p0dalirius/Shift-Happens-Uncovering-to-builtin-command-injection-in-Windows-context-menus
GitHub: p0dalirius/Shift-Happens-Uncovering-to-builtin-command-injection-in-Windows-context-menus
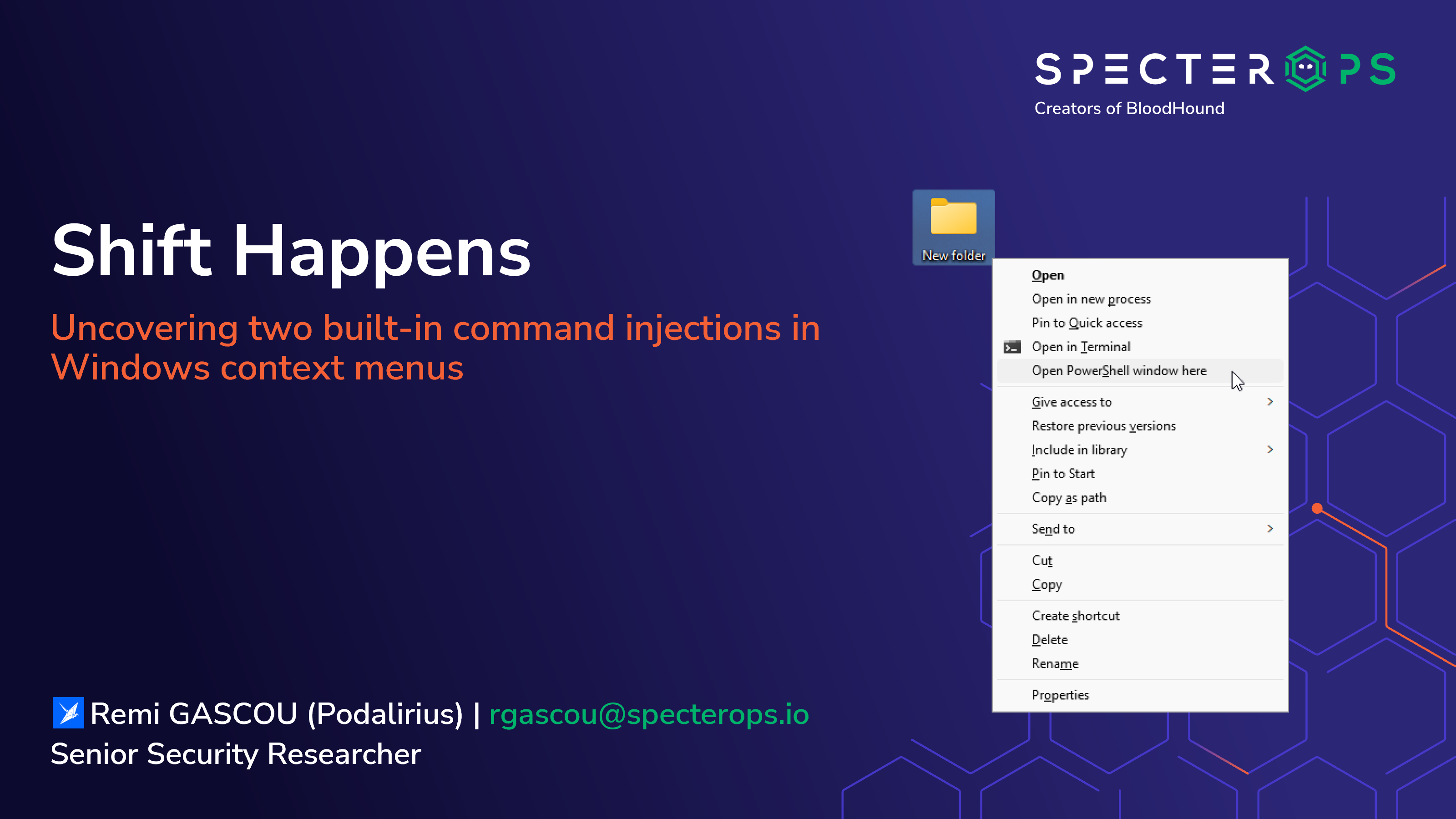
演示Windows右键菜单中两个内置命令注入漏洞的多种利用场景和幻灯片资料。
Stars: 9 | Forks: 1
## 幻灯片
本次演讲的幻灯片可以在这里找到:[SpecterOps - Shift Happens - Uncovering two builtin command injections in Windows context menus .pdf](./SpecterOps%20-%20Shift%20Happens%20-%20Uncovering%20two%20builtin%20command%20injections%20in%20Windows%20context%20menus%20.pdf)
## 场景
- [SH01 - 名称中带有 payload 的文件夹](./Scenarios/SH01%20-%20Folder%20with%20payload%20in%20its%20name/)
- [SH02 - 指向名称中带有 payload 的文件夹的快捷方式](./Scenarios/SH02%20-%20Shortcut%20to%20a%20folder%20with%20payload%20in%20its%20name/)
- [SH03 - 名称中带有 payload 的文件夹的 explorer 窗口背景](./Scenarios/SH03%20-%20Background%20of%20the%20explorer%20window%20of%20a%20folder%20with%20a%20payload%20in%20its%20name/)
- [SH04 - 父级文件夹中带有 payload 的文件夹的 explorer 窗口背景](./Scenarios/SH04%20-%20Background%20of%20the%20explorer%20window%20of%20a%20folder%20with%20a%20payload%20in%20one%20of%20its%20parent%27s%20folders/)
- [SH05 - 名称中带有 payload 的用户](./Scenarios/SH05%20-%20A%20user%20with%20a%20payload%20in%20its%20name/)
- [SH06 - 自带 payload (exe)](./Scenarios/SH06%20-%20Bring%20your%20own%20payload%20%28exe%29/)
- [SH07 - 自带 payload (ps 脚本)](./Scenarios/SH07%20-%20Bring%20your%20own%20payload%20%28ps%20script%29/)
## 贡献
如果您有其他想要提出的场景,欢迎随时提交 pull request。
标签:AI合规, Conpot, DNS 解析, IPv6, PoC, PowerShell, SpecterOps, Windows安全, 右键菜单, 命令注入, 恶意软件, 搜索语句(dork), 数据展示, 暴力破解, 本地提权, 漏洞分析, 红队, 绕过防御, 网络安全, 路径探测, 隐私保护