brianchaplow/HomeLab-SOC-v2
GitHub: brianchaplow/HomeLab-SOC-v2
在家庭实验室环境中构建的企业级安全运营中心参考架构,集成了SIEM、入侵检测、威胁情报自动化和紫队演练环境。
Stars: 0 | Forks: 0
# 🛡️ HomeLab SOC v2
[](https://opensearch.org/)
[](https://suricata.io/)
[](https://docker.com/)
[](https://cloudflare.com/)
[](https://opnsense.org/)
一个基于消费级硬件构建的生产级安全运营中心(SOC),在家庭实验室环境中展示企业级安全监控能力。
**实时基础设施:** 该 SOC 主动监控 [brianchaplow.com](https://brianchaplow.com) 和 [bytesbourbonbbq.com](https://bytesbourbonbbq.com),处理真实攻击流量并自动阻断威胁。
## 🔄 演进:v1 → v2
这是我的 HomeLab SOC 项目的**第二次迭代**。原版 ([HomeLab-SOC](https://github.com/brianchaplow/HomeLab-SOC)) 验证了概念;v2 实现了企业级架构。
| Aspect | v1 (Original) | v2 (Current) |
|--------|---------------|--------------|
| **Network** | Flat 192.168.50.0/24 | 5 VLANs (10.10.x.0/24) |
| **Firewall** | Consumer router (ASUS) | OPNsense on Protectli VP2420 |
| **Switching** | TP-Link TL-SG108E (8-port 1G) | MokerLink 10G L3 (8×10G + 4×SFP+) |
| **Traffic Capture** | Basic SPAN | Full port mirror with VLAN visibility |
| **Purple Team** | Kali only | Isolated VLAN 40 with DVWA, Juice Shop, Metasploitable |
| **AD Lab** | None | smokehouse.local (DC01 + WS01) with Sysmon |
| **IPs Blocked** | 100+ | 2,000+ |
| **Dashboards** | Basic | 4 purpose-built (SOC Overview, NIDS, Endpoint, Threat Intel) |
**为什么开发 v2?** 扁平网络适合学习,但无法模拟企业环境。适当的 VLAN 分段实现了真实的紫队演练,攻击流量被隔离、监控和记录——就像生产环境一样。
## 📊 关键指标
| Metric | Value |
|--------|-------|
| 🎯 **Suricata Rules** | 47,487 (ET Open + 10 custom) |
| 🚫 **IPs Auto-Blocked** | 2,000+ at Cloudflare edge |
| 🌐 **VLANs** | 5 (enterprise segmentation) |
| 🖥️ **Windows Events** | 83K+ across AD lab |
