V33RU/bluesploit
GitHub: V33RU/bluesploit
一个 Metasploit 风格的蓝牙安全测试框架,覆盖经典蓝牙和 BLE 双协议,内置 101 个模块和 40+ 个 CVE 漏洞利用,面向授权渗透测试与安全研究。
Stars: 77 | Forks: 5
# BlueSploit - Bluetooth 漏洞利用框架
一个 Metasploit 风格的蓝牙安全测试框架,支持经典蓝牙 BR/EDR 和 BLE,专为授权的渗透测试和安全研究而构建。
```
██████╗ ██╗ ██╗ ██╗███████╗███████╗██████╗ ██╗ ██████╗ ██╗████████╗
██╔══██╗██║ ██║ ██║██╔════╝██╔════╝██╔══██╗██║ ██╔═══██╗██║╚══██╔══╝
██████╔╝██║ ██║ ██║█████╗ ███████╗██████╔╝██║ ██║ ██║██║ ██║
██╔══██╗██║ ██║ ██║██╔══╝ ╚════██║██╔═══╝ ██║ ██║ ██║██║ ██║
██████╔╝███████╗╚██████╔╝███████╗███████║██║ ███████╗╚██████╔╝██║ ██║
╚═════╝ ╚══════╝ ╚═════╝ ╚══════╝╚══════╝╚═╝ ╚══════╝ ╚═════╝ ╚═╝ ╚═╝
```
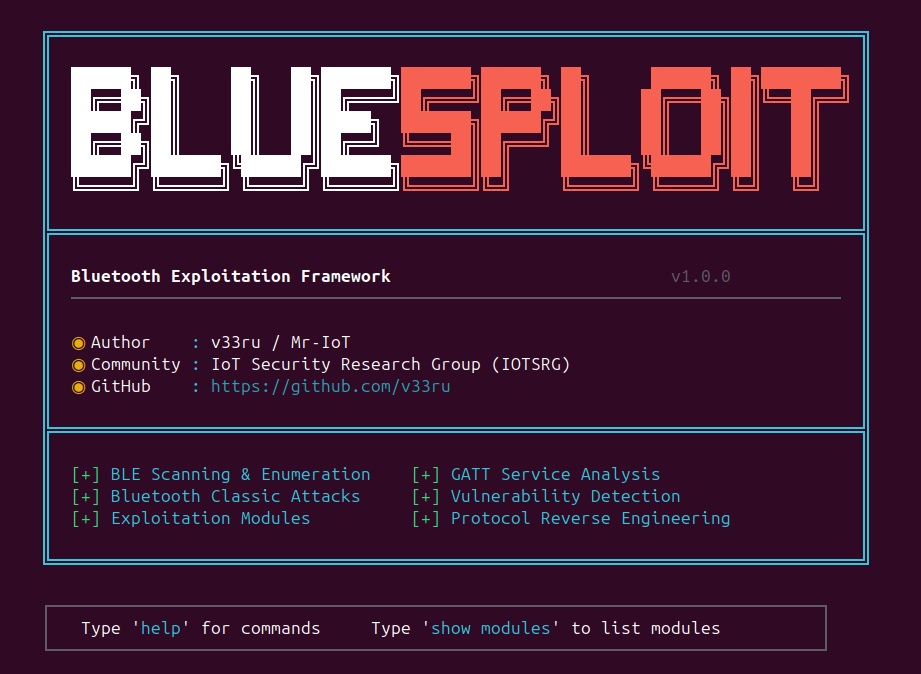
### 控制台预览
## 功能
- 横跨 6 大类别的 **101 个模块**:漏洞利用、扫描器、侦察、DoS、辅助工具、后渗透
- 实现了 **40+ 个 CVE**,并附带有效的概念验证漏洞利用 (2010 → 2026)
- **跨平台安装** — Linux (apt/dnf/yum/pacman/zypper/apk/xbps/emerge) + macOS (CoreBluetooth)
- **硬件支持** Ubertooth One, nRF52840, BTLEJack, HackRF One, YARD Stick One
- **交互式 CLI**,具备 Metasploit 风格的命令接口
- 通过 btmon/tcpdump 为所有模块运行提供 **PCAP 捕获**
- **双协议**覆盖:Bluetooth Classic (BR/EDR) 和 Bluetooth Low Energy (BLE)
## 安装说明
### 一键安装(推荐)
`install.sh` 会自动检测您的发行版 / 操作系统并安装所有内容:
```
git clone https://github.com/V33RU/bluesploit.git
cd bluesploit
./install.sh # basic
./install.sh --full # all extras (rich, cmd2, scapy, classic BT)
./install.sh --classic # add Bluetooth Classic support (Linux only)
./install.sh --dev # add dev tooling (pytest, black, flake8)
./install.sh --no-deps # skip system packages (Python deps only)
```
支持的包管理器:**apt, dnf, yum, pacman, zypper, apk, xbps, emerge** + macOS Homebrew。
### 手动安装
```
git clone https://github.com/V33RU/bluesploit.git
cd bluesploit
pip install -r requirements.txt
# 或作为 package
pip install .
