kodurusairam/azure-sentinel-soc-lab
GitHub: kodurusairam/azure-sentinel-soc-lab
这是一个 Microsoft Sentinel SOC 实验室项目,演示如何在 Azure 上部署云原生 SIEM 并使用 KQL 进行威胁检测与事件响应。
Stars: 0 | Forks: 0
# 🛡️ Microsoft Sentinel SOC 实验室




## 🏗️ 架构

## 📋 项目概览
| 详情 | 值 |
|--------|-------|
| 平台 | Microsoft Azure |
| SIEM | Microsoft Sentinel |
| 工作区 | sentinal-workspace |
| 区域 | 印度中部 |
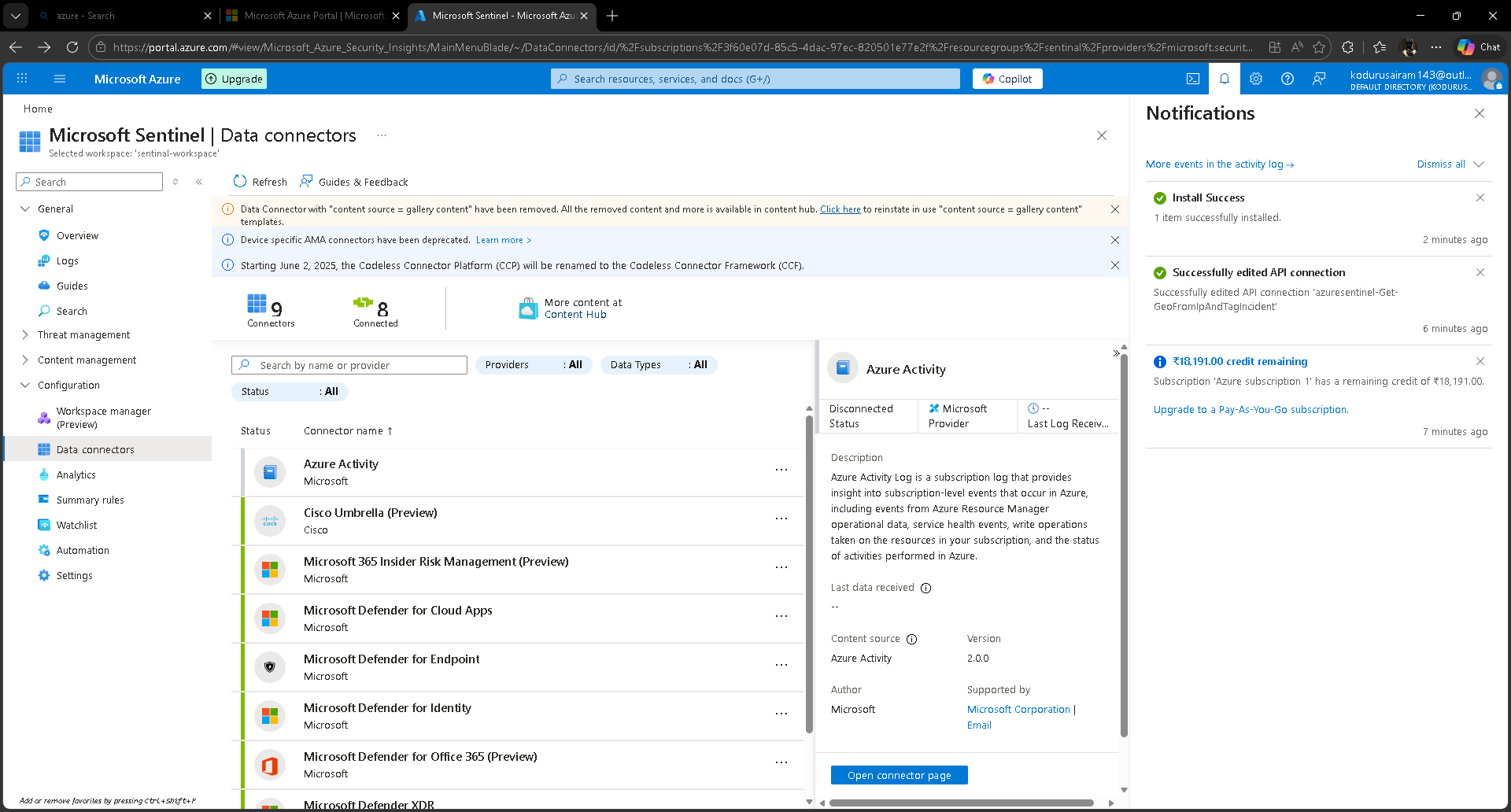
| 数据连接器 | 8 个 (培训实验室) + Azure Activity (手动) |
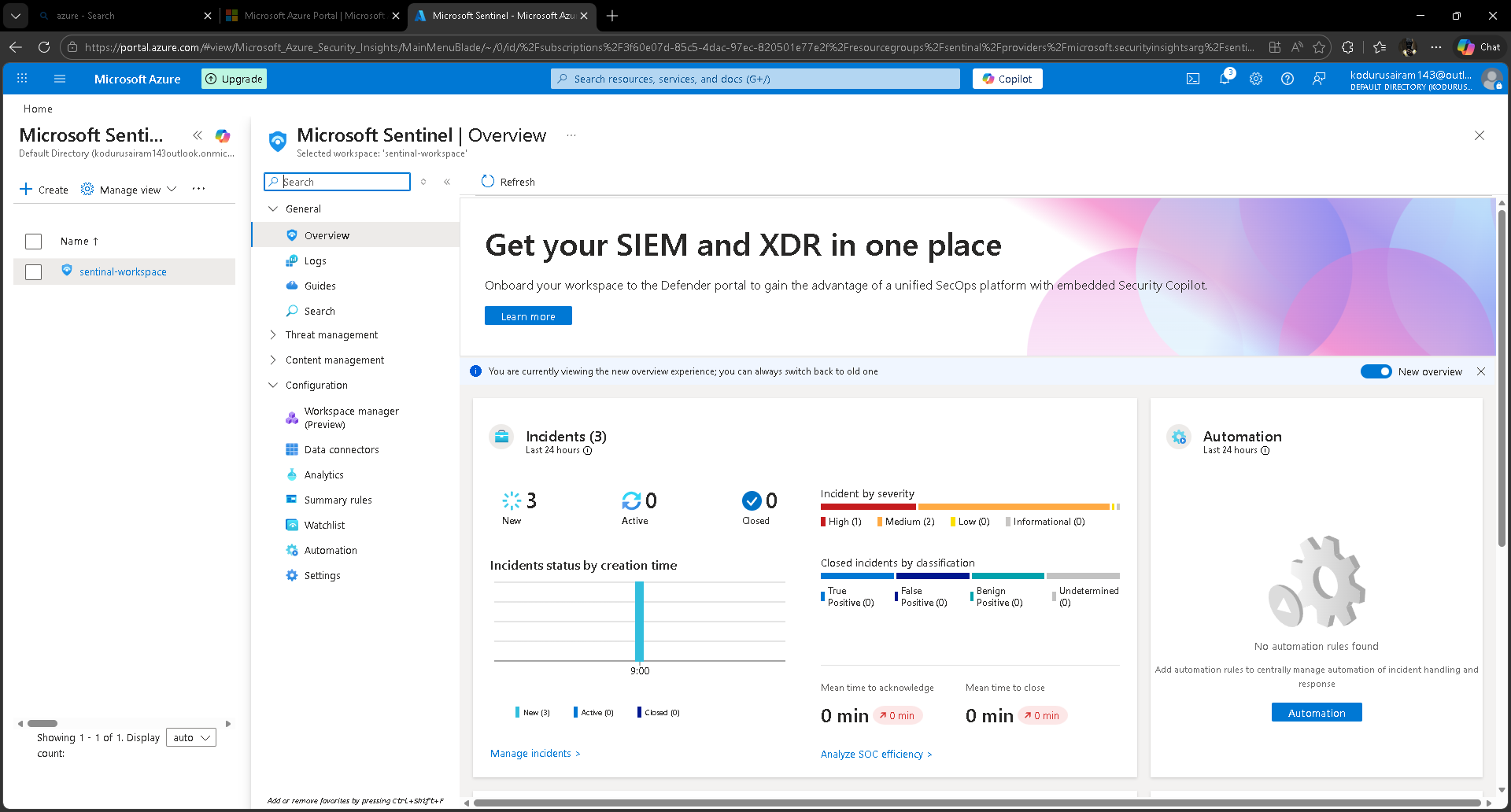
| 生成的事件 | 3 个 (1 个高危, 2 个中危) |
| KQL 查询 | 4 条 SOC 检测查询 |
## 🔧 实验室设置
### Log Analytics Workspace
- 创建资源组:`sentinal-rg`
- 部署 Log Analytics Workspace:`sentinal-workspace` (印度中部)
### 2. Microsoft Sentinel 部署
- 将 Sentinel 添加到 `sentinal-workspace`
