MikkoParkkola/nowifi
GitHub: MikkoParkkola/nowifi
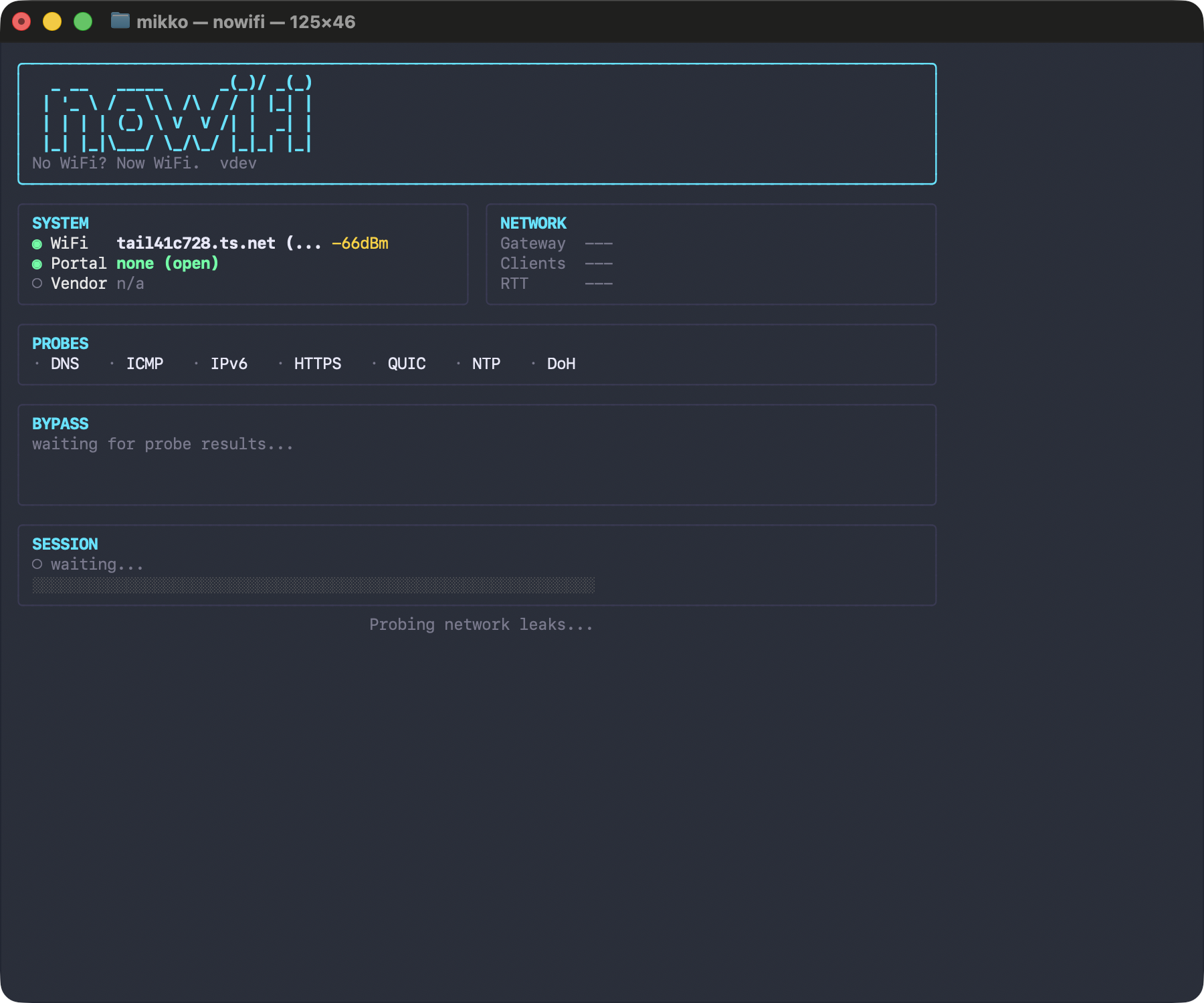
一款通过多技术自动探测与绕过 captive portal 并提供 WPA 破解的一体化工具。
Stars: 1 | Forks: 0
# nowifi
[](LICENSE)
[](https://github.com/MikkoParkkola/nowifi/actions/workflows/ci.yml)
[](https://goreportcard.com/report/github.com/MikkoParkkola/nowifi)
[](https://github.com/MikkoParkkola/nowifi/releases)
[](https://github.com/MikkoParkkola/nowifi/releases)
[](go/go.mod)
[](https://libraries.io/github/MikkoParkkola/nowifi)
[](https://github.com/MikkoParkkola/nowifi)
### 没有 WiFi?现在有 WiFi。
**Author: Mikko Parkkola**
One command. 43 techniques. Browser works immediately.
