IkramCaffoor/Scan-Things
GitHub: IkramCaffoor/Scan-Things
一个轻量级自动化侦察工具,将Nmap扫描、目录爆破和子域名枚举整合为一键式流程,专为CTF练习和渗透测试信息收集阶段设计。
Stars: 0 | Forks: 0
# 扫描事项
/ ___|| _ \ / \ | \ | | ____|_ _| _ \
\___ \| | | |/ _ \ | \| | _| | | | |_) |
___) | |_| / ___ \| |\ | |___ | | | __/
|____/|____/_/ \_\_| \_|_____| |_| |_|
```
Scan-Things v1.0
Automated Reconnaissance Tool
Smart Recon for Domains & IPs
```
============================================================
**一个简单而强大的自动化侦察扫描器,专为渗透测试练习而构建。**
Scan-Things 会自动执行:
- 完整的 Nmap 服务和脚本扫描
- Web 服务器目录暴力破解(支持 IP 和域名)
- 子域名枚举(当提供域名时)
非常适合 Hack The Box、TryHackMe 以及真实目标侦察。
## 演示
## 功能特性
- 智能检测:同时支持 IP 地址和域名
- 运行带有服务版本检测的 Nmap 扫描 (-sC -sV)
- 对常见扩展名 (.php, .html, .txt, .git) 进行目录暴力破解
- 当目标是域名时自动进行子域名枚举
- 创建整洁的结果文件 (`found_directories.txt` 和 `found_subdomains.txt`)
- 将所有内容保存在带有时间戳的文件夹中,便于整理
- 简洁的 msfconsole 风格输出
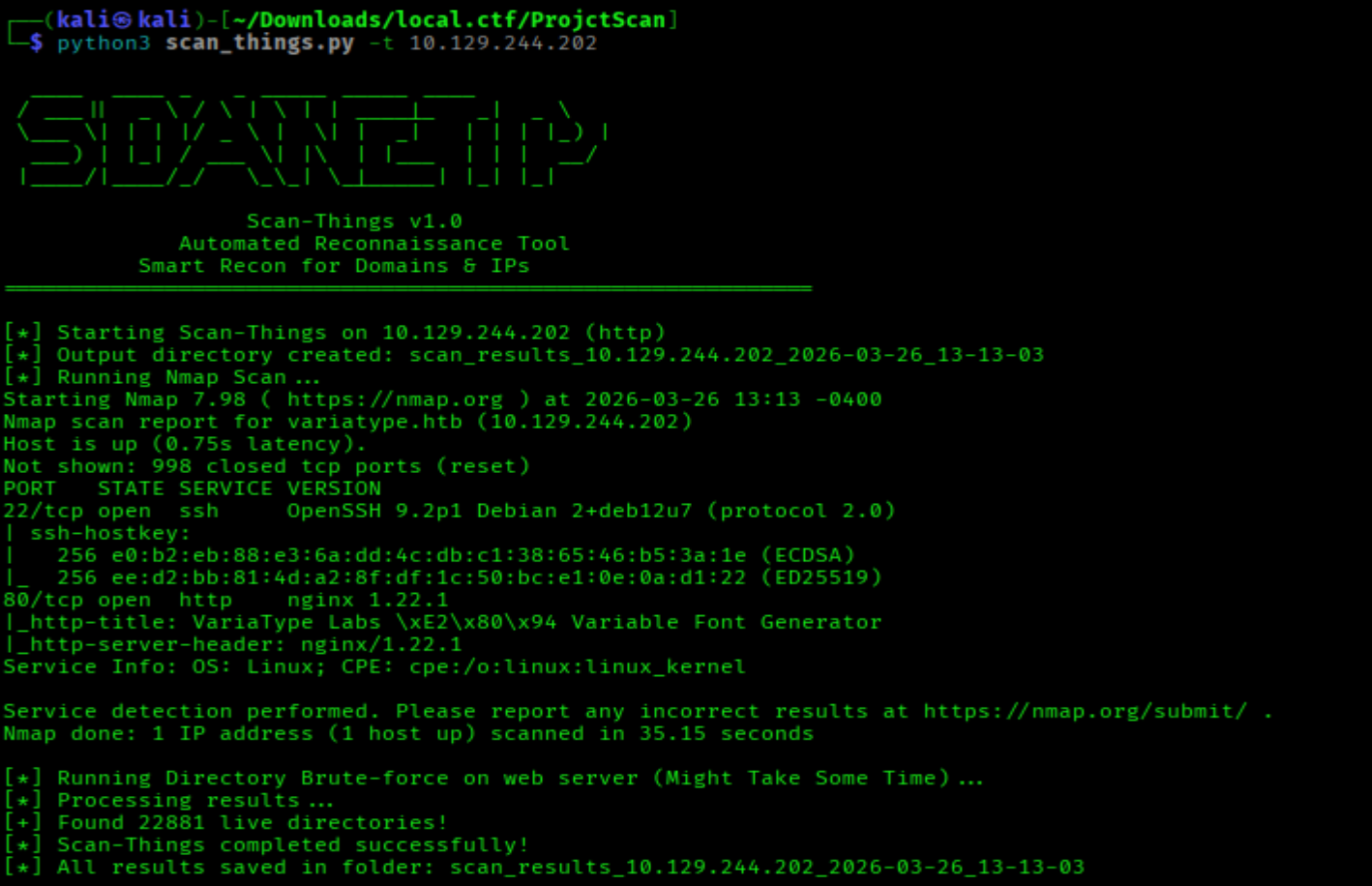
示例:我使用了 HackTheBox 靶机:
┌──(kali㉿kali)-[~/Downloads/local.ctf/ProjctScan]
└─$ python3 scan_things.py -t 10.129.244.202
/ ___|| _ \ / \ | \ | | ____|_ _| _ \
\___ \| | | |/ _ \ | \| | _| | | | |_) |
___) | |_| / ___ \| |\ | |___ | | | __/
|____/|____/_/ \_\_| \_|_____| |_| |_|
```
Scan-Things v1.0
Automated Reconnaissance Tool
Smart Recon for Domains & IPs
```
============================================================
[*] 在 10.129.244.202 (http) 上启动 Scan-Things
[*] 输出目录已创建:scan_results_10.129.244.202_2026-03-26_13-13-03
[*] 正在运行 Nmap 扫描...
