googleSandy/secops-skills
GitHub: googleSandy/secops-skills
为 Google SecOps 提供结构化的 AI 代理技能,解决 SIEM 查询与 YARA-L 规则编写中的知识准确与更新问题。
Stars: 3 | Forks: 1
#  Google SecOps Agent Skills
[](LICENSE)
[](.github/workflows/update-references.yml)
[](https://agentskills.io)
[](https://cloud.google.com/security/products/security-operations)
Agent Skills for [Google Security Operations](https://cloud.google.com/security/products/security-operations) (SecOps / Chronicle) — giving AI agents accurate, up-to-date knowledge to write SIEM queries, build detection rules, and navigate the detection engineering workflow.
Built to the [Agent Skills](https://agentskills.io) open specification — works with any agent that supports it.
## 📚 Skills
### [`secops-siem-search`](skills/secops-siem-search/SKILL.md)
Syntax reference and field guidance for authoring SecOps SIEM queries for investigations and threat hunting.
Covers: UDM filter queries · stats/aggregation · event-event joins · raw log search · reference list lookups · entity investigations · enriched data (geolocation, VirusTotal) · entity context (`graph.*`) · data availability timing
### [`secops-yara-l`](skills/secops-yara-l/SKILL.md)
Syntax reference and patterns for authoring YARA-L 2.0 detection rules and search queries. Rules should always be tested in your environment before deployment.
Covers: single-event rules · multi-event correlation · sliding/tumbling/hop windows · composite rules · outcome aggregations · multi-stage search queries · Z-score and MAD anomaly detection · entity graph joins · metrics behavioral analytics
### [`secops-detection-engineering`](skills/secops-detection-engineering/SKILL.md)
Knowledge and guidance for the SecOps detection engineering workflow — from writing a rule to getting it into production.
Covers: understanding the rule lifecycle (test → retrohunt → deploy) · choosing run frequency · diagnosing detection delays · MTTD optimization · context-aware analytics · risk scoring · Safe Browsing and threat intel IOC joins · composite detection chains · troubleshooting compilation and runtime errors
## 🚀 Installation
Clone the repo and point your agent at the `skills/` directory:
```
git clone https://github.com/googleSandy/secops-skills.git
```
Each skill is a self-contained directory under `skills/`. How you load them depends on your agent:
- **Agent Skills-compatible agents** — configure your agent to load skills from `secops-skills/skills/`, or copy individual skill directories into your agent's skills path (e.g. `~/.agents/skills/`, `~/.claude/skills/`, or wherever your agent looks)
- **Other agents** — drop the skill directory alongside your project and reference the `SKILL.md` in your system prompt or context
Each skill is independent — install one, two, or all three depending on what you need.
## 📁 Structure
```
secops-skills/
├── llms.txt # Skill index for LLM discovery
└── skills/
├── secops-siem-search/
│ ├── SKILL.md # Skill entry point
│ ├── evals/evals.json # Test cases for evaluation
│ └── references/ # Auto-generated reference files (UDM, search)
├── secops-yara-l/
│ ├── SKILL.md
│ ├── evals/evals.json
│ └── references/ # Auto-generated reference files (YARA-L syntax)
└── secops-detection-engineering/
├── SKILL.md
├── evals/evals.json
└── references/ # Auto-generated reference files (Workflows, rules)
```
## 🔄 Keeping References Up to Date
Reference files are scraped from Google Cloud's live documentation using a combination of a general recursive crawler and a specialized updater (`scripts/update_references.py`) for structured tables.
### Automated (GitHub Actions)
The included workflow can be configured to run periodically to keep the reference library up to date.