```
sudo nowifi
```
` | TLS 1.3 ECH domain fronting (#24) |
| `sudo nowifi --masque-server https://proxy:443` | MASQUE tunnel via HTTP/3 Extended CONNECT (#27) |
| `sudo nowifi --wt-server https://proxy:443/wt` | WebTransport tunnel over HTTP/3 (#28) |
| `sudo nowifi --h2-proxy https://proxy:443` | HTTP/2 CONNECT tunnel (gRPC-style) (#29) |
| `sudo nowifi --sse-server https://relay.example.com` | SSE streaming tunnel (#30) |
| `sudo nowifi --grpc-server https://proxy:443` | gRPC bidi streaming tunnel (#31) |
| `sudo nowifi --connectip-server https://proxy:443` | CONNECT-IP full IP tunnel (#32) |
| `sudo nowifi -i en1` | Use a different WiFi interface (default: `en0`) |
| `nowifi recon -o klm.json` | Passive network fingerprint for contributing provider profiles |
| `nowifi diagnose` | Read-only security assessment (no changes to network) |
| `nowifi diagnose -r json -o report.json` | Save diagnosis as JSON file |
| `nowifi crack` | 8-technique WPA/WPA2 cracking pipeline (ordered fastest-to-slowest, stops on first recovered password) |
| `nowifi crack --scan-only` | Scan for WiFi networks without attacking |
| `nowifi scan` | Scan nearby WiFi networks with signal/security info |
| `nowifi watch` | Maintain access -- auto-reconnect on session expiry |
| `nowifi history` | Show past audit sessions |
| `nowifi tools` | Show which external tools are installed/missing |
| `nowifi tools -d` | Checksum-verified auto-download of missing tools (chisel, hysteria, cloudflared) |
| `nowifi server create` | Create a tunnel server (CF Worker or VPS) |
| `nowifi server list` | List active tunnel servers |
| `nowifi server destroy` | Destroy a tunnel server |
| `nowifi server info` | Show which techniques need a server |
| `sudo nowifi server listen` | Run the HTTP/3-ALPN tunnel server (peer for `--http3-server`) |
| `nowifi ecosystem` | Show complementary tools (bettercap, wifiphisher, etc.) |
| `nowifi setup` | Interactive first-time setup wizard |
| `nowifi doctor` | System health check |
| `nowifi ui` | Launch the web dashboard |
| `nowifi menubar` | Launch the macOS menubar app |
| `nowifi score` | Grade nearby WiFi networks (A-F) |
| `sudo nowifi reset` | Emergency network reset after crash/kill |
## 43 种技术
### 门户绕过(35 种技术)
These work when you're connected to WiFi but stuck behind a captive portal login page.
