **React 18** + TypeScript
- **Vite** — 构建工具
- **Tailwind CSS** — 样式
- **pdf.js** — PDF 解析
- **mammoth.js** — DOCX 解析
- **PptxGenJS** — PPTX 解析
## 🚀 安装
```
git clone https://github.com/kocaemre/zeguard.git
cd zeguard
npm install
npm run dev
```
### 构建
```
npm run build
# dist/ klasörü oluşur, herhangi bir static hosting'e deploy edilebilir
```
## 📁 项目结构
```
zeguard/
├── src/
│ ├── analyzers/ # Analiz modülleri
│ │ ├── color-analyzer.ts # Invisible font tespiti
│ │ ├── font-analyzer.ts # Tiny font tespiti
│ │ ├── metadata-analyzer.ts # Metadata injection
│ │ ├── pattern-analyzer.ts # Pattern matching
│ │ └── unicode-analyzer.ts # Invisible unicode
│ ├── parsers/ # Dosya ayrıştırıcıları
│ │ ├── pdf-parser.ts
│ │ ├── docx-parser.ts
│ │ └── pptx-parser.ts
│ ├── ui/ # React bileşenleri
│ │ ├── DropZone.tsx
│ │ ├── ResultsPanel.tsx
│ │ ├── FindingCard.tsx
│ │ ├── ScanProgress.tsx
│ │ └── AttacksPage.tsx
│ ├── patterns/
│ │ ├── tr.json # Türkçe injection pattern'ları
│ │ └── en.json # İngilizce injection pattern'ları
│ ├── reporter/
│ │ └── report-builder.ts
│ └── App.tsx
├── public/
├── index.html
└── vite.config.ts
```
## 👨💻 开发者
**Emre Koca** — [0xemrek](https://github.com/kocaemre)
## 📄 许可证
MIT标签:AI安全, Chat Copilot, DOCX安全, mammoth.js, pdf.js, PDF安全, PPTX安全, React 18, Tailwind CSS, TLS, TypeScript, Unicode隐藏字符, Vite, ZeGuard, 元数据注入, 前端安全, 安全插件, 客户端安全工具, 提示词注入检测, 文件上传安全, 本地文件分析, 浏览器端解析, 网络安全, 自定义脚本, 防御工具, 隐形字体检测, 隐私保护, 默认DNS解析器