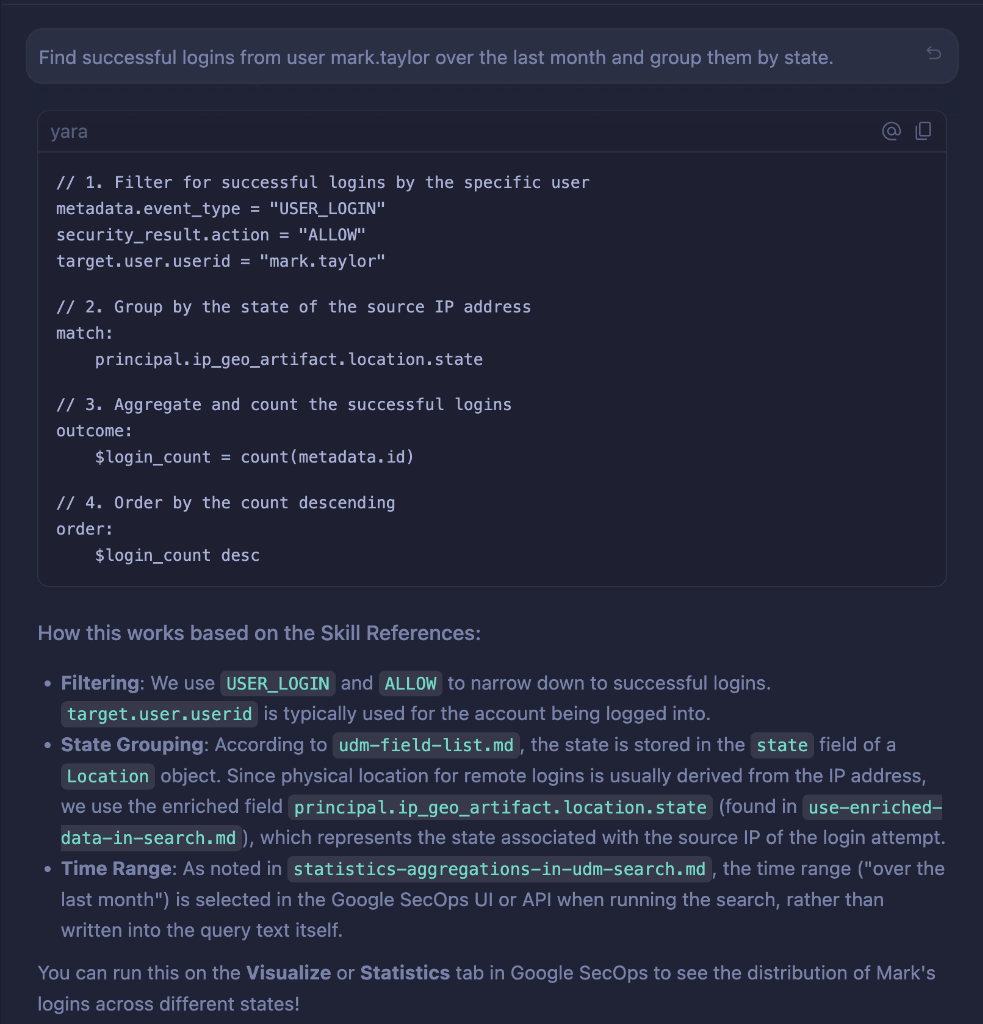
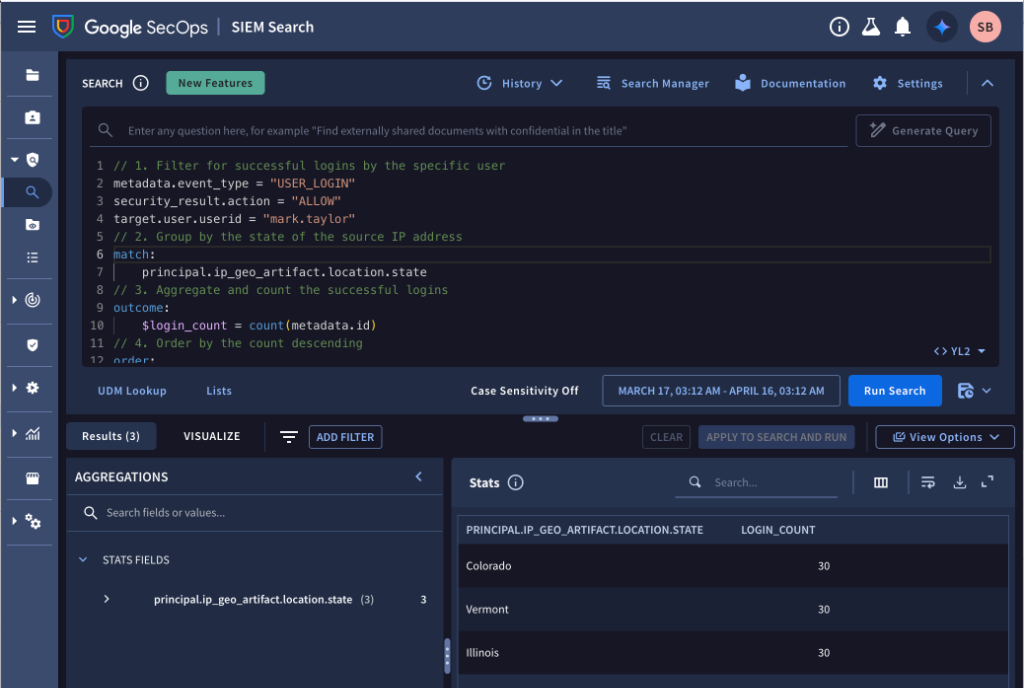
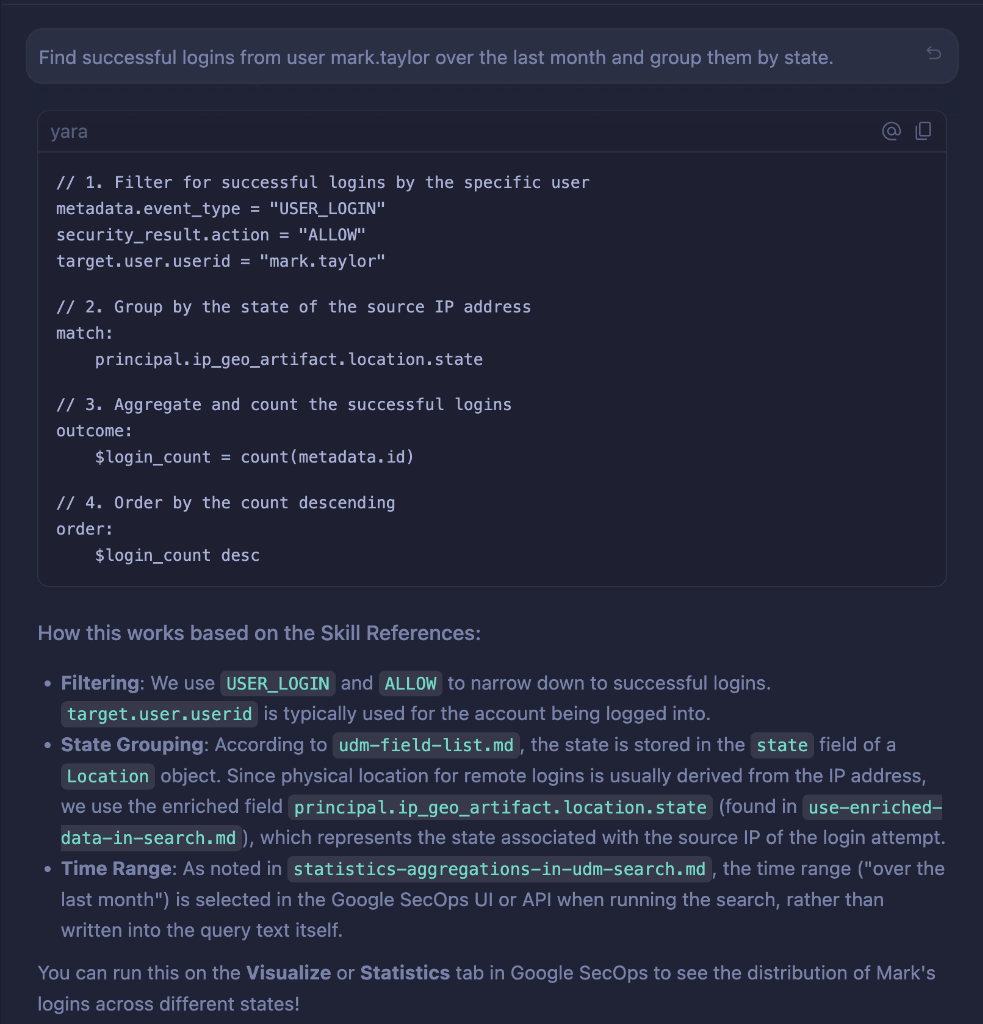
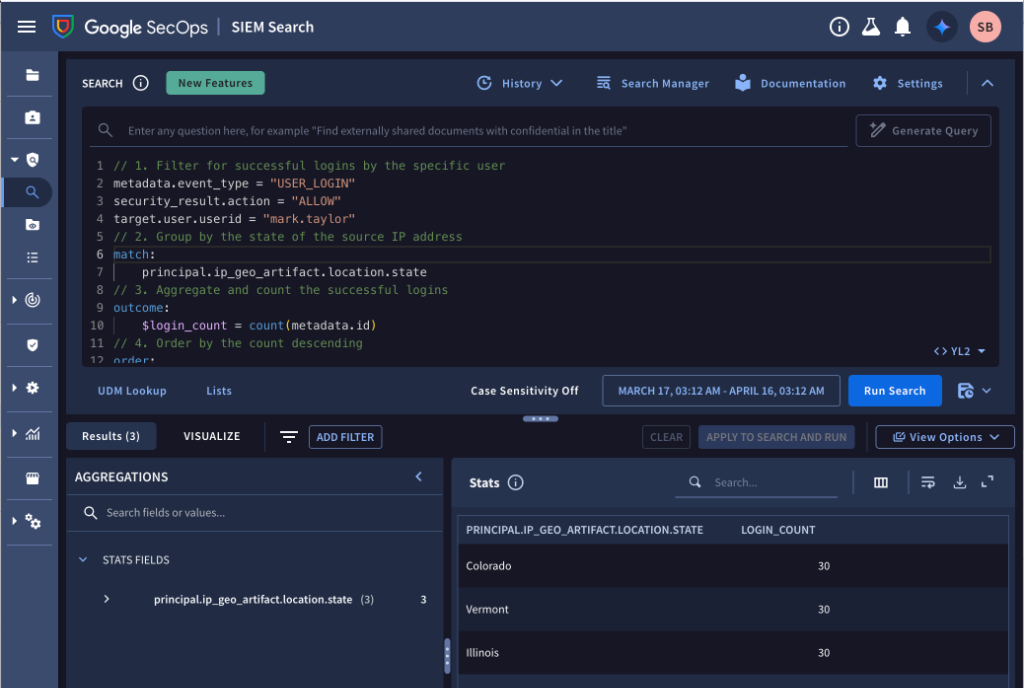
## 📊 Example Use Case: UDM Search
Google SecOps Agent Skills
[](LICENSE)
[](.github/workflows/update-references.yml)
[](https://agentskills.io)
[](https://cloud.google.com/security/products/security-operations)
Agent Skills for [Google Security Operations](https://cloud.google.com/security/products/security-operations) (SecOps / Chronicle) — giving AI agents accurate, up-to-date knowledge to write SIEM queries, build detection rules, and navigate the detection engineering workflow.
Built to the [Agent Skills](https://agentskills.io) open specification — works with any agent that supports it.
## 📚 Skills
### [`secops-siem-search`](skills/secops-siem-search/SKILL.md)
Syntax reference and field guidance for authoring SecOps SIEM queries for investigations and threat hunting.
Covers: UDM filter queries · stats/aggregation · event-event joins · raw log search · reference list lookups · entity investigations · enriched data (geolocation, VirusTotal) · entity context (`graph.*`) · data availability timing