| 🗺️ **Countries Detected** | 15+ source countries |
| ⏱️ **Enrichment Cycle** | Every 15 minutes |
## 🏗️ 架构
流量在到达 SOC 之前经过三层安全防护:
```
┌─────────────────┐
│ INTERNET │
└────────┬────────┘
│
┌──────────────────▼──────────────────┐
│ CLOUDFLARE (Edge) │
│ │
│ • WAF & Bot Fight Mode │
│ • JA3 Fingerprinting │
│ • Auto-block API ← SOC Automation │
│ │
│ brianchaplow.com │
│ bytesbourbonbbq.com │
└──────────────────┬──────────────────┘
│
┌──────────────────▼──────────────────┐
│ GCP VM (Origin) │
│ │
│ • Apache Web Server │
│ • Fluent Bit Log Shipper │
│ • Umami Analytics │
└──────────────────┬──────────────────┘
│
Tailscale WireGuard Tunnel
│
┌──────────────────▼──────────────────┐
│ OPNsense Firewall │
│ Protectli VP2420 │
│ 10.10.10.1 │
└──────────────────┬──────────────────┘
│
┌──────────────────▼──────────────────┐
│ MokerLink 10G Switch │
│ 12-Port L3 • Port Mirror (SPAN) │
│ All VLANs → eth4 │
└──────────────────┬──────────────────┘
│
┌──────────┬──────────┬─────────┴─────────┬──────────┐
│ │ │ │ │
▼ ▼ ▼ ▼ ▼
┌─────────┐ ┌─────────┐ ┌─────────┐ ┌──────────┐ ┌─────────┐
│ VLAN 10 │ │ VLAN 20 │ │ VLAN 30 │ │ VLAN 40 │ │ VLAN 50 │
│ Mgmt │ │ SOC │ │ Lab │ │ Targets │ │ IoT │
│─────────│ │─────────│ │─────────│ │──────────│ │─────────│
│10.10.10x│ │10.10.20x│ │10.10.30x│ │10.10.40.x│ │10.10.50x│
│ │ │ │ │ │ │ │ │ │
│ PITBOSS │ │smoke- │ │ Proxmox │ │ DVWA │ │ TP-Link │
│ │ │ house │ │ pitcrew │ │ Juice │ │ Switch │
│ │ │ (QNAP) │ │ smoker │ │ Shop │ │ │
│ │ │ │ │ │ │ Meta- │ │ │
│ │ │ sear │ │ AD Lab │ │ sploit- │ │ │
│ │ │ (Kali) │ │ DC01 │ │ able │ │ │
│ │ │ │ │ WS01 │ │ │ │ │