| # | Technique | How it works | Severity |
|---|-----------|-------------|----------|
| 1 | **IPv6 bypass** | Portal only filters IPv4; IPv6 passes unfiltered | Critical |
| 2 | **HTTPS/WS tunnel** | Chisel WebSocket tunnel through HTTPS to your server | Critical |
| 3 | **CNA User-Agent spoof** | Portal auto-approves Apple CNA/Wispr User-Agent requests | High |
| 4 | **JS-only bypass** | Portal enforces auth only in JavaScript, not server-side | High |
| 5 | **HTTP CONNECT abuse** | Tunnel through the portal's transparent proxy via CONNECT | High |
| 6 | **MAC clone (idle)** | Clone an inactive authenticated device's MAC address | Critical |
| 7 | **MAC clone (any)** | Clone any authenticated device's MAC from ARP table | Critical |
| 8 | **DNS tunnel** | IP-over-DNS via iodine (50-500 Kbps) | High |
| 9 | **ICMP tunnel** | IP-over-ping via hans (100-300 Kbps) | High |
| 10 | **VPN on port 53** | WireGuard/OpenVPN on DNS port, usually allowed | High |
| 11 | **Whitelist domain** | Tunnel via whitelisted CDN domain | Medium |
| 12 | **Session cookie replay** | Sniff and replay portal auth cookies (HTTP portals) | High |
| 13 | **Portal default creds** | Try default admin passwords on portal management | Critical |
| 14 | **MAC rotate** | Fresh random MAC for new session/quota/time limit | High |
| 15 | **DHCP rotate** | New IP via DHCP release/renew cycle | Medium |
| 16 | **QUIC tunnel** | Hysteria2 over UDP/443 (looks like HTTP/3 to DPI) | Critical |
| 17 | **CF Workers proxy** | Serverless proxy via Cloudflare Workers (no server needed) | Critical |
| 18 | **NTP tunnel** | Data encoded in NTP extension fields on UDP/123 | High |
| 19 | **DoH tunnel** | DNS-over-HTTPS to Cloudflare/Google (whitelisted endpoints) | High |
| 20 | **CAPPORT extend** | RFC 8908 captive-portal API — surfaces session state and user-portal URL | Medium |
| 21 | **DoQ tunnel** | DNS-over-QUIC (RFC 9250) to public resolver, bypasses DNS interception | High |
| 22 | **HTTP/3 tunnel** | Pure-Go QUIC tunnel with ALPN `h3` on UDP/443, SOCKS5 wrapper | Critical |
| 23 | **DHCP Option 121 route** | CVE-2024-3661 "TunnelVision" — honor DHCP-advertised static routes that bypass the portal's filter chain (serverless) | High |
| 24 | **ECH domain fronting** | TLS 1.3 Encrypted Client Hello (RFC 9147) cloaks the real SNI behind a CDN cover name | Critical |
| 25 | **WG-over-WebSocket** | WireGuard/tunnel payloads in WS binary frames on TCP/443 (looks like Teams/Zoom) | Critical |
| 26 | **Secondary interface** | Use cellular/USB-Ethernet/Bluetooth-PAN to exit the carrier, bypassing portal entirely (serverless) | Critical |
| 27 | **MASQUE tunnel** | HTTP/3 Extended CONNECT (RFC 9220/9298) — identical to Apple Private Relay/Cloudflare WARP | Critical |
| 28 | **WebTransport tunnel** | RFC 9220 WebTransport over HTTP/3 — looks like Google Meet/Zoom to DPI | Critical |
| 29 | **HTTP/2 CONNECT tunnel** | HTTP/2 binary-framed CONNECT — looks like gRPC/Cloud API to DPI | Critical |
| 30 | **SSE streaming tunnel** | Server-Sent Events downlink + HTTP POST uplink — looks like a news feed | High |
| 31 | **gRPC bidi streaming tunnel** | HTTP/2 + application/grpc framing — looks like Kubernetes/microservice API traffic | High |
| 32 | **CONNECT-IP tunnel** | RFC 9484 full IP tunnel via QUIC datagrams — identical to Apple Private Relay | Critical |
| 33 | **Cloudflare WARP tunnel** | Zero-config — auto-registers free WARP device, tunnels via HTTP/2 CONNECT | Critical |
| 34 | **Portal self-relay** | Zero-config — tunnels through portal-whitelisted domains (Stripe, Google, Apple) via HTTP/2 CONNECT | Critical |
| 35 | **TURN relay** | Zero-config — relays through public WebRTC TURN servers on TCP/443, indistinguishable from video calls | High |
### 匿名遥测(可选,零成本)
nowifi can send anonymous data about which bypass techniques succeed on which captive portals. Purpose: security research + improved technique ordering in future releases.