### [`secops-yara-l`](skills/secops-yara-l/SKILL.md)
Syntax reference and patterns for authoring YARA-L 2.0 detection rules and search queries. Rules should always be tested in your environment before deployment.
Covers: single-event rules · multi-event correlation · sliding/tumbling/hop windows · composite rules · outcome aggregations · multi-stage search queries · Z-score and MAD anomaly detection · entity graph joins · metrics behavioral analytics
### [`secops-detection-engineering`](skills/secops-detection-engineering/SKILL.md)
Knowledge and guidance for the SecOps detection engineering workflow — from writing a rule to getting it into production.
Covers: understanding the rule lifecycle (test → retrohunt → deploy) · choosing run frequency · diagnosing detection delays · MTTD optimization · context-aware analytics · risk scoring · Safe Browsing and threat intel IOC joins · composite detection chains · troubleshooting compilation and runtime errors
## 🚀 Installation
Clone the repo and point your agent at the `skills/` directory:
```
git clone https://github.com/googleSandy/secops-skills.git
```
Each skill is a self-contained directory under `skills/`. How you load them depends on your agent:
- **Agent Skills-compatible agents** — configure your agent to load skills from `secops-skills/skills/`, or copy individual skill directories into your agent's skills path (e.g. `~/.agents/skills/`, `~/.claude/skills/`, or wherever your agent looks)
- **Other agents** — drop the skill directory alongside your project and reference the `SKILL.md` in your system prompt or context
Each skill is independent — install one, two, or all three depending on what you need.
## 📁 Structure
```
secops-skills/
├── llms.txt # Skill index for LLM discovery
└── skills/
├── secops-siem-search/
│ ├── SKILL.md # Skill entry point
│ ├── evals/evals.json # Test cases for evaluation
│ └── references/ # Auto-generated reference files (UDM, search)
├── secops-yara-l/
│ ├── SKILL.md
│ ├── evals/evals.json
│ └── references/ # Auto-generated reference files (YARA-L syntax)
└── secops-detection-engineering/
├── SKILL.md
├── evals/evals.json
└── references/ # Auto-generated reference files (Workflows, rules)
```
## 🔄 Keeping References Up to Date
Reference files are scraped from Google Cloud's live documentation using a combination of a general recursive crawler and a specialized updater (`scripts/update_references.py`) for structured tables.
### Automated (GitHub Actions)
The included workflow can be configured to run periodically to keep the reference library up to date.