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-26 13:13 -0400
Nmap scan report for variatype.htb (10.129.244.202)
Host is up (0.75s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u7 (protocol 2.0)
| ssh-hostkey:
| 256 e0:b2:eb:88:e3:6a:dd:4c:db:c1:38:65:46:b5:3a:1e (ECDSA)
|_ 256 ee:d2:bb:81:4d:a2:8f:df:1c:50:bc:e1:0e:0a:d1:22 (ED25519)
80/tcp open http nginx 1.22.1
|_http-title: VariaType Labs \xE2\x80\x94 Variable Font Generator
|_http-server-header: nginx/1.22.1
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 35.15 seconds
[*] 正在 Web 服务器上运行目录暴力破解(可能需要一些时间)...
[*] 正在处理结果...
[+] 发现 22881 个存活目录!
[*] Scan-Things 成功完成!
[*] 所有结果已保存在文件夹中:scan_results_10.129.244.202_2026-03-26_13-13-03
┌──(kali㉿kali)-[~/Downloads/local.ctf/ProjctScan]
└─$ ls
scan_results_10.129.244.202_2026-03-26_13-13-03 scan_things.py
┌──(kali㉿kali)-[~/Downloads/local.ctf/ProjctScan]
└─$ cd scan_results_10.129.244.202_2026-03-26_13-13-03
┌──(kali㉿kali)-[~/Downloads/local.ctf/ProjctScan/scan_results_10.129.244.202_2026-03-26_13-13-03]
└─$ ls
directories.json found_directories.txt nmap_scan.txt
## 安装说明
```
git clone https://github.com/yourusername/scan-things.git
cd scan-things
# 安装所需工具(仅一次)
sudo apt update
sudo apt install nmap ffuf -y
# 可选但建议用于获取更好的 wordlists
sudo apt install seclists -y
```
标签:CTF工具, CTI, HTB, Nmap, Python, TryHackMe, 子域名枚举, 安全脚本, 插件系统, 无后门, 漏洞搜索, 白帽, 目录爆破, 系统安全, 网络安全, 网络安全审计, 自动化侦察, 虚拟驱动器, 轻量级扫描器, 逆向工具, 隐私保护