```
nowifi telemetry enable # opt in
nowifi telemetry status # show state
nowifi telemetry disable # opt out
```
**Collected**: technique ID, success, provider, duration, version, country
**NEVER collected**: IP, MAC, SSID, portal URL, DNS names, or any personal identifier
Data goes to a single Cloudflare Worker running on the free tier (100K events/day). Source: [worker/telemetry/](worker/telemetry/).
### WPA 破解(4 种技术)
These crack the actual WiFi password when you don't have it. The stages run in order, and slower fallback steps only run if the earlier capture and smart-crack stages fail.
| # | Technique | How it works |
|---|-----------|-------------|
| 31 | **PMKID capture** | Extract PMKID from AP's first message -- no clients needed (~60% of APs) |
| 32 | **WPS Pixie-Dust** | Exploit weak RNG in WPS (~30% of WPS-enabled APs, 5-30s) |
| 33 | **Handshake capture + hashcat** | Deauth a client, capture 4-way handshake, GPU crack |
| 34 | **WPS PIN brute force** | Brute force 11,000 PIN combinations (2-10 hours, last resort) |
### 智能破解(4 种额外策略)
| # | Technique | How it works |
|---|-----------|-------------|
| 35 | **Smart common passwords** | Top 1000 WiFi passwords (embedded, no wordlist needed) |
| 36 | **Numeric mask attack** | 8-digit patterns common in ISP-issued routers |
| 37 | **Word+number rules** | Hashcat rules combining dictionary words with numbers |
| 38 | **Online brute force** | wpa_supplicant PSK attempts (no monitor mode needed) |
The smart-crack pipeline also runs dictionary, smart-brute, and (opt-in) full-brute stages between rules and online brute force, in increasing cost order.
## 外部工具
nowifi works out of the box for many techniques. External tools unlock tunnel and cracking capabilities.
```
# 检查已安装内容
nowifi tools
# 校验和验证的自动下载支持工具
nowifi tools -d
```
| Tool | Unlocks | Install |
|------|---------|---------|
| chisel | HTTPS/WS tunnel (#2) | `nowifi tools -d` |
| hysteria | QUIC tunnel (#16) | `nowifi tools -d` |
| cloudflared | DoH tunnel (#19) | `nowifi tools -d` |
| iodine | DNS tunnel (#8) | `brew install iodine` |
| hans | ICMP tunnel (#9) | `brew install hans` |
| hashcat | WPA cracking (GPU) | `brew install hashcat` |
| aircrack-ng | WPA cracking (CPU) | `brew install aircrack-ng` |
| hcxdumptool | PMKID/handshake capture | `brew install hcxdumptool` |
| hcxpcapngtool | Convert captures for hashcat | `brew install hcxtools` |
| reaver | WPS Pixieust/PIN attacks | `brew install reaver` |
## 隧道服务器设置
Many techniques work without any server (MAC clone, IPv6, CNA spoof, etc.). Tunnel-based bypasses need a server you control outside the portal's network.
### 最快:Cloudflare Workers(免费)
```
nowifi server create
# 部署一个免费的 Cloudflare Worker 作为 HTTPS 代理(每天 100K 请求)
```
### VPS(DigitalOcean / Hetzner)
```
nowifi server create -p digitalocean -t do_xxx_token
# 每小时 0.007 美元创建带有预安装 chisel+iodine+hans 的 droplet
```
### 您自己的服务器
```
# 在服务器上:
chisel server --reverse --port 443
# 在笔记本电脑上(在门户之后):
sudo nowifi -t https://your-server.example.com
```
### HTTP/3-ALPN 隧道服务器(#22,纯 Go,无需外部二进制文件)
```
# 在服务器上(一次):
sudo nowifi server listen --addr 0.0.0.0:443 --hostname tunnel.example.com
# 自动生成自签名证书(或传递 --cert/--key 以使用 Let's Encrypt)
# 在笔记本电脑上(在门户之后):
sudo nowifi --http3-server https://tunnel.example.com:443
```
The server speaks QUIC with ALPN `h3` on UDP/443. From a middlebox's point of view the traffic is indistinguishable from a browser HTTP/3 session, so it passes TCP-only DPI and most captive-portal filters.
### DoH/DoQ(无需服务器)
Technique #21 (DoQ) connects to a public resolver (default `dns.adguard.com:853`), so no infrastructure is required. Same for #19 (DoH — Cloudflare/Google).