## 📊 Example Use Case: UDM Search
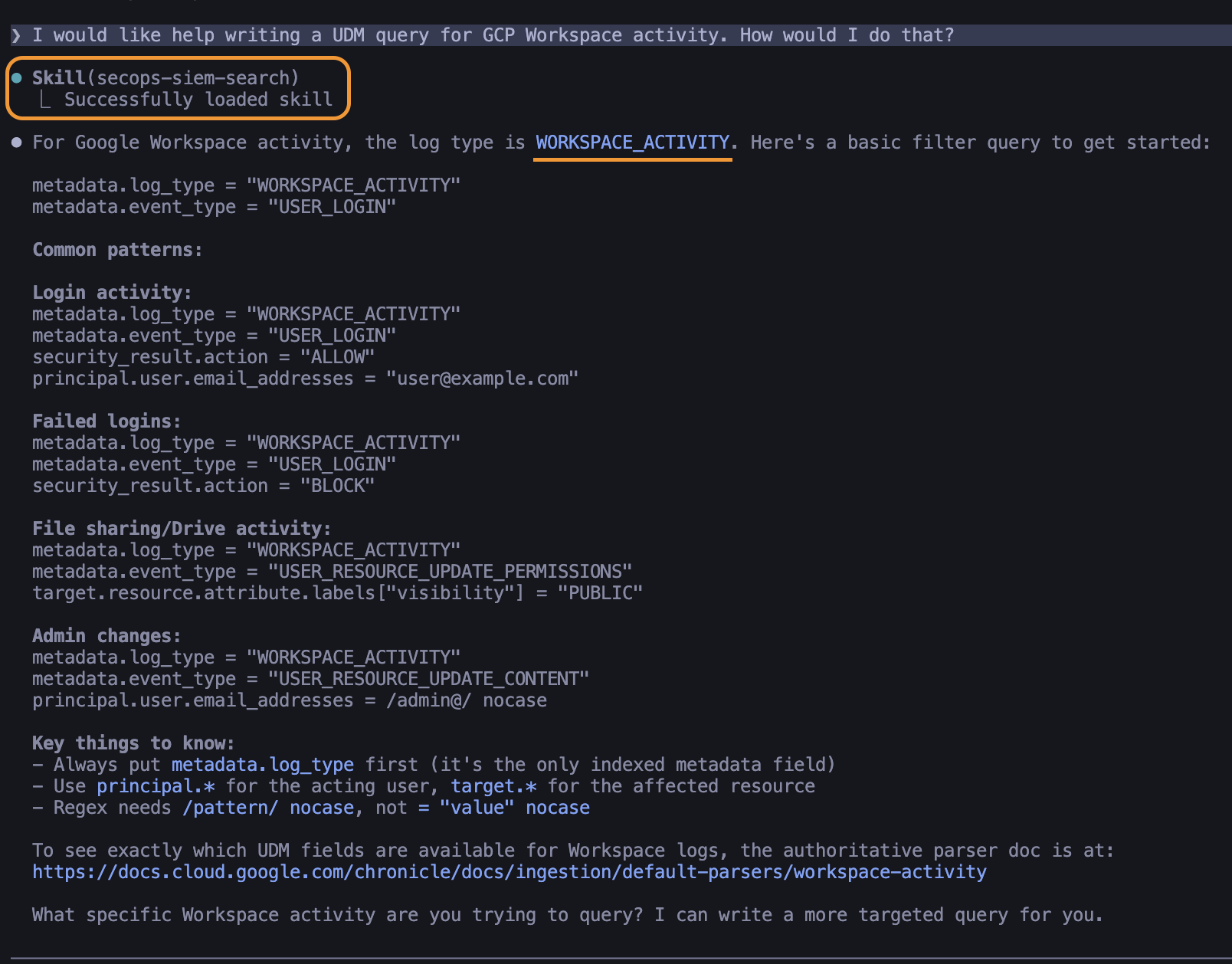 ### Here is an example of how to use the UDM Search skill to find successful logins and group them by state:
### Here is an example of how to use the UDM Search skill to find successful logins and group them by state:
 ## 🧪 Evaluation
Each skill includes test cases in `evals/evals.json` following the [AgentSkills evaluation format](https://agentskills.io/skill-creation/evaluating-skills). Results comparing with-skill vs. without-skill are in `evals-workspace/`.
To run evals, follow the [AgentSkills evaluation guide](https://agentskills.io/skill-creation/evaluating-skills).
## ⚙️ Compatibility
- **Google SecOps (SecOps / Chronicle) SIEM** required
- **Detection Engine** required for `secops-yara-l` and `secops-detection-engineering`
- YARA-L version: 2.0
- ATT&CK version referenced: v14.1+
## ⚖️ License
Apache 2.0 — see [LICENSE](LICENSE).