└─────────┘ └────┬────┘ └─────────┘ └────┬─────┘ └─────────┘
│ │
│ Purple Team Attacks │
│ (Isolated) │
└───────────────────────────┘
```
### 数据流
| Flow | Path |
|------|------|
| **Web Traffic** | Internet → Cloudflare → GCP VM → Tailscale → smokehouse → OpenSearch |
| **SPAN Capture** | All VLANs → MokerLink (mirror) → smokehouse eth4 → Suricata |
| **Windows Events** | DC01/WS01 → Sysmon → Fluent Bit → OpenSearch |
| **Threat Intel** | New IP → AbuseIPDB lookup → Score ≥90 → Cloudflare auto-block |
| **Purple Team** | sear (VLAN 20) → Targets (VLAN 40) → Detection validation |
## 🌐 网络分段
| VLAN | Name | Subnet | Purpose |
|------|------|--------|---------|
| 10 | Management | 10.10.10.0/24 | Network device administration |
| 20 | SOC | 10.10.20.0/24 | smokehouse (QNAP), sear (Kali) |
| 30 | Lab | 10.10.30.0/24 | Proxmox hosts, AD domain |
| 40 | Targets | 10.10.40.0/24 | Isolated vulnerable VMs |
| 50 | IoT | 10.10.50.0/24 | Smart home (segmented) |
### 防火墙规则
| Source | Destination | Action | Purpose |
|--------|-------------|--------|---------|
| SOC (VLAN 20) | All VLANs | Allow | Monitoring access |
| Lab (VLAN 30) | Targets (VLAN 40) | Allow | Purple team attacks |
| Targets (VLAN 40) | Any | Deny | Complete isolation |
| IoT (VLAN 50) | Internet only | Allow | Block lateral movement |
### 烧烤主题命名规则 🍖
| Hostname | Role | VLAN | IP |
|----------|------|------|-----|
| **smokehouse** | QNAP NAS (SOC platform) | 20 | 10.10.20.10 |
| **sear** | Kali attack box | 20 | 10.10.20.20 |
| **PITBOSS** | Windows laptop | 10 | 10.10.10.100 |
| **pitcrew** | Proxmox (AD lab) | 30 | 10.10.30.20 |