## 食谱
Hands-on guides for specific scenarios:
- [VPN over Cloudflare Quick Tunnel](docs/recipes/vpn-over-quick-tunnel.md) — carry a VPN through a TCP-only captive portal using zero-config UDP (`nowifi server create -p cloudflare-quick --udp`), plus four alternative strategies (chisel-legacy, OpenVPN TCP, wstunnel, Tailscale/ZeroTier).
See [`CHANGELOG.md`](CHANGELOG.md) for the full release history.
## 架构(Go)
```
cmd/nowifi/main.go Entry point
internal/
cli/ Cobra commands (audit, diagnose, crack, tools, ...)
detect/ Portal detection: canary URLs, DNS hijack, vendor fingerprinting
probe/ Leak enumeration: DNS, ICMP, IPv6, HTTPS, QUIC, NTP, DoH, ports
bypass/ 22 bypass techniques, ordered most-powerful-first
crack/ WPA cracking: PMKID, handshake, hashcat, WPS, smart crack
tunnel/ Tunnel management: chisel, iodine, hans, hysteria
platform/ OS abstraction: macOS (darwin.go) / Linux (linux.go)
report/ Terminal, markdown, and JSON report generation
toolchain/ External tool discovery, auto-download, version management
server/ Cloudflare Workers + VPS provisioning (DO, Hetzner)
config/ Persistent config (~/.nowifi/config.json)
capture/ Audit trail storage (~/.nowifi/captures/)
guard/ State restoration on exit (MAC, proxy, DNS)
monitor/ WiFi monitor mode management
discover/ WiFi network scanning
portal/ Auto-login to known portal types
clone/ MAC address cloning
inflight/ Airline portal intelligence: 7 provider profiles, 40+ airlines
score/ WiFi network scoring (A-F grade)
ui/ Web dashboard + menubar app
```
## 负责任使用
This tool is for **authorized security assessments** of captive portal implementations.
- **Only test networks you own or have explicit written authorization to test.** Unauthorized access to computer networks is illegal in most jurisdictions (e.g., CFAA in the US, Computer Misuse Act in the UK, Rikoslaki 38:8 in Finland).
- **Deauthentication attacks** (technique #22, WPA handshake capture) actively interfere with other users' connections. This may violate telecommunications regulations even on networks you own, if it affects third parties.
- **MAC cloning** another device's address takes over their authenticated session, disconnecting them. Only use this in controlled lab environments or with explicit consent.
- **Session cookie replay** involves capturing other users' network traffic. This may violate wiretapping laws in your jurisdiction.
The authors accept no liability for misuse. This tool is published for defensive research, security assessment, and education.
## 更多工具
| Tool | What it does |
|------|-------------|
| [trvl](https://github.com/MikkoParkkola/trvl) | AI travel agent — flights, hotels, ferries, 33 MCP tools |
| [axterminator](https://github.com/MikkoParkkola/axterminator) | macOS GUI automation — 30 MCP tools, audio/camera capture |
| [mcp-gateway](https://github.com/MikkoParkkola/mcp-gateway) | Universal MCP gateway — single-port multiplexing |
| [nab](https://github.com/MikkoParkkola/nab) | Token-optimized HTTP client for LLMs |
All tools: `brew tap MikkoParkkola/tap && brew install trvl axterminator mcp-gateway nab nowifi`
## 许可
[AGPL-3.0](LICENSE) -- Copyright (C) 2026 Mikko Parkkola
标签:Captive Portal绕过, EVTX分析, Go语言, Homebrew, PMKID, VEH, WiFi恢复, WiFi破解, WPA/WPA2破解, WPS PIN攻击, WPS Pixie-Dust, 一键联网, 二进制发布, 在线暴力破解, 多技术绕过, 字典攻击, 开源工具, 握手包捕获, 数据泄露防护, 无WiFi, 日志审计, 智能破解, 浏览器即刻可用, 程序员工具, 程序破解, 网络安全, 网络工具, 网络恢复, 网络探测, 认证绕过, 隐私保护, 隐私工具