- 从 Content Hub 安装 Microsoft Sentinel Training Lab Solution
- 培训实验室自动配置了 8 个数据连接器
- Azure Activity 连接器断开连接 — 已手动重新配置
### 3. 生成的事件
- 培训实验室攻击模拟自动生成 3 个实时事件
- 1 个高危严重性,2 个中危严重性
## 🔍 KQL 检测查询
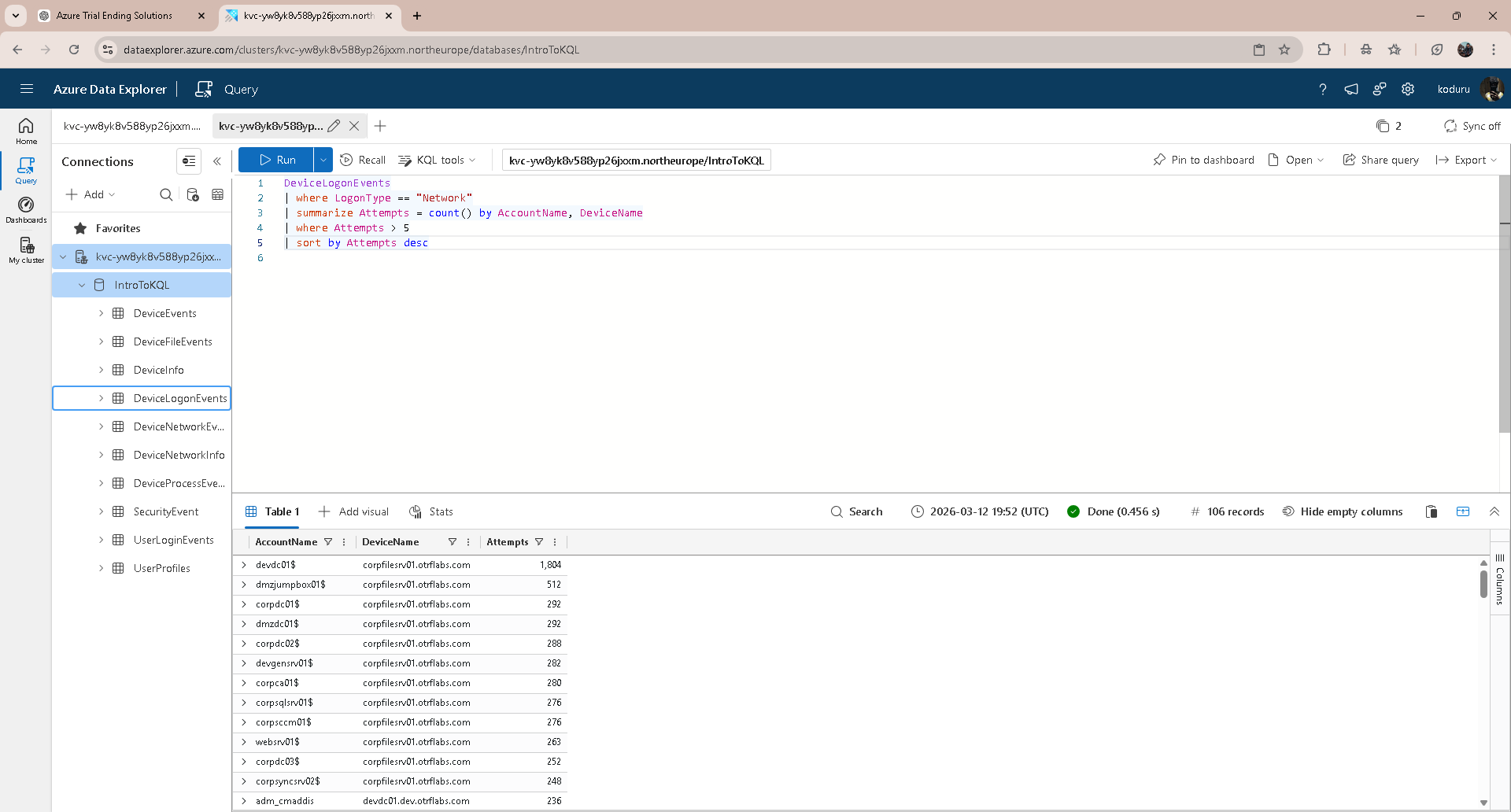
### 1. 暴力破解检测
```
DeviceLogonEvents
| where LogonType == "Network"
| summarize Attempts = count() by AccountName, DeviceName
