SungjunCho/PCAP-Analyzer
GitHub: SungjunCho/PCAP-Analyzer
一款 AI 辅助的 PCAP 流量分析工具,能够自动解析网络数据包并生成 Snort 检测规则草案,帮助蓝队加速检测工程工作流。
Stars: 0 | Forks: 0
# PCAP-Analyzer
PCAP Analyzer – AI 辅助检测工程工具
## ✨ v2.1.0 版本更新
### 🔍 增强的检测引擎
- **基于关键词的模式检测**:自动检测攻击模式(Log4j, SQLi, XSS 等)
- **特定协议规则生成**:针对 HTTP, DNS, FTP, TELNET, SMTP 的专用 Snort 规则
- **白名单引擎**:过滤合法流量并减少误报
### 🛡️ 高级攻击模式检测
- Log4j Shell 攻击:`${jndi:ldap://}` 模式检测
- Web 应用攻击:SQL 注入、XSS、路径遍历
- 协议滥用:FTP 凭据泄露、SMTP 枚举、Telnet 检测
### 📊 新增功能
- **关键词管理 UI**:轻松管理检测模式
- **全局白名单**:针对合法流量的预配置排除规则
- **协议统计**:实时协议分布分析
- **HTTPS 流量过滤**:自动排除 443 端口流量
### 🎯 提升准确性
- 通过多层检测减少误报
- 内容大小优化(3-40 字节)
- 基于模式的评分系统
- 消除重复规则
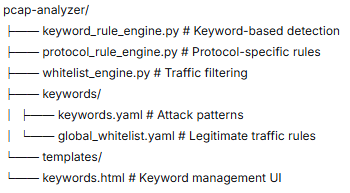
### 📁 新文件结构
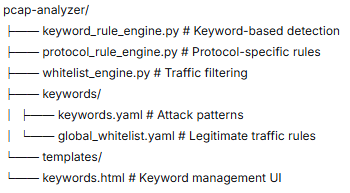 text
### 🔧 快速开始
```
# 安装依赖
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 访问 Web 界面
http://127.0.0.1:5000
Overview
This project presents an experimental Detection Engineering Automation Framework designed to support IPS/IDS rule drafting workflows.
The system analyzes uploaded PCAP files, extracts full payload data, detects suspicious patterns, and automatically generates draft Snort rules. Additionally, it provides payload visualization (Hex + ASCII), rule specificity scoring, and false positive estimation.
This tool does not replace detection engineers, but assists in accelerating the initial rule drafting process.
A web app that analyzes PCAP files and generates Snort rules with false positive scoring.
## 🚀 快速开始
```bash
# 克隆并安装
git clone https://github.com/yourusername/pcap-analyzer.git
cd pcap-analyzer
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 或运行单文件版本
python app_single.py
Then open http://127.0.0.1:5000
📦 Two Versions Available
Feature app_single.py (v1.0) app_multi.py (v2.0) ⭐
File Upload Single file only Multiple files
Drag & Drop ❌ ✅
Progress Bar ❌ ✅
Export Rules ❌ ✅ (single file or ZIP)
Max File Size 100MB 500MB
Status ⚠️ Deprecated ✅ Recommended
📁 Project Structure
text
pcap-analyzer/
├── app_multi.py # ✅ New multi-file version
├── app_single.py # ⚠️ Legacy single-file version
├── requirements.txt # Dependencies
├── templates/
│ ├── multi_upload.html # UI for v2.0
│ └── index.html # UI for v1.0
└── static/
└── style.css # Shared styles
🎯 Which Version Should I Use?
