DurgaRamireddy/Phishing-Simulation-SOC-Investigation-Lab
GitHub: DurgaRamireddy/Phishing-Simulation-SOC-Investigation-Lab
一个完整的钓鱼模拟与SOC调查实验环境,使用GoPhish执行凭据窃取攻击,通过Splunk分析Windows EventID 4688进程创建日志来检测和调查钓鱼执行行为。
Stars: 0 | Forks: 0
# 钓鱼模拟与 SOC 调查实验
一个端到端的钓鱼模拟和 SOC 调查实验环境,构建于隔离的 VMware 环境中,部署 GoPhish 攻击者基础设施,针对 Windows 受害者执行凭据窃取活动,并使用 Splunk 和 Windows Security 事件日志调查完整的攻击链。
**MITRE ATT&CK:** T1566.002 · T1204.001 · T1078 · T1056.003
**Tools:** GoPhish · Splunk Enterprise 9.3.2 · Splunk Universal Forwarder · VMware
## 实验架构
```
┌─────────────────────────────────────────────────────┐
│ Host-Only Network: 192.168.255.0/24 │
│ │
│ ┌──────────────────┐ ┌──────────────────────┐ │
│ │ Ubuntu VM │ │ Windows 10 VM │ |
│ │ 192.168.255.131 │◄─────│ 192.168.255.132 | │
│ │ │ │ │ │
│ │ • Splunk 9.3.2 │ │ • Victim Endpoint │ │
│ │ • GoPhish 0.12.1│ │ • SUF 10.2.1 │ │
│ │ (Attacker Infra)│ │ • Log Source │ │
│ └──────────────────┘ └──────────────────────┘ │
│ │
| │
│ │
└─────────────────────────────────────────────────────┘
```
**日志管道:** Windows 10 -> Splunk Universal Forwarder (端口 9997) -> Ubuntu 上的 Splunk Enterprise
## 攻击链
```
[1] SETUP [2] DELIVERY [3] EXECUTION [4] CAPTURE
GoPhish deployed -> Phishing email -> Victim clicks -> Credentials
on Ubuntu crafted with link at harvested:
with fake IT spoofed sender 22:50:44 john.doe /
portal page and urgent CTA Edge from Password123
explorer.exe
```

## MITRE ATT&CK 映射
| Technique | ID | Tactic | Evidence |
|---|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | Initial Access | GoPhish campaign with spoofed IT identity |
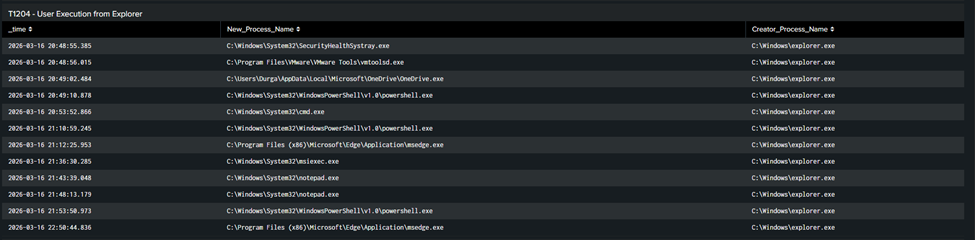
| User Execution: Malicious Link | T1204.001 | Execution | Edge spawned by explorer.exe at 22:50:44 (EventID 4688) |
| Valid Accounts | T1078 | Defense Evasion | Harvested credentials captured by GoPhish |
| Web Portal Capture | T1056.003 | Credential Access | Fake login form submitted to attacker server |
## 关键取证发现
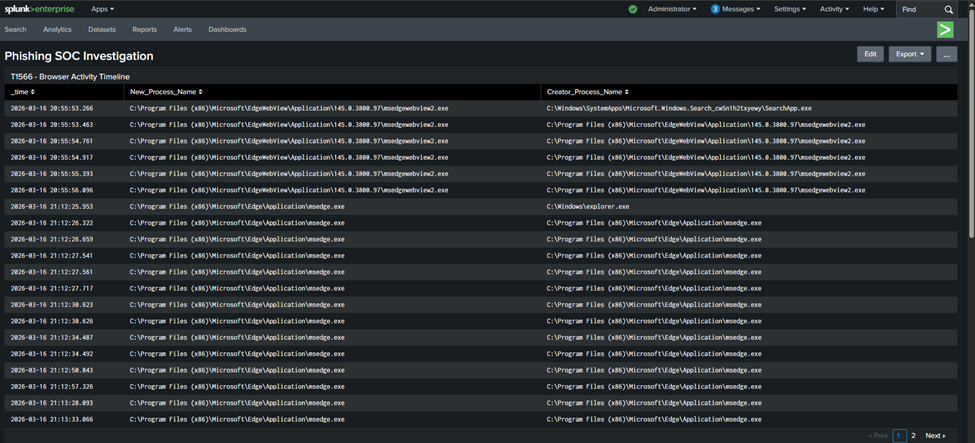
关键的 IOC 是 **Microsoft Edge 直接从 `explorer.exe` 启动**,通过 Windows Security EventID 4688 捕获:
```
Time: 2026-03-16 22:50:44
Process: C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
Parent: C:\Windows\explorer.exe
Host: DESKTOP-FL9KRGR
```
这种父子关系是一个可靠的钓鱼执行信号,与其他进程触发的正常浏览器启动截然不同。它确认了用户与钓鱼链接的交互,而无需任何网络层面的可见性。
## Splunk 检测查询 (SPL)
### T1566 - 浏览器活动时间线
```
index=main host="DESKTOP-FL9KRGR" EventCode=4688 New_Process_Name="*msedge*"
| table _time, New_Process_Name, Creator_Process_Name
| sort _time
```
### T1204 - 来自 Explorer 的用户执行 (关键 IOC)
```
index=main host="DESKTOP-FL9KRGR" EventCode=4688 Creator_Process_Name="*explorer*"
| table _time, New_Process_Name, Creator_Process_Name
| sort _time
```
### T1078 - 账户登录事件
```
index=main host="DESKTOP-FL9KRGR" EventCode=4624
| table _time, Account_Name, Logon_Type, Source_Network_Address
| sort _time