Rule examples sourced from [chronicle/detection-rules](https://github.com/chronicle/detection-rules) are also Apache 2.0.
## 🧪 Evaluation
Each skill includes test cases in `evals/evals.json` following the [AgentSkills evaluation format](https://agentskills.io/skill-creation/evaluating-skills). Results comparing with-skill vs. without-skill are in `evals-workspace/`.
To run evals, follow the [AgentSkills evaluation guide](https://agentskills.io/skill-creation/evaluating-skills).
## ⚙️ Compatibility
- **Google SecOps (SecOps / Chronicle) SIEM** required
- **Detection Engine** required for `secops-yara-l` and `secops-detection-engineering`
- YARA-L version: 2.0
- ATT&CK version referenced: v14.1+
## ⚖️ License
Apache 2.0 — see [LICENSE](LICENSE).
Rule examples sourced from [chronicle/detection-rules](https://github.com/chronicle/detection-rules) are also Apache 2.0.
 Google SecOps Agent Skills
[](LICENSE)
[](.github/workflows/update-references.yml)
[](https://agentskills.io)
[](https://cloud.google.com/security/products/security-operations)
Agent Skills for [Google Security Operations](https://cloud.google.com/security/products/security-operations) (SecOps / Chronicle) — giving AI agents accurate, up-to-date knowledge to write SIEM queries, build detection rules, and navigate the detection engineering workflow.
Built to the [Agent Skills](https://agentskills.io) open specification — works with any agent that supports it.
## 📚 Skills
### [`secops-siem-search`](skills/secops-siem-search/SKILL.md)
Syntax reference and field guidance for authoring SecOps SIEM queries for investigations and threat hunting.
Covers: UDM filter queries · stats/aggregation · event-event joins · raw log search · reference list lookups · entity investigations · enriched data (geolocation, VirusTotal) · entity context (`graph.*`) · data availability timing
### [`secops-yara-l`](skills/secops-yara-l/SKILL.md)
Syntax reference and patterns for authoring YARA-L 2.0 detection rules and search queries. Rules should always be tested in your environment before deployment.
Covers: single-event rules · multi-event correlation · sliding/tumbling/hop windows · composite rules · outcome aggregations · multi-stage search queries · Z-score and MAD anomaly detection · entity graph joins · metrics behavioral analytics
### [`secops-detection-engineering`](skills/secops-detection-engineering/SKILL.md)
Knowledge and guidance for the SecOps detection engineering workflow — from writing a rule to getting it into production.
Covers: understanding the rule lifecycle (test → retrohunt → deploy) · choosing run frequency · diagnosing detection delays · MTTD optimization · context-aware analytics · risk scoring · Safe Browsing and threat intel IOC joins · composite detection chains · troubleshooting compilation and runtime errors
## 🚀 Installation
Clone the repo and point your agent at the `skills/` directory:
```
git clone https://github.com/googleSandy/secops-skills.git
```
Each skill is a self-contained directory under `skills/`. How you load them depends on your agent:
- **Agent Skills-compatible agents** — configure your agent to load skills from `secops-skills/skills/`, or copy individual skill directories into your agent's skills path (e.g. `~/.agents/skills/`, `~/.claude/skills/`, or wherever your agent looks)
- **Other agents** — drop the skill directory alongside your project and reference the `SKILL.md` in your system prompt or context
Each skill is independent — install one, two, or all three depending on what you need.
## 📁 Structure
```
secops-skills/
├── llms.txt # Skill index for LLM discovery
└── skills/
├── secops-siem-search/
│ ├── SKILL.md # Skill entry point
│ ├── evals/evals.json # Test cases for evaluation
│ └── references/ # Auto-generated reference files (UDM, search)
├── secops-yara-l/
│ ├── SKILL.md
│ ├── evals/evals.json
│ └── references/ # Auto-generated reference files (YARA-L syntax)
└── secops-detection-engineering/
├── SKILL.md
├── evals/evals.json
└── references/ # Auto-generated reference files (Workflows, rules)
```
## 🔄 Keeping References Up to Date
Reference files are scraped from Google Cloud's live documentation using a combination of a general recursive crawler and a specialized updater (`scripts/update_references.py`) for structured tables.
### Automated (GitHub Actions)
The included workflow can be configured to run periodically to keep the reference library up to date.
## 📊 Example Use Case: UDM Search
Google SecOps Agent Skills
[](LICENSE)
[](.github/workflows/update-references.yml)
[](https://agentskills.io)
[](https://cloud.google.com/security/products/security-operations)
Agent Skills for [Google Security Operations](https://cloud.google.com/security/products/security-operations) (SecOps / Chronicle) — giving AI agents accurate, up-to-date knowledge to write SIEM queries, build detection rules, and navigate the detection engineering workflow.