| where Attempts > 5
| sort by Attempts desc
```
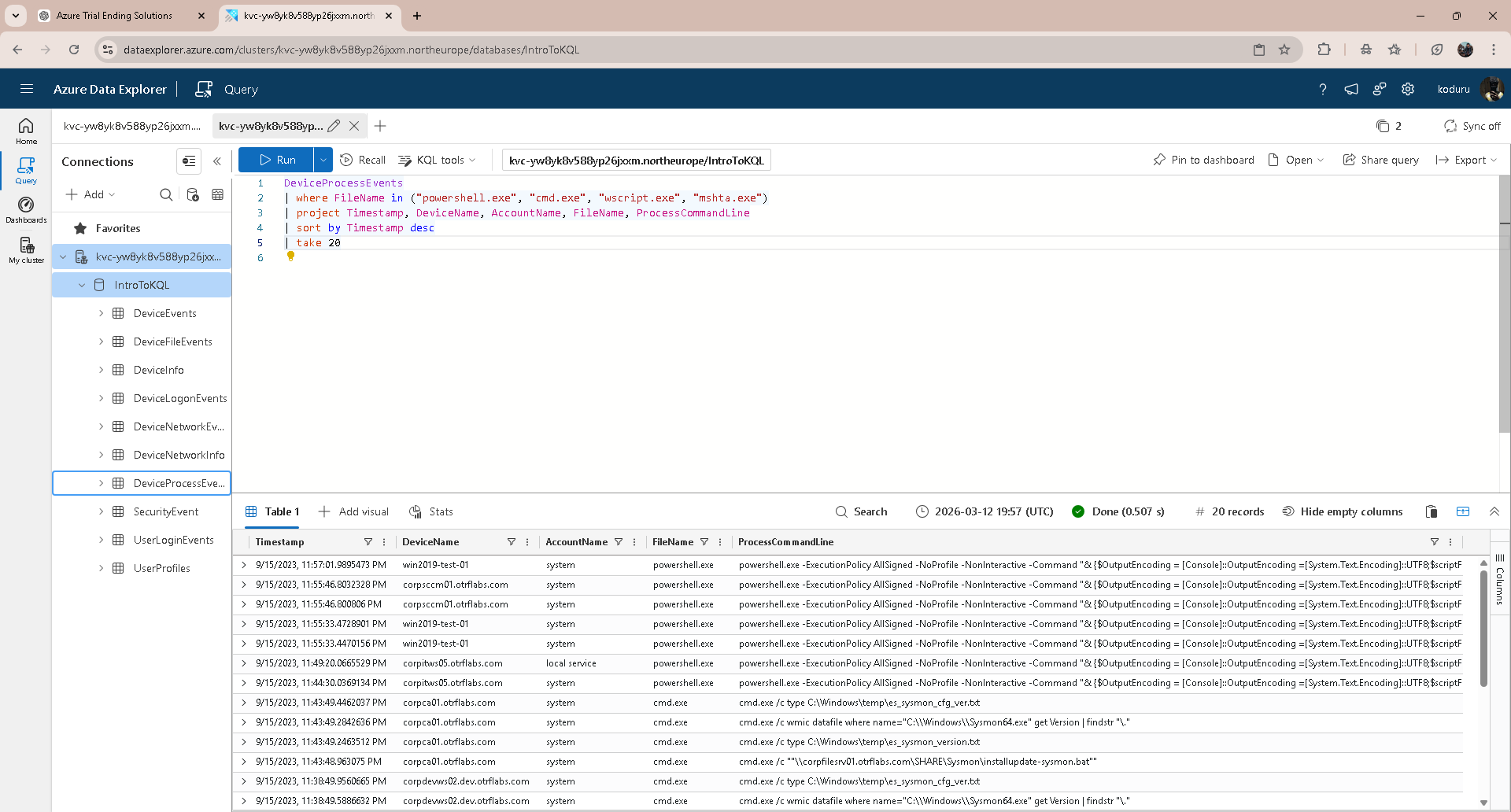
### 2. 可疑进程执行 (LOLBins)
```
DeviceProcessEvents
| where FileName in ("powershell.exe", "cmd.exe", "wscript.exe", "mshta.exe")
| project Timestamp, DeviceName, AccountName, FileName, ProcessCommandLine
| sort by Timestamp desc
| take 20
```
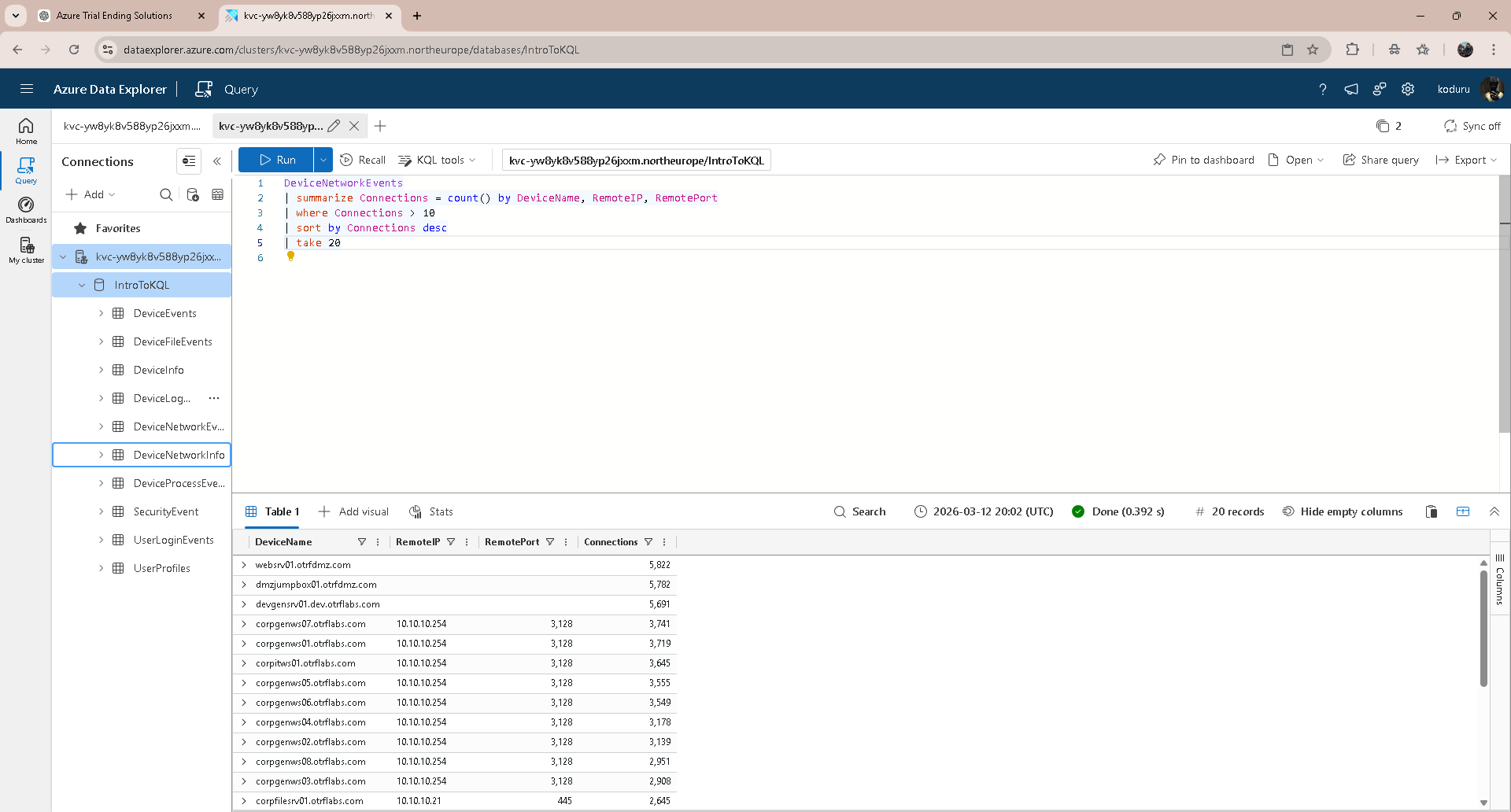