| **smoker** | Proxmox (targets) | 30 | 10.10.30.21 |
## 🔧 组件
### SOC 技术栈 (smokehouse - 10.10.20.10)
| Container | Port | Purpose |
|-----------|------|---------|
| **OpenSearch** | 9200 | SIEM backend, log storage |
| **OpenSearch Dashboards** | 5601 | Visualization, threat hunting |
| **Suricata** | Host network | Network IDS (47,487 rules) |
| **Fluent Bit** | 5514 | Log aggregation |
| **soc-automation** | — | Enrichment, auto-blocking |
| **Zeek** | — | Network security monitor |
| **CyberChef** | 8000 | Data analysis |
| **InfluxDB** | 8086 | Time-series metrics |
| **Grafana** | 3000 | Infrastructure dashboards |
### AD 实验环境 (VLAN 30)
| VM | IP | Role |
|----|-----|------|
| DC01 | 10.10.30.40 | Domain Controller (Server 2022) |
| WS01 | 10.10.30.41 | Workstation (Windows 10) |
**Domain:** smokehouse.local
**Telemetry:** Sysmon deployed via GPO → Fluent Bit → OpenSearch
### 紫队靶机 (VLAN 40 - 隔离)
| Target | IP | Purpose |
|--------|-----|---------|
| DVWA | 10.10.40.10 | Web app vulnerabilities |
| Juice Shop | 10.10.40.11 | OWASP vulnerable app |
| Metasploitable | 10.10.40.20 | Classic practice target |
## 📈 仪表板
针对不同操作需求构建的四个专用仪表板:
### SOC 概览 (作品集首页)
高管视图,显示组合网络 + 端点覆盖范围,包含地理威胁分布和 7 天时间线。
### NIDS - 检测概览
Suricata 运行指标:告警量、热门签名、协议细分、源/目的地分析。
### 端点 - Windows 安全
来自 AD 实验室的 Windows 遥测数据:事件分布、Sysmon 覆盖范围、认证模式 (4624/4625/4672)。
### SOC - 威胁情报
外部威胁评估:AbuseIPDB 富化、自动封锁 IP 追踪、地理来源、风险评分。
## 📸 截图
## ⚡ 自动化
| Schedule | Script | Function |
|----------|--------|----------|
| Every 15 min | `enrichment.py` | Query AbuseIPDB for new IPs |
| Hourly | `autoblock.py` | Push score≥90 IPs to Cloudflare |