Built to the [Agent Skills](https://agentskills.io) open specification — works with any agent that supports it.
## 📚 Skills
### [`secops-siem-search`](skills/secops-siem-search/SKILL.md)
Syntax reference and field guidance for authoring SecOps SIEM queries for investigations and threat hunting.
Covers: UDM filter queries · stats/aggregation · event-event joins · raw log search · reference list lookups · entity investigations · enriched data (geolocation, VirusTotal) · entity context (`graph.*`) · data availability timing
### [`secops-yara-l`](skills/secops-yara-l/SKILL.md)
Syntax reference and patterns for authoring YARA-L 2.0 detection rules and search queries. Rules should always be tested in your environment before deployment.
Covers: single-event rules · multi-event correlation · sliding/tumbling/hop windows · composite rules · outcome aggregations · multi-stage search queries · Z-score and MAD anomaly detection · entity graph joins · metrics behavioral analytics
### [`secops-detection-engineering`](skills/secops-detection-engineering/SKILL.md)
Knowledge and guidance for the SecOps detection engineering workflow — from writing a rule to getting it into production.
Covers: understanding the rule lifecycle (test → retrohunt → deploy) · choosing run frequency · diagnosing detection delays · MTTD optimization · context-aware analytics · risk scoring · Safe Browsing and threat intel IOC joins · composite detection chains · troubleshooting compilation and runtime errors
## 🚀 Installation
Clone the repo and point your agent at the `skills/` directory:
```
git clone https://github.com/googleSandy/secops-skills.git
```
Each skill is a self-contained directory under `skills/`. How you load them depends on your agent:
- **Agent Skills-compatible agents** — configure your agent to load skills from `secops-skills/skills/`, or copy individual skill directories into your agent's skills path (e.g. `~/.agents/skills/`, `~/.claude/skills/`, or wherever your agent looks)
- **Other agents** — drop the skill directory alongside your project and reference the `SKILL.md` in your system prompt or context
Each skill is independent — install one, two, or all three depending on what you need.
## 📁 Structure
```
secops-skills/
├── llms.txt # Skill index for LLM discovery
└── skills/
├── secops-siem-search/
│ ├── SKILL.md # Skill entry point
│ ├── evals/evals.json # Test cases for evaluation
│ └── references/ # Auto-generated reference files (UDM, search)
├── secops-yara-l/
│ ├── SKILL.md
│ ├── evals/evals.json
│ └── references/ # Auto-generated reference files (YARA-L syntax)