### 3. 网络信标 / C2 检测
```
DeviceNetworkEvents
| summarize Connections = count() by DeviceName, RemoteIP, RemotePort
| where Connections > 10
| sort by Connections desc
| take 20
```
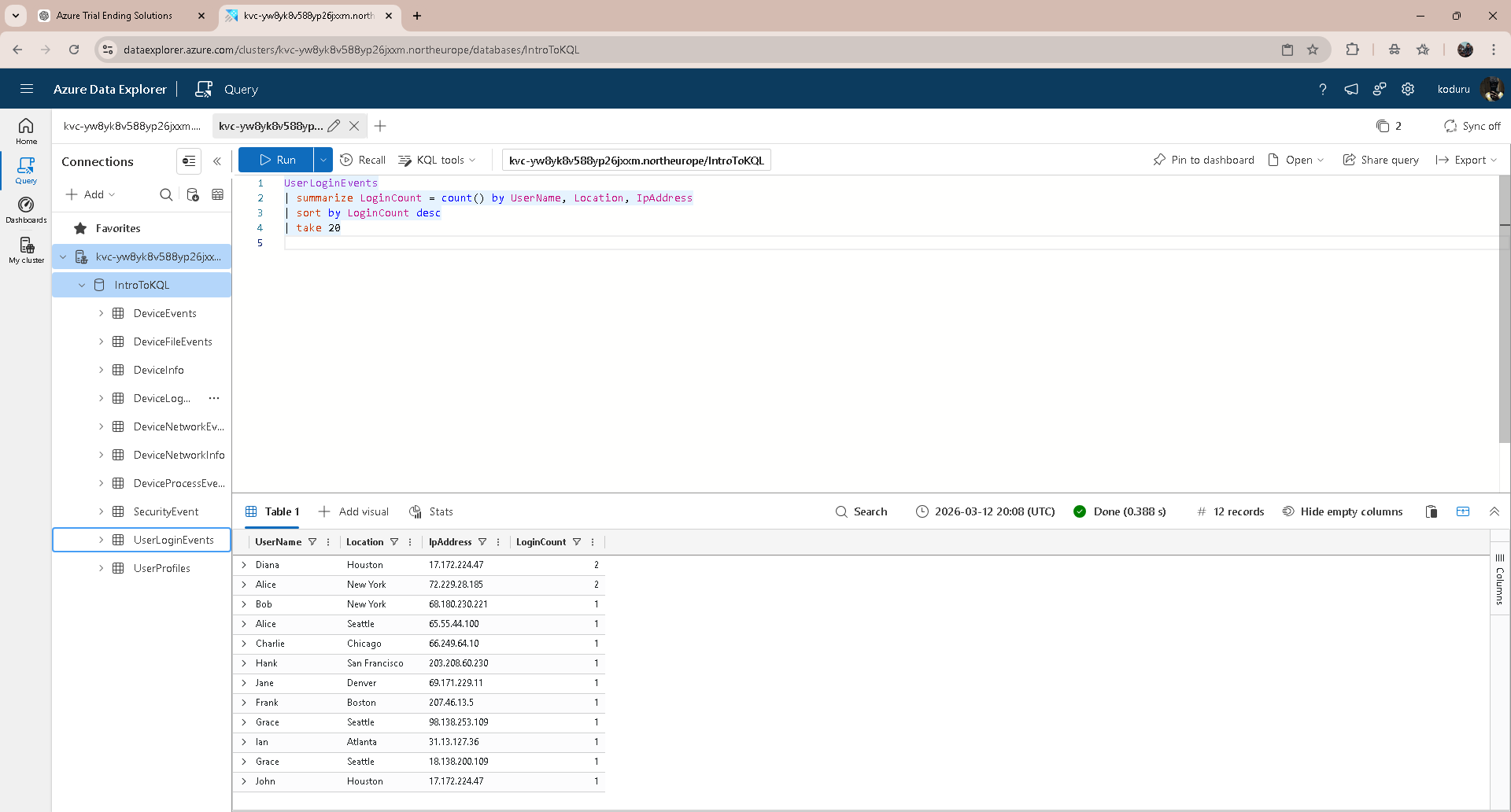
### 4. 不可能移动 / 登录异常
```
UserLoginEvents
| summarize LoginCount = count() by UserName, Location, IPAddress
| sort by LoginCount desc