| 0600/1800 | `digest.py` | Watch turnover reports |
| Sunday 0800 | `digest.py --weekly` | Weekly threat summary |
**自动封锁标准:**
- AbuseIPDB 置信度分数 ≥ 90
- 最少 5 次报告
- 推送到 Cloudflare 账户级防火墙
- 自动跨所有域名封锁
**告警:** Discord webhooks + email (soc-alerts@brianchaplow.com)
## 📁 仓库结构
```
HomeLab-SOC-v2/
├── README.md
├── CHANGELOG.md # v1 → v2 migration notes
├── configs/
│ ├── .env.example # Environment template
│ ├── docker-compose.yml # Full SOC stack
│ ├── fluent-bit/
│ │ ├── fluent-bit-qnap.conf
│ │ ├── fluent-bit-vm.conf
│ │ ├── fluent-bit-windows.yaml
│ │ ├── parsers-qnap.conf
│ │ ├── parsers-vm.conf
│ │ └── sysmon_parser.lua
│ └── opensearch/
│ └── geoip-pipeline.json
├── scripts/
│ ├── soc-startup.sh # QNAP boot script
│ └── soc-automation/
│ ├── Dockerfile
│ ├── requirements.txt
│ ├── enrichment.py
│ ├── autoblock.py
│ └── digest.py
├── dashboards/
│ ├── soc-overview-portfolio.ndjson
│ ├── nids-detection-overview.ndjson
│ ├── endpoint-windows-security.ndjson
│ └── soc-threat-intelligence.ndjson
├── detection-examples/
│ ├── sqlmap-detection.md # SQLmap attack → alert walkthrough
│ └── sample-alerts.json
├── docs/
│ └── architecture.md # Detailed technical docs
└── screenshots/
├── soc-architecture-v2.png
└── dashboard-*.png
```
## 🚀 快速开始
### 前置条件
- Docker & Docker Compose
- Linux server (QNAP, Proxmox, or similar)
- Cloudflare account (free tier works)
- AbuseIPDB API key (free: 1000 checks/day)
- MaxMind GeoLite2 license (free)
### 部署
1. **克隆仓库**
git clone https://github.com/brianchaplow/HomeLab-SOC-v2.git
cd HomeLab-SOC-v2
2. **配置环境**
cp configs/.env.example configs/.env
# 使用您的 API keys 进行编辑
3. **部署技术栈**