```
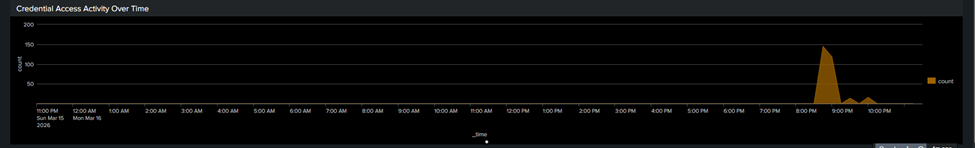
### 凭据访问活动随时间变化
```
index=main host="DESKTOP-FL9KRGR" EventCode=5379
| timechart count span=15m
```
## Splunk 仪表板
4 面板 SOC 调查 dashboard,将每个检测映射到 MITRE ATT&CK 技术:

## 入侵指标 (IOCs)
| Type | Value | Context |
|---|---|---|
| IP | 192.168.255.131 | GoPhish phishing server |
| URL | `http://192.168.255.131/?rid=SrjXtqB` | Phishing landing page with campaign ID |
| Email | it-support@company-internal.com | Spoofed sender identity |
| Credentials | john.doe@company-internal.com / Password123 | Harvested credentials |
| Process | msedge.exe spawned by explorer.exe | Phishing click indicator (EventID 4688) |
## 检测缺口与经验教训
**发现的缺口:**
- 没有网络层面的 URL 可见性 - Sysmon EventID 3 或 network tap 可以捕获访问的实际钓鱼 URL。进程创建日志确认了执行,但未确认目的地。
- 在默认审计策略下,EventID 5379 字段值(`Target_Name`, `User_Name`)为空 - 需要高级审计策略配置才能进行完整的凭据访问日志记录。
**有效的方法:**
- 通过端口 9997 的 Splunk Universal Forwarder 全程保持稳定(由于在此 VMware 环境中持续出现 `code 17 - globally disabled` 错误,放弃了 HEC)
- EventID 4688 进程创建日志提供了足够的取证证据来确认钓鱼执行,而无需任何网络可见性
- GoPhish dashboard 在攻击者侧提供了凭据捕获的即时确认
## 生产环境检测规则
```
// Alert: Browser spawned by explorer.exe outside business hours
index=main EventCode=4688
(New_Process_Name="*chrome*" OR New_Process_Name="*msedge*" OR New_Process_Name="*firefox*")
Creator_Process_Name="*explorer*"
| eval hour=strftime(_time, "%H")
| where hour < 8 OR hour > 18
| stats count by host, New_Process_Name, _time
// Alert: Credential manager access spike
index=main EventCode=5379
| bucket _time span=5m
| stats count by _time, host
| where count > 50
```
## 防御建议
| Control | Purpose |
|---|---|
| MFA on all accounts | Harvested passwords become useless without second factor |
| Email security gateway (Proofpoint, Mimecast) | URL rewriting and sandboxing before delivery |
| DNS filtering (Cisco Umbrella) | Block phishing domains at resolution |
| Sysmon with SwiftOnSecurity config | Network connection logging (EventID 3) for URL visibility |
| Regular phishing simulation training | Build user resilience against social engineering |
## 关键要点
本实验表明,仅凭进程创建日志 (EventID 4688) 就足以确认钓鱼执行,explorer.exe 与浏览器之间的父子关系是一个可靠且低噪声的信号,不需要网络可见性。它还强化了为什么 MFA 是对抗凭据窃取攻击最有效的单一控制措施:无论钓鱼页面多么具有说服力,如果没有第二因素,捕获的密码将毫无价值。
## 项目结构
```
├── README.md
├── Phishing_SOC_Incident_Report.docx
└── splunk/
└── dashboard_phishing_soc.xml
```
## 相关项目
[Splunk HOME SOC 检测实验](https://github.com/DurgaRamireddy/Splunk-HOME-SOC-Detection-Lab---End-to-End-Alert-Lifecycle) - 完整的 SOC Tier 1 告警生命周期,包括暴力破解、PowerShell 持久化检测和 4 面板 dashboard。
**作者:** Durga Sai Sri Ramireddy | MS Cybersecurity, University of Houston
[](https://linkedin.com/in/durga-ramireddy)
[](https://github.com/DurgaRamireddy)
标签:ATT&CK模拟, Cloudflare, Conpot, EventID 4688, GoPhish, MITRE ATT&CK, SOC Lab, SOC调查, Sysmon, VMware, Windows事件日志, Windows安全, 凭证收集, 安全运营中心, 数据展示, 端点检测, 红队, 网络安全实验, 网络映射, 网络靶场, 进程分析