```
### 各发行版系统前置条件
| 发行版 | 命令 |
|--------|---------|
| Debian / Ubuntu / Kali | `sudo apt install bluez bluetooth libbluetooth-dev python3-dev libglib2.0-dev pkg-config build-essential` |
| Fedora / RHEL / Rocky | `sudo dnf install bluez bluez-libs-devel python3-devel glib2-devel pkgconf-pkg-config gcc gcc-c++ make` |
| Arch / Manjaro | `sudo pacman -S bluez bluez-utils glib2 pkgconf base-devel` |
| openSUSE | `sudo zypper install bluez bluez-devel python3-devel glib2-devel pkg-config gcc gcc-c++ make` |
| Alpine | `sudo apk add bluez bluez-dev python3-dev glib-dev pkgconfig build-base linux-headers` |
| Void | `sudo xbps-install -Sy bluez bluez-devel python3-devel glib-devel pkg-config base-devel` |
| macOS | 无需安装 — CoreBluetooth 为内置组件(仅通过 `bleak` 支持 BLE) |
### 特定硬件的软件包(可选)
```
# Ubertooth One
sudo apt install ubertooth wireshark
# HackRF One
sudo apt install hackrf gr-bluetooth
# nRF52840 — 刷入 nRF Sniffer firmware,安装 Wireshark plugin
# BTLEJack — 将 BTLEJack firmware 刷入 micro:bit
# YARD Stick One
pip install git+https://github.com/atlas0fd00m/rfcat.git
```
## 快速入门
```
# 启动 interactive console
sudo python bluesploit.py
# 列出所有可用 modules
sudo python bluesploit.py --list
```
### 使用示例
```
bluesploit > use exploits/keystroke_injection
bluesploit (keystroke_injection) > set target AA:BB:CC:DD:EE:FF
bluesploit (keystroke_injection) > set payload hello world
bluesploit (keystroke_injection) > options
bluesploit (keystroke_injection) > run
```
## 控制台命令
| 命令 | 描述 |
|---------|-------------|
| `help` | 显示所有命令 |
| `use ` | 选择一个模块 |
| `set ` | 设置模块选项 |
| `options` | 显示当前模块选项 |
| `run` / `exploit` | 执行选定的模块 |
| `back` | 取消选择当前模块 |
| `show modules` | 列出所有模块 |
| `search ` | 按名称/描述搜索模块 |
| `info [module]` | 显示详细的模块信息 |
| `exit` / `quit` | 退出框架 |
## 模块 (101)
### 漏洞利用 (69)
| 模块 | CVE | 描述 |
|--------|-----|-------------|
| `exploits/keystroke_injection` | CVE-2023-45866 | 0-click Bluetooth HID 击键注入 |
| `exploits/bluffs` | CVE-2023-24023 | BLUFFS 会话密钥降级 |
| `exploits/bluffs_mitm` | CVE-2023-24023 | BLUFFS 主动 MITM 攻击 |
| `exploits/braktooth_esp32` | CVE-2021-28139 | BrakTooth ESP32 LMP 崩溃 / ACE |
| `exploits/bluefrag` | CVE-2020-0022 | Android Bluetooth A2DP RCE |
| `exploits/bias` | CVE-2020-10135 | BIAS 认证绕过 |
| `exploits/badkarma` | CVE-2020-12351 | BleedingTooth L2CAP 类型混淆 RCE |
| `exploits/badchoice` | CVE-2020-12352 | BleedingTooth A2MP 信息泄露 |
| `exploits/knob` | CVE-2019-9506 | 密钥协商熵检查 |
| `exploits/knob_active` | CVE-2019-9506 | 主动密钥熵降级 |
| `exploits/sweyntooth` | CVE-2019-16336+ | SweynTooth BLE 链路层漏洞利用 |
| `exploits/blueborne_linux_rce` | CVE-2017-1000251 | Linux BlueZ L2CAP 栈溢出 RCE |
| `exploits/blueborne_leak` | CVE-2017-0781 | Android 蓝牙信息泄露 |
| `exploits/bnep_heap_disclosure` | CVE-2017-13258 | Android BNEP 堆信息泄露 |