Use app_multi.py (v2.0) if you need:
Multiple file analysis
Batch processing
Export features
Better performance
Use app_single.py (v1.0) if you:
Need quick single file check
Have limited resources
Want minimal interface
🔧 Quick Example
Multi-file version:
bash
python app_multi.py
# 拖放多个 .pcap 文件
# 点击 “Analyze”
# 下载结果为 ZIP
Single-file version:
bash
python app_single.py
# 选择一个 .pcap 文件
# 查看基本结果
📝 Requirements
text
Flask==2.3.0
scapy==2.5.0
🤝 Contributing
Fork it
Create feature branch
Commit changes
Push to branch
Open Pull Request
```
text
### 🔧 快速开始
```
# 安装依赖
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 访问 Web 界面
http://127.0.0.1:5000
Overview
This project presents an experimental Detection Engineering Automation Framework designed to support IPS/IDS rule drafting workflows.
The system analyzes uploaded PCAP files, extracts full payload data, detects suspicious patterns, and automatically generates draft Snort rules. Additionally, it provides payload visualization (Hex + ASCII), rule specificity scoring, and false positive estimation.
This tool does not replace detection engineers, but assists in accelerating the initial rule drafting process.
A web app that analyzes PCAP files and generates Snort rules with false positive scoring.
## 🚀 快速开始
```bash
# 克隆并安装
git clone https://github.com/yourusername/pcap-analyzer.git
cd pcap-analyzer
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 或运行单文件版本
python app_single.py
Then open http://127.0.0.1:5000
📦 Two Versions Available
Feature app_single.py (v1.0) app_multi.py (v2.0) ⭐
File Upload Single file only Multiple files
Drag & Drop ❌ ✅
Progress Bar ❌ ✅
Export Rules ❌ ✅ (single file or ZIP)
Max File Size 100MB 500MB
Status ⚠️ Deprecated ✅ Recommended
📁 Project Structure
text
pcap-analyzer/
├── app_multi.py # ✅ New multi-file version
├── app_single.py # ⚠️ Legacy single-file version
├── requirements.txt # Dependencies
├── templates/
│ ├── multi_upload.html # UI for v2.0
│ └── index.html # UI for v1.0
└── static/
└── style.css # Shared styles
🎯 Which Version Should I Use?
Use app_multi.py (v2.0) if you need:
Multiple file analysis
Batch processing
Export features
Better performance
Use app_single.py (v1.0) if you:
Need quick single file check
Have limited resources
Want minimal interface
🔧 Quick Example
Multi-file version:
bash
python app_multi.py
# 拖放多个 .pcap 文件
# 点击 “Analyze”
# 下载结果为 ZIP
Single-file version:
bash
python app_single.py
# 选择一个 .pcap 文件
# 查看基本结果
📝 Requirements
text
Flask==2.3.0
scapy==2.5.0
🤝 Contributing
Fork it
Create feature branch
Commit changes
Push to branch
Open Pull Request
```
 text
### 🔧 快速开始
```
# 安装依赖
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 访问 Web 界面
http://127.0.0.1:5000
Overview
This project presents an experimental Detection Engineering Automation Framework designed to support IPS/IDS rule drafting workflows.
The system analyzes uploaded PCAP files, extracts full payload data, detects suspicious patterns, and automatically generates draft Snort rules. Additionally, it provides payload visualization (Hex + ASCII), rule specificity scoring, and false positive estimation.
This tool does not replace detection engineers, but assists in accelerating the initial rule drafting process.
A web app that analyzes PCAP files and generates Snort rules with false positive scoring.
## 🚀 快速开始
```bash
# 克隆并安装
git clone https://github.com/yourusername/pcap-analyzer.git
cd pcap-analyzer
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 或运行单文件版本
python app_single.py
Then open http://127.0.0.1:5000
📦 Two Versions Available
Feature app_single.py (v1.0) app_multi.py (v2.0) ⭐
File Upload Single file only Multiple files
Drag & Drop ❌ ✅
Progress Bar ❌ ✅
Export Rules ❌ ✅ (single file or ZIP)
Max File Size 100MB 500MB
Status ⚠️ Deprecated ✅ Recommended
📁 Project Structure
text
pcap-analyzer/
├── app_multi.py # ✅ New multi-file version
├── app_single.py # ⚠️ Legacy single-file version
├── requirements.txt # Dependencies
├── templates/
│ ├── multi_upload.html # UI for v2.0
│ └── index.html # UI for v1.0
└── static/
└── style.css # Shared styles
🎯 Which Version Should I Use?