| take 20
```
## 📸 截图
### Sentinel 概览 — 实时事件
### 数据连接器
### KQL — 暴力破解检测
### KQL — 可疑进程执行
### KQL — 网络信标
### KQL — 登录异常
## 🛠️ 展示技能
- Microsoft Azure — 资源组、Log Analytics、订阅
- Microsoft Sentinel — 部署、数据连接器、事件管理
- KQL — summarize、where、project、sort、dcount、make_set
- 威胁检测 — 暴力破解、LOLBins、C2 信标、不可能移动
- SOC 工作流 — 事件分类、严重性定级、威胁追踪
## 📄 文档
包含截图的完整项目文档请见 [Azure-Sentinel-SOC-Threat-Hunting-Lab.pdf](Azure-Sentinel-SOC-Threat-Hunting-Lab.pdf)
## 👤 作者
**Sairam Koduru**
SOC 分析师 | TryHackMe Top 1% | [github.com/kodurusairam](https://github.com/kodurusairam)
标签:Azure, IP 地址批量处理, KQL, LOLBins, Microsoft Sentinel, TGT, 免杀技术, 可疑进程监控, 命令与控制, 安全实验室, 安全编排自动化响应, 安全运营中心, 攻防演练, 数据连接器, 日志分析工作区, 暴力破解检测, 红队行动, 网络安全, 网络映射, 速率限制, 隐私保护