| `exploits/whisperpair` | CVE-2025-36911 | Google Fast Pair 劫持 — 在未开启配对模式的情况下强制配对 |
| `exploits/zephyr_ble_smp_crash` | CVE-2025-10456 | Zephyr RTOS BLE 固定通道整数溢出 DoS |
| `exploits/airoha_race_chain` | CVE-2025-20700/20701/20702 | Airoha 3 阶段 BLE→Classic→RACE RCE 链 |
| `exploits/rfcomm_privesc_race` | CVE-2026-23671 | Windows RFCOMM 驱动竞态条件 — 本地 EoP 提权至 SYSTEM |
| `exploits/apple_bt_dos` | CVE-2026-20650 | 通过畸形数据包导致 Apple BT 子系统崩溃 |
| `exploits/harmonyos_bt_oob` | CVE-2026-28540 | Huawei HarmonyOS 蓝牙 OOB 堆信息泄露 |
| `exploits/bluebugging` | - | 通过 RFCOMM 进行 AT 命令注入 |
| `exploits/bluesnarfing` | - | OBEX 文件窃取(联系人、短信、日历) |
| `exploits/a2dp_inject` | - | A2DP 音频注入与媒体控制 |
| `exploits/ble_mitm` | - | BLE 中间人(MITM)中继 |
| `exploits/ble_pairing_downgrade` | - | 强制使用 JustWorks/传统配对 |
| `exploits/ble_replay` | - | BLE GATT 捕获与重放 |
| `exploits/ble_sc_bypass` | - | BLE Secure Connections 绕过 |
| `exploits/ble_longrange` | - | BT 5.x coded PHY / 远距离攻击 |
| `exploits/mesh_attack` | - | BLE Mesh 配置 MITM 与重放 |
| `exploits/unauth_write` | - | 未经身份验证的 BLE GATT 写入 |
| `exploits/rfcomm_shell` | - | RFCOMM 反向/绑定 shell |
| `exploits/obex_exploit` | - | OBEX OPP/FTP 文件推送/拉取 |
| `exploits/pin_bruteforce` | - | 经典蓝牙 4 位 PIN 暴力破解 |
### 扫描器 (5)
| 模块 | 描述 |
|--------|-------------|
| `scanners/vuln_scanner` | 基于设备配置文件的自动 CVE 检测 |
| `scanners/vuln_scan` | 快速 BLE 漏洞扫描 |
| `scanners/blueborne_scan` | BlueBorne 漏洞检测 |
| `scanners/ble_vuln_scanner` | 全面的 BLE 安全评估 |
| `scanners/hidden_scanner` | 通过暴力破解发现不可见设备 |
### 侦察 (6)
| 模块 | 描述 |
|--------|-------------|
| `recon/discovery` | 带详细信息的 BLE 设备发现 |
| `recon/gatt_enum` | BLE GATT 服务/特征枚举 |
| `recon/sdp_enum` | 经典 SDP 服务枚举 |
| `recon/adv_parser` | BLE 广播深度分析与指纹识别 |
| `recon/oui_lookup` | MAC 地址厂商识别 |
| `recon/version_fingerprint` | 通过蓝牙进行 OS/固件指纹识别 |
### DoS (10)
| 模块 | 描述 |
|--------|-------------|
| `dos/bluesmack` | L2CAP echo 洪泛 |
| `dos/l2ping_flood` | L2CAP ping 洪泛 |
| `dos/sdp_flood` | SDP 查询洪泛 |
| `dos/rfcomm_flood` | RFCOMM 连接耗尽 |
| `dos/notify_flood` | BLE 通知洪泛 |
### 辅助工具 (6)
| 模块 | 描述 |
|--------|-------------|
| `auxiliary/hw_detect` | 检测所有已连接的蓝牙硬件 |
| `auxiliary/ble_fuzzer` | BLE ATT/GATT/SMP 协议模糊测试器 |
| `auxiliary/ubertooth_sniff` | Ubertooth One 被动嗅探器 |
| `auxiliary/nrf_sniffer` | nRF52840 BLE 数据包捕获 |
| `auxiliary/btlejack_capture` | BTLEJack 连接跟踪与劫持 |
### 后渗透 (2)
| 模块 | 描述 |
|--------|-------------|
| `post/link_key_dump` | 从 BlueZ 中提取存储的 link key |
| `post/bt_impersonation` | 使用窃取的 link key 冒充已配对设备 |
## 支持的硬件
| 设备 | 协议 | 用例 |
|--------|----------|----------|
| USB 蓝牙适配器 (HCI) | Classic + BLE | 扫描、漏洞利用、连接 |
| Ubertooth One | Classic + BLE | 被动嗅探、频谱分析 |
| nRF52840 Dongle | BLE | 被动 BLE 嗅探 |
| BTLEJack (micro:bit) | BLE | 连接劫持与注入 |
| HackRF One | Classic | 原始蓝牙基带捕获 |