└── secops-detection-engineering/
├── SKILL.md
├── evals/evals.json
└── references/ # Auto-generated reference files (Workflows, rules)
```
## 🔄 Keeping References Up to Date
Reference files are scraped from Google Cloud's live documentation using a combination of a general recursive crawler and a specialized updater (`scripts/update_references.py`) for structured tables.
### Automated (GitHub Actions)
The included workflow can be configured to run periodically to keep the reference library up to date.
## 📊 Example Use Case: UDM Search
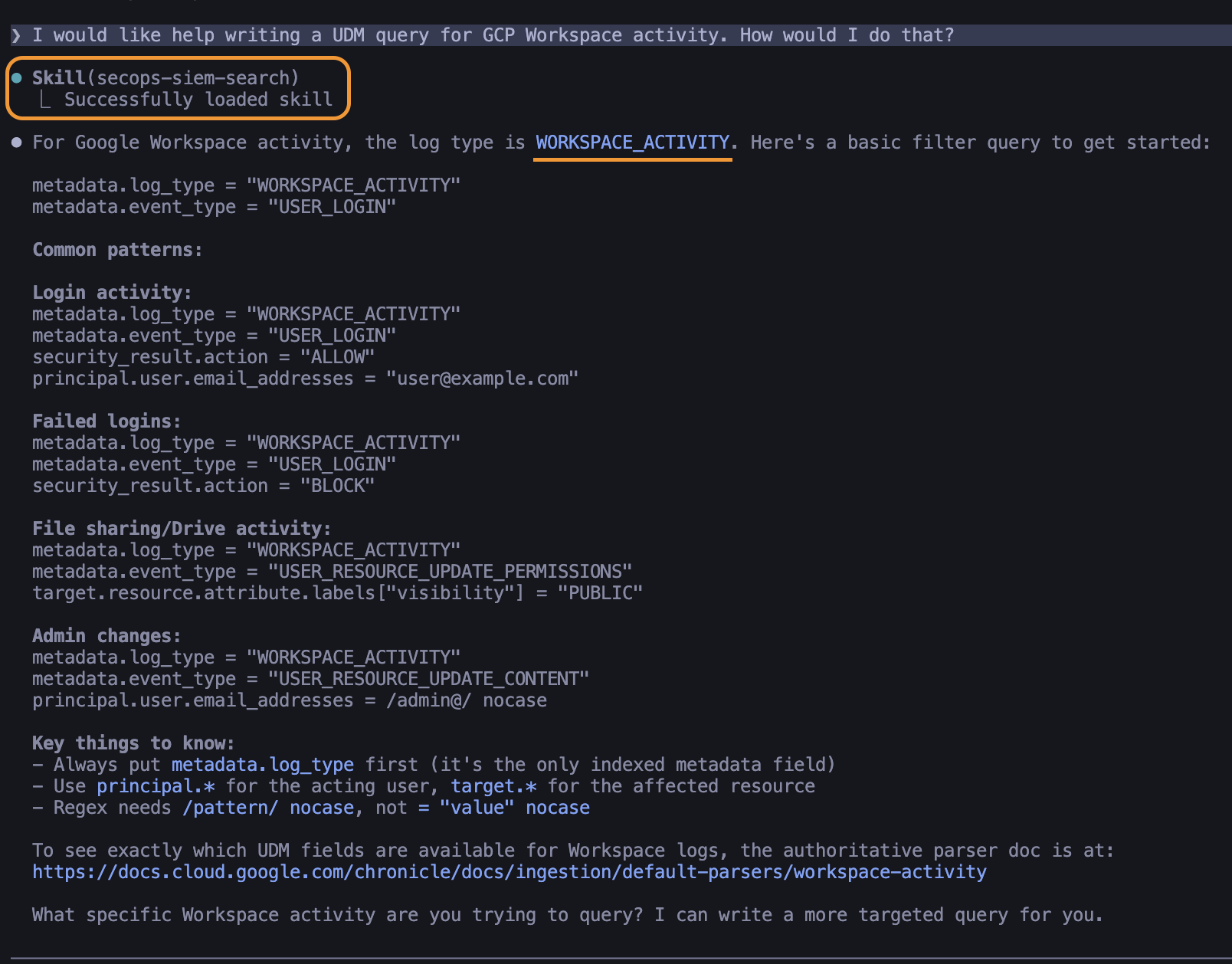 ### Here is an example of how to use the UDM Search skill to find successful logins and group them by state:
### Here is an example of how to use the UDM Search skill to find successful logins and group them by state:
 ## 🧪 Evaluation
Each skill includes test cases in `evals/evals.json` following the [AgentSkills evaluation format](https://agentskills.io/skill-creation/evaluating-skills). Results comparing with-skill vs. without-skill are in `evals-workspace/`.
To run evals, follow the [AgentSkills evaluation guide](https://agentskills.io/skill-creation/evaluating-skills).
## ⚙️ Compatibility
- **Google SecOps (SecOps / Chronicle) SIEM** required
- **Detection Engine** required for `secops-yara-l` and `secops-detection-engineering`
- YARA-L version: 2.0
- ATT&CK version referenced: v14.1+
## ⚖️ License
Apache 2.0 — see [LICENSE](LICENSE).
Rule examples sourced from [chronicle/detection-rules](https://github.com/chronicle/detection-rules) are also Apache 2.0.
## 🧪 Evaluation
Each skill includes test cases in `evals/evals.json` following the [AgentSkills evaluation format](https://agentskills.io/skill-creation/evaluating-skills). Results comparing with-skill vs. without-skill are in `evals-workspace/`.
To run evals, follow the [AgentSkills evaluation guide](https://agentskills.io/skill-creation/evaluating-skills).
## ⚙️ Compatibility
- **Google SecOps (SecOps / Chronicle) SIEM** required
- **Detection Engine** required for `secops-yara-l` and `secops-detection-engineering`
- YARA-L version: 2.0
- ATT&CK version referenced: v14.1+
## ⚖️ License
Apache 2.0 — see [LICENSE](LICENSE).
Rule examples sourced from [chronicle/detection-rules](https://github.com/chronicle/detection-rules) are also Apache 2.0.标签:Agent Skills, AI Agents, Apache 2.0 许可, Ask搜索, Chronicle, Google SecOps, Homebrew安装, SecOps, SIEM 查询, VirusTotal, YARA-L, YARA-L 2.0, 事件关联, 云安全架构, 图分析, 地理定位, 安全搜索, 安全运营, 实体调查, 开源规范, 异常检测, 扫描框架, 技能规范, 数据可用性, 日志搜索, 检测规则, 网络资产发现, 聚合统计, 自动化更新, 逆向工具, 防御加固