cd configs
docker-compose up -d
4. **访问仪表板**
- OpenSearch Dashboards: `http://:5601`
- CyberChef: `http://:8000`
详细设置和 VLAN 配置请参阅 [docs/architecture.md](docs/architecture.md)。
## 🎯 紫队验证
没有验证的检测只是空想。隔离的 VLAN 40 支持攻击模拟:
```
# SQLmap 注入测试 (来自 VLAN 20 上的 sear → VLAN 40 上的 DVWA)
sqlmap -u "http://10.10.40.10/vulnerabilities/sqli/?id=1" \
--cookie="PHPSESSID=xxx;security=low" \
--batch --dbs
```
**结果:**
- Suricata 捕获了 10,000+ 条流记录
- 触发了 SQL 注入签名
- OpenSearch 中记录了完整的攻击时间线
- 验证了目标隔离(无法到达 SOC 或逃逸 VLAN 40)
完整演练请参阅 [detection-examples/sqlmap-detection.md](detection-examples/sqlmap-detection.md)。
## 🗺️ 路线图
### 已完成 (v2)
- [x] Core SIEM (OpenSearch + Fluent Bit)
- [x] Network IDS (Suricata 47K+ rules)
- [x] Automated threat intel (AbuseIPDB)
- [x] Edge auto-blocking (Cloudflare API)
- [x] GeoIP enrichment (MaxMind + CF headers)
- [x] VLAN segmentation (5 VLANs, OPNsense + MokerLink)
- [x] AD Lab with Sysmon telemetry
- [x] Purple team target range (isolated VLAN 40)
- [x] 4 purpose-built dashboards
### 进行中
- [ ] Sigma rules for Windows detection
- [ ] MITRE ATT&CK dashboard mapping
- [ ] Atomic Red Team integration
### 计划中
- [ ] Index lifecycle management
- [ ] Wazuh agent deployment
- [ ] Automated purple team playbooks
## 🛠️ 技术栈
| Category | Technologies |
|----------|-------------|
| **Firewall** | OPNsense (Protectli VP2420) |
| **Switching** | MokerLink 10G (L3, SPAN) |
| **SIEM** | OpenSearch, OpenSearch Dashboards |
| **Network Security** | Suricata, Zeek |
| **Log Pipeline** | Fluent Bit |
| **Edge Security** | Cloudflare WAF, Bot Fight Mode |
| **Threat Intel** | AbuseIPDB, MaxMind GeoLite2 |