Use app_multi.py (v2.0) if you need:
Multiple file analysis
Batch processing
Export features
Better performance
Use app_single.py (v1.0) if you:
Need quick single file check
Have limited resources
Want minimal interface
🔧 Quick Example
Multi-file version:
bash
python app_multi.py
# 拖放多个 .pcap 文件
# 点击 “Analyze”
# 下载结果为 ZIP
Single-file version:
bash
python app_single.py
# 选择一个 .pcap 文件
# 查看基本结果
📝 Requirements
text
Flask==2.3.0
scapy==2.5.0
🤝 Contributing
Fork it
Create feature branch
Commit changes
Push to branch
Open Pull Request
```
text
### 🔧 快速开始
```
# 安装依赖
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 访问 Web 界面
http://127.0.0.1:5000
Overview
This project presents an experimental Detection Engineering Automation Framework designed to support IPS/IDS rule drafting workflows.
The system analyzes uploaded PCAP files, extracts full payload data, detects suspicious patterns, and automatically generates draft Snort rules. Additionally, it provides payload visualization (Hex + ASCII), rule specificity scoring, and false positive estimation.
This tool does not replace detection engineers, but assists in accelerating the initial rule drafting process.
A web app that analyzes PCAP files and generates Snort rules with false positive scoring.
## 🚀 快速开始
```bash
# 克隆并安装
git clone https://github.com/yourusername/pcap-analyzer.git
cd pcap-analyzer
pip install -r requirements.txt
# 运行多文件版本(推荐)
python app_multi.py
# 或运行单文件版本
python app_single.py
Then open http://127.0.0.1:5000
📦 Two Versions Available
Feature app_single.py (v1.0) app_multi.py (v2.0) ⭐
File Upload Single file only Multiple files
Drag & Drop ❌ ✅
Progress Bar ❌ ✅
Export Rules ❌ ✅ (single file or ZIP)
Max File Size 100MB 500MB
Status ⚠️ Deprecated ✅ Recommended
📁 Project Structure
text
pcap-analyzer/
├── app_multi.py # ✅ New multi-file version
├── app_single.py # ⚠️ Legacy single-file version
├── requirements.txt # Dependencies
├── templates/
│ ├── multi_upload.html # UI for v2.0
│ └── index.html # UI for v1.0
└── static/
└── style.css # Shared styles
🎯 Which Version Should I Use?
Use app_multi.py (v2.0) if you need:
Multiple file analysis
Batch processing
Export features
Better performance
Use app_single.py (v1.0) if you:
Need quick single file check
Have limited resources
Want minimal interface
🔧 Quick Example
Multi-file version:
bash
python app_multi.py
# 拖放多个 .pcap 文件
# 点击 “Analyze”
# 下载结果为 ZIP
Single-file version:
bash
python app_single.py
# 选择一个 .pcap 文件
# 查看基本结果
📝 Requirements
text
Flask==2.3.0
scapy==2.5.0
🤝 Contributing
Fork it
Create feature branch
Commit changes
Push to branch
Open Pull Request
```
标签:AI安全, AMSI绕过, Chat Copilot, CISA项目, DNS枚举, Flask, IP 地址批量处理, Log4j, PCAP分析, PE 加载器, Python, Snort规则生成, Web安全, XSS, 入侵检测系统, 协议分析, 威胁检测, 安全数据湖, 无后门, 权限提升, 流量可视化, 漏洞情报, 网络安全, 网络安全工具, 自动化规则生成, 蓝队分析, 误报过滤, 路径遍历, 逆向工具, 隐私保护