| YARD Stick One | Sub-GHz | RF 分析与注入 |
## 包含的 CVE
| CVE | 名称 | 影响 |
|-----|------|--------|
| CVE-2023-45866 | HID 击键注入 | 通过 HID 实现 0-click RCE |
| CVE-2023-24023 | BLUFFS | 会话密钥降级 / MITM |
| CVE-2021-28139 | BrakTooth | ESP32 任意代码执行 |
| CVE-2020-0022 | BlueFrag | Android RCE |
| CVE-2020-10135 | BIAS | 认证绕过 |
| CVE-2020-12351 | BadKarma | Linux RCE |
| CVE-2020-12352 | BadChoice | Linux 信息泄露 |
| CVE-2019-9506 | KNOB | 加密密钥降级 |
| CVE-2019-16336 | SweynTooth | BLE 协议栈崩溃 |
| CVE-2017-1000251 | BlueBorne (Linux) | Linux RCE |
| CVE-2017-0781 | BlueBorne (Android) | Android 信息泄露 |
| CVE-2017-13258 | BNEP 堆信息泄露 | Android 内存泄露 |
| CVE-2025-36911 | WhisperPair | Google Fast Pair 劫持 |
| CVE-2025-10456 | Zephyr BLE 崩溃 | Zephyr RTOS DoS / 内存破坏 |
| CVE-2025-20700/20701/20702 | Airoha RACE 链 | Airoha 芯片组 RCE (Sony/Bose/JBL/29+ 设备) |
| CVE-2026-23671 | RFCOMM 提权竞态 | Windows RFCOMM 驱动本地 EoP 提权至 SYSTEM |
| CVE-2026-20650 | Apple BT DoS | Apple BT 子系统崩溃 |
| CVE-2026-28540 | HarmonyOS BT OOB | Huawei HarmonyOS 蓝牙堆信息泄露 |
## 项目结构
```
bluesploit/
├── bluesploit.py # Main entry point
├── setup.py # Package installation
├── requirements.txt # Python dependencies
├── core/
│ ├── base.py # Module base classes & data models
│ ├── interpreter.py # Interactive CLI (Metasploit-style)
│ ├── loader.py # Dynamic module loader
│ ├── hardware.py # Hardware detection & abstraction
│ ├── capture.py # PCAP capture (btmon/tcpdump)
│ ├── utils/
│ │ └── printer.py # Colored output & banners
│ └── ui/
│ └── themes.py # Color themes
├── modules/
│ ├── exploits/ # 69 exploit modules
│ ├── scanners/ # 5 scanner modules
│ ├── recon/ # 6 reconnaissance modules
│ ├── dos/ # 10 denial-of-service modules
│ ├── auxiliary/ # 6 auxiliary/hardware modules
│ └── post/ # 2 post-exploitation modules
└── data/
├── oui/ # MAC address OUI database
├── profiles/ # Device profile definitions
├── signatures/ # Vulnerability signatures
└── wordlists/ # PIN wordlists for brute-force
```
## 环境要求
- **Python** 3.8+
- **操作系统:** 带有 BlueZ 协议栈的 Linux(所有主要发行版 — 参见安装表)或 macOS(仅通过 CoreBluetooth 支持 BLE)
- **权限:** 大多数 Linux 模块需要 Root / sudo 权限(原始 HCI 套接)
### 核心依赖
| 包 | 用途 |
|---------|---------|
| `bleak` | BLE 扫描与 GATT(跨平台) |
| `pybluez2` | 经典蓝牙 L2CAP/RFCOMM/HCI |
| `scapy` | 数据包构造与注入 |
| `cryptography` | 密钥派生与密码分析 |
| `bluepy` | 底层 BLE 访问 |
| `pyserial` | 硬件 Dongle 通信 |
| `btlejack` | BLE 连接劫持 |
| `rich` | 终端 UI(表格、进度条) |
| `cmd2` | 高级 REPL |
## 作者
**Mr-IoT** / Mr-IoT
## 许可证
本项目采用 [MIT 许可证](LICENSE) 进行授权。
## 免责声明
**本工具仅供教育目的和授权的安全测试使用。**
- 仅可对您拥有或已获得明确书面授权测试的设备使用
- 未经授权访问计算机系统和网络是违法行为
- 作者不对因滥用本工具造成的任何损害负责
- 请始终遵守当地关于无线安全测试的法律法规
标签:BLE, BR/EDR, BTLEJack, CVE利用, HackRF, nRF52840, PCAP, Python开发, Ubertooth, 交互式CLI, 反取证, 安全评估, 密码管理, 拒绝服务, 插件系统, 渗透测试框架, 硬件黑客, 经典蓝牙, 网络安全, 蓝牙低功耗, 蓝牙安全, 逆向工具, 防御, 隐私保护