| **Connectivity** | Tailscale (WireGuard) |
| **Containers** | Docker, Docker Compose |
| **Automation** | Python, Cron |
| **Alerting** | Discord Webhooks, Email |
## 👤 作者
**Brian Chaplow**
- 🌐 Website: [brianchaplow.com](https://brianchaplow.com)
- 💼 LinkedIn: [linkedin.com/in/brianchaplow](https://linkedin.com/in/brianchaplow)
- 🐙 GitHub: [@brianchaplow](https://github.com/brianchaplow)
- 🍖 Blog: [bytesbourbonbbq.com](https://bytesbourbonbbq.com)
## 📄 许可证
MIT License - 详见 [LICENSE](LICENSE)
## 🙏 致谢
- [Emerging Threat Open](https://rules.emergingthreats.net/) - Suricata ruleset
- [SwiftOnSecurity](https://github.com/SwiftOnSecurity/sysmon-config) - Sysmon inspiration
- [AbuseIPDB](https://abuseipdb.com) - Threat intelligence
- [MaxMind](https://maxmind.com) - GeoIP databases
点击展开仪表板截图
### SOC 概览 高管摘要,结合了 Suricata IDS 告警 (51K+)、Windows 端点事件 (83K+)、地理威胁分布和 7 天时间线。 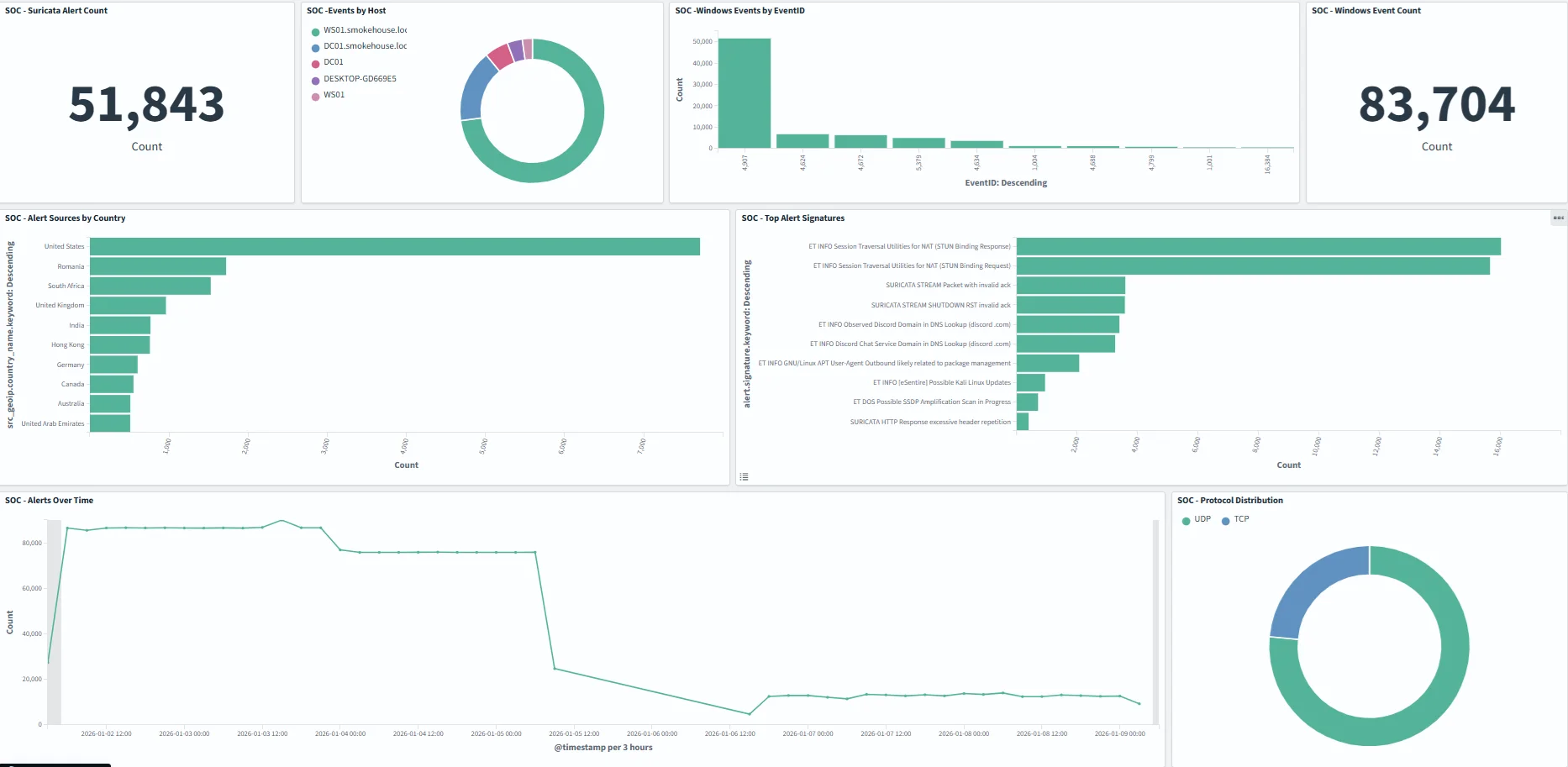 ### NIDS - 检测概览 Suricata 运行指标,显示协议分布、热门告警签名和随时间变化的告警量。 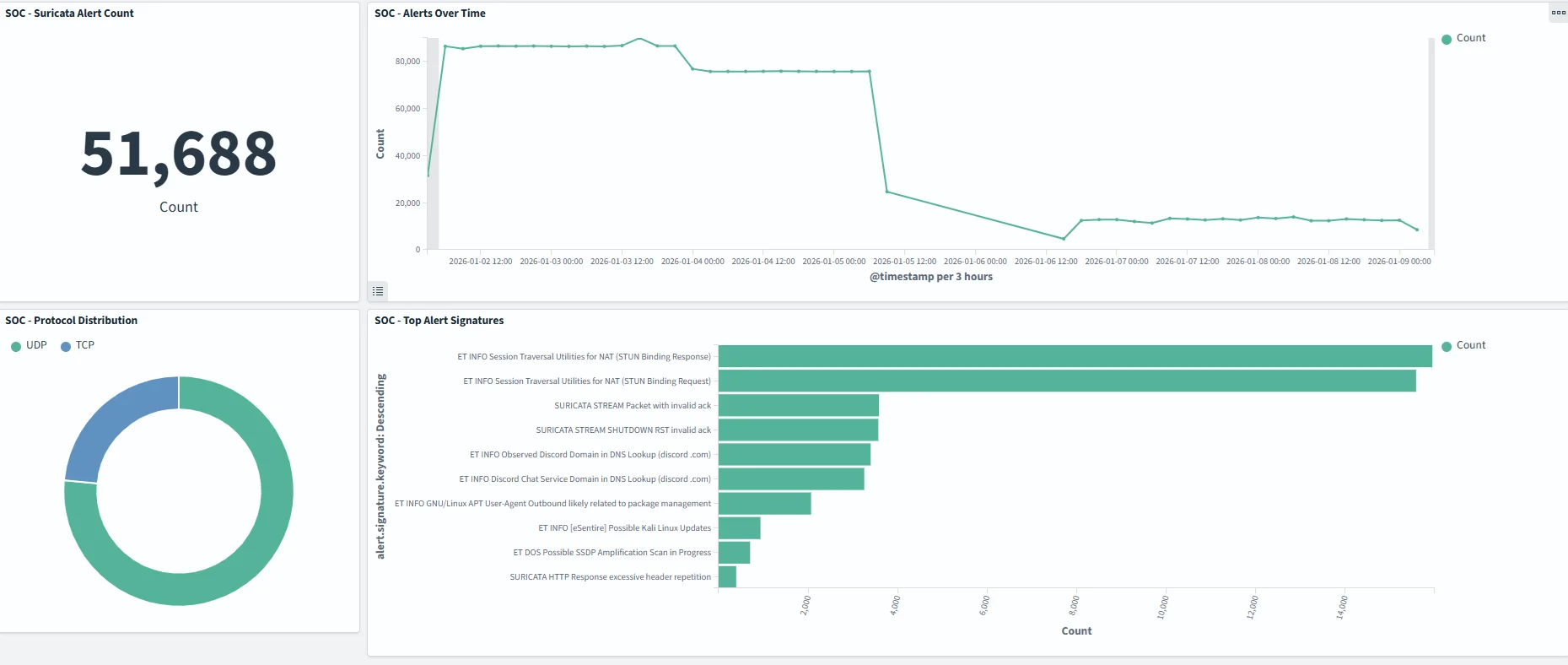 ### 端点 - Windows 安全 来自 AD 实验室 (DC01, WS01) 的 Windows 事件遥测,显示已加入域主机上的 EventID 分布。 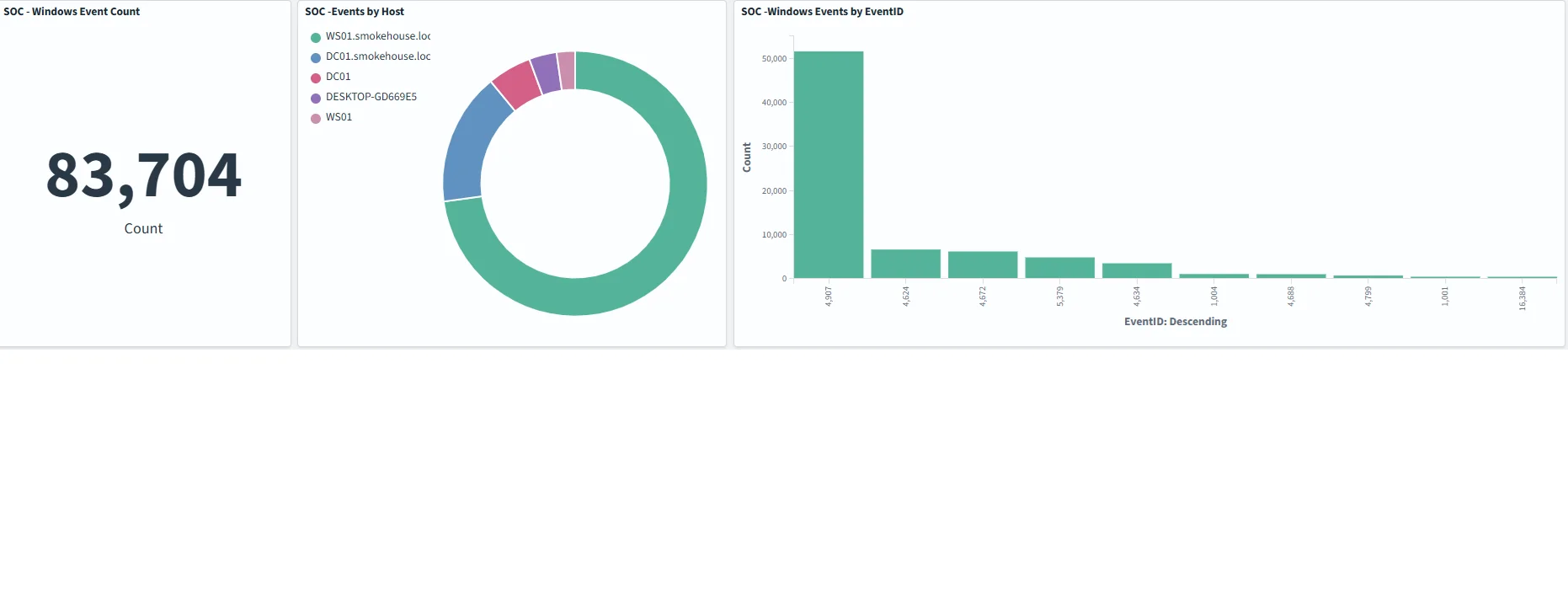 ### 威胁情报 外部威胁分析,显示主要攻击 IP、地理来源和告警计数。 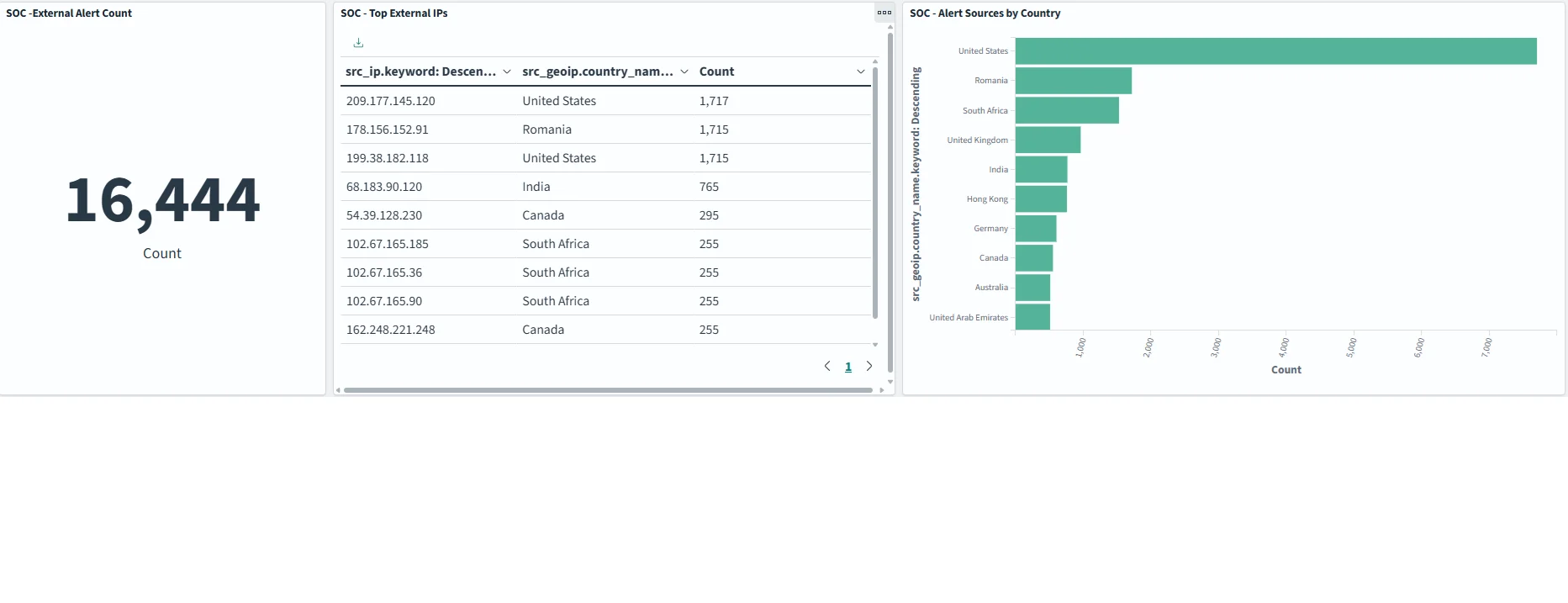标签:Active Directory, AD域, CISA项目, Cloudflare, Docker, DVWA, Go语言工具, IP 地址批量处理, IT运维, Metaprompt, Metasploitable, MITRE ATT&CK, NIDS, OPNsense, PE 加载器, Plaso, Socks5代理, Suricata, VLAN划分, WAF, Web报告查看器, Windows服务器, 仪表盘, 企业级安全, 威胁情报, 威胁阻断, 安全架构, 安全运营中心, 安全防御评估, 实验室环境, 家庭实验室, 家庭数据中心, 容器化, 开发者工具, 数据展示, 架构设计, 流量监控, 现代安全运营, 端口镜像, 紫队, 红队, 网络分段, 网络安全, 网络安全监控, 网络映射, 自动化扫描, 自动化防御, 请求拦截, 逆向工具, 防火墙, 隐私保护, 驱动开发